Security Risk: Dangerous
Exploitation Level: Easy/Remote
DREAD Score: 7/10
Vulnerability: SQL Injection
Patched Version: 12.0.8
Update 11/3/2017:
We are always looking for the latest to be shared with you and now we have released our WordPress Security Guide, were you can read all about vulnerabilities and best practices to keep your website protected.
As part of a vulnerability research project for our Sucuri Firewall, we have been auditing popular open source projects looking for security issues.
While working on the WordPress plugin WP Statistics, we discovered a SQL Injection vulnerability. This plugin is currently installed on 300,000+ websites.
Are You at Risk?
This vulnerability is caused by the lack of sanitization in user provided data. An attacker with at least a subscriber account could leak sensitive data and under the right circumstances/configurations compromise your WordPress installation.
If you have a vulnerable version installed and your site allows user registration, you are definitely at risk.
Technical Details
WordPress provides an API that enables developers to create content that users can inject to certain pages just using a simple shortcode:
[shortcode atts_1=”test” atts_2=”test”]
Among other functionalities, WP Statistics allows admin users to get detailed information related with the number of visits by just calling the shortcode below:
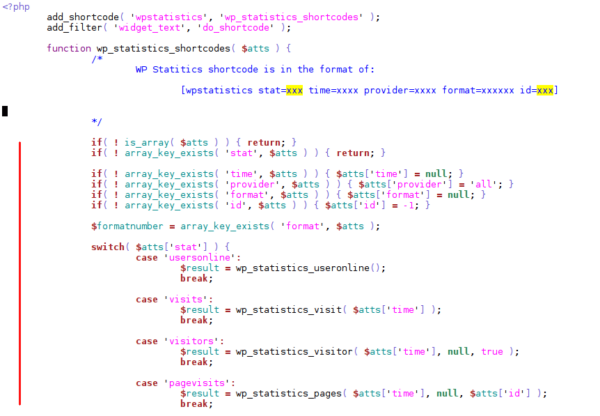
As you can see on the above image, some attributes of the shortcode wpstatistics are being passed as parameters for important functions and this shouldn’t be a problem if those parameters were sanitized, but as we’ll see this is not the case.
One of the vulnerable functions wp_statistics_searchengine_query() in the file “includes/functions/functions.php” is accessible through WordPress’ AJAX functionality thanks to the core function wp_ajax_parse_media_shortcode().
This function doesn’t check for additional privileges, allowing subscribers to execute this shortcode and inject malicious data to its attributes. (This attack vector was also described here).
In a number places in the code, user input coming from attributes of the wpstatistics’ shortcode are included in SQL queries without being sanitized. Below one of the queries that were exploitable:
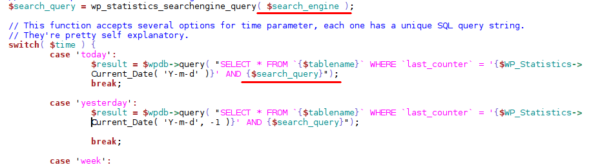
The wp_statistics_searchengine_query() basically returns the same value as the one passed in the shortcode attribute provider and its content is added directly to the raw SQL query.
Update as Soon as Possible
If you’re using a vulnerable version of this plugin, update as soon as possible!
In the event where you cannot do this, we strongly recommend leveraging the Sucuri Firewall or equivalent technology to have the vulnerability patched virtually.











5 comments
WOW! I literally just deleted this plugin off of a client’s site today before even seeing this post! Thank you Sucuri!
Plz give me some POC
Many thanks 😀
Hey John, thank you very much for sharing important information and pointing out the vulnerability in WP Statistics. I’ve upgraded the plugin to version 12.0.9 and it looks like the version you’ve used is 12.0.8. You mentioned “Upgrade as soon as possible” If possible can you please share updates by taking a look again on 12.0.9 version of this plugin? Can we use it anymore?
This is fixed since version 12.0.8, they released another version (12.0.9) to fix a reflected XSS. If you are using the last version you are good, (although this is always relative) .
Thank you, that’s great
Comments are closed.