An SQL injection, or SQLi, is a cyberattack that targets websites and applications that use SQL databases. These dangerous attacks involve injecting malicious SQL code into existing SQL statements through a website’s input fields, ultimately allowing unauthorized access to sensitive information, including customer records, intellectual property, and personal data.
SQL injection attacks can affect any application that uses a SQL database and handles data, including websites, desktops, and phone apps — with extremely serious consequences. Attackers can leverage SQLi to locate the credentials of administrators and gain complete control over affected websites, applications, and database servers.
Contents
SQL injections are typically performed via web page or application input. These input forms are often found in features like search boxes, form fields, and URL parameters.
To perform an SQL injection attack, bad actors need to identify vulnerabilities within a web page or application. After locating a target, attackers create malicious payloads and send their input content to execute malicious commands.
In some cases, bad actors may simply leverage an automated program to carry out an SQLi for them — all they need to provide is the URL of the target website to obtain stolen data from the victim.
The Open Web Application Security Project (OWASP) lists injection attacks, which include SQL injections, as the third most serious web application security risk in 2021. SQL injection vulnerabilities can be exploited in a variety of different ways.
A few common methods for SQL injections include executing commands on the database server, retrieving data based on errors, or interfering with the query logic.
This type of SQL injection is the most popular method performed by attackers.
This injection technique allows bad actors to extract data from the database by extending the results from the original query. It uses the UNION SQL operator to integrate two SELECT statements into a single result, then returns it as part of the response.
Typically more sophisticated and difficult to perform than other varieties of injections, attackers perform blind SQL injections when generic error messages are received from the target.
Blind SQL injections differentiate themselves from regular SQL injections in the method that they retrieve information from the database. In this technique, bad actors query the database for true or false questions, then determine the answer based on the response, as well as the time it takes to retrieve a server response when using it with time-based attacks.
This type of attack overwrites the logic and conditions of the query to its own. It is commonly used in permission or authentication queries, where they trick the database into thinking they have elevated permissions or correct credentials.
Boolean-based SQL injections are also used in blind SQL injections, where they proceed by elimination to extract data from the database. By sending tons of requests, each with a condition slightly different from the precedents, attackers can figure out what is the data stored based on the result of the operation.
In an error based SQL injection, attackers exploit database errors from a web page or application that have been triggered by unsanitized inputs.
During an attack, this technique uses error messages to return full query results and reveal confidential information from the database. This method can also be used to identify if a website or web application is vulnerable and obtain additional information to restructure malicious queries.
During a normal SQL injection, bad actors can simply read text as it is returned. However, when attackers are unable to retrieve information from a database server, they will often employ time-based SQL injections to achieve their results. This works by using operations which take a long time to complete—often many seconds.
Time-based SQL injections are commonly used when determining if vulnerabilities are present on a web application or website, as well as in conjunction with Boolean-based techniques during Blind SQL injections.
In the following SQL injection example, we try to login by comparing the user input (username and password) to those stored in the database.
Caution
This is an example of what NOT to do — this query has multiple flaws by design. Notably, it is vulnerable to SQL injection, and does not use hashed and salted passwords.
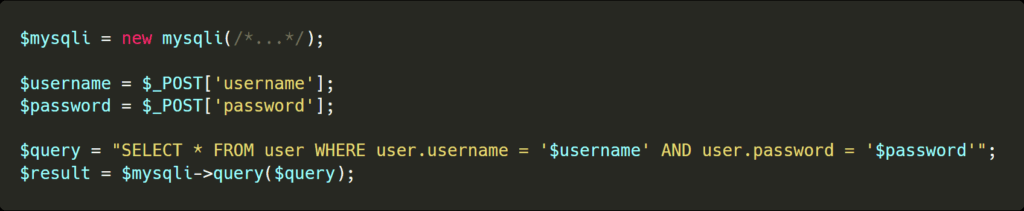
In this example, the query is built by concatenating the user-specified values (username and password) directly into the query.
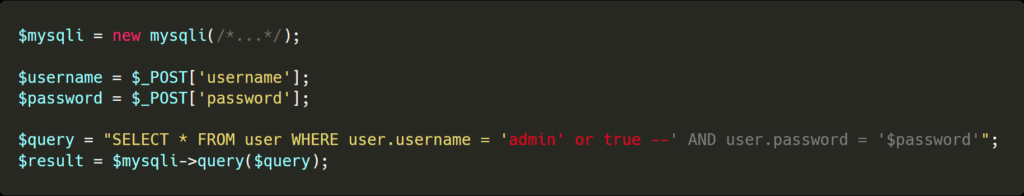
This makes it easy for an attacker to escape the quotes and inject more SQL operations. By having the following username admin’ or true — it is possible for an attacker to login with the account of his choice.
SQL injections are notoriously difficult to detect. Unlike cross-site scripting, remote code injection, and other types of infections, SQL injections are vulnerabilities that do not leave traces on the server. Instead, the exploit executes genuine queries on the database. As a result, the majority of attacks are detected once an attacker has used a vulnerability to perform malicious actions or gained administrative access.
By taking precautionary measures and actively monitoring your database and its queries, you can identify if an attacker is running malicious injections on your website.
The Sucuri Firewall can help virtually patch website vulnerabilities like SQLi and block attacks against your website.
Attackers frequently target websites that use known vulnerabilities. Undisclosed, unpatched, or zero-day vulnerabilities also account for a large percentage of SQL injections during targeted attacks.
The easiest way to protect your website against SQL injections is to keep all of your third party software and components up to date. However, a number of techniques exist that you can use to help prevent SQL injection vulnerabilities.
Prepared statements are used to ensure none of the dynamic variables you need in a query can escape their position. The core query is defined beforehand, with the arguments and their types afterward.
Since the query knows the type of data that is expected, such as string or number, they know exactly how to integrate them to the query without causing issues.
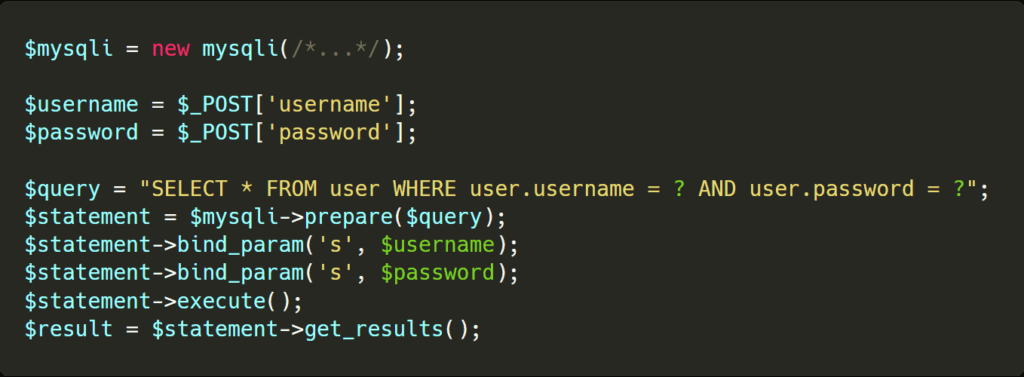
In this example, even if the username or password variables attempt to escape their query, the prepared statements properly escape their characters to prevent unexpected behavior or SQLi.
Stored procedures are frequent SQL operations that are stored on the database itself, varying only with their arguments. Stored procedures make it much more difficult for attackers to execute their malicious SQL, as it is unable to be dynamically inserted within queries.
As a rule of thumb, never trust user-submitted data. You can perform allowlist validation to test user input against an existing set of known, approved, and defined input. Whenever data is received that doesn’t meet the assigned values, it is rejected—protecting the application or website from malicious SQL injections in the process.
The Principle of Least Privilege is a computer science principle that strengthens access controls to your website to mitigate security threats.
To implement this principle and defend against SQL injections:
During a normal SQL injection, bad actors can simply read text as it is returned. However, when attackers are unable to retrieve information from a database server, they will often employ time-based SQL injections to achieve their results. This works by using operations which take a long time to complete—often many seconds.
Time-based SQL injections are commonly used when determining if vulnerabilities are present on a web application or website, as well as in conjunction with Boolean-based techniques during Blind SQL injections.
You can protect against generic SQL injections with a web application firewall. By filtering potentially dangerous web requests, web application firewalls can catch and prevent SQL injections.
Note
This method only prevents attackers from reading the cookie. Attackers can still use the active browser session to send requests while acting as an admin user. This method is also useful only when relying on cookies as the main identification mechanism.
Our Website Application Firewall (WAF) stops bad actors, protects your website against malicious code, and helps prevent website hacks.
Follow these steps to identify and fix SQL injection attacks in your environment.
The first step in recovering from cross-site scripting is to identify where the vulnerability is located. You can refer to our helpful hacked website guide for detailed steps.
Once you have obtained information about the location of the malware, remove any malicious content or bad data from your database and restore it to a clean state. You’ll also want to check the rest of your website and file systems for backdoors.
Vulnerabilities in databases, applications, and third-party components are frequently exploited by hackers. Once you have identified the vulnerable software, apply patches and updates to the vulnerable code along with any other out-of-date components.
When a compromise occurs, it is important to change all of your passwords and application secrets as soon as the vulnerability is patched. Prevent reinfection by cleaning up your data to ensure that there are no rogue admin users or backdoors present in the database.
Set up a monitor to identify any rogue SQL statements to your database. A tool that uses behavioral analysis and/or machine learning can help detect indicators of compromise (IoC) to your website.
Consider setting up a website firewall to filter malicious requests to your website and server. These can be particularly useful to provide protection against new vulnerabilities before patches are made available.
Get Help with SQL Injection Attacks
If you believe your website has been impacted by an SQL injection attack and need help, our website malware removal and protection services can repair and restore your hacked website.
Our dedicated incident response team can help safely remove malicious code from your website file systems and database, restoring it to its original state.
Say on top emerging website security threats with our helpful guides, email, courses, and blog content.