Authored by Daniel Cid, Tony Perez.
We have been blogging about the massive brute force attacks against WordPress websites over the past few days, today we want to provide better context of the scale by sharing some more data on what we saw and continue to see.
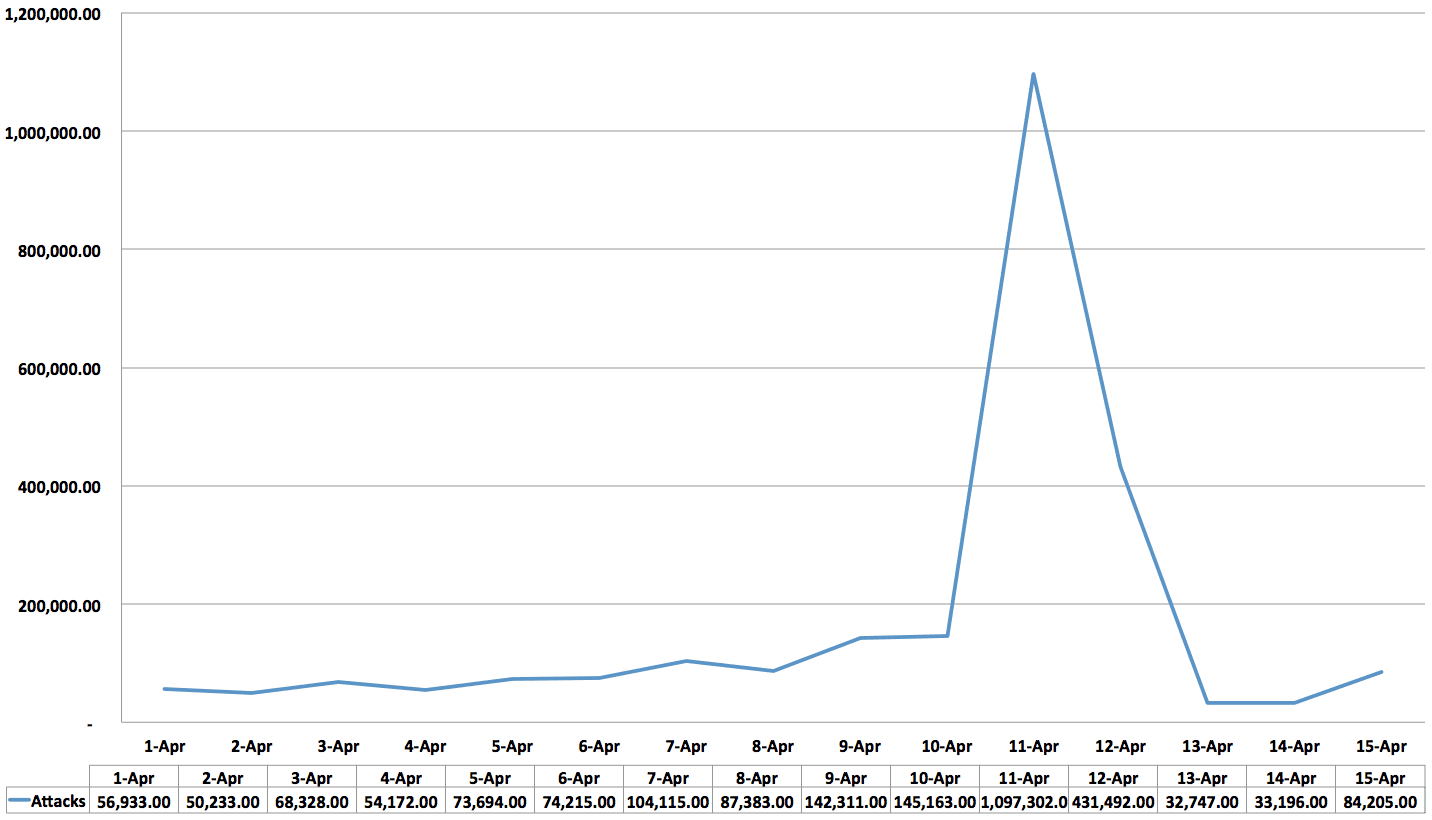
In our previous report, we said that the number of scans detected almost tripled from the old averages, increasing from around 30,000 scans per day to around 100,000 per day in April.
However, the numbers are a lot larger than that. We compiled the averages per day again and on Thursday (April 11), the number of scans increased to more than 1,000,000 scans, which is more 30x the averages. This is the compilation per day:
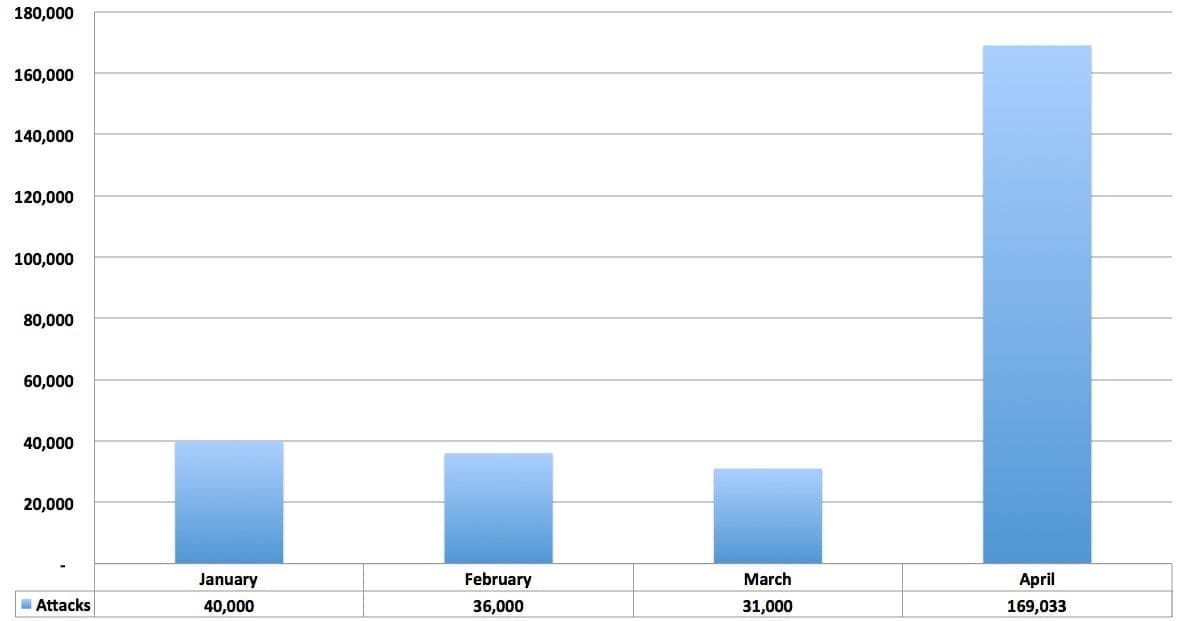
To put into perspective how this relates to previous months, here’s a breakdown of daily averages going back to January:
So yes, what started as a blip turned into a large-scale attack in a short 24 hour period. To undermine the scale of the attack would be a mistake, but to over speculate on intention is just as a grave a mistake. Fortunately, we do have more data on the IP ranges, usernames and passwords being used. For the most part it’s remained pretty consistent, that’s good to know as it makes some of the preventive techniques being discussed in various forums fairly effective.
By far, the most effective strategy to defend against such an attack is through the implementation of some form of multi-factor or two-factor authentication. This is a more effective long-term strategy, whether through the implementation of a plugin like Google Authenticator or Duo Security. There are also a series of other techniques that could prove very beneficial, specifically employing a whitelist approach to those allowed access to your wp-admin panels.
A white-list approach will allow you to dictate which IP’s are allowed, while explicitly denying all other IPs. This can be done via your .htaccess files and/or via your web application firewall (WAF). Another effective strategy would be through a second layer of authentication using some of the basics like Basic Access Authentication. This would provide an effective defensive layer against automated attacks targeting default wp-admin panels.
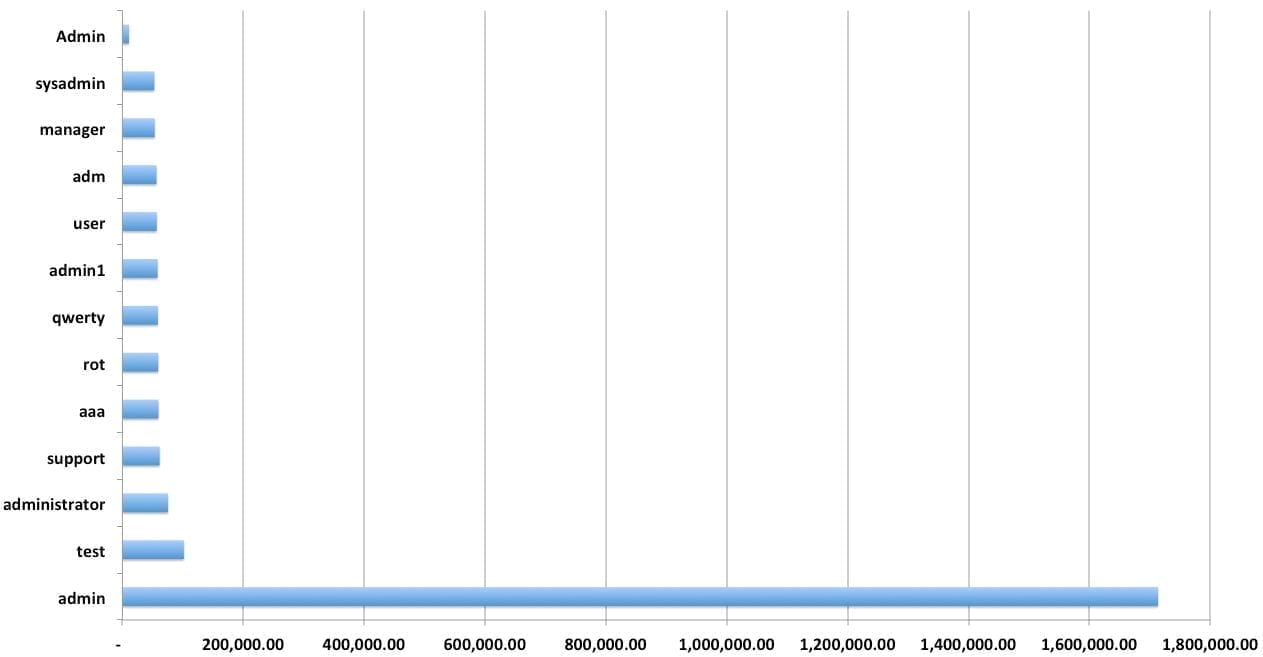
Lastly, we often try to focus on things like proper use of the “administrator” role in the place of focusing on users “admin” or “administrator” (fundamentally different). In this case, where a botnet is leveraging wordlists and using those specific users and password combinations, it does make sense to avoid those users all together. I would probably recommend avoiding the list of users below in general. That being said, don’t be fooled, the use of the name itself is only half the battle. In this case it makes sense, but enumerating the users and their roles is fairly straightforward, and this would only protect you against these types of automated attacks.
More Data
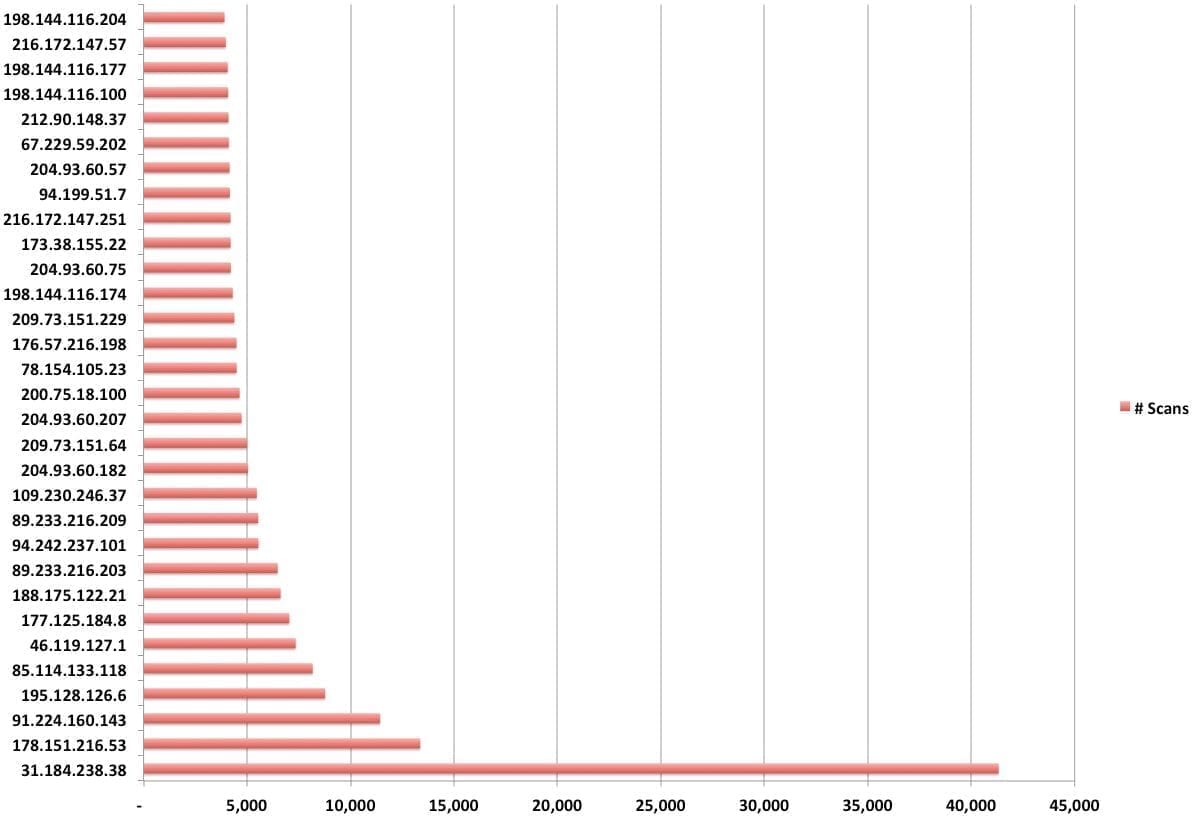
So yes, what started as an above average brute force attack, went on to become a very large scale attack. As for the top usernames, passwords and IP addresses being attempted, there hasn’t been much change, fortunately.
Here are the top data points for each category:
IP Attack Distribution
Username Distribution
Top Password Combinations
Based on what we’re seeing, we believe that the attacks are making use of a number of username/password lists. One that appears to have a lot of similarities to the combinations includes: http://pastebin.com/raw.php?i=UTUsmPm6. The top combinations however are these:
21144 [pwd] => admin
14377 [pwd] => 123456
14087 [pwd] => password
11366 [pwd] => 12345678
10409 [pwd] => 666666
9700 [pwd] => 111111
9336 [pwd] => 1234567
8902 [pwd] => qwerty
8269 [pwd] => 123321
8193 [pwd] => 12345
7752 [pwd] => 123123
7692 [pwd] => 159753
7364 [pwd] => 1234567890
6901 [pwd] => 0
6609 [pwd] => 123qwe
6179 [pwd] => 123654
6160 [pwd] => #@F#GBH$R^JNEBSRVWRVW
6067 [pwd] => 112233
5964 [pwd] => 159357
5392 [pwd] => $#GBERBSTGBR%GSERHBSR
5326 [pwd] => 12345qwe
5281 [pwd] => 1234
5141 [pwd] => 654321
5060 [pwd] => 147852
5058 [pwd] => %G#GBAEGBW%HBFGBFXGB
5024 [pwd] => RGA%BT%HBSERGAEEAHAEH
4963 [pwd] => 222222
4928 [pwd] => 7777777
4900 [pwd] => 147258
4898 [pwd] => 123
4861 [pwd] => aethAEHBAEGBAEGEE%
4838 [pwd] => 121212
The Impacts
It’s unfortunate, but over the past few days there has been a lot of speculation around the intent of these attacks. We’re a detection and remediation company by trade and we still can’t clearly outline the true intentions of the attacks. We did however shared our thoughts on possible intentions a few days ago, but again they are highly speculative. What we do know is that the attack was real and it appears to be dying down.
We also know that the botnet performing the attacks is fairly decent in size, but not using anything complex in terms of username and password lists. We know that the IP’s have remained fairly constant, making defense a lot easier and we also know that it appears to be throttling down.







24 comments
The Internet is a better place with you in it.
Thank you for this fine work and review,
-Jim
Some of the Top Password Combinations are just mind-boggling!
I love when you talk data-y to me. Still hoping to hear what is actuqlly being done with compromised machines? Are they furthering the attack, injecting links, exporting DB data, etc?
All of the above – mostly SEO spam and email spam, but also a large amount of iframe injections distributing a nasty rootkit (TDL3/4 aka TDSS or Alureon variants), if your site was compromised get help from a security professional that knows Windows and web security – the rootkit will hide any malware including itself from “regular” malware scanners including MBAM. If only the PC or only the site are cleaned up, one can re-infect the other. This is not all cases but it’s a pretty bad worst-case scenario and it is happening. There are a lot of long-forgotten unattended WordPress sites out there so this will take some time to clean up.
How do you know if they managed to get in ? and what to do if you think your hit ?
Hi Glenn, hard to say. Depends on what and how you’re monitoring and auditing your environment. If you are, you’d likely see a payload being dropped, but it’s more important that you just get cray with it and purge things out.
okay, a non-tech blogger here (the dangerous kind?) so I’m thinking I could take the top 5 IP addresses in your graphic and block them from my cpanel? would this be a helpful thing to do? -and no, I don’t use ‘admin’ to log in, I at least got that part right… thanks for the article.
You want to block them from your cpanel? I’d advise blocking them from your WordPress install. You could possibly use Cpanel to block them yes..
oh right, I think I meant my control panel at my hosting company, I can block IP addresses there..yeah, I hardly know my way around…
Seconding the sentiment of Jim Walker. The work Sucuri is doing to support the WordPress community is hugely appreciated.
Thank you for sharing this info.
This article highlights a well known exploit. But it can only be exploited if the site owner, I hesitate to use the term… webmaster, fails to follow the most basic rules for WP security. Beginners make the mistake all the time. I made this mistake. But the way hacking is these days (hell even 30 years ago for that matter) I quickly learned the ambiguous path I tread. Unauthorized pen-testing and subsequent ownership (like a little bitch) is a clear and present danger. Arm yourself. Word to the wise, security is best when setup during (soon after) site installation. Just search security plugins onhttp://wordpress.org/extend/plugins/ the forum files will fill in the blanks. Look for most stars and number of downloads to point the way. As always, though, read the fine print and good luck. (ps You will get owned eventually, if not already, more times than you can count if you do not mind security on some level. Stay on top as best you can. Or else. https://www.facebook.com/Protious.comLLC
.
This is horrible, I hired a Chicago based company, http://freshserve.net/ to remove the hack. Everything has been perfect sense then.
Hi Guys, this is spam. The link is to a one page site who is piggy backing on Sucuri services to overcharge end users.
Security n00b here…can someone explain how to read the chart of username/password combos that were being tried the most? e.g.
21144 [pwd] => admin
14377 [pwd] => 123456
14087 [pwd] => password
I’ve been making practice of not keeping any accounts with an “admin” password and making non-generic passwords. It’s been great reading the sucuri blog to help with basic preventative measures. Thanks all.
Its like when you create your username, make sure that your password is not related to your family, your own name, birthday or someone you knew.
Make sure that your password is not easily be comprehend by someone.
A mix character case must be your guide from A-Z, a-z, 0-9 as well as special characters.
and last thing is to make a habit of changing your password from time to time.
Thanks Daniel
Makes me feel a whole lot safer being with you guys.
Looking to upgrade from 5 sites to 10 sites coverage in the next week or so.
Thank you for this info, useful data to know (users/passwords).
A client of mine got his site hacked, he used the deadly admin/admin combo.
The worst part was that he didn’t want to change his username or password (and I can’t make him) so I made this plugin for a two-factor auth type login (uses email instead of text messages/one time pads etc).
(If it’s not appropriate to link to plugins, please remove the link.)
http://wordpress.org/extend/plugins/two-factor-auth/
Now he has a secure login and doesn’t have to change his username and/or password.
Thanks Daniel for posting!Specially the data you provided for the IP attacks,username and top password combinations are useful.
Hi Daniel
Thanks for the article, I have been Googling to find an example of any one implementing both Google Two Factor authentication and .htaccess security for wp-admin and wp-login.php. I was wondering which method would be a better to protect against brute force attack or should I implement both methods?
We’ve attempted to try and block these attacks and I’ve written a guide how to do the same if anyone’s interested: http://blog.ed.gs/useful/wordpress-brute-force-protection-hack/
Comments are closed.