After many suggestions, we decide to setup a blog to better communicate with our users. Expect updates from http://sucuri.net and some security-related posts from us.
You May Also Like
October Cybersecurity Month
- October 1, 2018
Since 2003, October has been recognized as National Cybersecurity Awareness Month. It is an annual campaign to raise awareness about the importance of cybersecurity and…
WordPress Database Brute Force and Backdoors
- March 11, 2020
We regularly talk about brute force attacks on WordPress sites and explain why WordPress credentials should always be unique, complex, and hard to guess. However,…
How to Audit & Cleanup WordPress Plugins & Themes
- Last Updated: February 21, 2026
WordPress makes it easy to extend your website with powerful functionality. Plugins and themes allow site owners to add features, customize design, and integrate new…
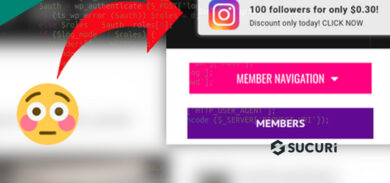
Magbo Spam Injection Encoded with hex2bin
- March 3, 2023
We recently had a new client come to us with a rather peculiar issue on their WordPress website: They were receiving unwanted popup advertisements but…
Personal Online Security – Account Management
- January 24, 2020
Continuing a series on how to better strengthen your personal online privacy, we are looking to take personal inventory of how we connect online. These…
How to Add SSL & Move WordPress from HTTP to HTTPS
- March 6, 2019
Moving a WordPress website from HTTP to HTTPS should be a priority for any webmaster. Recent statistics show that over 33% of website administrators across…
ThinkPHP 5.x – Remote Code Execution Actively Exploited In The Wild
- April 8, 2019
Earlier this year, we noticed an increase in attacks aiming at ThinkPHP. ThinkPHP is a PHP framework that is very popular in Asia. If you…
Can you be Hacked by Visiting a Website?
- March 16, 2022
Visiting websites throughout the decades has always had its risks. With the creation of Flashplayer and JavaScript, site visitors could potentially be impacted by malicious…
What Should You do if Your WordPress Site was Hacked?
- January 19, 2022
These days WordPress infections are very common. In 2021, internetlivestats.com counted over 81 million websites hacked. If you’re one of the millions, you need to…
CoinImp Cryptominer and Fully Qualified Domain Names
- July 5, 2018
We are all familiar with the conventional domain name notation, where different levels are concatenated with the full stop character (period). E.g. “www.example.com”, where “www”…









2 comments
“/>
“/>
[click here](javascript:alert(document.domain))
Comments are closed.