Two factor authentication (2FA) provides an extra layer of security that passwords alone can’t provide. Requiring an extra step for users to verify their identity reduces the chance a bad actor can gain access to data however.
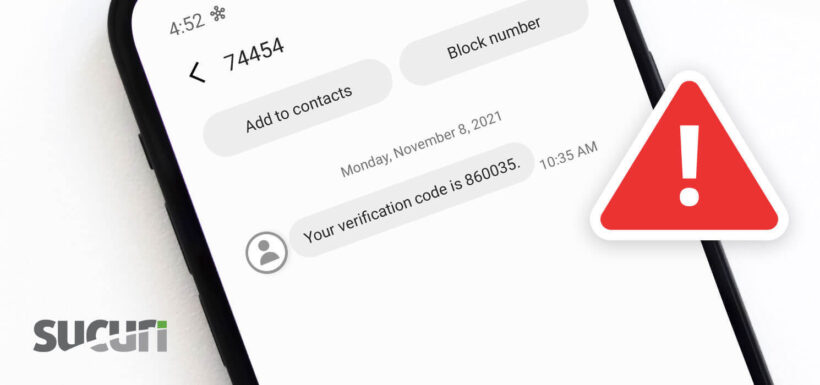
One of the most common methods of 2FA is SMS text messages. The problem is that SMS isn’t actually a secure medium. Hackers have several tools in their arsenal that can intercept, phish, and spoof SMS. Despite this security flaw and better options for authentication, SMS-based 2FA is still widely used due to how nothing else is required.
How Hackers Intercept SMS
It’s always a good idea to add 2FA to any application to increase security, since requiring further authentication for any login ensures better protection. As password attacks are becoming more sophisticated however, it’s become more apparent even complex passwords can be cracked.
Why use an insecure form of communication for this extra security step? After all, SMS messages are based on telephone networks. In fact, hackers originally were a bunch of folks finding cool ways to get around phone networks. Intercepting SMS is actually considered “old hat” to many hackers.
As our founder Daniel Cid points out, it’s not just the phone networks, but the phone companies that are bad at security.
“Your voicemail is protected by only a 4-digit PIN. And on most carriers you can access your voicemail remotely.
Easy to phish. If you know some basic information about the person, you can get the PIN changed.
Easy to spoof. It is very easy to spoof an SMS message. There is no SSL or certificate to verify where it really came from.”
Steps have been taken over the years by Google to attempt to secure and verify the sender of those SMS’s. If you are interested in this for your business you can learn a bit more about it here: How Verified SMS works.
Spoofing and Phishing
Spoofing can be combined with phishing to gain access to an account. This process allows hackers to falsify a message to make it appear as if it’s coming from a legitimate source. The message alerts the victim that they need to reply with the security code. Simultaneously, the hacker triggers a login 2FA request. If the victim replies with the code, the hacker can use it to gain access.
Following best practices to prevent phishing isn’t enough to make SMS authentication secure. As Daniel mentions, a hacker with basic information about a victim can have enough to get their PIN changed.
The same method of social engineering can be used to swap SIM information for a phone number.
A hacker can simply pretend to be a victim and activate a new phone with the number. Before a victim notices this, the hacker will already have breached any 2FA. This is known as SIM swapping.
This process may seem a bit convoluted, but it’s surprisingly effective. For example, Cloudflare was breached using a similar method. Their phone provider, AT&T, was tricked into redirecting their voicemail and then access to their email was gained through a 2FA account recovery process. If it can happen to an industry leader in cybersecurity, it can happen to anyone.
Remote Desktop Protocol (RDP)
Hackers can also swap SIM information through a Remote Desktop Protocol (RDP). These attacks require initial social engineering to have the RDP program installed. As Joseph Cox reported to Vice in January 2019, hackers have no problem gaining remote access to phone company systems. One hacker even went as far as calling some employees and managers “brain dead.”
Social Engineering Calls
A more recently popular method that attackers use to get ahold of your 2FA SMS codes, is to social engineer your mobile service provider and pretend to be you. They may even use information about you they’ve obtained via other means to request a secondary SIM. They may claim they lost it or that it was stolen and then intercept the reception of the new SIM and use it. Usually, when this happens your own SIM immediately loses service because your number is now fully under the control of the attacker. At that point, they can request 2FA codes at will. This example is a low-tech method that is quite effective.
Better Alternatives to 2FA SMS
While it’s understandable one would avoid SMS-based 2FA due to these concerns, this doesn’t solve the problem of needing 2FA in the first place. In order to prevent brute force and other kinds of attacks targeting password-only authentication, some form of 2FA is necessary.
The good news is there are more secure alternatives to SMS-based 2FA. Implementing one of these options will help ensure your accounts are safer from bad actors.
Hardware Authentication
Hardware authentication relies on a dedicated physical device that grants account access. Along with the password, users will still have to input a random token code generated by the device. Logins will automatically fail without the generated code.
The physical nature of this method does have the potential for devices to be lost or stolen, yet it does address some of the security issues inherent with SMS-based 2FA.
Software Authentication
Software authentication is essentially the same principle as hardware authentication, but instead of requiring a physical device, token codes are generated with a mobile application. The most popular authentication app is Google Authenticator, but there are many other options out there. For example, RSA now offers their SecurID authentication as an app.
It may seem counterintuitive to recommend authentication based on a mobile device, but the software doesn’t rely on SMS or the phone network for authentication, which eliminates the inherent flaw in SMS-based 2FA. This kind of authentication is still open to phishing, so the usual precautions should be taken.
IP-based Authentication
This method checks the user’s IP address when logging in. You only allow logins from known IP addresses and ranges. IP-based authentication can be used in conjunction with other forms of authentication to add another layer of security.
Conclusion
In conclusion, phones and text messages were designed with convenience, not security in mind. If you’re the target of an attack, relying on SMS for authentication can actually cause a bigger problem than it solves. However, SMS still remains a very popular 2FA method despite these issues, primarily due to its familiarity with the average user.
If a more secure option for 2FA is available, utilize it. If SMS is the only 2FA option available, it’s understandable to choose it over no protection at all. However, be sure to educate yourself about the risks that come along with it.
Some tech savvy people still opt for SMS 2FA because it provides them with the easiest route to recover information. But in those cases, there is still a smart way to use SMS 2FA. You can maintain an entirely separate SIM card that’s exclusively used to receive 2FA codes. This makes it much harder for any attacker to discover the number and compromise the security.
While stronger 2FA methods are recommended, they’re not a replacement for a good password strategy. Think about it the same way you think about your home: A strong deadbolt on the front door is great, but it doesn’t matter if you leave the key under the mat.
For more cybersecurity content, sign up to receive posts about current security issues, vulnerabilities, and exploits.