These days WordPress infections are very common. In 2021, internetlivestats.com counted over 81 million websites hacked. If you’re one of the millions, you need to take action to fix and protect your site. Of course, a hacked site will put any site owner into panic mode. This article will provide insight on what to do if your website is hacked and how to move forward. WordPress sites can be hacked due to a variety of reasons, which we cover in Why are WordPress sites targeted by hackers?
First things first, confirm that your WordPress site has actually been hacked. You can do this by scanning the site using a tool like our SiteCheck scanner or our free WordPress plugin. This will also help confirm if your site is on any blocklists. Next, check for recently modified files (or any core files) and confirm the date of these changes with the user who changed them.
Once you’ve confirmed that your WordPress site is indeed infected, you need to remove all of the malicious content.
Cleaning infected files & database tables
In order to manually remove an infection from your site files login to your server via SFTP or SSH. If you’re unsure what these login credentials are, have your hosting provider assist further. Once logged in, make an initial backup of the site before any changes are made. During the clean up process the site will likely appear broken or offline, so some site owners will turn on “maintenance mode” either with a splash page plugin or theme in the meantime. Also, if any previous backups stored look clean, these could be useful to compare against the current site to identify the malicious code.
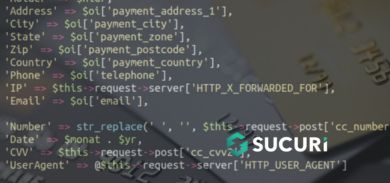
Once a backup and maintenance mode is in place, you can proceed with manually removing the malicious code and replacing any core files that were infected. Ensure that any hidden backdoors are removed. Hackers generally leave a way to get back into the site. The majority of the time, the malicious code uses some form of encoding, so it’s critical these are removed entirely to avoid reinfections. Some backdoors commonly found include the following PHP functions:
- base64
- str_rot13
- gzuncompress
- eval
- exec
- system
- assert
- stripslashes
- preg_replace (with /e/)
- Move_uploaded_file
Pro tip: Any other websites residing in the same hosting environment could also be cross contaminated. Make sure those are either cleaned or removed entirely if no longer being used.
Removing malware from a website database will require you to first login to your database admin panel. You should make a backup of the database before making any changes.
Next, find any spammy keywords or links within the tables and remove them. Using tools such as Search-Replace-DB or Adminer will also come handy, but make sure to remove them once you’re done.
Malicious PHP functions such as eval, base64_decode, gzinflate, preg_replace, str_replace, etc are commonly found within the database. Sometimes the payload is itself a chunk of base64 encoded content, or obfuscated using the fromCharCode( function. Once these are all removed, make sure your site is still operational.
Once both the site files and database are thoroughly cleaned, it’s important to remove any unfamiliar users in case these accounts were created by a hacker. A best practice is assigning admin privileges to only one user and setting other user roles to the least amount of privileges needed (I.E. The Principle of Least Privilege).
If all else fails and you’re still not confident with the malware removal process or do not have enough time to manually remove it yourself, having a Sucuri analyst clean it up for you is another option to consider.
Removing Malware Warnings
If your site is listed on a blocklist, you can manually request your website be removed from it once the infection is cleaned up. If you’re suspended from your web host, first reach out to them providing the details about how you have removed the malware. For each blocklist authority, fill out a review request form. Depending on where the site is blocklisted, the response time can vary anywhere from 24 to 72 hours. Once all requests have been submitted, it’s just a waiting game. Until then, it’s important to put in place some post-hack preventative measures so the site is not reinfected.
How to protect WordPress sites moving forward
Protecting WordPress sites is crucial in today’s modern web environment. As automated attacks continue to target vulnerable plugins, themes and versions, site owners must remain vigilant about keeping security risks low and updating anything that’s out-of-date. After your site has been successfully cleaned up, make sure all passwords are updated using strong characters. As previously mentioned, using the Principle of Least Privilege with user accounts is a simple and effective website security precaution..
Utilizing a Web Application Firewall reduces entry points for attackers as well. Since attackers exploit vulnerabilities with plugins and themes, this will patch up holes in your website software, even if you haven’t applied the latest security updates. A Web Application Firewall will also protect against Brute Force Attacks, mitigate Distributed Denial of Service (DDoS) attacks, and provide performance optimization.
In Conclusion
Manual cleanups can be a grueling process, especially for a non tech-savvy person. If you’re pulling your hair out because your site has been hacked, and you don’t know what to do, don’t hesitate to turn to a professional. These infections can take time to fully be rectified, but once they are, you’ll feel a weight lifted. More importantly, you’ll learn a lesson about the importance of website security. Do yourself a favor and try to get ahead of a website infection by employing some hardening measures to your website.
If you’re a site owner that experienced or currently is experiencing a WordPress hack, I hope this information has helped you consider what to look for in your malware removal process.