OK – your WordPress site is hacked. Now what? Questions we frequently get from new users are, “Why was my WordPress site hacked?” and “What should I do after a WordPress hack?”
Of course, these are reasonable questions to ask; it’s extremely frustrating to find out that your site has been compromised and you need to tackle a malware infection or increase security controls. Surely you’d want to understand why and how to quickly deal with your hacked WordPress site.
However — while all websites are susceptible to hacks, certain errors could be increasing the vulnerability of your website. In this post, we’ll delve into a few of the main reasons why WordPress gets hacked and how it happens. We’ll also cover some common red flags and signs of a hacked WordPress environment, and what to do if your WordPress was hacked. This will help you to recognize potential mistakes, effectively recover from a hack, and take measures to safeguard your site from future attackers.
Contents:
- Why does WordPress get hacked?
- Key reasons why WordPress gets hacked
- What are the signs of a hacked WordPress site?
- What is the best way to prevent a WordPress hack?
- Getting help with hacked WordPress sites
Why does WordPress get hacked?
WordPress powers over 43% of all websites on the web, translating into hundreds of millions of websites worldwide. This popularity makes it a prime target for hackers, particularly websites that are not well-secured or contain known software vulnerabilities.
That being said, we need to make an important distinction: WordPress is not the only CMS platform targeted by hackers. In fact, to varying degrees all websites on the internet are prone to hacking attempts.
Understanding the hacker’s motive
Hackers have a wide range of motivations for their illicit activities. Some are merely novices learning to exploit less secure sites. Others might have more nefarious intentions, such as distributing malware, launching attacks on other websites, sending spam, or using compromised domains for black hat SEO.
Some attackers focus on stealing sensitive data such as personal information, credit card numbers, or login credentials. These can be sold on the dark web or used to commit fraud and identity theft. Others may simply be looking to disrupt services or make a political statement.
However, it’s important to note that not all hackers are motivated by illicit gains or malicious intent. Some hackers, often referred to as “white hat” hackers, exploit vulnerabilities in order to expose them and help improve the system’s security.
Regardless of the motive, the outcome of a hack is almost always detrimental to the website owner. It can lead to lost data, reputation issues, and even legal consequences if sensitive customer information is compromised.
Key reasons why WordPress gets hacked
Now that we understand the motivations behind a hack, let’s take a look at some of the key reasons why WordPress gets hacked.
- Unpatched WordPress core, plugins & themes
- Weak passwords and usernames
- Unprotected WordPress admin panels
- Improper isolation in shared server environments
- Unrestricted access to wp-config
Let’s go over these reasons in closer detail.
1. Unpatched WordPress core, plugins & themes
The core WordPress CMS is secure, but only if you maintain it to the latest version and properly configure it.
Since the code base is publicly accessible, anyone can review and analyze the source code. And whenever a bug or security issue is reported by the open-source community, developers update WordPress core to patch the issue.
However, these updates don’t apply to your extensible components like plugins and themes. You’ll need to patch each piece of software individually (and on a regular basis) to mitigate risk.
Not updating your WordPress software and components can leave your site exposed to known issues. To protect your environment and mitigate risk, it’s crucial to update your WordPress core (along with all your plugins and themes) as soon as a new patch is available.
Hackers often use automated tools to quickly find and attack websites with known vulnerabilities — so it’s important to act quickly when it comes to software updates.
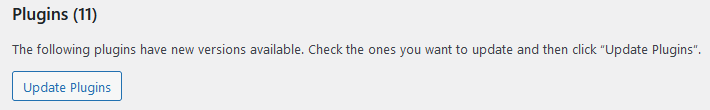
If you don’t have automatic plugin and theme updates enabled, you can manually update plugins in your WordPress dashboard from the following location: Dashboard > Updates > Plugins
2. Weak passwords and usernames
Passwords are your WordPress site’s first line of defense. Automated tools can easily crack a weak password, giving an attacker unauthorized access to your posts, pages, files and database.
That’s why it’s so essential to use strong, unique passwords for all your accounts, including:
- WordPress admin account
- Web hosting control panel account
- FTP accounts
- MySQL databases
- Email accounts used for WordPress admin and hosting
We recommend creating unique passwords with a combination of letters, numbers, and special characters — at least 12 characters long. Password generators can make it easy to quickly create new unique credentials for your accounts.
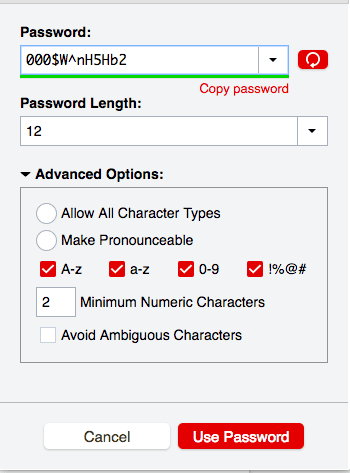
Furthermore, steer clear of default admin usernames; it only takes a second to change admin to something unique and makes it that much harder to guess the credentials to your account.
3. Unprotected WordPress admin panels
The WordPress admin area and default login pages /wp-login.php and /wp-admin are one of the most frequently targeted areas of WordPress. Since it’s where you can control all aspects of your website, it’s also consequently where hackers can do the most damage.
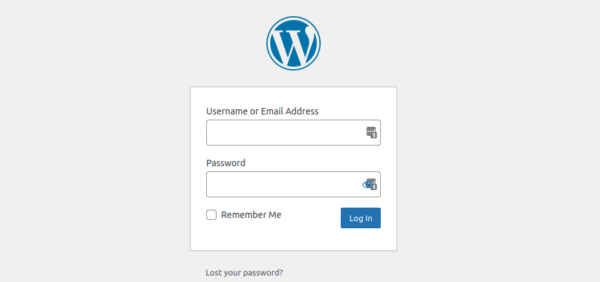
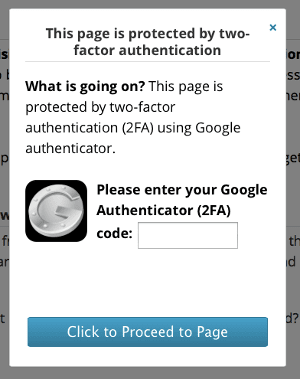
By default, WordPress does not limit the number of failed login attempts (nor does it contain any native 2FA system), rendering it particularly vulnerable to brute force attacks.
Protect your WordPress site by adding layers of authentication and restricting unauthorized access to sensitive pages like wp-login and wp-admin.
The Sucuri firewall makes it easy to implement protected pages across your website and provides options for password protection, 2FA, captcha and IP address restrictions.
Reach out to our experienced 24/7 team to get help with setup if you need a hand!
4. Improper isolation in shared server environments
We deal with plenty of new clients who have “soup kitchen servers”. These are web servers with a huge number of websites, installations, and configurations all crammed into the same environment.
The issue with these environments is that a single compromised website can infect all others on the shared account or server, leading to cross-site contamination.
You can help prevent this issue by using separate cPanel instances for each website and configuring a secure VPS environment with PHP-FPM to host multiple sites.
5. Unrestricted access to wp-config
The wp-config.php file is an integral part of your WordPress website. This core file is responsible for running your site and houses important configurations such as database location details, login credentials, and advanced options for database elements, security keys, and developers.
If you’re new to WordPress, it’s crucial to start by restricting access to this file. One way to do this is by moving your wp-config file one directory level above the root folder, making it inaccessible to the internet. If the file is not found in the root folder, WordPress will automatically search for it in the directory above the root.
For those whose servers use .htaccess: you can further restrict access by adding a rule to deny anyone searching for it.
The directives for Apache 2.4 are as follows:
<FilesMatch "wp-config\.php">
Require all denied
</FilesMatch">Salts and keys
The wp-config file includes a section dedicated to salts and keys that boost the security of cookies and passwords in transit between your browser and web server.
You can set up your salts and keys by adding or editing these lines after the other define statements:
define(‘AUTH_KEY’, ‘include salt here’);
define(‘SECURE_AUTH_KEY’, ‘include salt here’);
define(‘LOGGED_IN_KEY’, ‘include salt here’);
define(‘NONCE_KEY’, ‘include salt here’);Set file permissions
Since the wp-config.php file contains highly sensitive information, it’s essential to configure file permissions to prevent unauthorized access or modification.
A permission level of 600 should suffice, but you can start with 400 and escalate as necessary. Always begin with the least permissive configuration and only increase permissions when required. Never set permissions to 777 unless you’re an expert or have an excellent reason.
Disable plugin and theme installers
Wp-config can also define vital information about WordPress plugins and themes. For instance, you can disable the theme and plugin file editors or installers by adding the following lines to your wp-config file:
define( 'DISALLOW_FILE_EDIT', true ); //disables file editor define( 'DISALLOW_FILE_MODS', true ); //disables both file editor and installer
Bear in mind that this will also block plugin updates. You can still update plugins and themes using WP-CLI or manually via sFTP.
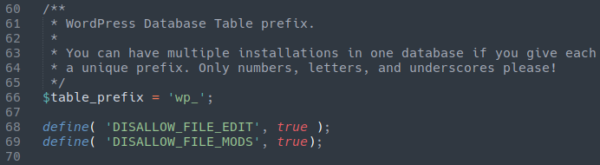
Attackers often exploit theme and plugin installers to install backdoors. So, this simple step can make it more challenging for them to create fake plugins for unauthorized access.
What are the signs of a hacked WordPress site?
Think your WordPress site is behaving strangely but not too sure if it was hacked? Let’s take a look at some of the most common red flags and warning signs of a hacked WordPress website:
- Can’t log in to the WordPress dashboard.
- There’s new content or static pages on your site.
- Browser warnings appear when you navigate to your site.
- Visitors are unexpectedly redirected to other websites.
- Google search results show warnings for your WordPress site.
- The hosting provider for your WordPress site is warning about unusual activity.
- A security plugin is warning you about unexpected changes, logins, new users, or malware detections.
Can’t log in to the WordPress dashboard.
Can’t log in to your WordPress dashboard? Well, there’s no point in assuming you’ve been hacked just yet. Before you start panicking, try a simple password reset to rule out the fact that you might have just forgotten your password.
If a password reset doesn’t work or you don’t receive the reset email, then this is a red flag that something unusual may have occurred and warrants further investigation.
Our security analysts often find that attackers delete the WordPress admin user or change user passwords to prevent access once they hack the site. So, if you are unable to reset your password and you believe that your account was deleted or tampered with, this is a definite sign of a hacked WordPress site.
There’s new content or static pages on your site.
In some cases hackers will compromise a website to deface it or inject it with SEO spam content. But, it makes sense to check with other website editors and admins before you outright assume it’s a hack.
If you find new, unexpected content or pages on your website and you’re certain that you (or another legitimate website user) didn’t put it there, your site was likely compromised and you’ll need to do a bit more digging.
New content doesn’t just mean full paragraphs of text, either — sometimes attackers will try to hide spam text in hidden divs or inject links to spammy websites into your existing website pages. In other cases, they will generate entirely brand new pages on your website.
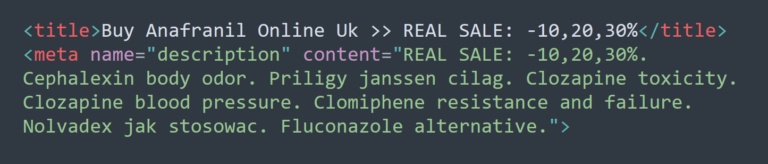
So, if you just encountered some strange spammy keywords, content, links or other signs of website tampering, you’ll want to scan and check your site for malware.
Browser warnings appear when you navigate to your site.
To protect users, modern web browsers use automated processes to detect website malware. Data from a wide range of sources is collected and aggregated to help find websites that might be harmful to website visitors.
So if a browser like Chrome, Firefox, or Edge detects malware on your website, they’ll issue a warning to help prevent visitors from navigating to the website until the problem is fixed. This is most certainly a sign of a hack and should be investigated further.
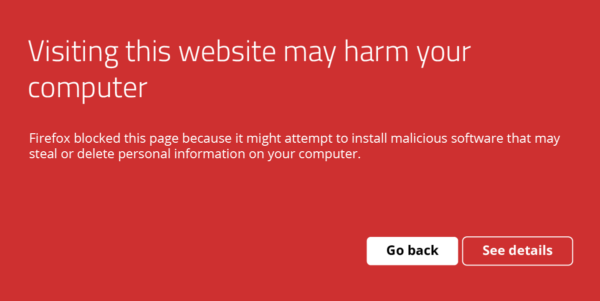
In most cases, the browser warning will likely contain information on how to diagnose or resolve the problem. But you will certainly want to take steps to find and fix the hack on your WordPress site.
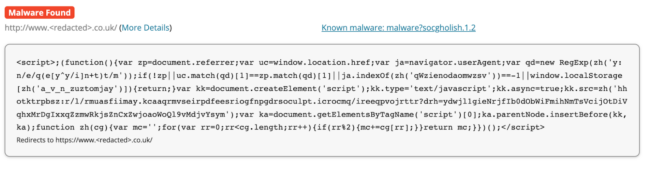
Visitors are unexpectedly redirected to other websites.
Hackers are known to add redirect scripts to compromised websites in order to monetize traffic to third-party spam sites, trick victims into loading and installing fake browser updates, or even distribute malware.
Scripts that execute malicious redirects can lurk anywhere on a website. We’ve seen them in databases where they differentiate between real traffic and search engine bots, and then sent legitimate traffic to a malware download.
The malicious redirect was triggered from a search engine results page, not within the infected website. One click, and wham — malware starts downloading.
So, if your website is redirecting you or website visitors to strange and unexpected websites, this is definitely a sign of a hack. You’ll want to scan for injected malware as soon as possible.
Google search results show warnings for your WordPress site.
Just like web browsers, search engines like Google also have a vested interest in protecting users. So if Google’s algorithms and crawlers detect that there’s malicious code on your WordPress site, they will issue a “This site may be hacked” warning like this:
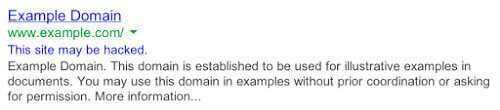
Google is pretty accurate when it comes to detecting website malware infections. If you see this warning for your site in search results, it’s a credible sign that your WordPress site was hacked.
The hosting provider for your WordPress site is warning about unusual activity.
Your hosting provider will reach out if they detect any wide range of problems, including but not limited to:
- Malware infection
- Server resource overuse
- Payment failures
- Terms of service violations
- Other important account activity
If your host has detected some unsual activity or a malware infection, you’ll want to take it very seriously and address it as soon as possible as it’s a definitely sign of an issue. If you don’t take measures to resolve the problem, you could risk an account suspension.
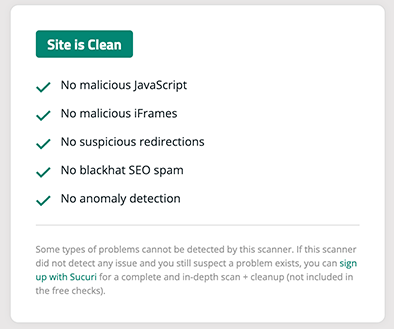
A security plugin is warning you about unexpected changes, logins, new users, or malware detections.
Security plugins like the Sucuri WordPress Plugin contain a wide range of useful security features that can help you detect malicious behavior on your WordPress site.
If the plugin finds website malware or detects unexpected changes to your files, you’ll be able to know pretty quickly to determine if your site is hacked or not.
What is the best way to prevent a WordPress hack?
The unfortunate reality is that no single security measure can provide a 100% guarantee against hackers. However, implementing a defense-in-depth strategy that includes hardening your WordPress website and leveraging a reliable website firewall can significantly improve your chances of preventing a hack.
The Sucuri firewall helps to ward off brute force attacks, blocking any unwarranted access to your wp-admin or wp-login page and preventing automated attacks. It also mitigates Distributed Denial of Service (DDoS) attacks, which try to overwhelm a server or application resources. Another excellent feature is its ability to virtually patch known vulnerabilities in the event that you’re unable to update your website software in a timely manner.
There’s no installation necessary — just a simple switch of your DNS A Record to enable it. For further details, check out this video on how to prevent a hack with a website firewall.
Getting help with hacked WordPress sites
Pretty certain that your WordPress site was hacked? We’ve got your back!
If you’re the do-it-yourself type, we’ve got a comprehensive guide that details all the steps you can take to respond to a hacked site and clean up WordPress malware.
Some key steps to respond to a hacked WordPress site include:
- Scan your WordPress site for malware and signs of infection
- Check core WordPress file integrity
- Remove malware from your WordPress files and database
- Get rid of website backdoors to prevent reinfection
- Secure WordPress user accounts
- Patch and update your website software, plugins, and themes
- Harden your WordPress environment
You’ll find all these and more in the how to fix a hacked WordPress guide. Just follow along and reach out if you get stuck!
For those that need a hand or want some help as soon as possible, our experienced security analysts are available 24/7 around the clock to help you remove malware from WordPress and get your site protected from future hacks. Sign up for the plan that best suits your needs or chat with us to learn more!