Defacement is easily one the most obvious signs of a hacked website. In these attacks, bad actors gain unauthorized access to an environment and leave their mark through digital vandalism, altering its visual appearance or content in the process.
In many cases, website defacements display social or political messages that are completely unrelated to the site’s original content — with the ultimate goal of blackmailing or embarrassing the website owner, enacting revenge, or promoting alternative viewpoints.
Unlike many other attacks, defacers seek attention and publicity; they often disclose contact information or a name so they can be associated with the defacement.
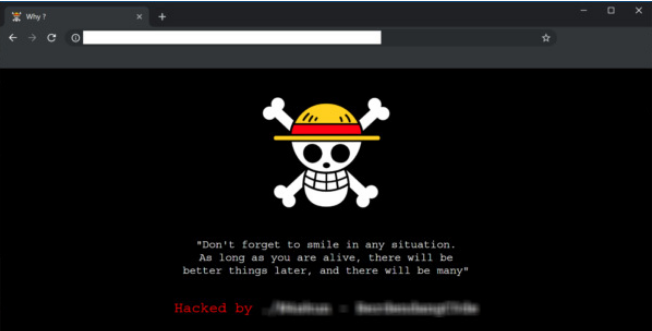
So, if you’re a website owner and you access your homepage one day only to find that all of hard work and content replaced with something like this, you may have fallen victim to website defacement:
How do hackers deface websites?
Hackers deface websites by gaining unauthorized access to an environment. The methods can vary, but popular methods of entry include exploiting vulnerabilities in third-party plugins, brute forcing admin pages, or leveraging stolen login credentials.
Once a foothold has been established, the hacker can gain edit access to the website and make whatever changes they see fit.
Just as the methods of defacement will vary, the depth of the attack can also differ. It may be as simple as the website’s index.php file being modified. This kind of hack can be fixed by simply replacing the hacked index.php file with a clean copy.
But hackers may also go a bit deeper in their defacement and alter important core files as well. In this case, you may be looking at a more difficult malware cleanup scenario.
Why do hackers deface websites?
While many hacks are designed to generate some form of value for the attacker, website defacements are typically a different kind of attack. Mostly, the defacer is just trying to share a message. In some cases, they’re just looking to flaunt their skills and leave a “calling card” to gain a bit of street cred, while others might deface a website for the sheer fun or challenge. But defacements can also be motivated by political, religious or ideological goals; for example, protesting a specific movement in an act of civil disobedience.
Regardless of the intent, finding your site with a “hacked by” message is something you’ll want to get resolved as soon as possible.
Examples of website defacements
Website defacements tend to look like… well, what you might expect when you think of a stereotypical hack. Scary imagery like a skull and crossbones, biohazard symbols, or other imagery designed to draw attention to the hack.
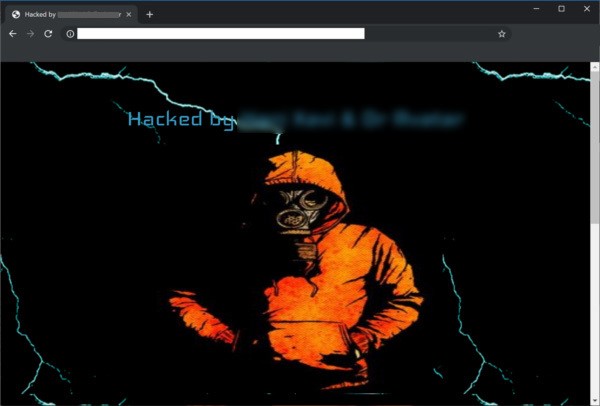
Hackers will also take credit for the attack by leaving their mark or “signatures.” Most common hacker signatures are usually pretty generic with wording such as “hacked by”, “pwnd by,” “defaced by,” “Been Hacked By,” “YOU GOT HACKED,” and other such jargon.
Some hackers will even just go with plain text defacements:
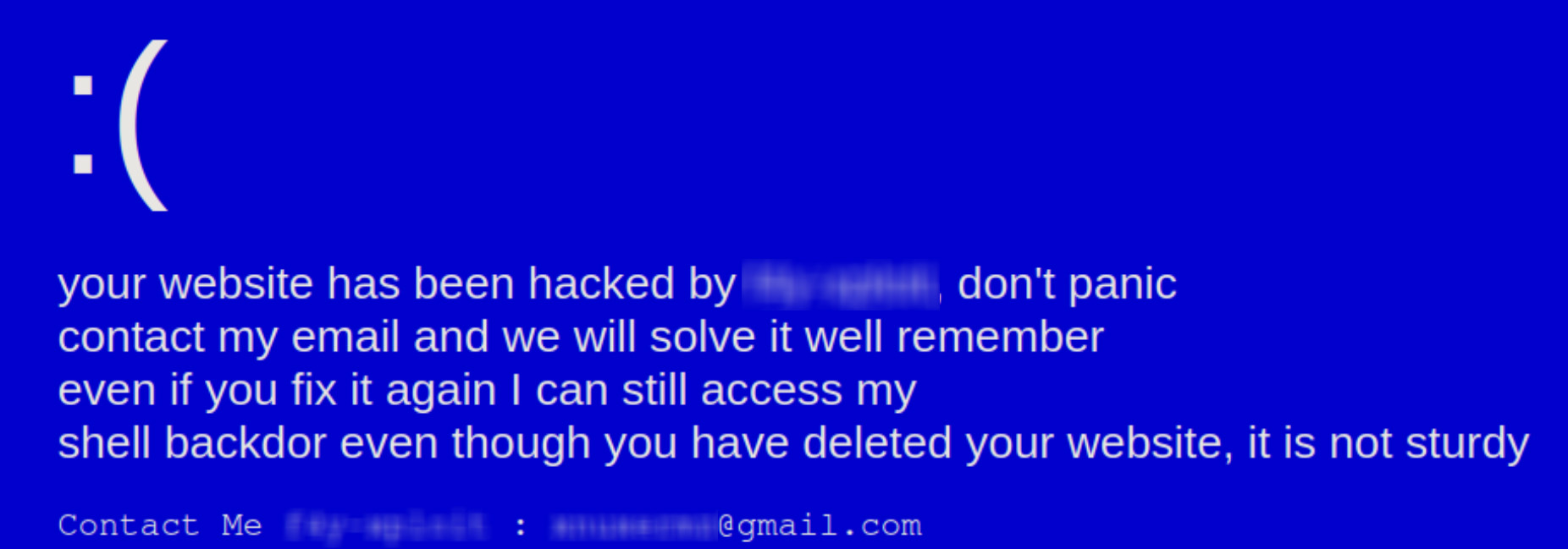
Because the nature of these attacks is publicity, we’ve decided not to provide any of the most recent groups’ names.
What are the consequences of a website defacement?
The consequences of a defaced website are much the same as any other hack — it’s just more obvious that your website’s security has been breached and the environment has been tampered right off the bat.
Trust will be immediately diminished when users visit a page that is clearly displaying signs of being hacked, which can have an immediate impact on your reputation, website sales, churn, and bounce rates.
And the longer you allow your website to display the defacement, the worse things will get. An outward-facing website compromise containing inappropriate content can result in a blacklist from Google and other search engines. This means your site may stop ranking in search results and organic traffic may plummet. Getting off of a blacklist can be difficult, which is why you’ll want to clean up any website defacements as soon as possible.
How to recover from a defaced website
If you’ve been keeping regular backups, recovering a defaced website is easy. Simply restore your site back to its original form from the last uncompromised backup. But if you do not have a backup, recovery may require a bit more work.
In a case where a backup restoration is not possible, you will want to:
- Log into your server via SFTP or SSH.
- Make a backup of your site in its current state.
- Identify any recently changed files on the server and confirm any changes with users who might have made them.
- Scan for backdoors and remove any malicious code from the environment.
- Restore suspicious CMS system files with fresh copies from a stock installation.
- For any custom or premium files, open the file with a text editor to remove any suspicious code.
- Test to verify the site is still operational after changes.
You can follow our hacked website guide for complete, step-by-step instructions. Once the site is back to its original state, you’ll want to take a few more precautions to ensure that hackers can’t regain access to your website.
- Change all your passwords – If a user account was compromised during the hack, make sure the attackers do not have access. Changing credentials helps – be sure to use strong, unique passwords for all of your accounts.
- Update all of your themes and plugins – Known vulnerabilities in third-party plugins and themes are a likely source of compromise. Keeping them up to date with the latest patches ensures you are running the most secure version for your website.
- Practice the principle of least privilege – Check your user settings and only grant users the bare minimum of access they need to do their work. This will limit the chances of hackers being able to gain access to deface your website.
- Use a web application firewall – Website firewalls can help protect admin pages, block bad bots, and virtually patch known vulnerabilities on your website to defend against hackers.
But if you are feeling at all uncomfortable about cleaning up a defaced website on your own, don’t worry. Help is available. Sucuri offers website security solutions that can clean your site and protect you from any future website defacements.