As many know, we have been offering our free website malware scanner – Sucuri SiteCheck, since early in 2011. In our commitment to continue to give back to the community, we want to share some statistics. We’d like to share the distribution of infections based on the number of sites that are being scanned using Sucuri SiteCheck.
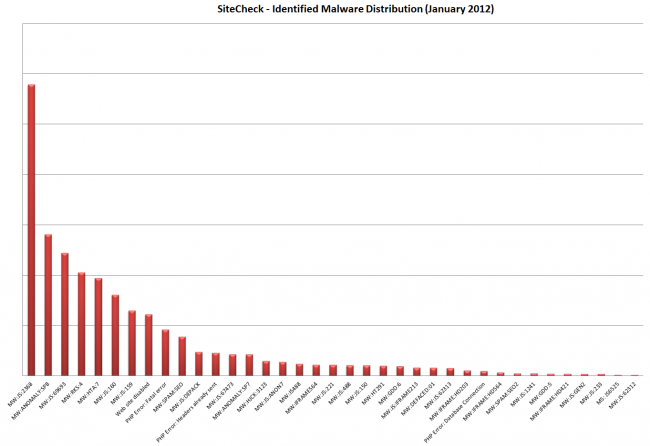
In January, we scanned a couple 100 thousand sites. From those we were able to better understand the distribution of malware.
From this, we can see that the top three infections are coming from the following
Malware Entry: MW:JS:2368 – 21%
Description: A malicious and encoded javascript file was found inside the site content and is being used to distribute malware (from newportalse.com and other domains). Any user visiting the infected site could be compromised (desktop antivirus will flag it as JS:Cruzer-B, JS/Obfuscated, JS/Cruzer.C.gen, JS/TrojanDownloader.Agent.NKW and others, depending on the intermediary domains and AV product).
Malware Entry: ANOMALY:SP8 – 18%
Description: A suspicious block of javascript or iframe code was identified. It loads a (possibly malicious) code from external web sites that we could not properly identify. Those types of code are often used to distribute malware from external web sites while not being visible to the user.
Malware Entry: MW:JS:69693 – 9%
Description: A malicious javascript code was identified. It has been used on many compromised WordPress sites to redirects visitors to multiple exploit kits (Blackhole, etc).
Note that every javascript file gets compromised by this malware (in addition to backdoors left by the attackers).
If you have questions, let us know in the comments below. Or feel free to send us an email – info@sucuri.net










1 comment
What was the percentage affected out of the scanned sites?
Comments are closed.