Do you run your website on WordPress? Have you checked the integrity of your core install lately for SPAM like “Google Pharmacy” stores or other fake stores?
We have been tracking and analyzing a growing trend in SEO spam, or Search Engine Poisoning (SEP) attacks in which thousands of compromised WordPress websites are being used to hide fake stores and spam doorways. In every case, the attacker is leveraging one of the core install directories – wp-includes.
Abusing /wp-includes/ With Spam
By default, every WordPress installation comes with 3 main directories: /wp-content, /wp-admin and /wp-includes. Generally, /wp-includes is reserved for generic code and is the heart of WordPress where all major core files are stored. It’s a folder that doesn’t need to be remotely accessed and should not contain any externally accessible or executable HTML or PHP files.
Unfortunately, that is not what we’re seeing. Thousands of WordPress sites seem to have been hacked, and in each case spam has been injected into their core directory wp-includes. We have found it’s not specific to pharmaceuticals either, it includes things like “Payday spam” and “cheap bags”, “cheap watches” and many other forms of spam content.
This type of spam injection has 3 main characteristics:
- The spam pages are hidden inside a random directory inside wp-includes (eg: /wp-includes/finance/paydayloan or /wp-includes/werty/).
- The spam is conditional and often based on the referrer.
- We’ve noticed that, in almost every instance, the websites are running outdated WordPress installs or cPanel – this is obviously conjecture.
Here is a small list of 100 hacked WordPress websites with spam injected in their /wp-includes directories. All of them are publicly accessible by doing some Google searches:
http://www.immunomix.com/ITIpress/wp-includes/finance/paydayloan/payday-loans-instant.html
http://microwaveamps.co.uk/wp-includes/js/thickbox/lib/loans/payday-loans-in-london-uk.html
http://www.scifidimensions.com/wp-includes/finance/cashadvance/cash-advance-loan-lenders.html
http://www.beereading.com/wp-includes/finance/cashadvance/cash-advance-loans.html
http://vastema.com/wp-includes/cheap-hermes-lindy-bags-on-sale.html
http://www.antibabypillerezeptfrei.net/wp-includes/js/crop/advancement/helpers/blrmalaysiabank.html
http://todayscliche.com/wp-includes/palco.html
http://www.ethosindia.com/wp-includes/mambo.php?p=55
http://www.turnerforte.com/blog/wp-includes/finance/cashadvance/cash-advance-credit.html
http://www.ednapletonblog.com/wp-includes/werty/replica-36596.html
http://www.pettycustomhomes.com/wp-includes/cheap-kids-nba-jerseys-3167596.html
http://www.pondproshop.com/reference/wp-includes/catalog/services/vybe/vybe-band-reviews.html
http://firefly-path.net/wp-includes/pomo/qwe/4/Buy-Balenciaga-High-Quality-Replica-Clutches.php
http://wolfgangcapellari.com/wp-includes/pomo/rolex-imitation.html
http://byphandyman.com.au/wp-includes/people/replica-bvlgari-fake-watches.html
http://rumbaytimbal.com/wp-includes/reviews/
http://www.preservinggoodstock.com/wp-includes/louis-vuitton-bags-5641302.html
http://www.domagojkovacic.com/wp-includes/wholesale-jerseys-from-china-7479567.html
http://maciejkot.pl/wp-includes/detect.html
http://allinseopack.com/wp-includes/js/plupload/oscar-leeser-bio-i12.com
http://www.marinavendrell.com/wp-includes/store/diet/solpria/solpria-cleanse-reviews.html
http://missouriche.org/wp-includes/louisvuitton19.html
http://vastema.com/wp-includes/replica-hermes-birkin-25-cm.html
http://www.conemund.org/eng/wp-includes/replica.php
http://cri-technologies.com/wp-includes/pomo/mkheaf.php?psdjvwei=uplink%20dwd
http://www.giser.net/wp-includes/headt.php
http://chicksdigme.com/wp-includes-old/vanilla-sky-lyrics-owl-city-i0.com
http://jewelrypictures.org/wp-includes/js/imgareaselect/ghd-machine-i5.com
http://www.jobshopsf.com/wp/wp-includes/finance/autoloan/car-loan.html
http://www.ebrice.com/wp-includes/shop/health/tagaway/buy-tag-away-discount-price.html
http://amr-nadim.net/wp-includes/fake-hermes-clic-clac-bracelet–5621.html
http://jesicaglot.com.ar/wp-includes/news/replica-watches_14626.html
http://funaki.ens-serve.net/wp-includes/images/news/black-evening-dresses.html
http://linkarbeid.no/wp-includes/replica-celine-tas.html
http://www.iwillstandupforyou.com/wp-includes/nfljerseys-19244-6847676.html
http://www.viparenda.com.ua/wp-includes/pomo/index/shorewatches.htm
http://www.lelieuunique.com/site/wp-includes/wp-about.php?p=124-chaussure-christian-louboutin-pas-cher.html
http://redtouch.com.mt/wp-includes/news/oris-aquis-depth-gauge-replica-watch-hands-on.html
http://www.stridesforstars.com/wp-includes/rewrite/list.html
http://perfectgroup.se/wp-includes/replica/rolex
http://www.cowalrugby.co.uk/wp-includes.php
http://janmccraylaw.com/wp-includes/watches/replica-32802.html
http://bekarty.pl/wp-includes/be/cartier-swiss-replica.html
http://conceitorio.com.br/home/wp-includes/indo/rolex-airking.html
http://www.liftstudios.ca/wp-includes/images/arrows/lib/chanel/wallets/Chanel-Wallet-On-a-Chain-Replica.php
http://mag.amazing-kids.org/wp-includes/js/crop/lib/vuitton/LV-Bags/Louis-Vuitton-Overnight-Bags-Replica.php
http://atelier.aencre.org/wp-includes/js/thickbox/lib/louboutin/model/christian-louboutin-crystal-daffodil-pumps-replica.php
http://feo.nusta.com.ua/wp-includes/images/news/buswatches.htm
http://cafetaxa.dk/wp-includes/replica-watches-uk/
http://www.socialned.nl/wp-includes/php/tag/michael-kors-outlet-washington
http://podcasttennis.free.fr/wordpress/wp-includes/js/tinymce/themes/advanced/ejezuli/inig/
http://www.baypointmarina.com/wp-includes/brand/ralph-lauren-sleepwear.html
http://nsldigest.org/wp-includes/css/wp-pointer/Buy-Good-Replica-Louis-Vuitton-Shoes_25510.html
http://supportambitiongroup.com/wp-includes/css/download-free-porn-no-sign-up.php
http://icmcc.org/wp-includes/js/jcrop/gearshifter.php?dqq=506
http://w3f.pl/wp-includes/pomo/silagra-50-price.html
http://www.fedusa.org.za/wp-includes/js/tinymce/wp-mce-help.php
http://www.styleslicker.com/wp-includes/js/buytadalafil/index.php?page=4
http://nclarkplaning.co.uk/blog/wp-includes/Cardiovascular/ventolin-mdi-buy.html
http://www.cadillacpizzapub.com/livemusic/wp-includes/finance/creditscore/annual-credit-score.html
http://www.nagaloka.org/wp-includes/filesd/1137a750e374cebd95e7bfb4c05c60a0
http://www.immunomix.com/ITIpress/wp-includes/finance/creditreport/credit-report-and-score.html
http://www.elpaisdealtamira.es/wp-includes/js/crop/lib/vuitton/LV-Replica/Louis-Vuitton-Replica-AAA.php
http://yogagals.com/wp-includes/bottega-veneta.html
http://www.baypointmarina.com/wp-includes/brand/ralph-lauren-bicester-village.html
http://nrca-railroad.com/wp-includes/js/crop/_notes/vuitton/LV-Outlets/Louis-Vuitton-Outlet-Store-in-Kansas-City-Missouri-MO.php
http://www.madeleineking.co.uk/wp-includes/the-wine-house-lichfield-i10.com
http://www.mecalfab.com/mecalfab1/wp-includes/discountstore/kitchen/ninjamegablender/mega-ninja-blender.html
http://oisa.org/trl/wp-includes/onlineshop/naturalproducts/powerprecision/buy-power-precision-lean-muscle-formula.html
http://www.elpaisdealtamira.es/wp-includes/js/crop/lib/vuitton/LV-Replica/Louis-Vuitton-Replica-AAA.php
http://adamriemer.me/wp-includes/user/index.php?p=netflix-rentals-netflix-dvd-movie
http://adcaustintech.com/javaegl/wp-includes/user/index.php?p=netflix-shares
http://todomejora.org/wp-includes/js/crop/lib/loans/payday-loans-without-checking-account-requirements.html
http://www.thekookmovie.com/wp-includes/php
http://www.moorefinefoods.com/wp-includes/heads7.html
http://www.businsure.com.au/wp-includes/jordanretroretails.com.html
http://www.airjordanpaschererfr.com/
http://stoleti.cz/wp-includes/images/index.php
http://www.chriswind.net/wp-includes/nets1121.html
http://icmcc.org/wp-includes/js/jcrop/gearshifter.php?dqq=196
http://www.demalagana.es/wp-includes/jordan11spacejambox.com.html
http://www.iarld.com/wp-includes/sageron.html
http://www.maintenantlagauche.com/wp-includes/class-wp-login.php
http://www.thesinbin.ca/wp-includes/images/jordansbred-us.com.html
http://www.plantingdandelions.com/wp-includes/x-jordan.html
http://www.martaortells.com/wordpress/wp-includes/images/jordansinfrared.com.html
http://missouriche.org/wp-includes/nikefree11.html
http://www.accqtrak.com/WordPress/wp-includes/Text/Diff/Renderer/Year57.php
http://urbancampout.com/wp-includes/glass.php
http://kortshoes.nl/wp-includes/The/fake-replica-watches.html
http://wolfgangcapellari.com/wp-includes/pomo/rolex-imitation.html
http://vastema.com/wp-includes/buy-hermes-lindy-handbags-outlet.html
http://maciejkot.pl/wp-includes/detect.html
http://nrca-railroad.com/wp-includes/js/crop/_notes/vuitton/LV-Buy/Buy-Louis-Vuitton-in-Warsaw-Poland.php
http://www.elpaisdealtamira.es/wp-includes/js/crop/lib/vuitton/LV-Cheap/Cheap-Louis-Vuitton-Luggage-Knock-Off.php
http://dibach.com/wp-includes/Text/Lifestyle/dating-lord-elgin-watches.php
http://www.iwillstandupforyou.com/wp-includes/real-gucci-belt-for-men-cheap-8163353.html
http://www.missouriche.org/wp-includes/index.html
http://www.lonestarlandscaping.biz/wp-includes/store/diet/greencoffee/where-can-i-buy-green-coffee-bean.html
http://www.andersonmontana.com/test/wp-includes/Text/Diff/Renderer/Filter17.php
http://www.cerbone.com/wp-includes/store/exercise/contourabs/contour-abs-reviews.html
http://www.smkgear.com/_wp/wp-includes/discountstore/home/solaramerica/solar-america-home-power-station.html
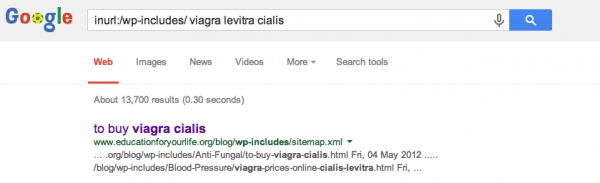
This is a very small sample. A quick search on Google using inurl:/wp-includes viagra levitra cialis reveals more than 13,000 pages. As you rotate out the spam keywords that number increases dramatically. You quickly start painting a pretty dire picture as you run more scans:
If you find yourself with similar symptoms, we recommend replacing your core install or seeking professional help.
If you prefer a Do it Yourself (DIY) method, then be sure to manually replace the core installs. Don’t just select “update” in your administrator panel because doing so won’t remove the file and while it may address the issue on the surface, it won’t be getting to the bottom of the issue.
Conditional Redirects
The term conditional should not be new to most of our readers, but if you’re new we recommend diving into our older posts to better understand how it works. A good place to start is our most recent post on redirects that were occurring only on mobile devices and targeting porn websites.
If you click on any of these URLs, you will see doorways for different types of spam. Some are just like the Google Pharmacy screenshot and some with really complex fake stores. However, if you are coming from a Google search, referrer = google.com, they will redirect you to the final spam destination.
And what is the final spam destination? These are the ones we have been able to isolate to date:
http://www.greboxs.com/ http://www.mkbagsesale.com/ http://www.shoebuy.com http://www.top-online-pills.com/
We don’t know if they are really malicious or being used by affiliate spammers, but they appear to be the final destination for all these spam pages.
How Are These WordPress Sites Getting Hacked?
While we don’t have definitive proof, as we do not have control of these environments, each instance we have analyzed always shows one common denominator – out of date software. We cannot stress the importance of patching your software via upgrades and if you can’t, be sure to leverage tools that allow you to operate safely on the web with your out of date software. The last thing any website owner wants is to find out later that their brand and system resources have been used for nefarious acts.









6 comments
I normally use the following .htaccess code to prevent wp-includes access, although obviously if the hacker has access to FTP thats not likely to help is it ? Could you tell me if this helps or whether ive been using it for no apparent reason lol
# Block the include-only files.
RewriteEngine On
RewriteBase /
RewriteRule ^wp-admin/includes/ – [F,L]
RewriteRule !^wp-includes/ – [S=3]
RewriteRule ^wp-includes/[^/]+.php$ – [F,L]
RewriteRule ^wp-includes/js/tinymce/langs/.+.php – [F,L]
RewriteRule ^wp-includes/theme-compat/ – [F,L]
# END Block the include-only files.
IndexIgnore *
For preventing access to parts of WordPress that should never be called directly (oooh, those evil hackers!) I use this in .htaccess (in the WordPress root folder) :
SetEnvIf Request_URI (?i)^/(wp-includes|wp-content|uploads|wp-admin/includes)/(.*).php$ badRequestString=$0–$1
SetEnvIf Request_URI (?i)^/wp-includes/ms-files.php$ !badRequestString
Deny from env=badRequestString
Using environment variables allows writing exceptions to rules. In this case, allow ms-files.php to be called.
(I don’t use the test for mod_rewrite. If your host doesn’t have mod_rewrite, Change Hosts! SiteGround, WPEngine, others that have strong emphasis on security.)
Hi. I get the same problem. Sorry i know english badly.
i understand, that solution need to find in file .htacess rules right?
i tried change file rules in WP themes from 755 to 444, this help (different spam links don’t appear in site’s footer).
But i don’t know how to defence wp-includes directory. I’ll be please that you show me solution.
Thank you!
Replica Handbags Incredible Sales For Black Friday
Hurry Up, Offer Available Only This Friday!
And counting … with the viagra google dork: “About 36,400 results (0.58 seconds) ” … ehm … sad but lol
Google index checker analyses on how easily and quickly google is able to crawl or index on a website. This tool is also useful in checking the google index stats of multiple websites at a time. It can access about ten URL’s at once
Comments are closed.