We are proud to be releasing our latest Hacked Website Trend Report for 2018.
This report is based on data collected and analyzed by the GoDaddy Security / Sucuri team, which includes the Incident Response Team (IRT) and the Malware Research Team (MRT).
The data presented is based on the analysis of 33,592 cleanup requests and summarizes the latest trends by bad actors. We’ve built this analysis from prior reports to identify the latest tactics, techniques, and procedures (TTPs) detected by our Remediation Group.
We’ve summarized a few key takeaways from our Hacked Website Trend Report:
- WordPress continues to be the leading website CMS for cleanup requests (90% of all websites cleaned by Sucuri in 2018).
- There was a notable decrease in the number of updated Joomla! installations at the point of infection.
- The blacklist telemetry showed a 6% reduction in sites being blacklisted. Blacklist authorities only detected 11% of the sites we cleaned as malicious in 2018, which speaks to the importance of proper scanning and detection controls.
- Our malware families analysis showed that SEO spam increased to 51.3% (up from 44% in 2017).
- There was a sharp increase in general malware distribution; from 47% in 2017, up to 56.4% in 2018.
- The number of detected mailer scripts decreased (from 19% to 12.5% in 2018).
CMS Analysis
Based on our data, the three most commonly infected CMS platforms were WordPress (90%), Magento (4.6%), and Joomla! (4.3%).
It’s important to note that this data does not imply these platforms are more or less secure than others.
Sucuri is well established in the WordPress community and offers a free security plugin, which likely influenced the results. This data is purely a reflection of the most common platforms seen in our environment and client base.
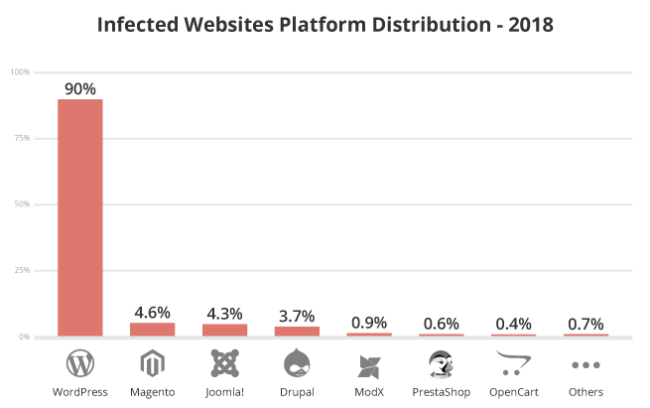
The majority of the compromises analyzed in this report were associated with improper deployment, vulnerabilities in extensible components, configuration issues, and lack of maintenance by webmasters — not with the core of the CMS application itself.
Outdated CMS Analysis
Our report also assesses the number of outdated platforms at the point of infection. A CMS was considered out of date if the environment was not patched with the most recent recommended security version at the time services were performed.
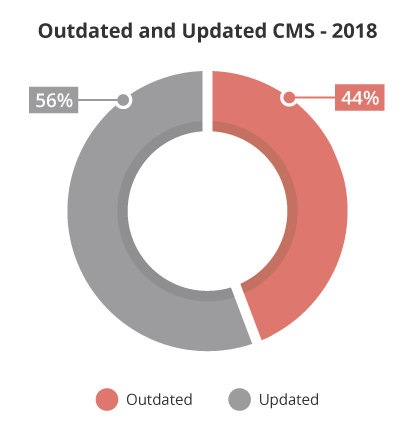
In 2018, WordPress experienced a decline in the number of outdated vulnerable versions at the point of infection — a total of 36.7% of WordPress clean up requests had an outdated version. CMS extensions, like plugins and themes, continue to be primary attack vectors and makes their role more significant for this particular CMS, however.
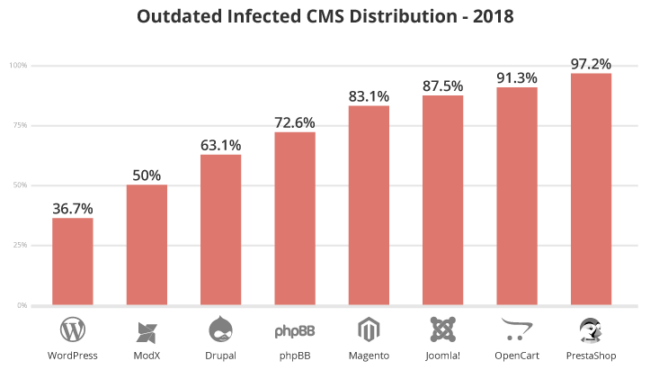
Based on our cleanup data, Drupal had a 2.2% decrease in out-of-date versions from the previous year. Joomla! rose sharply from 69.8% in 2017 to 87.50% in 2018. At the current moment, these CMS’ do not possess functionality for automatic updates. This likely contributes to a larger window for attackers to target known vulnerabilities.
Magento websites (83.1%) were mostly out of date and vulnerable at the point of infection, up 2.8% from 2017. We also noticed high percentages of other outdated open-source e-commerce platforms.
Attacks that target e-commerce websites are often lucrative for bad actors, as they may yield valuable customer data such as credit card details and sensitive user information.
We strongly encourage e-commerce website owners to update their software. It’s imperative that website owners update their software with the latest security enhancements and vulnerability patches. We’ve put together a helpful e-commerce security course if you are looking for more guidance.
Blacklist Analysis
Our 2018 blacklist analysis identified that approximately 11% of our website cleanup requests had been blacklisted by a prominent blacklist authority, a 6% decrease from 2017.
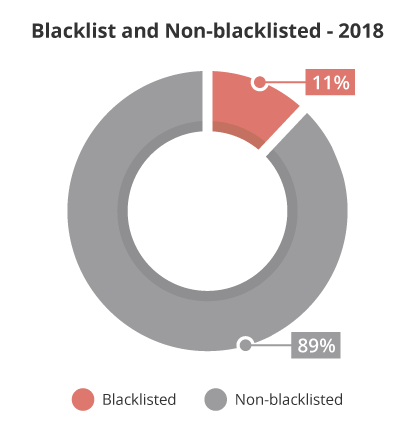
This data accentuates the importance of website monitoring to detect suspicious activity and other security issues. As a website owner, you can’t depend solely on blacklist authorities to identify if a website has been compromised.
Our latest Hacked Website Trend Report investigates which blacklist authorities were responsible for flagging infected websites and elaborates further on this topic.
Malware Families
A fascinating component of our 2018 research included various infection trend analysis and how they correlate to malware families and malicious payloads.
Malware families are a crucial element of our research here at Sucuri. They allow us to assess and understand a bad actor’s tactics, techniques, and procedures (TTP) and give us valuable insights to help us mitigate further attacks and protect our customers.
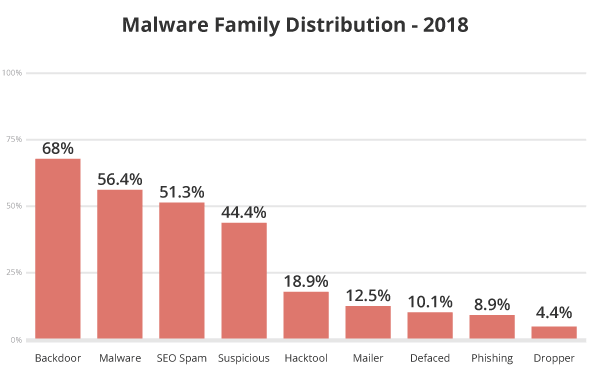
In our analysis of 2018 website infections, 68% of all compromises had at least one PHP-based backdoor hidden within the site. We also saw an increase in malware distribution — from 47% in 2017 to 56.4% in 2018.
Mailer script infections decreased from 19% to 12.50%, and 51.3% of all infections were related to SEO spam campaigns.
You can find more information about malware families within our report, which is available from our website and in PDF format.
We take great pride in our research efforts and hope that you’ve found our latest report engaging and insightful. We’d especially like to thank Fioravante Souza, Denis Sinegubko, Marc-Alexandre Montpas, Tiago Pellegrini, and Tony Perez for their extremely valuable contributions. Without their expertise, this report would not have been possible.
Our researchers and analysts will continue to expand on the data we collect during remediation, but any feedback or recommendations would be appreciated. We’d love to hear what you think!