We’ve recently noticed an increase in reports of phishing and malware being distributed via SMS text messages.
During one investigation, we identified fake messages sent from a random number pretending to be Amazon. The message contents ask the victim to click on the link to confirm their shipping address.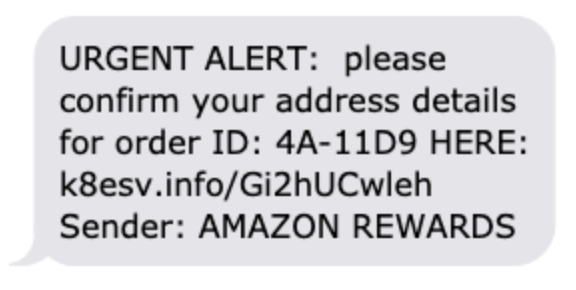
The URL bears no resemblance to Amazon and clearly doesn’t employ Amazon’s URL shortener (amzn.com). Unfortunately, we were unable to confirm exactly what the attackers were directing users to since hxxp://k8esv[.]info now returns a 404 (Not Found) response, but it’s clear that it’s being used for phishing or malware.
In most phishing cases seen distributed via SMS, victims are taken to a fake page ― for example, one that looks like Amazon’s signup page ― and asked to login to access important order information or confirm a purchase.
To the untrained eye, these SMS phishing pages might appear to belong to the real Amazon website, but submitting login credentials typically results in a successful phish ― and an account compromise.
The suspicious domain is hosted on 47.240.4.254 which also appears to be hosting other similar domains:
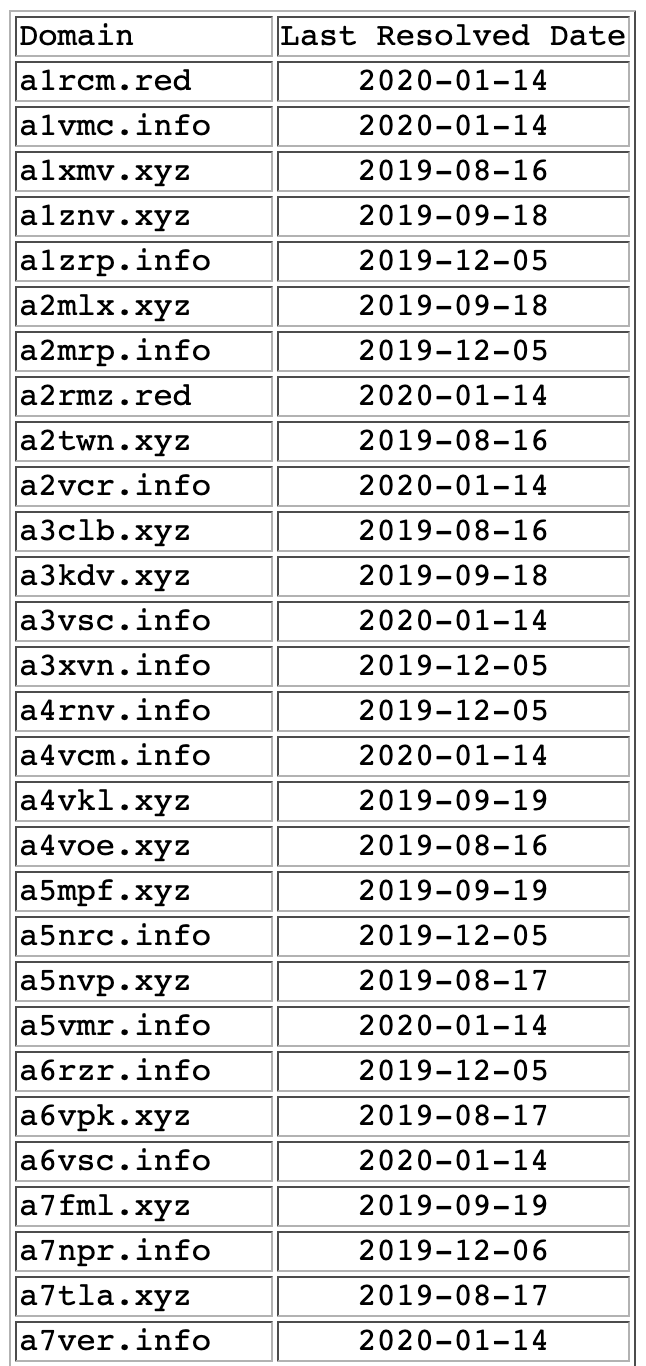
The IP address belongs to Alibaba Cloud:
Alibaba.com LLC AL-3 (NET-47-235-0-0-1) 47.235.0.0 - 47.246.255.255 ALICLOUD-HK ALICLOUD-HK (NET-47-240-0-0-1) 47.240.0.0 - 47.240.255.255
The domain was registered through namecheap.com and has WHOIS protection, so we can’t see who was responsible for registering hxxp://k8esv[.]info. What we can tell is that these other suspicious domains were also registered there, suggesting the same person was involved.
We’re finding many variations of SMS phishing campaigns, and not every text looks the same. Users should always exercise caution when receiving SMS from unknown numbers.
To mitigate risk, avoid clicking on any links inside text messages ― especially if they are coming from an unknown number and lead to suspicious URLs. If you receive an SMS message similar to this one, login directly to your Amazon account via the Amazon website and check if there are any issues or status updates that require your attention from the account dashboard.
We will continue investigating this campaign to see if we can get more details about the attack.