Our malware removal service is particularly effective because it combines automated and human elements. The process gets off to a quick start thanks to cleanup scripts developed by our threat researchers.
Real people also get their hands dirty handling tough work that shouldn’t be automated.
The automated scripts identify and remove a lot of website malware using the same threat definitions that power our Web Application Firewall (WAF) and SiteCheck website scanner.
Meanwhile, our remediation teams verify automated results and handle cleanup that’s better left to experienced specialists, like nuking spam or removing a site from search engine blacklists.
From a high level, website cleanup is achieved in four stages, each involving both manual and automated aspects:
- Ticket created
- Site prepped
- Cleanup time
- Following up
Let’s take a look.
1. Ticket created

When a client submits a malware removal request, our system automatically creates a ticket to track the process, start to finish. Remediation teams evaluate the scope of the infection and tag each issue affecting the website.
If the client has a plan with a guaranteed service level agreement (SLA), the ticket is prioritized in our queue to meet the response time. If there’s no SLA, the ticket is added to the queue for the next available team member to handle.
Some of our plans offer very attractive pricing, but don’t include a guaranteed SLA. With more affordable plans, cleanup time varies depending on our volume of requests.
Either way, the most important aspect of this phase is determining how we access the website. Going back and forth for login credentials significantly slows down the cleanup process. Having them ready lets us get started right away.
And if you aren’t familiar with stuff like FTP credentials, don’t worry. It’s easy to learn the basics.
2. Site prepped

With issues tagged and login credentials in hand, a member of our remediation teams manually logs in to the hosting account of the infected website. The remediation specialist uploads automated tools developed to identify and remove some malware.
The remediation specialist then manually interacts with the site like a visitor would. The idea here is getting the website ready and seeing how it functions before cleanup.
3. Cleanup time
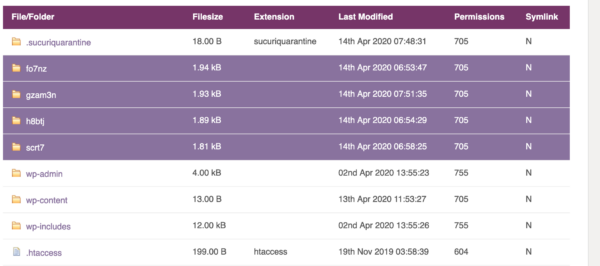
Now that we’ve manually interacted with the site to understand some of its issues, our automated tools check for vulnerabilities and signs of infection. These include outdated versions of the CMS and its components, and malware identified by our researchers.
The automated tools fix the issues they uncovered, but this is only the first step. The remediation specialist still has work to do.
Some hacks require human verification, such as spam comments on a blog. Our remediation specialist removes these hacks by manually combing through files and databases. They also go back and interact with the site like a visitor, to evaluate its state after cleanup.
In a minority of cases, the first analyst may need to escalate the ticket to a senior support tier. This can happen with new malware strains or complex infections that require an experienced analyst to safely remove.
4. Following up
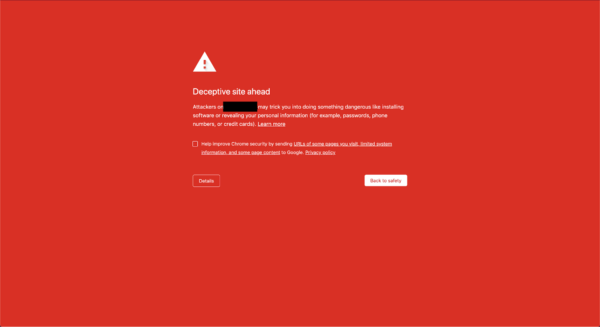
Once our remediation specialist is confident the website is ready to go back into the wild, they check search engine blacklists. If the site is blacklisted, our remediation specialist submits requests to restore good standing.
This is also an opportunity for education. We inform the website owner of every issue we remediated and offer post-cleanup steps to take. If more evidence of the infection is discovered, we repeat the entire process, free of charge, until the site is completely clean.
Act fast to clean your hacked website
The steps we just explored at a high level are deeply involved, and that might dissuade some website owners from taking immediate action. Unfortunately, this is a mistake with expensive consequences. Infections need to get cleaned, ASAP.
The longer a hack remains in place, the harder it becomes to clean and the more damage it causes. It’s always recommended to take proactive measures and act immediately in the event of a hack, either by seeking professional help or cleaning it yourself.