Security Risk: High Exploitation Level: Easy CVSS Score: 9.9 Vulnerability: Remote code execution (RCE) Patched Version: 3.6.3
On April 12th, an important security update was released for the Elementor plugin patching a critical remote code vulnerability which allows all authenticated users, including subscribers, to upload and execute arbitrary PHP code on a vulnerable website.
This vulnerability, identified as CVE-2022-1329, is extremely severe. With over 5 million active installations of Elementor at the time of writing, a significant number of websites are impacted.
WordPress websites using the Elementor plugin should patch immediately. Sucuri web application firewall users are protected from this issue.
Technical Details
Originally reported by WordFence’s Threat Intelligence Team, this critical vulnerability leverages a lack of capability checks found in vulnerable versions of the plugin.
Attackers are able to upload malicious code as a fake plugin archive file and use the vulnerable upload_and_install_pro action to execute their payload in the compromised environment. By exploiting this vulnerability, attackers can easily take over the site or access resources on the web server.
Update Elementor
To protect against this vulnerability, we strongly encourage Elementor users to update their plugin to a version 3.6.3 or greater as soon as possible.
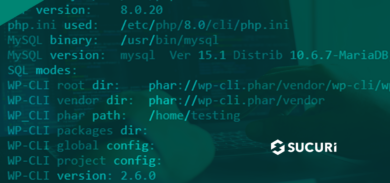
Users who are unable to update immediately can leverage the Sucuri Firewall to virtually patch their website against all known vulnerabilities.