Even the most diligent site owners should consider when they had their last website security check. As our own research indicates, infections resulting from known website vulnerabilities continue to plague website owners. In our 2023 Hacked Website Report, WordPress accounted for 95.5% of the infected sites our incident response team cleaned that year, a figure that closely mirrors its dominant share of the CMS market rather than reflecting any inherent flaw in the platform.
However, Patchstack’s 2026 State of WordPress Security report adds important context: 11,334 new vulnerabilities were disclosed across the WordPress ecosystem in 2025. That’s a 42% increase over 2024, with roughly 91% of them originating in plugins and themes rather than WordPress core. Statistics like these highlight why it’s so important to regularly scan your website for vulnerabilities.
Vuln scanners will look at your online property and web apps much like a bad actor would, carefully searching out any insecure or vulnerable code that could lead to a hack. But if you’re aware of those security threats, you can patch them and harden your site before they are exploited by an attacker.
If you do have an infected site as a result of a software vulnerability, it’s critical you act quickly; either fix the malware yourself or have a professional do it for you.
How to scan your website for vulnerabilities
Here are six website security check and vulnerability scanning tools that can help you scan your site for vulnerabilities.
1. SiteCheck
If you need a quick answer to whether your website is infected or flagged, SiteCheck gives you that in seconds. This free remote scanner checks any URL for malware, blocklist warnings, defacements, SEO spam, outdated CMS software, and injected malicious code. There is no setup required. Paste in your site’s address and you get a clear report, which is why millions of site owners rely on it every month.
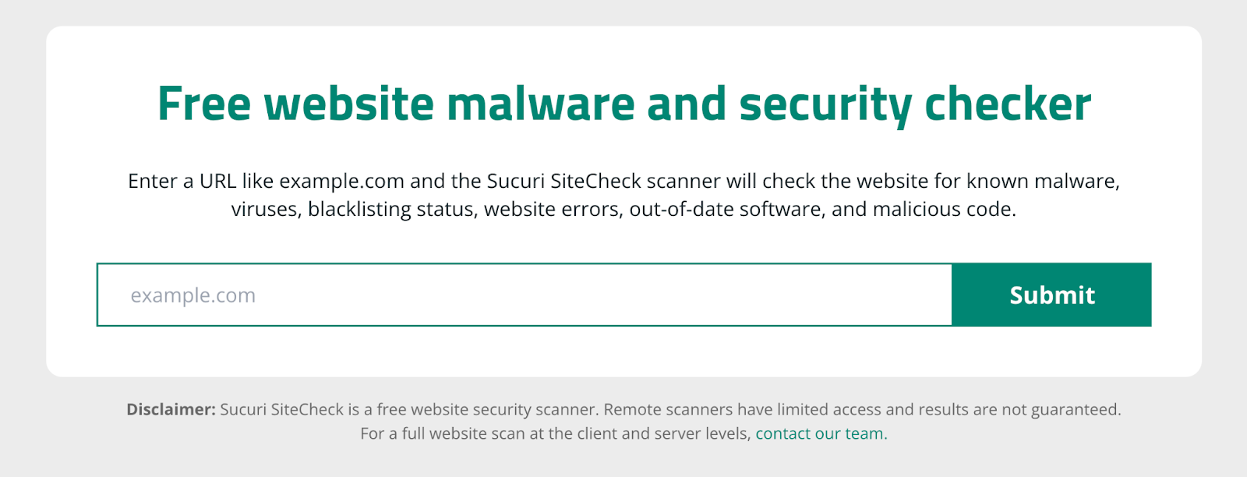
SiteCheck scans your site from the outside, just like a visitor or search engine would. That makes it especially effective at spotting threats that show up in the browser, such as credit card skimmers, malicious redirects, and obvious signs of compromise. It will not catch malware hidden deep in your server files or database, so for a full picture you should combine it with a server-side scanner. Still, as a first step that requires no setup, it is one of the fastest ways to find out if your site is at risk.
2. WPScan
With the widespread adoption of WordPress today (WP powers more than 43% of sites on the web), it might seem like the free WPScan is nothing short of a miracle. WPScan, now part of Automattic, runs a large, manually curated database of WordPress vulnerabilities across core, plugins, and themes. Their team of security researchers updates it daily, giving site owners a reliable source for tracking new risks as they emerge.
Installation might require some plain-language documentation, but once you’ve checked out the Github repo and set it on your Linux or Mac machine, you get access to a website security check from a team that maintains an active vulnerability database.
You can check out our helpful guide on how to install WPScan and scan your website for vulnerabilities.
Note: The standalone WPScan WordPress plugin is no longer actively supported for non-enterprise users. For DIY site owners, the WPScan team now recommends the free Jetpack Protect plugin, which is powered by the same WPScan vulnerability database.
3. MageReport
Online retailers using the popular Magento Open Source and Adobe Commerce platforms can use the MageReport tool, which was engineered specifically for this ecosystem.

In particular, Magento 1 users will want to keep vulnerability scanner tools close at hand, as it reached end-of-life on June 30th, 2020 and is no longer receiving updates.
Magento 2 and Adobe Commerce users shouldn’t get comfortable either. Critical flaws continue to surface, most recently SessionReaper (CVE-2025-54236), a 9.1-severity unauthenticated remote code execution vulnerability disclosed in September 2025 that was actively exploited against unpatched stores within weeks. Adobe’s free built-in Magento Security Scan Tool is another option worth running alongside MageReport.
4. Snyk
If you’re looking for a thorough scan of your web application, Snyk makes it easy to check your code, dependencies, containers, and infrastructure for known vulnerabilities. They cover most of the languages and frameworks you’re likely to use, so you can scan your site’s code for vulnerabilities before attackers find them. That means fewer blind spots and a better chance of catching issues before they turn into downtime or cleanup headaches.
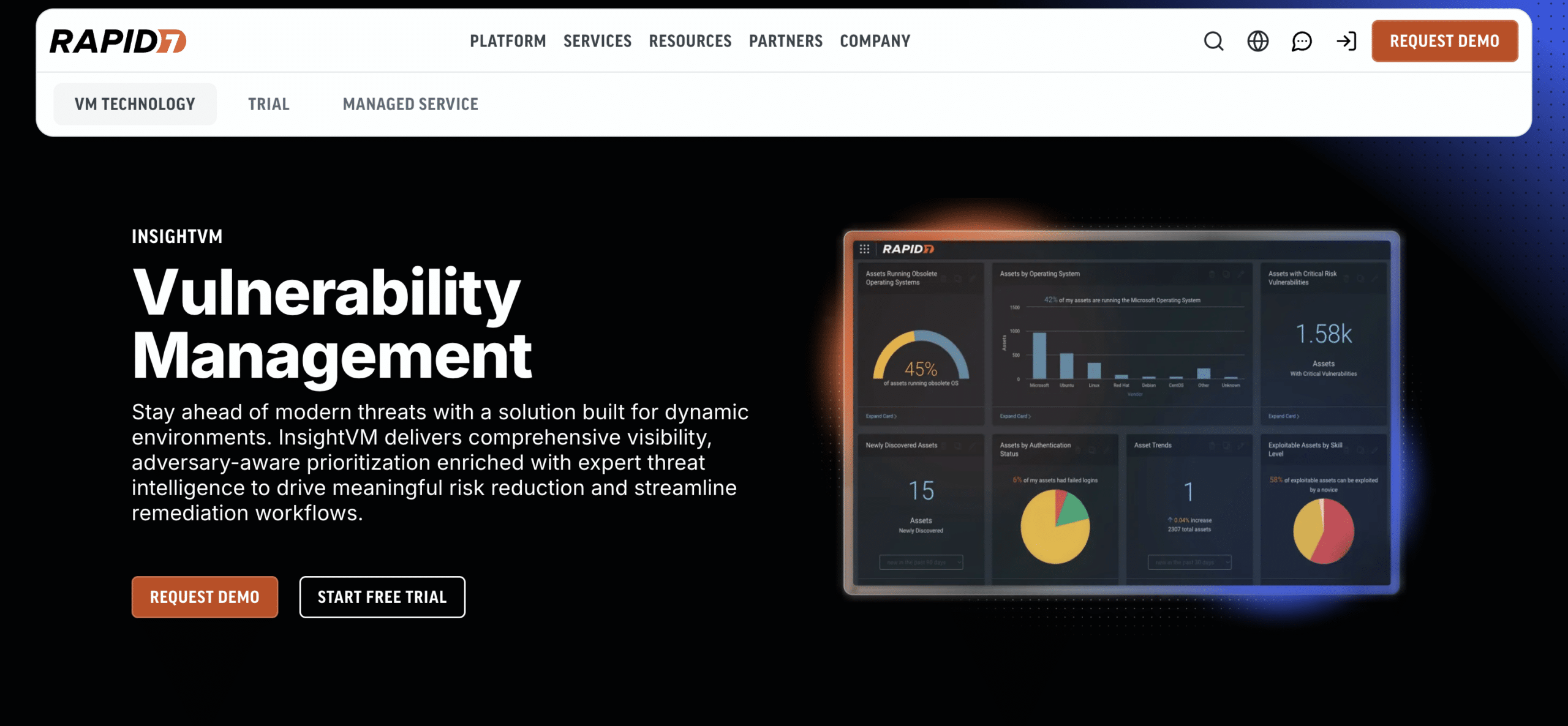
5. Rapid7 InsightVM
Rapid7’s vulnerability management platform, now called InsightVM and previously known as Nexpose, is a server-side scanner built to identify security gaps in real time. For site owners looking to spot vulnerabilities before they turn into downtime or compromise, it offers a practical way to scan your environment, with a free trial available for those who want to see how it fits into their workflow. This helps you stay on top of vulnerabilities as they emerge.
Vulns are presented in a list with risk scores, offering a clearer picture of which vulnerabilities are truly critical. InsightVM’s Active Risk scoring incorporates CVSS v3+ standards and real-world exploit intelligence (including data from sources like AttackerKB), so the issues most likely to be exploited in the wild rise to the top instead of getting lost in the noise.
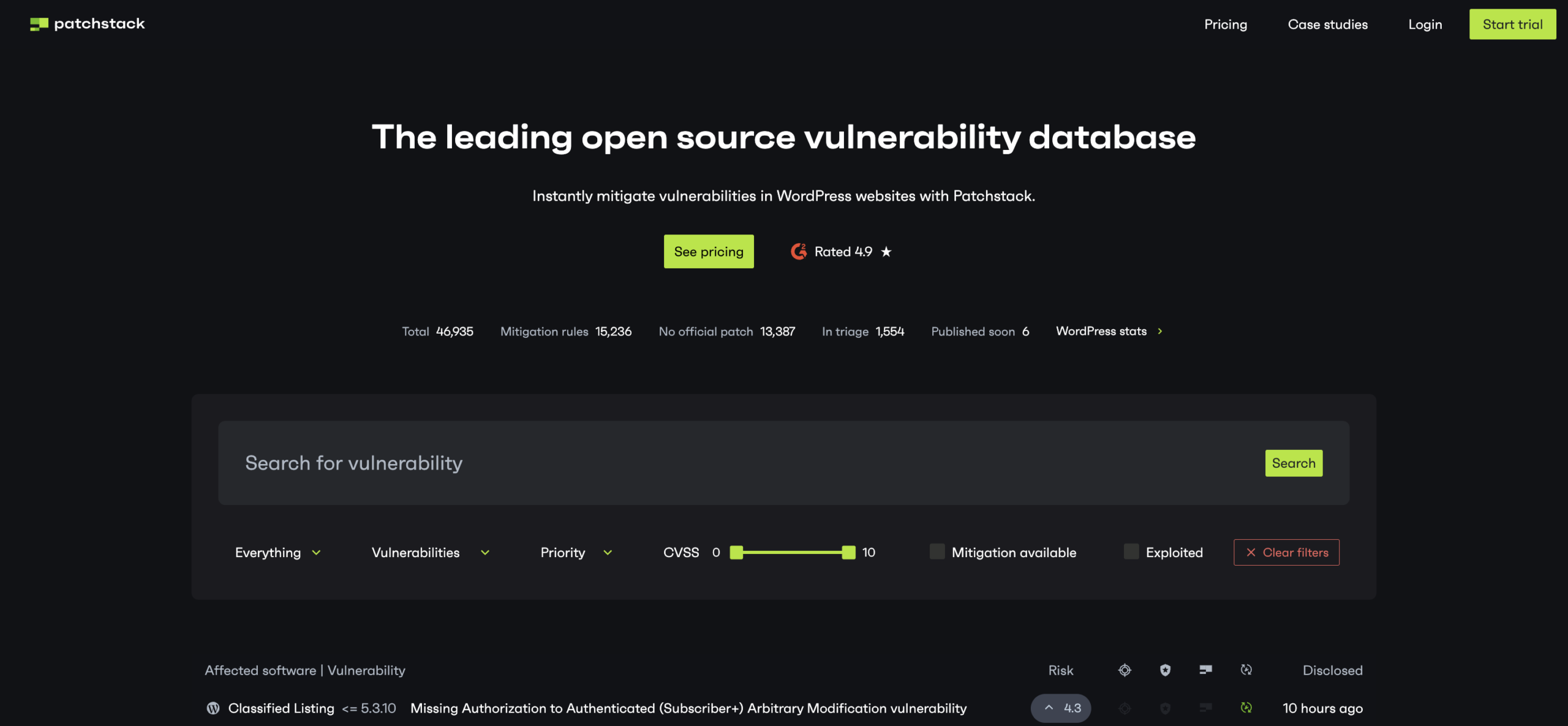
6. PatchStack
Installing the PatchStack plugin on your WordPress site can make checking for plugin, theme, and CMS vulnerabilities a breeze. Patchstack has become the leading vulnerability intelligence provider for the WordPress ecosystem, reporting roughly 67% of all named WordPress vulnerabilities in 2025.
To get started, you’ll need to register for a Patchstack account, add your web application to the dashboard, and then activate their plugin on your site. Once installed, you’ll be able to see an overview of your website’s security, set up custom alerts, and easily generate security reports on the fly from the Patchstack account dashboard. Paid plans include virtual patching, which means your site gets a set of targeted rules to block attacks against known vulnerabilities before an official fix is released. This is especially important for WordPress sites, since 46% of the vulnerabilities disclosed in 2025 had no patch available at the time of disclosure. Without this layer, your site could be exposed for weeks or longer while waiting for a developer update.
Wrapping up: Don’t wait for a website security check
They’re out there. Bad actors work around the clock looking to profit from website vulnerabilities, and it may only be a matter of time before they target you.
However, there’s no need for stress when you’re regularly using one of these vulnerability scanner tools to spot if something is wrong with your website.
Frequently asked questions about website vulnerability scanning
How often should I scan my website for vulnerabilities?
At a minimum, run a free remote scan weekly and a deeper server-side scan monthly. Run an additional scan immediately after installing or updating any plugin, theme, or extension. Also scan after any major code, hosting, or DNS change. Exploitation now happens within hours of public disclosure for some flaws, so weekly is the floor, not the ceiling.
What’s the difference between a remote scan and a server-side scan?
A remote scan like SiteCheck visits your site from the outside and inspects what visitors and search engine bots can see. It is useful for catching client-side malware, blocklist warnings, SEO spam, and visible signs of compromise. A server-side scan runs inside your hosting environment and inspects files, processes, and databases directly. This is how you find hidden backdoors, phishing pages, and obfuscated PHP malware that never appear in the rendered HTML. Most sites benefit from running both.
Are free website vulnerability scanners good enough?
For most small and mid-sized sites, yes. A free remote scanner paired with a CMS-specific scanner (WPScan or Patchstack for WordPress, MageReport for Magento) covers the basics well. Enterprises, e-commerce stores, and high-traffic sites should add a paid platform that provides continuous server-side monitoring, a web application firewall, and access to a professional incident response team.
Which website vulnerability scanner should I start with?
If you don’t know where to begin, start with SiteCheck. It’s free, requires no installation, and gives you a public-facing snapshot of your site’s health in seconds. From there, add a scanner that fits your platform: WPScan or Patchstack for WordPress, MageReport for Magento/Adobe Commerce, and Snyk or InsightVM if you’re managing custom application code or larger infrastructure.
Looking for a comprehensive website security solution? We’ve got you covered. Our website security platform includes vulnerability detection, protection, and malware clean ups in case your site is already hacked.