During the last couple of years, website ransomware has become one of the most actively developing types of malware. After infamous fake anti-viruses, this it the second most prominent wave of malware that makes money by directly selling “malware removal” services to users of infected computers. But unlike fake anti-viruses, that were mostly harmless, and used as a social engineering technique to make people pay for removal of non-existing threats, ransomware is a much more serious beast. It doesn’t pretend to be a good guy. It actually makes your computer unusable unless you pay the ransom.
So what happened? Why don’t we see large scale fake anti-virus campaigns any more while ransomware is all the rage? I guess the answer is the payment method.
Fake AV and Credit Cards
Fake anti-viruses pretended to be backed by reputable companies. To look legit they had to accept credit cards and thus work with banks. As a prevalent threat of that time (in 2008 alone more than a million people were tricked to pay them) such schemes attracted attention of authorities, who, among other things, managed to reveal money-laundering banks and credit card processing companies used by the scammers. Brian Krebs wrote how and why things began to change in 2012:
It doesn’t require a judge, a law-enforcement officer or even much in the way of sophisticated security capabilities. If you can purchase a product, then there’s a record of it and that record points back to the merchant account getting the money,” Savage said. “Visa and MasterCard frown on sales of illegal purchases made on their networks and will act appropriately on complaints from brandholders based on undercover purchases.
Since then, some of the banks had been closed, others [hopefully] decided to stay away from the scammers. As a result, today it’s not that easy to run really massive “scareware” campaigns that use exclusively white hat payment methods (which is crucial to look trustworthy).
Ransomware and Bitcoin
Ransomware doesn’t have to pretend to be a legitimate business. From the very beginning you know that you deal with criminals so it’s natural that the only payment method they accept is anonymous bitcoins. It’s definitely not as user-friendly a method as credit cards or PayPal, but who cares if the victim is already cornered and it’s the only way to recover their files (if they didn’t have a backup).
Were such ransomware schemes viable 5 to 8 years ago when fake anti-viruses thrived? Apparently, no. They couldn’t accept credit cards or PayPal as their transactions are easily traceable and there is no doubt that many victims would report such cases to police. Bitcoin, or other anonymous cryptocurrencies, were also not an option. First of all, most of them didn’t exist back then. For example, Bitcoin was created only in 2009. Secondly, even after 2009, it took a few years to build an ecosystem around bitcoin and reach the level of adoption that made it worthwhile.
With mass adoption of Bitcoin, soon we should see new types of malware and criminal schemes coming to existence.
Website Ransomware
At this point hackers are playing with an obvious idea of expanding ransomware from local computers to websites. In 2015, we began seeing more and more things such as DDoS attacks that extorted Bitcoins and encrypted websites, where hackers demanded ransom (1 Bitcoin or ~$420) to decrypt files.
CTB-Locker
This year we’ve been watching how infamous PC ransomware called CTB-Locker is trying to enter the new niche of website ransomware.
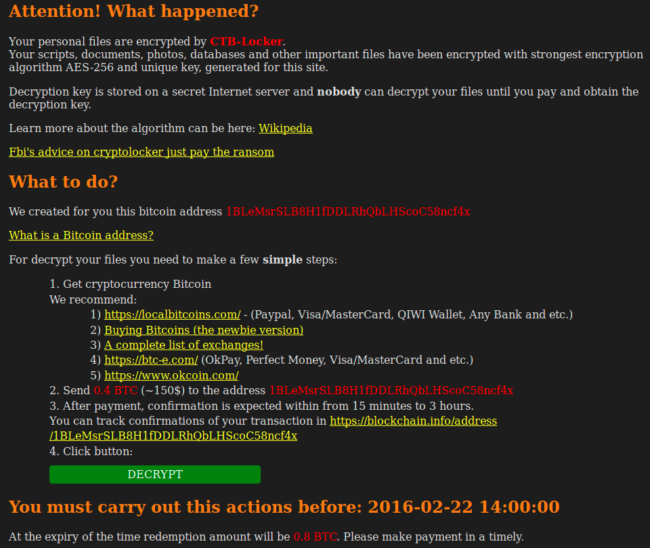
This is the message it placed on encrypted websites in February:
It’s pretty much standard CTB-Locker message screen ported from the PC version.
The ransom is 0.4 BTC (Bitcoins) if pay straight away or 0.8 BTC after a few days. As you can see the price (0.4 BTC / $170) is higher than typical fake-antivirus ($40-$80), but significantly lower than 3 BTC that the same CTB-Locker used to ask on encrypted PCs. It is also lower than 1 BTC, that ransomware demanded on encrypted websites back in December 2015.
Ransom Decrease in March
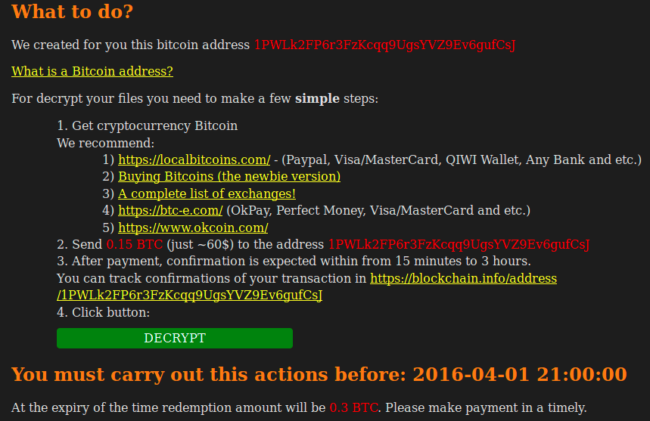
Apparently, this price drop was just an intermediate step. In March the CTB-Locker message looked like this:
As you can see, just a month later the ransom dropped from 0.4 BTC to 0.15 BTC (~$63), and from 0.8 BTC to 0.3 BTC (~$125) for late payments. Now the price range resembles the tried and true price range of fake anti-viruses. Is it a coincidence? Probably yes, but if you think more about it, you’ll notice that this “website ransomware” is more close to “scareware” than its desktop version. I’ll let you ponder on this idea for a moment. Meanwhile, let me show you some other interesting changes between the February and March version of CTB-Locker for websites.
“Free Decrypt”
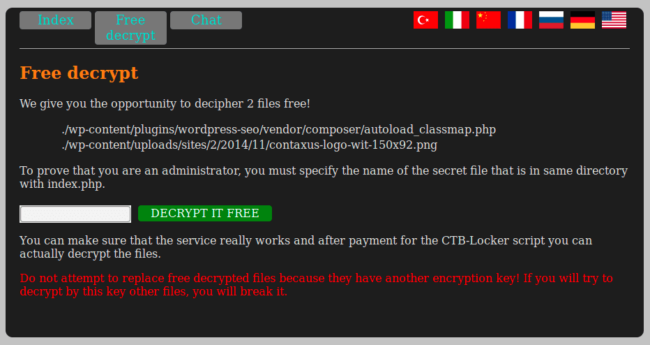
CTB-Locker encrypts two random files with a different key and allows the victim to decrypt them for free as a demonstration of its functionality.
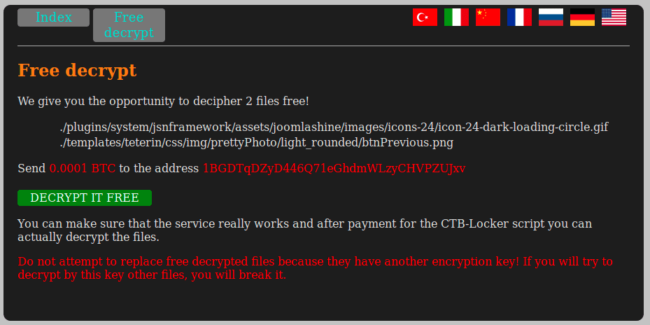
This helps increase confidence that after paying the ransom the website can be restored. But look how this feature changed in March:
Looks similar unless you notice that the “free” test now costs 0.0001 BTC.
What’s going on? Why do they ask money (0.0001 BTC is just 4 cents but still you have to pay) for the free test? Why are they adding obstacles instead of making the process smoother? I promise I’ll get back to these questions a bit later, after I show you one more important internal change in the March version of the CTB-Locker.
Decryption via Third-Party Gate Sites.
ThisIsSecurity does a great job describing how the February version of the website CTB-Locker works. It shows that successful decryption depends on the access.php scripts on about a hundred third-party “gate” sites. But this approach is not reliable. Those gate sites are hacked sites too, so the access.php script can be removed from them at any time. To increase chances that the decryption script works with a live gate, every such script has a list of three random predefined gates, i.e.
admins = ["hxxp://stian .malkenes .com/access.php", "hxxp://autobot .sk/access.php", "hxxp://cresynin .com/cgi-bin/access.php"];
But even these three predefined gates can’t provide an absolute guarantee that the site can be decoded after the payment.
The problem with this unreliable intermediate layer has been successfully solved in the March version of the CTB-Locker. The solution is very elegant. It’s based on the hottest topic in the Bitcoin world – blockchains.
Blockchains
Blockchains are just chains of verified transactions. Because of the distributed nature of the bitcoin system and strong cryptography, they can’t be tampered. Many people think that blockchain technology can potentially disrupt conventional financial business making lots of things cheaper and not requiring intermediaries such as banks, notaries, etc.
To understand how CTB-Locker uses blockchains, we need to know about the following features:
- Every bitcoin transaction is recorded in the global publicly-distributed blockchain database.
- If you send bitcoins to some wallet and the owner of that wallet spends the money, it will all be recorded in a public blockchain.
- The blockchain database is public and anyone can see all the transactions of any Bitcoin wallet. If you follow the blockchains, you can see the whole history of every coin.
- There are public (and quite reputable) services that allow you to view bitcoin blockchains. For example, blockexplorer.com and blockchain.info. CTB-Locker uses both of them.
- Each record in the blockchain contains all of the important information about the transaction such as timestamps, wallet addresses, sums, links to related transactions, etc.
- In 2014, version 0.9, Bitcoin protocol was extended so that transactions could contain small blocks of arbitrary text (metadata) in the OP_RETURN field. This OP_RETURN metadata is what makes blockchains applicable in so many fields completely unrelated to Bitcoin.
- [Most] Bitcoin transactions are not free. The fee system is not very simple, but it suffices to say that most transactions require at least a minimal fee of 0.0001 BTC.
Now you know enough to understand the change in the March version of website CTB-Locker.
Use of Blockchains in CTB-Locker
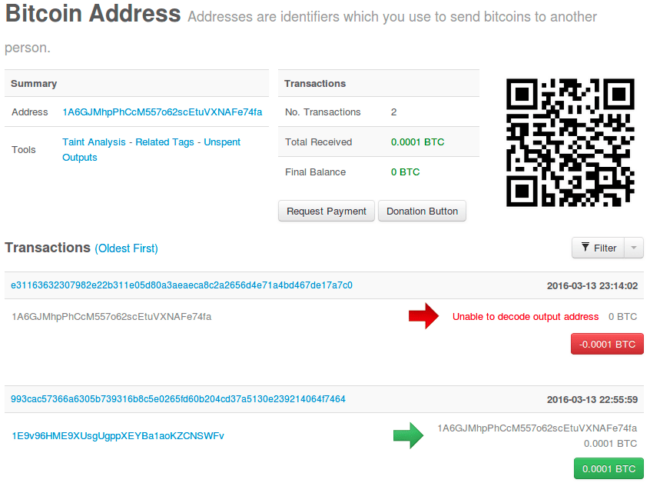
For each encrypted website, hackers create a new Bitcoin wallet with a unique address that they publish on the ransom demand page. For example: 1A6GJMhpPhCcM557o62scEtuVXNAFe74fa (this is a real bitcoin address generated for one real hacked site)
Decryption Keys in OP_RETURN
When the victim pays the ransom, or transfers the 0.0001 BTC fee for the “free” decryption, hackers check the transferred sum. If they see 0.0001 BTC, the wallet’s blockchain is appended with a new transaction whose OP_RETURN field contains the decryption key for the two free test files. If the victims pays the full price, they add a transaction with keys for both test and the rest of the encrypted files.
0.0001 BTC Fee
As you might already realize, hackers can’t simply append the OP_RETURN transaction to an empty wallet without revealing their other wallet. Moreover, they need to pay the 0.0001 BTC fee for such a transaction. This explains, why they ask victims to transfer a nominal minimal fee for the “free” decryption test. This initial transfer creates a blockchain for the wallet and provides enough money to pay the fee for the OP_RETURN transaction. The 0.0001 BTC fee is not considered a big barrier for the “free” test as this is really a very small amount of money for anyone (4 cents at the moment), and people who really want to decrypt their sites have to have Bitcoins anyway.
Viewing Bitcoin Transactions
A few minutes later, the OP_RETURN transaction gets validated and propagated through distributed nodes of the Bitcoin system and becomes visible in services that provide information on blockchains. Hackers suggest that their victims track their transactions on the blockhain.info site. For example, here’s a real “free decrypt” blockchain for one affected site: https://blockchain.info/address/1A6GJMhpPhCcM557o62scEtuVXNAFe74fa
Here you can see that there are transactions associated with this Bitcoin address. The first transaction (green) transferred 0.0001 BTC to this address on March 13th at 22:56. The second transaction (red) spent 0.0001 BTC 20 minutes later.
If you click on the red transaction link, you will see that the transaction fee was 0.0001 BTC and it has the OP_RETURN value (scroll down to the Output Scripts section), which decodes to e185da0a5b6acce8fa999e146f461558: . In this value, everything before the colon is the decryption test key and everything after the colon is the full site decryption key. Since it was a 0.0001 BTC transaction, OP_RETURN only contains the “free” decryption test key.
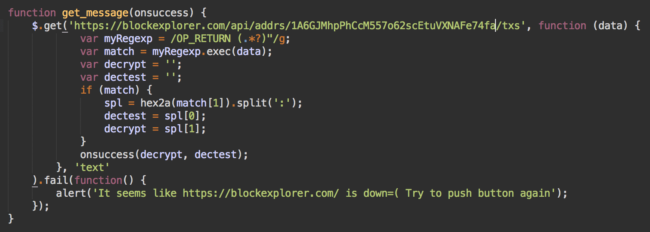
Blockexplorer API
This was a human-friendly representation of the blockchain. However, the CTB-Locker script prefers to work with a computer-friendly version provided by the API on the blockexplorer.com site.
Here you can see the same blockchain provided by the Blockexplorer API in the JSON format: https://blockexplorer.com/api/addrs/1A6GJMhpPhCcM557o62scEtuVXNAFe74fa/txs
So, instead of using unreliable gates on third-party hacked sites, the March version of the CTB-Locker reads the keys directly from public and much more reliable blockchain information services. That’s the beauty of Bitcoin transactions – everything is public and transparent, and at the same time it’s possible to keep things anonymous and not traceable to real IPs.
Failure of Website Lockers
Despite the smart technical solutions, I can’t call the website version of the CTB-Locker successful. They decrease their ransom for a reason: webmasters just don’t pay them.
The model that works for PCs doesn’t work for websites. If CTB-Locker encrypts a PC, the user loses really important files: documents, images, audio and video files, local archives, and backups. If they don’t have external backups (on external disks, other computers, cloud, etc.) all the files are lost. You might have a lot of junk on your computers, but if it stops booting, you’ll quickly realize that those are very important files (work-related or personal) and you’re willing to pay to recover them. That is the reason there are services that recover data from failed hard drives.
In case of both disk failure or file encryption, the cheapest recovery solution provides a fresh external backup. But we all know quite a lot of people who don’t do regular backups of data on their computers. This is especially true for people who are not that computer literate, and who are the most likely victims of various sorts of malware (including ransomware).
But if we look at websites, we’ll see that the majority of web hosting plans (even the cheapest ones) historically come with backups. This means that even most computer-illiterate webmasters can [kind of] easily restore their encrypted websites to a relatively fresh version in a very short period of time for absolutely free. So why pay the ransom?
That’s why in the beginning of this blogpost I said that website ransomware is more close to “scareware” that tries to trick webmaster to pay for the service they don’t actually need.
Conversion Rate of CTB-Locker for Websites
To prove this hypothesis, I googled for sites encrypted by the CTB-Locker and then routinely checked transactions for every bitcoin address published on the ransom demand pages (reminder, CTB-Locker generates unique bitcoin addresses for every encrypted website). Out of almost 100 sites I checked, only one had a real “free decryption test” 0.0001 BTC transaction (the one I used as an example above in this blogpost, and it was from someone who already had and used bitcoins before the attack – not a typical victim). Bitcoin wallets for all the rest of the encrypted sites had zero transactions. My investigation showed that none of the webmasters paid the ransom, still most of them successfully recovered their sites (I had to retrieve their ransom demand pages from Google’s cache). The few sites that still remain encrypted look abandoned (or their owners simply didn’t check them after the infection).
Summary
New technologies change our lives in many different ways. They open up exciting possibilities. But they are also responsible for new emerging threats. This blog post shows how ransomware (and especially crypto-ransomware) has gone mainstream thanks to Bitcoin and its underlying blockchain technology.
On the other hand, even smart use of a new technology is not a guarantee of success when you porting a tried-and-true business model from one niche to another. The devil is in the details. In the case of website crypto-ransomware, such overlooked details supply easy access to backups for most websites, which allows them to ignore ransom demands.
Nonetheless, I’m sure we’ll see more new waves of website ransomware attacks as hackers try to change their tactics and search for a magic recipe that will allow them to get money directly from owners of compromised websites.








4 comments
You beat me to the punch on this one. Have a 1/2 written article I started on this subject from a week or so back, which it seems I’ll never have time to post. This is the best summary I’ve seen on this subject to date. Nicely done.
To help spread the word, I posted a link back in the WordPress Security Facebook group as well.
Really interesting this post, thanks for all explanation and examples!
As known recently most of users have been infected by TESLACRYPT Virus which changes all important documents like pdf,doc,xls,mp3,mp4,mpeg,avi,etc to .vvv, .ecc, .ezz, .exx, .xyz, .zzz, .aaa, .abc, .ccc, .xxx, .ttt, .micro, mp3 and “no extension change on last version” are encrypted and not usable/readable unfortunately. I can help infected users to decrypt their files, you can contact with me with below email address if you or one of your friend had been infected this kind of virus. Also there is paid solution for .encrypted extensions, please write me if you are interested.
Email: mcerdem82@yahoo.com
My name is Scott. I am a professional photographer from Michigan. On
August 11, 2015 my computer was infiltrated by hackers utilizing an
advanced and evolving hacking and data encryption program. It is not the
only one of its kind, however the bad guys are continuing to invent new
and more powerful ways to separate people and companies from the things
they need the most. It is something that never should happen. It is
wrong what these people do and they are doing it every day. They are
doing it as I write this. They call it RANSOMWARE. It is a word I
myself, a common computer user, had not hear of.
These programs go by different names. They all do about the same thing,
which is to lock you out of your own computer and/or render files on
your hard drive inaccessible to you and most people on the planet
incidentally. It is a troublesome and disturbing new trend in cybercrime
and I feel law enforcement and our government are NOT doing nearly
enough to combat these people and their very REAL weapons.
They seem to be targeting at random. Individuals, Small businesses, and
even law enforcement its self. There is a new shared danger in this
fluid situation that is different from other computer virus programs in
that even with the best protection the government has at its disposal
there are people who know how to break in. Once one of these RANSOMWARE
programs is able to upload onto your system you may never know it is
there until it strikes. When it does, it is very fast and there is
nothing you can do to stop it. Your file icons will flicker and
disappear. You will see this happen as I did. The files will reappear,
but in an encrypted format that MOST people will never break, it seems.
You will need to know a lot about computer CODE and DECRYPTION.
If you start to see your files going away the only thing you can do is
unplug your system from the wall or shit it immediately down as fast as u
can. Just hit the button!! In some cases doing an immediate system
restore and/or factory restore can assist in the recovery of files. It
depends a lot on when your last hard drive RESTORE POINT was made. That
is something you should often do, particularly if you do a lot of work
on your computer and have more files you are dealing with.
The best thing you can do keep updated copies of important material. On
CD as well as computer that is NOT connected at all to the internet.
That is want I mostly do. I have computers for networking and I have
other for editing and other things. It is best to keep things separate,
now more than ever.
As of this writing there is no decryption for the version of this virus
program that has locked my files from me. It is called CTB-LOCKER. It
uses RSA-2048 ENCRYPTION. Please feel free to google these things so you
can learn more about what these programs really are, how they work and
how dangerous they really are. Or google RANSOMWARE. I am hopeful that
one day soon they will catch these evil people, or the good guys will
come up with a solution. Some of these people have actually stopped and
released their CODES so people could actually retrieve their data, but
every situation is different and no one can say for sure if decryption
will ever happen. I know there are a lot of people out there like me who
have been victimized by these evil people and I want them to know that I
feel their pain. I want to see these evil bad people in court. I want
them to know that they have HURT PEOPLE and I want to see them go away
for the rest of their lives.
I want to thank Roxy Lopez again for her courage in taking on this
global issue and I thank here again for her time. Hopefully together we
can get this very serious issue into a greater light and maybe the bad
guys will have less places to hide.
Sincerely
Scott Matthew Smith
Comments are closed.