Today we’re releasing our quarterly Hacked Website Report for 2016/Q2. The data in this report is based on compromised websites we worked on, with insights and analysis performed by our Incident Response Team (IRT) and Malware Research Team (MRT).
CMS Analysis
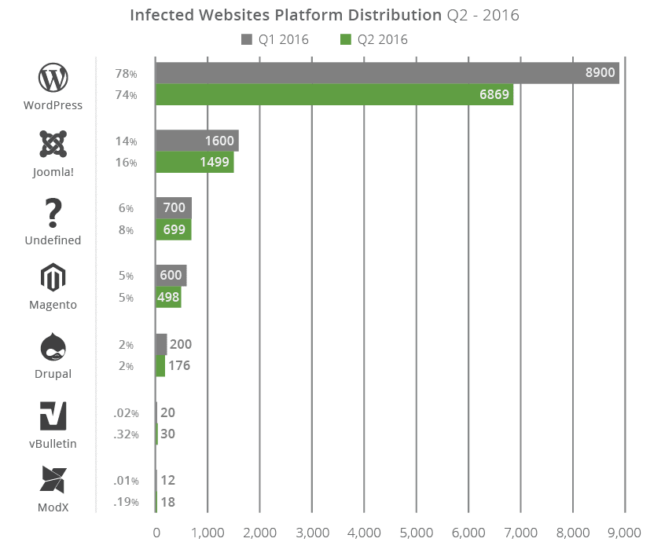
Our analysis consisted of over 9,000 infected websites. The graphs below show a side-by-side comparison with our 2016/Q1 report.
The four open-source Content Management Systems (CMS) we focus on in our report include WordPress (78%), Joomla! (14%), Magento (5%), and Drupal (2%).
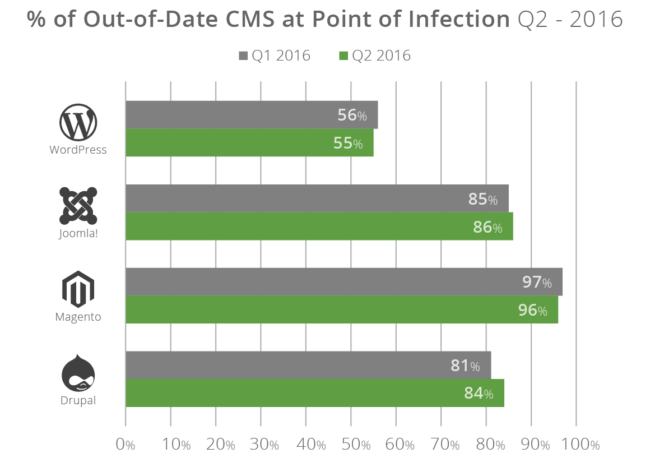
We dive into specific information about out-of-date software found on websites going through our cleanup process. Some interesting datasets include that WordPress installations were out-of-date 55% of the time while Joomla! (86%), Drupal (84%), and Magento (96%) continue to lead the way with out-of-date software.
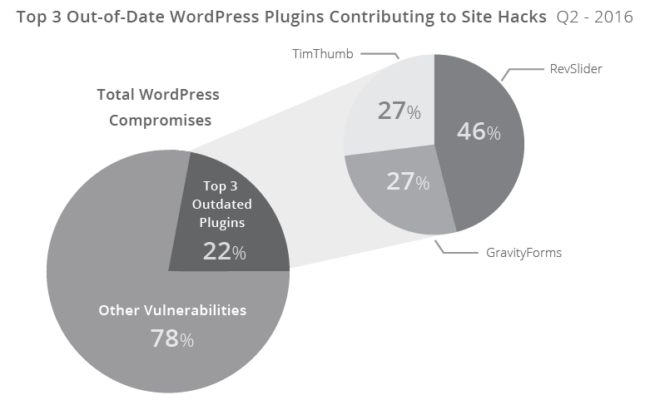
We briefly cover specific extensible components within the WordPress platform. As it makes up the largest sampling in our environment (78%), we place special emphasis on the top three plugin vulnerabilities contributing to 22% of WordPress site hacks.
In this report, we also include a new telemetry dataset that shows the most popular WordPress and their distribution amongst the sample set. On average, we found that WordPress installations had 12 plugins installed at any given time.
Blacklist Analysis (New)
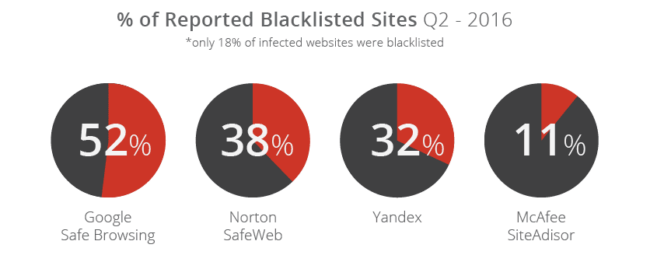
We introduced a new data set highlighting the number of websites that were blacklisted. We felt this was an important bit of data to include as the impacts to website owners can be devastating.
Per our data, 18% of the infected websites we analyzed were blacklisted, which means that 82% of the infected websites we worked on were not flagged. The most prominent blacklist was Google Safe Browsing with 52% of blacklisted sites. Here is a more complete distribution of the blacklist APIs we monitored:
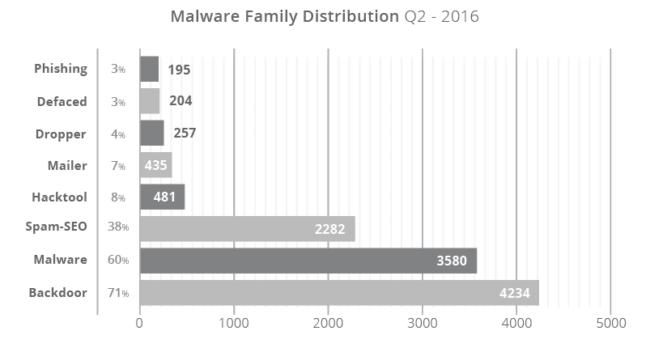
Malware Analysis
We also focused on understanding what attackers were doing once they successfully hacked a website, specifically the payloads they were using.
Our analysis shows that SEO spam continues to be a go-to for attackers, with a 6% increase over Q1. In total, 38% of sites had some form of SEO spam injection. Backdoors continue to be one of the many post-hack actions attackers take, with 71% of the infected sites having some form of backdoor injection.
Hacked Website Report – TL;DR – Cliffsnotes
Some quick takeaways that you might find interesting:
- WordPress continues to lead the infected websites we worked on (at 74%), and the top three plugins affecting that platform are still Gravity Forms, TimThumb, and RevSlider.
- WordPress saw a 1% decrease in out-of-date core software and infected websites, while Drupal had a 3% increase. Joomla! and Magento website deployments continue to show the most out of date instances of any platform.
- New data points show that on average, WordPress installations have 12 plugins, and the report provides a list of the most popular plugins within our set of compromised sites.
- New data points were introduced showing what percentage of infected websites were blacklisted. Only 18% were blacklisted, and Google made up 52% of that grouping (or 10% of the total infected sites).
- Analyzing the malware families showed that SEO spam continues to be on the rise, increasing to 38% this quarter (a 6% increase) and backdoors rose to 71% of compromised sites.
The report is available both on our site and in PDF format.
I’m especially proud of our ability to continue to share this type of information and hope you find it insightful. We will continue to expand on the data we collect and report on, but as usual, if you have recommendations let us know.










3 comments
Have you seen any database or memory-only payloads, such that no local files are modified?
Yes, a few. One example here where the backdoor was hidden in the database:
http://labs.sucuri.net/?note=2016-09-13
There were a few cases where it modified the database only, without touching any files, but I don’t think we ever wrote about them.
thanks,
When I add all the percentages in the CMS Analysis for Q1 and Q2 respectively, I get 105% (for Q1 as well as Q2). How come?
Comments are closed.