Consumers spent a whopping $35.3 billion during last year’s cyber week shopping season. With Cyber Monday accounting for $11.3 billion in revenue alone, this period remains one of the biggest online shopping events of the year.
Unfortunately, hackers are making bank alongside online retailers. As we enter the holiday season, ecommerce websites are at an increased risk for security threats like skimmers, MageCart, ransomware, and phishing. Software vulnerabilities remain one of the most common threats impacting ecommerce websites — with successful exploits known to result in heavy losses for unprepared web stores and organizations.
Don’t make it a sweet Black Friday for skimmers. Here are six ecommerce security threats to look out for during Black Friday and Cyber Monday.
Contents:
- Skimmers & MageCart
- Phishing
- SocGholish (Fake Browser Updates)
- Supply Chain Attacks
- Fake DDoS Verification Pages
- Software Vulnerabilities
Skimmers & Magecart
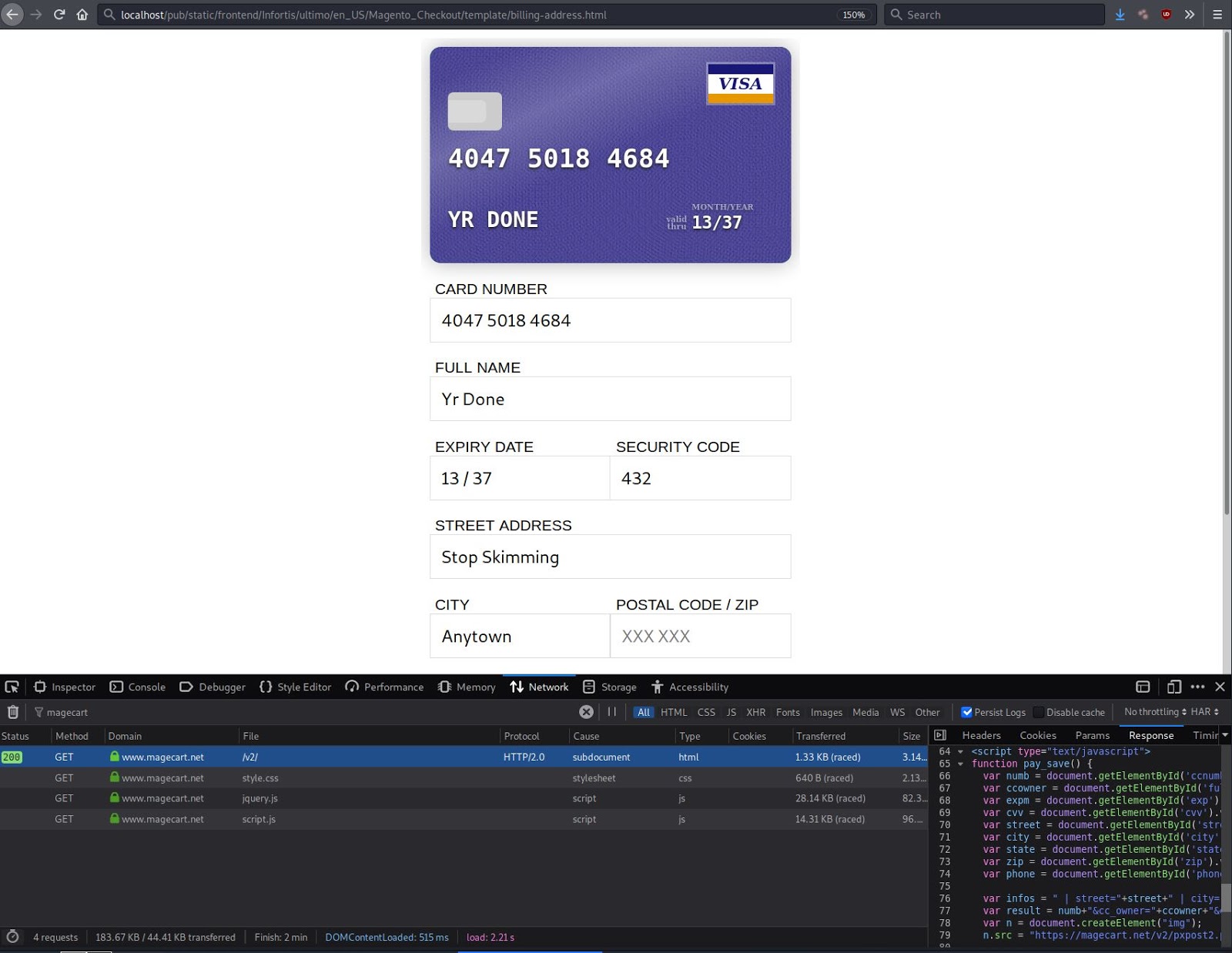
Magecart attacks are known for skimming credit card details and other sensitive information from compromised websites. Also referred to as card skimmers or credit card stealers, Magecart harvests and exfiltrates stolen data as it’s entered on checkout pages and payment forms.
Attacks can even steal data in real time from the purchase process — before the information has been submitted on the page. This means that if you (or any potential customers) enter personal information and credit card details on a compromised website but don’t complete the form submission, there’s still a risk that it can be stolen and harvested.
And while some variants of skimmers exist only on the server level, MageCart attacks are often found as malicious JavaScript injections. According to senior malware researcher Denis Sinegubko, the average ecommerce web page loads over 40 scripts — adding an extra layer of complexity when keeping an eye out for indicators of compromise.
In most cases, developers and website owners aren’t tracking who has added new scripts or if anything has been injected onto the website. But even just a single line of code from one malicious domain is enough for an attacker to swipe the details from the checkout page.
While Magecart derives its name from credit card stealers that targeted the popular ecommerce CMS Magento, attacks have since evolved to target platforms like WordPress, OpenCart, and Prestashop. Since 2021, our data reveals that WordPress detections have exceeded Magento for credit card skimmers — demonstrating how effective and prevalent the malware has become.
Impacts of a Magecart attack can include:
- Data theft. While credit card information is the primary target for Magecart, attacks can also steal personal information.
- Lost site revenue. A small to medium sized webstore may experience a loss in revenue and decreased sales due to infection and damaged reputation.
- Cross-site contamination. Infections are known to spread between shared server or hosting environments, affecting other retail or web store websites.
- Legal damages and compliance issues. Magecart attacks spell disaster when it comes to legal penalties and PCI compliance, potentially leading to hefty fines and inability to accept credit card payments.
Phishing
Phishing attacks continue to be a pervasive threat in 2023. This malware can be distributed through a variety of methods, but are most commonly circulated via popular communication channels like email, SMS, and messaging applications like Facebook or Instagram.
According to ProofPoint’s latest 2023 State of the Phish report, direct financial loss from successful phishing attacks increased by 76% in 2022. And earlier this year, Bolster’s threat research team reported on a widespread phishing campaign targeting popular retail brands to trick unsuspecting victims into purchasing on fake sites. This data clearly highlights the importance of securing ecommerce stores against phishing attacks.
In some cases, websites are compromised to serve phishing landing pages to harvest sensitive information. But in other cases, bad actors are known to send reputable-looking emails or messages from popular websites in an attempt to coerce victims into revealing account login information. From there, criminals can access shopper accounts, modify personal information, or carry out fraudulent transactions. They may even sell stolen data on the dark web.
Furthermore, account takeovers can severely damage an ecommerce shop’s reputation and brand. Like Magecart malware, phishing attacks can result in chargebacks, fraud, and PCI compliance issues. They can even lead to the inability to accept credit card information.
SocGholish (Fake Browser Updates)
Back in 2022, we shared information about the ongoing NDSW/NDSX malware campaign which has been one of the most common website infections detected and cleaned by our remediation team this year.
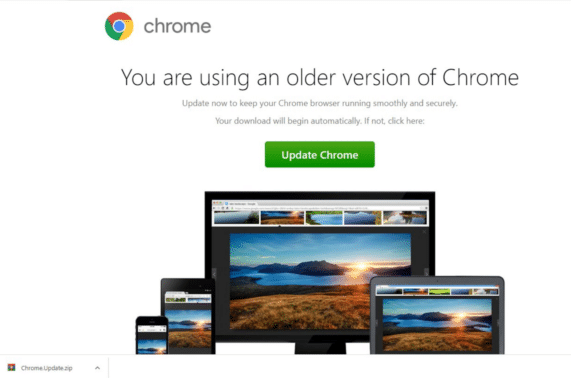
Also referred to as FakeUpdates or SocGholish, this malware redirects site visitors to web pages designed to trick victims into loading and installing fake browser updates like the one seen below.
We’re now eleven months into the year and our remote website scanner SiteCheck has already detected SocGholish malware on over 100,000 sites since the beginning of January, 2023.
And while it may seem unusual for attackers to target a webstore with fake browser updates when it’s possible to steal credit card details, the results of an infection can be quite lucrative for hackers.
Even just a single piece of injected JavaScript code can lead to downloading and installing malware, including remote access trojans and information stealers that harvest credentials from crypto wallets, social media, and online bank accounts.
Supply Chain Attacks
Supply chain attacks are known to specifically target trusted vendors who offer software or services. These attacks inject malicious code in an attempt to infect all users of the service or application.
Magento store owners using the popular FishPig extension were subject to a supply chain attack which compromised their software repository. Hackers leveraged this attack to infect targeted systems with Rekoobe Linux remote access trojan malware.
Supply chain attacks like these aren’t limited only to Magento CMS, however. In 2022, a massive supply chain attack led 93 WordPress plugins and themes to contain a malicious backdoor, granting bad actors full access to websites.
Of the four techniques used to inject malicious code, three are performed through supply chains. And since most modern websites use third-party APIs, open source or proprietary code, or maintain other third party dependencies, they can be affected by supply chain attacks like these ones.
Fake DDoS Verification Pages & Drive-By Downloads
WAF and CDN services regularly offer DDoS protection pages that perform browser checks to verify if traffic belongs to a site visitor or DDoS attack.
However, since August our team has seen a surge in JavaScript injections targeting WordPress websites to serve fake CloudFlare DDoS prompts that lead victims to download remote access trojans.

SiteCheck scan data reveals a total of 1,555 websites infected with this malware so far this year. The majority of these detections were for WordPress websites, some of which use WooCommerce for their webstores.
Furthermore, the campaign has recently evolved with new exploitation and obfuscation techniques. Newer variants have been found appending malicious JavaScript into WordPress core, theme, and plugin files.
Software Vulnerabilities
Attackers are always on the hunt for vulnerable websites using out-of-date plugins, themes, or other software. As seen in our yearly hacked report, software vulnerabilities are one of the leading causes of infection. Hackers use automated scripts to scan the internet for any unpatched websites, then launch targeted attacks against victims.
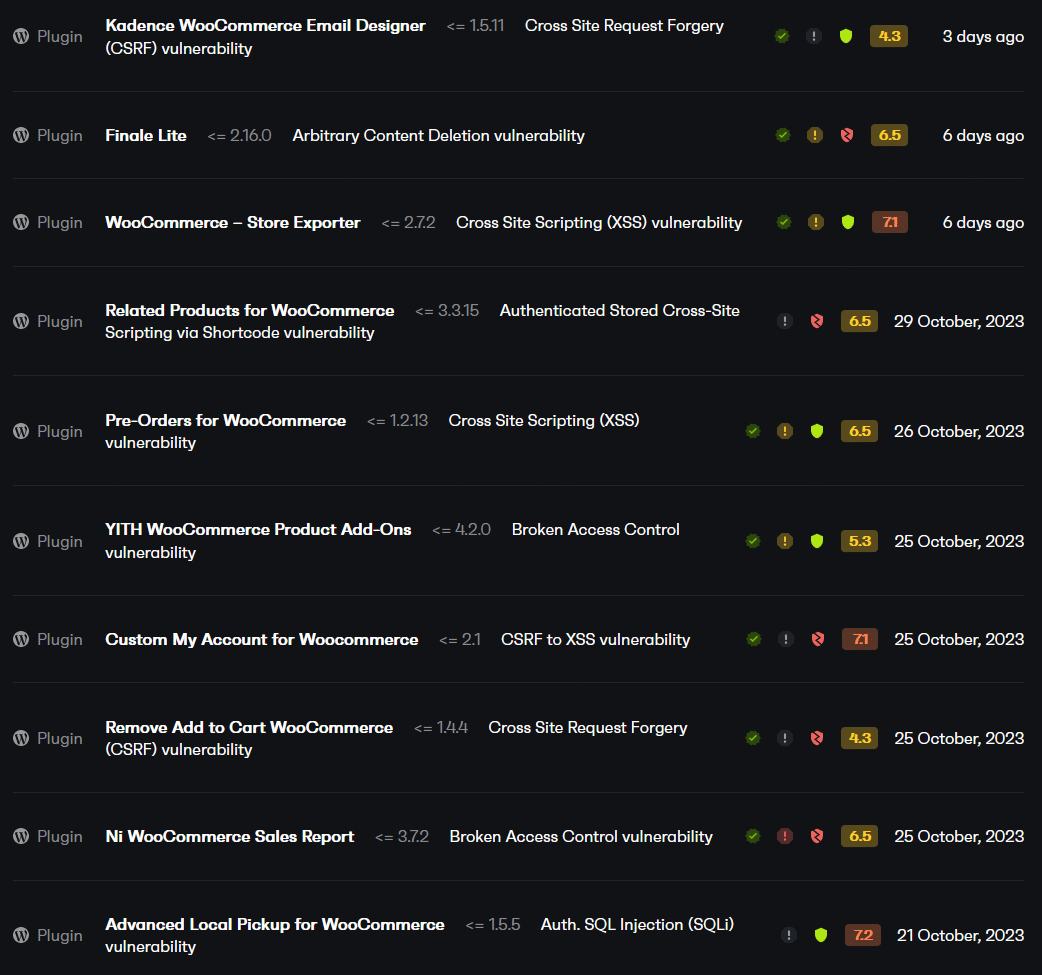
Let’s take a look at some of the most prevalent vulnerabilities facing ecommerce stores this holiday season.
WordPress & WooCommerce
With over 17% of webshops powered by WooCommerce, this easy-to-use solution has a far larger market share than other popular ecommerce platforms like Magento (9%).
Web store owners can find a plethora of WooCommerce plugins to enhance the shopping experience. But each one that’s installed on the environment increases the potential attack surface if left unpatched from known vulnerabilities.
Some common types of vulnerabilities affecting WordPress plugins include:
- Cross-site scripting (XSS)
- SQL injection (SQLi)
- Cross-site request forgery
- PHP object injection
- File deletion
- Sensitive data exposure
Developers are regularly releasing updates to patch known vulnerabilities in plugins. But when administrators don’t apply them in a speedy manner, the result can lead to infection. This is why patching your software with the latest updates is critical to mitigating risk.
Magento
On October 10th, 2023, Adobe released a security update for their Adobe Commerce and Magento Open Source platforms.
https://twitter.com/AdobeCommerce/status/1714280175293379030
A total of nine vulnerabilities were patched in this latest update, including a fix to resolve critical improper input validation, improper authorization, and stored cross-site scripting vulnerabilities.
Patching your ecommerce website software to the latest version is the most effective way to mitigate risk for these security threats and issues related to known vulnerabilities.
How to protect your ecommerce website from threats
More customers than ever are shopping online in the comfort of their own homes. So, protecting users from malware is essential for maintaining trust and PCI compliance for your online store.
Here are six steps you can take to protect your ecommerce store from security threats this holiday shopping season:
- Perform regular updates to your website software, plugins, themes, and other components.
- Enforce strong passwords for all of your FTP, database, and login credentials.
- Monitor and analyze your website and server logs for any indicators of compromise.
- Use a web application firewall to virtually patch known vulnerabilities and block brute force attacks.
- Avoid downloading or installing software from unofficial sources.
- Use multi-factor authentication or restrict access to admin pages to add extra layers of security.
If you believe your online store has been hacked or you want a hand protecting it against Magecart and other malware, our experienced analysts are here 24/7/365 to help rapidly clean up website malware and protect your store from hackers.