If you want a faster WordPress site, caching belongs at the center of your performance plan. It reduces the work your server has to do and turns slow, dynamic page builds into quick, static responses. On many unoptimized sites, that shift alone can reduce several seconds off page loads when paired with other best practices. The trick isn’t whether to cache but how to pick the right caching approach for your site’s content, traffic, and infrastructure.
This guide walks you through the major caching layers available to WordPress, the trade‑offs of each option, a brief overview of the settings that matter most, and where caching fits alongside other optimization tactics.
What caching actually does
Every time a non‑cached WordPress page is requested, your server:
- Loads WordPress core and active plugins/themes.
- Queries content and options from MySQL.
- Executes PHP to build the page.
- Sends the final HTML (plus CSS/JS/assets) to the browser.
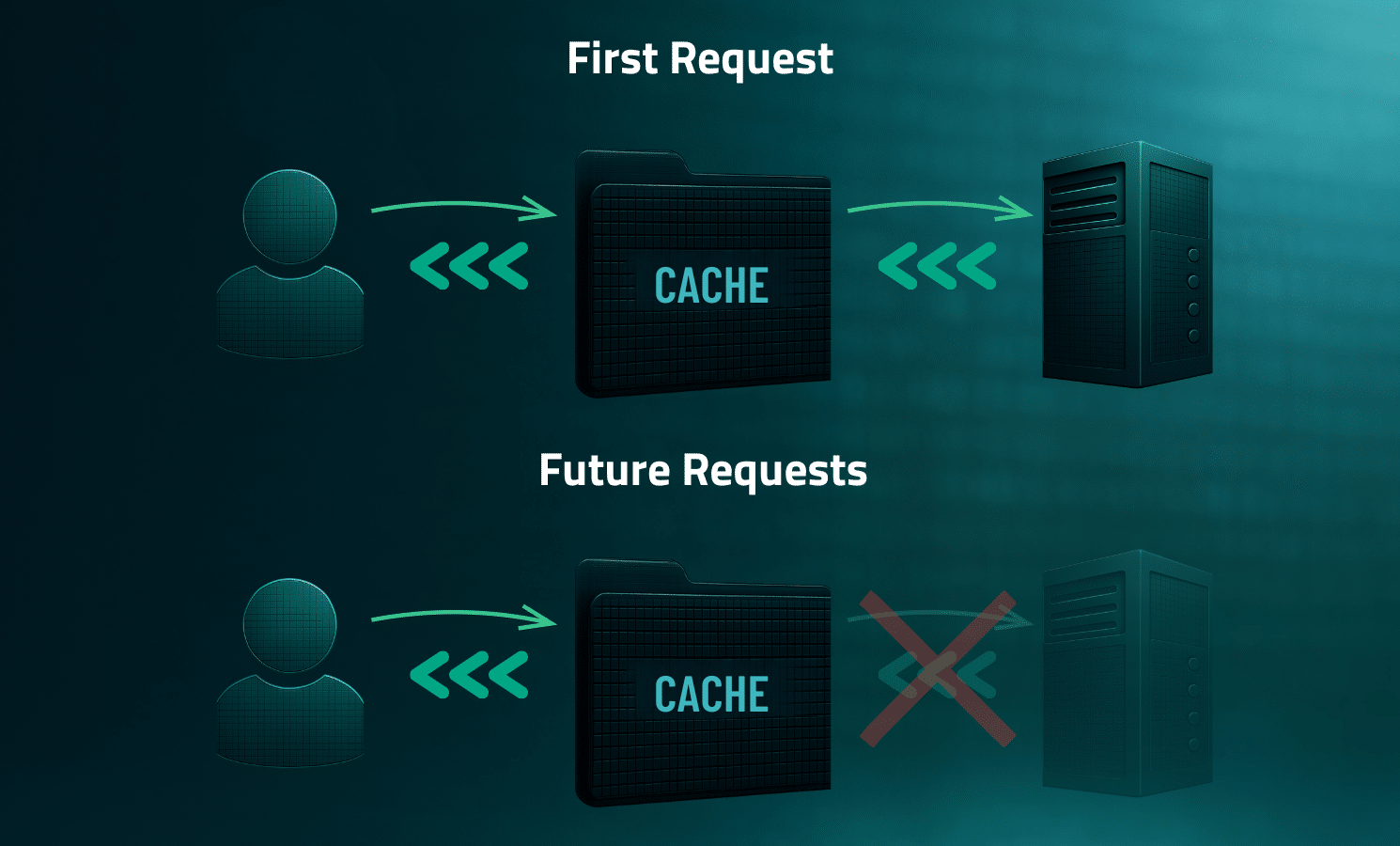
That full process repeats for every request, which is why it’s resource‑intensive. Page caching short‑circuits the heavy lifting by generating a static HTML copy the first time and serving that on subsequent visits. Most modern plugins can also work with a Content Delivery Network (CDN) so your cached pages are available from data centers near your visitors, reducing latency and helping with traffic spikes.
Key habit: When something significant changes (theme switch, plugin activation/deactivation, major design updates), clear your caches so visitors get the current version. Most plugins purge the cached copy when you update a post or page, but not every change triggers an automatic refresh, so “Clear All Cache” should still be part of your normal operations.
Performance goals and how caching helps
Caching supports, but does not replace, core performance work. It’s especially helpful for improving TTFB (Time to First Byte). By cutting origin processing time through caching retrieval, you’re providing a faster first byte and quicker render start.
It also applies to Google’s main Core Web Vitals:
- LCP (Largest Contentful Paint): Faster HTML delivery and CDN‑served assets often reduce LCP.
- INP (Interaction to Next Paint): Primarily affected by JavaScript; deferring non‑critical scripts can help.
- CLS (Cumulative Layout Shift): Caching can improve CLS indirectly; speeding up load times reduces the chance of layout shifts caused by late-loading elements.
Know your caching layers
While you don’t have to use every type, knowing what they do will help you choose wisely.
Page caching (server‑side)
Page caching is the most effective way to speed up a WordPress site by storing a static HTML version of a page. When a visitor requests a page, the server delivers the pre-generated HTML directly, bypassing the resource-intensive PHP processing and database queries of the standard WordPress execution. This results in significantly faster load times, dramatically reduced server load (improving scalability), and better SEO.
While caching can be implemented via WordPress plugins, the most efficient method is Host- or Server-Level Implementation (e.g., via NGINX or Varnish), where the cache is consulted before the request ever reaches the WordPress application for maximum performance.
Browser caching (client‑side)
Browser caching, or client-side caching, is a performance optimization technique where a web server instructs a visitor’s browser (via HTTP headers like Cache-Control and Expires) to save local copies of static assets (CSS, JS, images, etc.) for a specific time. This mechanism eliminates the need for repeat downloads when the visitor revisits the site, resulting in faster page load times for returning users, reduced server load, and an improved overall user experience.
Control is managed server-side through cache headers, with revalidation handled by ETag and Last-Modified. In a WordPress environment, these settings are typically managed using caching plugins, host-level optimizations, or direct configuration file modifications.
CDN/edge caching
A Content Delivery Network (CDN) is a geographically distributed network of edge servers (PoPs) that fundamentally improves website performance and reliability. Its primary functions include:
- Global Content Distribution by caching static and sometimes dynamic assets on edge servers closest to the user.
- Optimizing Performance (TTFB) by reducing latency for global audiences.
- Managing Traffic by acting as a buffer to cushion against sudden spikes and prevent the origin server from being overwhelmed.
- Enhance Security and Reliability through integrated features like WAFs and DDoS mitigation at the network edge.
Database (object) caching
Object caching involves storing the results of complex and frequently repeated database queries in memory. Its core benefit is dramatically reducing the load on the database server and significantly accelerating data retrieval time, which speeds up page rendering.
Object caching is most beneficial for highly dynamic and complex websites like large e-commerce stores (WooCommerce), membership sites, forums, and high-traffic news portals that generate heavy database interactions. Implementation typically uses specialized, persistent, in-memory systems like Redis or Memcached, requiring server-side configuration and integration via a dedicated WordPress plugin.
Opcode caching
Opcode caching is a server-side optimization that dramatically speeds up PHP applications like WordPress. When a PHP script runs, the human-readable code is compiled into lower-level “opcode” or “bytecode.” An opcode cache (most commonly OPcache) stores this compiled bytecode in memory after the first execution. This bypasses the time-consuming compilation step on subsequent requests, leading to a near-instantaneous speedup.
This process operates at a low, system-wide level, making it a foundational performance boost managed by the hosting environment or server administrator, and is not a setting a WordPress user manages via a site-specific plugin.
Start with your site’s constraints
Before choosing a tool, map your site’s behavior:
- Content type: Mostly static pages/posts vs. dynamic features (carts, dashboards, membership portals).
- Logged‑in traffic: High proportions of authenticated users often need different caching rules.
- Commerce: WooCommerce stores must exclude cart, checkout, and account pages from page caching. Widgets that show cart or order details should be excluded too to avoid inaccurate states.
- Team workflow: How often does content change? Who needs to purge caches, and when?
- Hosting platform: Do you have host‑level caching already? Some providers forbid additional caching plugins to avoid conflicts.
Host‑level/server caching
Many managed WordPress hosts provide caching at the server or reverse‑proxy layer.
Key Advantages:
- Tuned to the stack: Hosts can align cache rules, storage, and purging to their infrastructure for reliable performance.
- Simplicity: No plugin to maintain; fewer knobs to turn.
Trade‑offs:
- Limited customization: Advanced users may feel constrained by “one‑click” setups.
- Troubleshooting friction: You may rely on support to adjust rules or diagnose conflicts.
Lean into these solutions when you prefer simplicity, your host is stable, and your site isn’t a special case that needs granular rules. Keep in mind, your host may prohibit additional caching plugins, so it’s best to follow their guidance to avoid conflicts.
WordPress caching plugins
Caching plugins give you control and often bundle extra performance features (e.g., database cleanup, minification/aggregation, deferring JavaScript, removing unused CSS). Dedicated tools can sometimes outperform “all‑in‑one” features. For example, WP‑Optimize focuses on database cleanup, while Autoptimize is popular for aggregating/minifying CSS/JS/HTML.
If you want granular control (exclusions, separate mobile cache, preload behavior, purging strategy) or your host doesn’t include caching, plugins can provide the tools you need and also make it easy to integrate with a CDN.
Golden rule: Use only one caching plugin at a time. Running multiple caching plugins won’t make your site faster and can lead to issues.
CDN/edge caching
A CDN caches and serves content from locations closer to your visitors. Most caching plugins can connect to a CDN and add proper headers. CDN caching shines when:
- Your audience is globally distributed.
- You experience traffic surges (e.g., promotions, press).
- You want lower TTFB and fewer origin hits.
Pair page caching (at origin) with CDN caching for the best end‑to‑end results.
A repeatable testing workflow
1) Measure a baseline
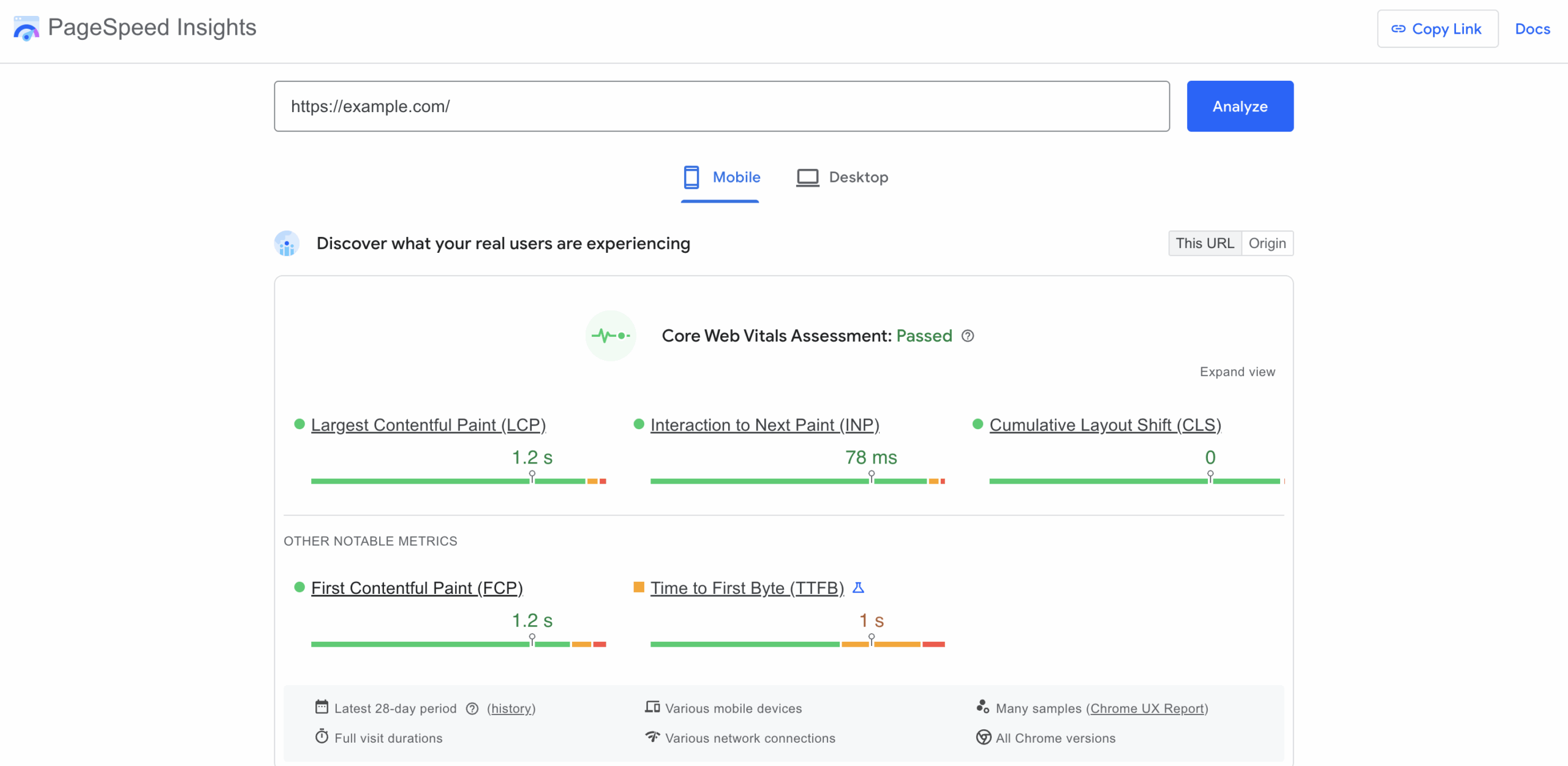
Use PageSpeed Insights (both mobile and desktop) for field/lab data and Core Web Vitals. Record TTFB, the Core Web Vitals discussed earlier (LCP, INP, CLS), and page size/requests.
2) Enable caching in stages
A phased approach is recommended for enabling caching to ensure stability and minimize risks:
- Prioritize Page Caching: Enable fundamental page caching (HTML output) first for the most immediate and significant performance gain, reducing PHP and database load.
- Implement Browser Cache Headers: Add client-side headers (Expires, Cache-Control) to instruct visitors’ browsers to store static assets (images, CSS, JS) locally, speeding up repeat visits.
- Introduce CDN/Edge Caching: Layer in a Content Delivery Network for global distribution, serving content from the nearest server (PoP) to reduce latency and provide defense against traffic spikes.
- Layer in Performance Optimizations: In the final stage, carefully introduce advanced, higher-risk optimizations like Deferring JavaScript, Minifying Code, and implementing Critical Path CSS (removing unused CSS) after thorough testing.
3) Verify functionality
Verify functionality by testing:
- Authentication States (Login/Logout): Verify users can log in and out correctly, and that personalized, logged-in experiences are never cached for general visitors.
- Interactive Elements and Forms: Test all forms (contact, subscription, comments, etc.) to confirm they submit successfully and correctly bypass the cache to prevent security or submission errors.
- Site Search Functionality: Perform various searches to ensure the results are dynamic, accurate, and not being served from a stale cache.
- E-commerce (If Applicable): Critically test the shopping cart, checkout, and account pages, which must be excluded from caching, by adding, modifying, and ordering items.
- Content Freshness and Cache Purging: Check that new or updated content appears immediately after publishing. If not, verify that the manual cache purge routine reliably clears the cache to display the fresh content.
4) Re‑measure and compare
Expect the biggest gains from page + CDN caching. Use real-user monitoring where available to confirm improvements for your audience and geographies.
When you should or should not cache
Is your host already caching pages?
If so, start there. Ask your host how to purge, how exclusions are handled, and whether a plugin is allowed for fine‑tuning. Avoid overlapping features that duplicate what the host already does.
Do you run WooCommerce or other dynamic features?
Exclude cart, checkout, and account pages and any AJAX/cart fragments or widgets that display per‑user data. Keep page caching for category and product pages where appropriate.
Is a large portion of traffic logged in?
Consider bypassing page cache for logged‑in users or enabling a “separate cache for logged‑in users” if your plugin/stack supports it. Keep object/opcode caching on the server for repetitive operations.
Do you have a global audience?
Add a CDN and enable edge caching of static assets and HTML where safe. Verify your purge workflow clears both origin and CDN caches after updates.
How often do you publish or change design?
Set sensible cache TTLs (time‑to‑live) and use preload/warmup so important pages are cached before the next visit. Build “Clear All Cache” into your release checklist after major updates.
Common issues and FAQ
Q: Why does my page show old content after an update?
Why it happens: A stale cache at the origin server or CDN.
How to fix it: Purge the cached version of the page. If you changed global elements (menus, header, templates), clear all caches (both origin and CDN).
Q: Why do forms or widgets stop working after enabling “defer JS”
Why it happens: A critical script is being delayed.
How to fix it: Exclude the affected script(s) or the specific page(s) from your defer/delay rules.
Q: How come product prices or cart counts are wrong?
Why it happens: Dynamic fragments are being served from page cache.
How to fix it: Exclude WooCommerce cart, checkout, and account pages from page caching, along with cart/AJAX fragments or any relevant cookies used to personalize the view.
Q: Why does my host say “no caching plugins allowed”
Why it happens: Often, this is due to your provider already running server‑level caching and attempting to avoid conflicts.
How to fix it: Use the host’s built‑in caching and follow their purge/exclusion guidance. Disable overlapping plugin features that duplicate the host’s cache.
Q: What should I do if visitors see outdated images or CSS?
Why it happens: Browsers or the CDN are still serving cached assets.
How to fix it: Purge caches at both the origin and CDN. Make sure your deployment checklist includes a full cache clear after theme or asset changes.
Final wrap‑up
Caching is one of the most effective, low‑friction ways to accelerate WordPress. It reduces server work, lowers TTFB, and when paired with solid optimization practices, helps deliver the fast, stable experience search engines and users expect. If you’re weighing host‑level caching against plugins and CDN options, pick the least complex stack that gives you precise control over exclusions and purging. Then test, verify, and iterate. Do that, and you’ll unlock the bulk of the gains available to most WordPress sites and begin shrinking those load times.