As a child, did you ever play that game where you sit in a circle and one person is responsible for whispering something into one persons ear, and that message gets relayed around the circle? Wasn’t it always funny to see what the final message received would be? Oh and how it would have morphed as it was processed and conveyed by each individual in the group.
This is what I see when I look at the WordPress Security Ecosystem.
The biggest challenge the ecosystem faces is product and service confusion. This is compounded by a variety of factors. I often categorize them, generally into two buckets – deliberate and non-deliberate confusion. For me deliberate product confusion comes often by marketeers and those looking to make a quick buck on what they perceive to be the next virtual gold rush. While non-deliberate confusion is introduced by those that mean well, or were once affected, and have come up with a genuine solution that likely addresses a very narrow issue.
An easy way to better appreciate this is to look at the WordPress Security Plugins specifically, as they’re tangible and that makes it easier to truly appreciate the nuances of the security space.
Contrary to popular belief, not all plugins are the same or created equal and you can’t compare them as that would not be an apples to apples comparison.
Interestingly enough, there are often pretty unique differentiating factors between each of the security plugins in the market, although in many cases there are one to one correlations. Human nature is also one of the contributing factors to confusion. As humans we are often configured to go the easiest route. We’re always looking for the one with the biggest audience, or the one that is pushed on us the most. If everyone else is using it, I should too. Rarely do we truly understand or give much thought to this phenomena.
The WordPress Security Plugin Ecosystem
If you were to go to the WordPress repository and do a quick search for Security you will likely find over 2,471 plugins that all have some keyword associated with Security. When writing this post, there were 33,213 plugins in the repo; that’s roughly 7% of the available plugins in the repo. If you do a search on google for WordPress Security Plugin you will find somewhere upward of 7,230,000 results on the topic.
How is any WordPress user supposed to make sense of this?
Below I will introduce four distinct categories I want you to think about when considering a WordPress Security Plugin. If you can leverage these categories, it will hopefully:
- Allow you to ask better questions.
- Employ the right solution for your needs.
- Provide better clarity into the tools you’re employing.
WordPress Security Plugin Categories
First we have to understand the type of plugins that exist. Yes, there is a very distinct categorization within the security domain, and each of the plugins fit into one domain predominantly, some are multi-faceted, overlapping other domains, but few actually do this well.
If I label a security plugin below in a specific category it’s because from my tests and reviews it’s where I see it fit. It doesn’t mean that the developer would not like it to fit in others, I just felt it was most effective where I place it. It also doesn’t mean that it won’t satisfy your specific situation. My writing is more general and is meant to address security as a whole, not specific configurations.
Here is a breakdown of the WordPress Security Plugin categories:

To understand this categorization you have to understand the Information Security wheel. The common wheel has always been defined by Protection, Detection, and Response. For Websites, and WordPress specifically I am extending it to include functions that large enterprise recognize and account for, but everyday website owners don’t. It’s such a problem, it deserves special attention.
Our categorizations are based on this model:
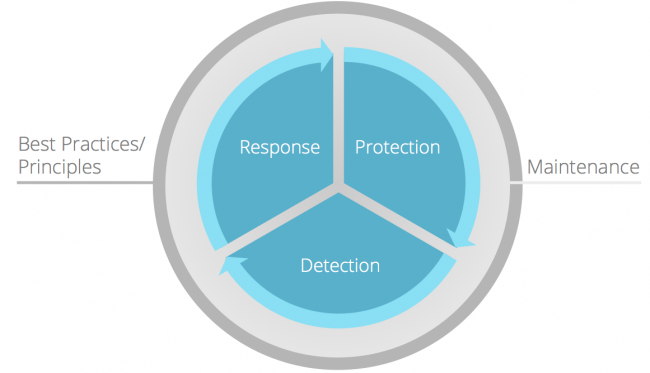
As I mentioned before, rarely do you have one single plugin that satisfies all aspects of security. It is imperative you understand this as a website owner. Understanding the security lifecycle helps you answer the question – which WordPress Security plugin am I looking for?
WordPress Security Plugin – Prevention Category
These plugins look to provide some level of prevention, otherwise known as a perimeter defense for your website. Their objective is to stop hacks from happening. The buzz word today is Website Firewall. It’s the idea that you can function as a filter of sorts for all incoming traffic to your website. The concept of firewalls is not new, they’ve been employed for years across the IT spectrum. Almost all the routers you are using to read this blog are employing some form of a firewall.
The biggest weakness you will find with these type of plugins is they are often 1) behind the power curve and 2) are limited to working at the application layer. In other words, the attack has to hit the server for them to respond.
There are a few plugins that like to employ the terminology of a Website Firewall, but are far from it. Others actually function very well. The BlogVault team put together a very good article on this subject a few weeks back, they were focused on a different issue, but their point is good. The types of tests they ran were in fact indicative of the types of website attacks a Firewall should prevent.
This includes things like:
- Remote Command Execution
- Cross Site Scripting
- Remote File Inclusion / Local File Inclusion Attacks
- Exploitation of Software Vulnerabilities
- Denial of Service (DoS)
- Brute Force Attempts
Why these are so important to you as the end-user is best illustrated in some of the latest WordPress Plugin Security disclosures, like the Slider Revolution Plugin, Custom Contact Forms Plugin, MailPoet Newsletter Plugin, or the recent abuse of XMLRPC in WordPress core.
What you will see, however, is this evolution in these plugins leveraging a concept of Virtual Patching. In short, as these disclosures get released, the plugin developers will scurry to push out a plugin update and say that you are now patched and protected.
The big thing you hear these days is specific to Brute Force protection. In the past the big solution was the Limit Logins plugin, now it’s a staple in almost every security plugin with the exception of Sucuri’s (we’ve removed it from ours). You then saw really great tools like BruteProtect, which was then acquired by Automattic, and will likely be pushed for free to all JetPack users. You also have a variety of others like iThemes Security, WordFence, Login Security Solutions and so many more that are trying to tackle this Brute Force challenge.
However, this should not be confused with what we categorize as an effective prevention plugin. This hyper focus on one very small attack vector provides a very false sense of security to most end-users. It’s why we don’t focus on that specific feature of a prevention security plugin.
WordPress Security Plugin – Detection Category
The act of Detection has always been the red-headed step child of security, not just in WordPress but in Security at large. It never gets the attention it deserves, and often the response is, “If I am protecting, why do I need to be detecting?” The answer is actually simpler than most realize, yet many refuse to accept it.
Protection is not a 100% solution, it never has been, and never will be. Imagine a world where your Home or Company Firewall was 100%, why would you need an AntiVirus product?
Protection is great for the known issues, and not so great for the unknown issues. What we all know, or should, is that with enough time and resources, crackers have the ability to find new points of entry (i.e., identify new attack vectors). This is where things like Detection come into play. While we have the utmost confidence in our ability to protect, we still want to ensure we have a mechanism available to use to detect in the event anything gets past our perimeter defense.
These plugins attempt to do this. They do it via a number of mechanisms, some do traditional File Integrity Checks, some do malware scans, some combine the two. As for which one is better? It just depends. The person that used one plugin and used it to detect their one infection will jump over mountains to say how awesome that one is. The one that used another and was successful with that one will likely do the same thing. It starts to come down to who has the bigger audience and the bigger evangelists.
You will find some that are free, and some that are not so free. Some are fully automated, and some are supported by humans. Where these plugins often become the big hits is if they are able to satisfy your immediate problem, specifically the problem being that you are infected.
What you have to remember is that there are many different types of infection and symptoms to account for. Do you fit any of these symptoms?
- Google, Yahoo, Bing have Blacklisted your website
- Clients are complaining that your website is being flagged by their AntiVirus
- Your host has disabled your website because of a Security issue
- Google / Bing search is showing Viagra, Levitra or other Pharmaceutical ads in the search results
- You are plagued with reinfections
- You see “This site is Hacked” or “This site may be compromised” on Google search
- People are complaining that your website is redirecting on their mobile devices, notebooks, desktops
- Something just feels off – you’re seeing weird activity, things are popping up or just want a second pair of eyes
These are just a small subset of issues that Detection plugins that exist today will do little to address, but are imperative to you as a website owner. Remember also that the effectiveness of these plugins is strictly determined by the order in which they are installed.
For instance, if the plugin is based on integrity checks, then it needs to be installed on a fresh install so that it can create a baseline to which to check from.
This category can also be extended to account for what are known as Vulnerability scanners, but with these you have to be very careful. Very few vulnerability scanners actually do vulnerability scans. Many will simply look for versions of themes and plugins that have known issues, and use their plugin to identify if you have it installed. Those that do try to scan for real vulnerabilities live are often ineffective because vulnerability scanning isn’t just about the code, it’s about stress testing as well. The tool is meant to be part of a process.
More often than not, I recommend non-tech / non-dev users stay clear of vulnerability scanners. They often generate a lot of noise and when it comes down to it, you really have no idea what to do next. It causes more headaches than you will want to deal with.
WordPress Security Plugin – Auditing Category
If Detection is the red-headed step-child, then Auditing is the Foster kid that no one wants. It’s the harsh reality. We live in a time where everything is supposed to be easy. You install this plugin and you have a carousel. You install this plugin and all your posts go to all your favorite social outlets. What’s this thing about auditing? You mean I have to actually actively monitor my websites activity, like really administer the website?
The answer is a resounding YES.
Contrary to popular belief, security is, fortunately or unfortunately, not a set it and forget it kind of thing. You have to invest time into the process. Get acclimated with what is going on, who is logging in, what is changing, when are they changing…
As the administrator of your website you should be asking questions like:
- Who is logging in?
- Should they be logging in?
- Why are they changing that post?
- Why are they logging in when they should be sleeping?
- Who installed that plugin?
What many don’t realize is that through basic administration, like auditing, you can sometimes achieve greater success in identifying, thwarting or responding to a compromise.
Food for thought.
WordPress Security Plugin – Utility Category
This is perhaps the widest bucket of security plugins, and the one that most of you reading this post likely employ. It’s perhaps the most diverse bucket of the entire WordPress Security Plugin ecosystem. There are only a few big ones that stick out, and few specific plugins that can be easily wrapped into this category.
We also reserve this category for toolsets like Backups or Maintenance plugins that address specific security functions. Think plugins that allow you to create backups, store locally or remotely, or plugins that allow you to administer and manage your website remotely. This of course is one small subcategory within this group.
The biggest plugins in this category are those we consider to be the swiss army knives of the security landscape. These plugins can be exhaustive in their security configuration options. They have every possible configuration you could or might ever want to employ. These plugins are not for the faint of heart.
I like to categorize these plugins as the Do It Yourself (DIY) security plugin, similar to those TV shows that my wife adores. You know, the ones where couples try to refurbish a house or landscape their backyard. Think of these plugins as your hardware store, or your very fancy toolbox; for the everyday user they will likely cause more issues than they are worth, but for the active administrator it might be the thing you have been looking for.
Especially in the WordPress community, built by those that love to tinker, these suites fall into that same user mindset. If there is something you want to do, but don’t want to it manually, it’s likely that one of these swiss-army knives of the WordPress Security Plugin ecosystem will enable you to do it. If it doesn’t, I can assure you they’d love to know what it is so that they can add it as a feature.
Which is Better For Your WordPress Security?
This is undoubtedly the question that many are asking, and likely the only reason you have read this far. The harsh reality, though, is that there isn’t a clear answer and the best answer is always dependent on your specific scenario. I enjoy reading the hacked and malware forums on .org because it is never more blatantly obvious to me how disconnected we are when it comes to security.
Rarely do we truly understand the user’s issue. We simply regurgitate what we have heard, not from experience, but from what others have said. We are so apt to not promoting an effective solution, regardless of whether it’s actually good for the user, because of sensitivities, yet we forget what the end-user is going through. We would rather spend hours / days / weeks having them try 150 different things, than encourage them to employ something that could get them functioning quickly. This is not just reserved for the .org, but for various WordPress communities like Facebook, Twitter, etc…
What it comes down to is what kind of end-user are you? What state of mind are you in and what are you looking to accomplish?
Here are a few different personas, or audience types, that you might fall into, and depending which is applicable to you the guidance and insight will be slightly different.
Here are 7 different questions that you can ask yourself when looking for a WordPress Security Plugin. They are not meant to be the only questions, but likely the most common:
Your Security Persona Defines The Best Solution
1. Are you a business owner that only cares about your website running and don’t want anything to do with security?
If so, then you’re likely not going to want to leverage any of these plugins and should leave your security needs to professionals that can help you.
Yes, I link to our company, but there are alternatives. The point is, find a professional and employ them, and don’t look for the one that says they are an expert, look for the ones that have the appropriate experience.
I know how to change my oil, yet I still take it in every 3 / 5 months to have it taken care of. I value my time too much to waste it. I presume the same applies to you and your business.
2. Are you currently infected?
You want to stick with Detection plugins, one very interesting plugin that works well enough for the common issues is the Anti-Malware (Get Off Malicious Scripts). You can also make use of services like our SiteCheck Security Scanner and Unmaskparasites to scan your website for malware. I should also reference the WordFence plugin as a decent Detection plugin. It’s had its ups and downs in its detection in the past, and still has its limitations but for many of the common issues, it works fine (although be mindful of false positives and the resource impacts inherent to them).
3. Are you Blacklisted by Google, Yahoo, Bing or something similar?
None of these plugins are going to help you. You’ll want to leverage a professional service to 1) identify the problem and 2) resubmit your website for review. Or you can do it yourself.
4. Do you like to tinker and want the ability to configure everything you find on those “The 10 Things You Need to Do To Harden Your WordPress Website” blog posts?
Then you’re going to want to stick with Utility plugins. One of our favorites, and best maintained, will be the iThemes Security (formerly Better WP Security) plugin. Mind you, this plugin has a lot of options. If you don’t know what you’re doing, it’s likely not going to be for you, so proceed at your own will.
5. Are you looking to stop hackers from getting in?
Then you are looking for Prevention plugins. We generally don’t recommend Website Firewalls that operate at the application layer, for a variety of reasons. There are a few out there that leverage the name, but are likely providing you a false sense of security. We’d recommend you leverage a service based product for this. It can range from services like those at CloudFlare, Incapsula or Sucuri. Do your homework and research the one that you feel will be most effective.
The one caveat to this will be Brute Force protection. It’s important to take some time to understand what Brute Force attacks are, and how they differ from other types of attacks – like Denial of Service. As of late, there has been a lot of hollering across the inter webs on this new, yet very old, attack method. There were arguments at one point that network latency was too big of an issue for Brute Force attacks to be realistic or impactful. The times have obviously changed and that’s no longer the case.
It’s become such a big issue that you see everyone getting into the game. It will likely be the new security gold rush as everyone rushes to implement a solution for Brute Force attempts. As this happens, we’ll continue to see an evolution in the attack spectrum, a case in point would be the recent attacks on XMLRPC that allowed the user to Brute Force your application while bypassing your wp-admin. In this scenario, none of the security plugins protecting you from BF were addressing the issue, until disclosed. Allow me to be clear though, the fact that they can be updated to address the issue once identified is pretty good as well.
6. Do you want to know what is going on with your website at any given time??
Then you want to look at Auditing plugins. Our favorite is the Sucuri Security – Auditing, Malware Scanner and Hardening Plugin. Granted it’s a bit selfish, but rightfully so we think.
Good administration is critical to Good Security posture, and we all know that security is based on risk management. Where risk is reduced, our posture is increased.
7. Are you none of the above, and are only looking to improve your security posture?
Then the recommendation is to leverage a little bit from each domain. It’s ok to have multiple security plugins. Each, as you can see above, is designed to address different aspects of the security lifecycle.
The thing to remember, however, is that each of these plugins have one common denominator. They are tools designed to help you manage and administer your website better. They are not the end all be all when it comes to security. If there were such a thing, there would be only one solution.









6 comments
Well… the big problem with file integrity plugins is that if an attacker -or malware- access to your site, he can put some code to modify the DB erasing security alerts (or disabling notifications). Or he can just edit 1 line of the security plugin to bypass the scan, as in Sucuri plugin happens.
IMHO checking file integrity using plugins is an error; the checking process should be done from server tools.
Thank you for dedicating your time (in hours) writing this reasonable summary.
Very comprehensive overview. I really think end-users need to fully understand that securing their website should not be taken lightly. Unfortunately, security is often considered as an option and mandatory. On top of it, 7,230,000 results for security search, is simply misleading them. How many think they’re covered when they are not?
This is a great article. It is an important reminder that security is like any other system, and the old quality management system axiom — Plan-Do-Check-Act is relevant it maintaining a secure site. I’ve forward this article to all my client’s who are in the ‘Set-It — Forget It’ mindset. Thanks for all your hard work and sharing your insights.
Today I learned that you can apparently change your own oil?
All kidding aside, great article – thanks again, Tony!
Hi Tony, thank you for sharing this informative piece of work. Security for WordPress is something that not many care about, but it is very effective to protect against the vulnerability. You have comprehensively talked about a subject which is quite essential to be highlighted.
Comments are closed.