Website errors can be a real test of patience. One common culprit is the 502 bad gateway error. Known for its ubiquity across the web, it doesn’t discriminate between small WordPress sites or well-known services like Gmail, Twitter, or Instagram.
You may encounter a 502 Bad Gateway error when a server upstream (i.e. one closer to the website than the client’s end) either fails to receive a valid response from another server or encounters an issue while trying to fulfill a request. Although these errors are generally related to server-side issues, in some cases, they can be triggered by problems with internet connections or website elements stored on your browser.
In this article, we will dive into the nature of a 502 Bad Gateway error and its possible triggers. We’ll also provide a systematic approach to diagnosing and fixing the error to keep your website up and running.
Contents:
- What is a 502 Bad Gateway error?
- How does a 502 error differ from other 5xx errors?
- What triggers a 502 error?
- Can a 502 error impact SEO?
- How to fix a 502 error
What is a 502 Bad Gateway error?
A 502 Bad Gateway error is a server-side error that indicates one server, acting as a gateway or proxy, received an invalid response from another server upstream. This usually happens when a server (for example, a website’s host or CDN provider) is unable to forward the client’s request correctly.
502 Bad Gateway errors can present in an assortment of ways. Some of the common variations include:
- HTTP 502
- Error 502
- 502 Bad Gateway
- 502 Service Temporarily Overloaded
- HTTP Error 502 – Bad Gateway
- 502 Proxy Error
- 502 Server Error: The server encountered a temporary error and could not complete your request
- Temporary Error (502)
- 502. That’s an error
These are just a few examples of messages you might encounter with a 502 error. Many systems and website hosts even have their own custom error messages for 502.
How are 502 errors different from other 5xx errors?
To provide a clearer understanding of the differences between a 502 error and other types of server-side errors, we’ve compiled an overview of usual 5xx responses you might come across on your website.
| Server Error | Description |
| 500: Internal Server Error | This is a general catch-all error when no specific message is suitable. |
| 501: Not Implemented | The server doesn’t support the functionality required for the request. |
| 502: Bad Gateway | One server received an invalid response from another, upstream server. |
| 503: Service Unavailable | The server can’t handle the request, usually due to being overloaded. |
| 504: Gateway Timeout | One server didn’t receive a prompt answer from another server that it was accessing while attempting to load the web page. |
| 505: HTTP Version Not Supported | The server does not support the HTTP protocol version used in the request. |
| 507: Insufficient Storage | The server is unable to store the data needed to complete the request. |
| 508: Loop Detected | The server detected an infinite loop while processing a request with “Depth: infinity”. |
| 511: Network Authentication Required | The client needs to authenticate to gain network access; mainly used by network proxies. |
Each of these server-side errors provides specific information that can help you diagnose the problem and find a solution accordingly.
What triggers a 502 Bad Gateway error?
A 502 Bad Gateway error can occur for various reasons, such as problems with server configurations, network issues, problematic plugins or third-party applications, or firewall setup.
These issues are known to result in a 502 error:
- Unstable server. If the server takes too long to respond due to heavy loads or disturbances, a 502 error can occur.
- Network problems. Internet connectivity issues or difficulties connecting to an upstream server may result in a 502 error.
- Faulty programming. Errors in website code or configurations can often lead to a 502 error.
- Plugin conflicts. If a plugin in WordPress is incorrectly configured, conflicts with other plugins, or is compromised by malware, this can lead to 502 errors.
- Proxy server issues. Problems with proxy servers can result in a 502 bad gateway error.
- Firewall configuration issues. Your firewall could be erroneously identifying threats and consequently blocking certain internet service providers or IP addresses.
- Server software timeouts. If the server software doesn’t receive a timely response from an upstream server it refers to, this can trigger a 502 error.
- Incorrect DNS settings. If the domain name’s DNS records are incorrectly assigned, a 502 error may arise.
- Server capacity reached. The server may exhaust its available resources and crash, prompting a 502 error message. This could happen due to an unexpected surge in web traffic or constrained memory capacity.
- Issues with your browser. It’s possible that there might be corrupted files within your browser cache that are causing problems.
A 502 error creates problems by displaying a bad gateway message to users when they attempt to access specific areas of a website. This typically occurs when the server, acting as a gateway or proxy, receives an invalid response from an upstream server.
Can a 502 error impact SEO?
Yes – a persisting 502 error can negatively influence SEO if left unresolved. If a short downtime of say, 10 minutes occurs, and frequent crawling is happening, the crawler often retrieves the page from cache. In instances where Google hasn’t yet got the opportunity to re-crawl before the site is restored, your SEO is typically unaffected.
Nevertheless, if your site experiences extended downtime, such as over 12 hours, Google might perceive the persisting 502 error as a site issue needing resolution. This could unfavorably affect your rankings over time.
If recurring 502 errors concern you, it’s crucial to understand why they’re happening in the first place. Some of the subsequent solutions provided can help to troubleshoot and fix the issue.
How to fix a 502 error
A 502 bad gateway error often signals a network or server problem, but it can also be due to a client-side issue. Let’s explore various ways to fix this error and get your website running again.
1. Reload the web page
This is the most straightforward method to deal with a 502 bad gateway error. If your server or host is bombarded with simultaneous requests, it might temporarily be unable to handle the load, causing the error.
Reloading the page is as simple as clicking the “Refresh” button on your web browser or pushing the F5 key on your keyboard (for Windows users), or Cmd + R (for Mac users). Alternatively, some users prefer doing a hard refresh, which you can perform by hitting Ctrl + F5 (Windows) or Cmd + Shift + R (Mac).
Performing a hard refresh ignores cached content and forces the browser to reload the fresh page from the server. This process might take longer but could be more effective in bypassing the error.
When you receive a 502 bad gateway error, the issue might not be with your site directly. Instead, it could be a result of server overload. By waiting a few moments and then attempting to reload your page, you give the server time to catch up with all its ongoing requests.
However, if you’re continuously encountering a 502 error even after repeated attempts at reloading, it implies a deeper issue and you may need to move on to the next troubleshooting steps.
2. Assess the site’s status
When facing a 502 error, the issue can either be localized to your device or network, or it might be that the website or server itself is down. To differentiate between the two, you can use online tools that evaluate whether a website is actually experiencing issues.
One popular tool is https://geopeeker.com/. To use this tool, copy the URL of the website you are trying to access and paste it into the search box. Then, hit Go!
This tool then checks the site from various geographical locations to determine if the website is down universally or the problem is only on your end.
There are other online tools like isitdownrightnow.com and sitecheck.sucuri.net that work in a similar manner. These tools provide insights about the website’s operational status – and in the case of SiteCheck, may even help you identify a malware infection or security issue.
3. Access the page in incognito mode
When you use your browser in incognito or private mode, it doesn’t load your existing cookies, cached content, or run all extensions. Many times, these are elements that can cause issues with how a website is loaded. So, the 502 bad gateway error you’re experiencing may disappear in this mode.
To access incognito mode:
- In Google Chrome and Microsoft Edge, press Ctrl+Shift+N.
- In Mozilla Firefox and Safari, press Ctrl+Shift+P.
If loading the website in incognito mode solves the problem, then it’s likely a browser extension responsible for the error.
In such a case, you need to find out which extension is causing the problem:
- Return to your browser’s normal mode.
- Disable your extensions one by one. After disabling each extension, refresh the page to see if the problem still persists.
- If the website loads without the 502 error, you’ve identified the problematic extension.
You can typically manage extensions from your browser’s settings. For example, in Google Chrome, you click More Tools -> Extensions.
4. Clear your browser cache
Clearing your browser cache is a basic but effective troubleshooting strategy. Your browser stores temporary files on your computer to help quickly load webpages. However, these files sometimes lead to conflicts, including triggering a 502 error.
The process of clearing cache varies slightly with each browser. Below is a basic breakdown of the steps needed for popular browsers:
Google Chrome:
- Open your browser and click on the three dots in the top right-hand corner.
- Navigate to Settings > Privacy & Security.
- Click Clear browsing data.
- Ensure that Cached Web Content is checked.
- Choose the time range or select All time to clear everything, then click Clear data.
Mozilla Firefox:
- Click on the hamburger menu (three stacked lines) in the top right-hand corner.
- Go to Settings > Privacy & Security.
- In the Cookies and Site Data section, click Clear Data.
- Ensure that Cached Web Content is checked, then click Clear.
Safari:
- From the menu at the top, click Safari > Preferences.
- Click on the Advanced tab.
- Check the box that says Show Develop menu in menu bar.
- From the menu bar, click Develop > Empty Caches.
Microsoft Edge:
- Click the three horizontal dots at the top right of the browser.
- Click Settings > Privacy, search, and services.
- Under the Clear browsing data heading, click on Choose what to clear.
- Check the box next to Cached images and files, then hit Clear.
You can ensure that you are not seeing a cached page on the website by reloading the URL with an appended variable like this: example.com?nocache
5. Test the page with a different device
If your browser checks don’t indicate a problem, try switching to a different device. Sometimes, specific settings, extensions, or software on the device you’re using may cause conflict with the website you’re trying to access, leading to a 502 error.
You can choose another computer or a mobile device for this purpose. If you opt to use a mobile device, be sure to disconnect it from your Wi-Fi and use your mobile data instead. This action will bypass your usual internet connection and can sometimes solve your issue if the problem is related to your network configuration.
If using another device resolves the problem and allows you to access the website, there might be something on your original device that’s causing the interference. This could be a problematic browser extension, corrupted system files, specific security settings, or even malware.
In this case, restart your initial device and also reboot your networking equipment, like router or modem. The golden rule of tech troubleshooting is to unplug your device, wait for a few moments, and plug it in again. This simple reset can often clear up any temporary software glitch or memory issue that may be causing the problem.
6. Check for DNS problems
DNS, or Domain Name System, is what links your website’s domain name to its IP address. If there’s a problem with your DNS, this could cause a 502 error, as your domain may not be directing to the correct IP address.
There are several potential DNS issues that could cause this problem:
- The primary issue could be that your domain isn’t resolving to the correct IP address. This could occur if there has been a recent change or error in setting up your DNS records.
- You could be dealing with a non-responsive DNS server. The server responsible for translating your domain to the correct IP may be down or unavailable.
- If you’ve migrated your website to a new host, there can be a delay before your updated DNS records fully propagate across the internet. This delay could be up to 24 hours in some cases – depending on your DNS records’ Time to Live (TTL) value.
To fix these issues, here are some methods you could use:
- If you believe that your problems are due to recently changed DNS records, you may want to wait until the new records have had time to propagate.
- You might want to check your DNS settings in your domain registrar’s panel to ensure they’re correct.
- You could try flushing your local DNS cache – clearing old data and forcing your computer to get new, fresh data. If your computer has outdated or incorrect DNS information stored, this could cause a 502 error. In Windows, you can do this by opening Command Prompt and typing in ipconfig /flushdns. For macOS users, you can clear DNS cache by typing dscacheutil -flushcache in Terminal.
- Lastly, you might consider temporarily changing your DNS servers. By default, these servers are set by your Internet Service Provider (ISP). But there are also public DNS servers, such as those provided by Google, which can be used. Some people even choose to use Google’s public DNS servers permanently as propagation (the updating of DNS information across the internet) can be faster.
Keep in mind that solving DNS issues can sometimes be a bit technical, and you might opt to get professional help. If you’re unsure, reaching out to your domain registrar, web host, or a knowledgeable professional can be a wise decision.
If you’re using a WAF or CDN, be sure to check that the correct Origin IP is set. This would very much mimic the effect of having the wrong DNS A record set.
7. Check with your host
A potential culprit of the 502 bad gateway error could be an issue stemming from your web hosting service. This problem often occurs when a script, query, or request is taking an excessive amount of time to execute and is subsequently canceled or killed by the server.
This scenario typically occurs with shared hosting environments, where multiple websites are hosted on the same server. To maintain site performance and prevent one site from using all the server’s resources, these hosts often implement what’s known as a “kill script”. This script terminates a request that has been running for too long to avoid it impacting other websites on the same server.
Another reason for a 502 error could be server unavailability due to a downtime or connectivity issue. In such cases, it’s recommended to check your host’s status page or raise a support ticket to understand and resolve the problem.
8. Check your CDN or Firewall
Content Delivery Networks (CDN) and firewalls are common elements in web infrastructure designed to increase speed and security. However, they can occasionally interfere, leading to a 502 bad gateway error.
CDN:
A CDN is a globally distributed network of servers that provides faster delivery of your web content by serving it from the location nearest to your visitor. However, sometimes configurations or errors in a CDN can cause access issues, such as a 502 bad gateway error.
If you’re using a standalone CDN provider, try disabling it temporarily to test if it’s causing the problem. If the error doesn’t occur when the CDN is turned off, then the CDN might be at fault. You might need to delve into the CDN configurations or contact technical support for the CDN service to resolve the issue.
Firewall:
Similar to a CDN, a web application firewall (WAF) can also cause a 502 error. The firewall sits between the user’s network and server, examining web traffic for any malicious activity. If the firewall incorrectly blocks legitimate traffic, it might trigger a 502 error.
A firewall might also be configured to block certain types of requests that are perfectly valid for your website’s functioning. Any misconfigurations can result in a 502 error.
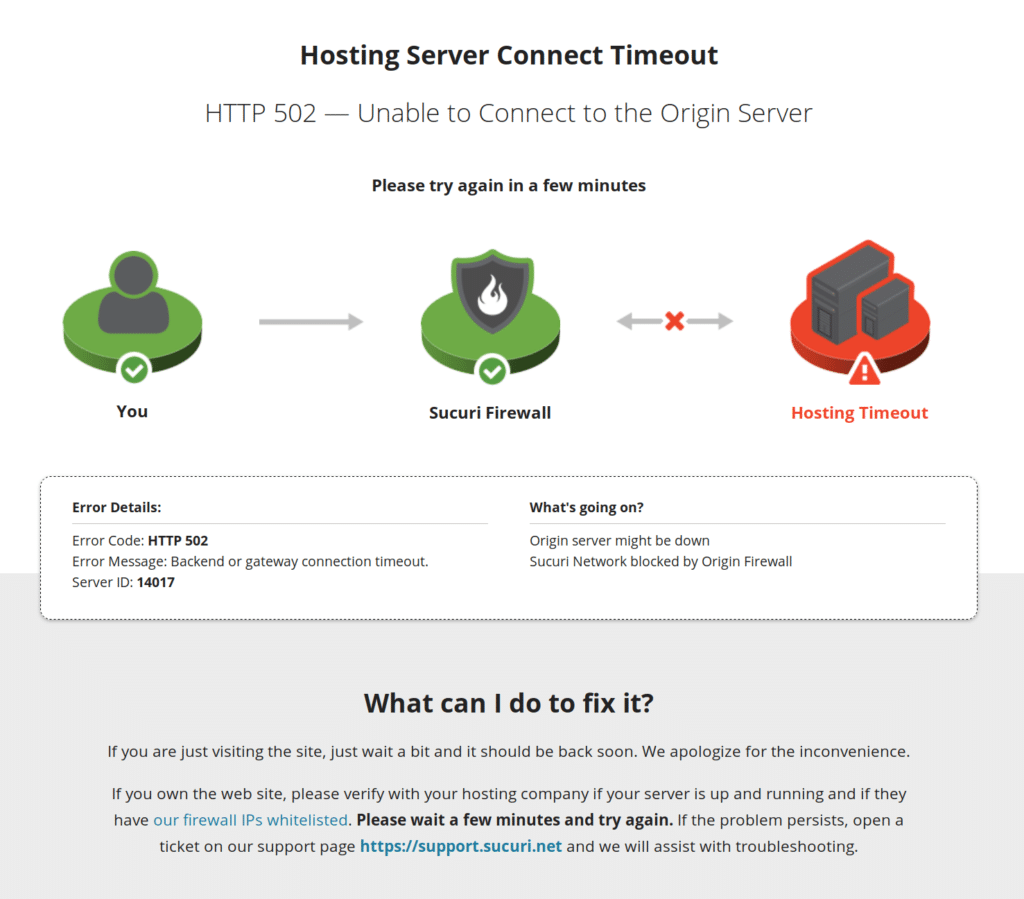
If you’re a Sucuri Firewall user and looking to troubleshoot a 502, try a firewall bypass and attempt to load the website again. If it loads successfully but you continue to receive 502’s, then either you need to set Hostname over TLS on the WAF security panel or your hosting server needs to allow the WAF IPs. But, there could also be some other issues such as the host header being too large.
How to bypass the firewall with hosts.txt
First, you must find and copy your hosting IP address by accessing the Hosting IP Address page of the WAF dashboard.
The next steps depend on your operating system.
Microsoft Windows
Follow these instructions to modify your hosts file in Windows.
- Press the Windows key, search for “notepad”, right-click on Notepad and select the option Run as administrator.
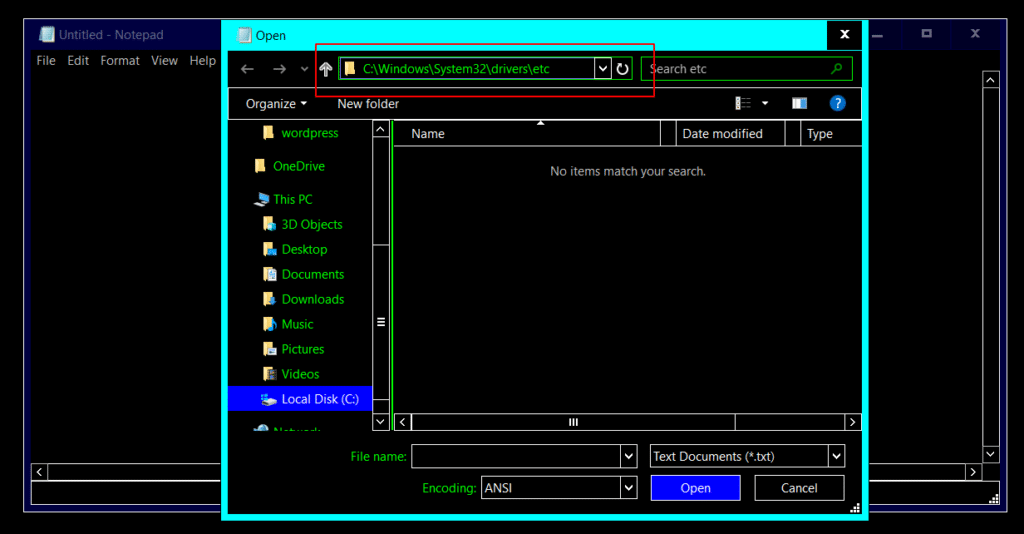
- Once the Notepad is open, go to File -> Open and type c:\windows\system32\drivers\etc on the path field. The “c:\” disk could be another letter, just make sure you’re accessing the primary disk of your system, which is usually where Windows was installed.
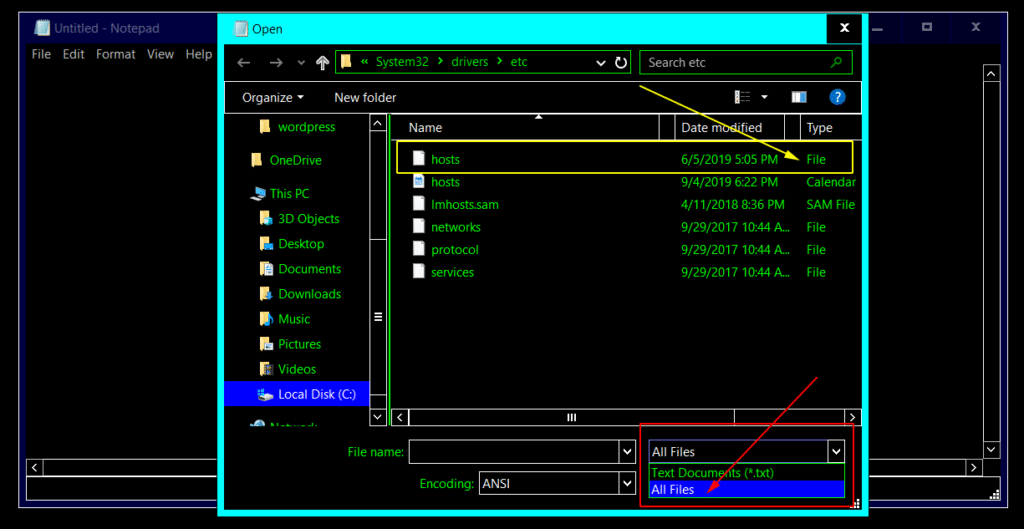
- The ‘hosts’ file won’t show right away because Notepad usually lists only text files, so you need to select “All Files” on the bottom of the window. Make sure you click on the ‘hosts’ file that shows as “File” on the Type column as there are two files named “hosts”.
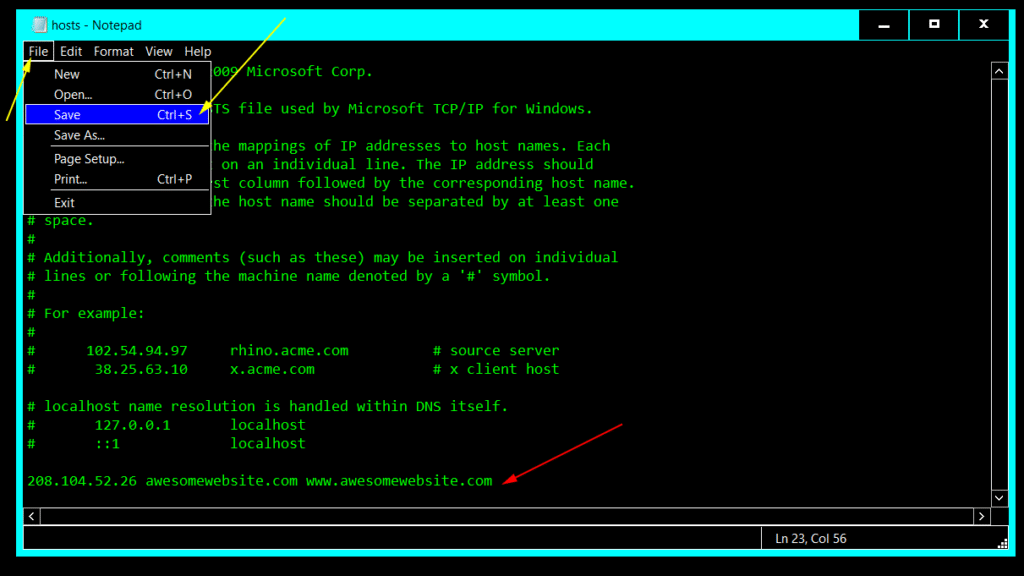
- At the very end of the file add a line following this structure:
208.104.52.26 www.awesomewebsite.com awesomewebsite.com
- Replace awesomewebsite.com with your domain and 208.104.52.26 with your hosting IP.
- Save the file and exit Notepad.
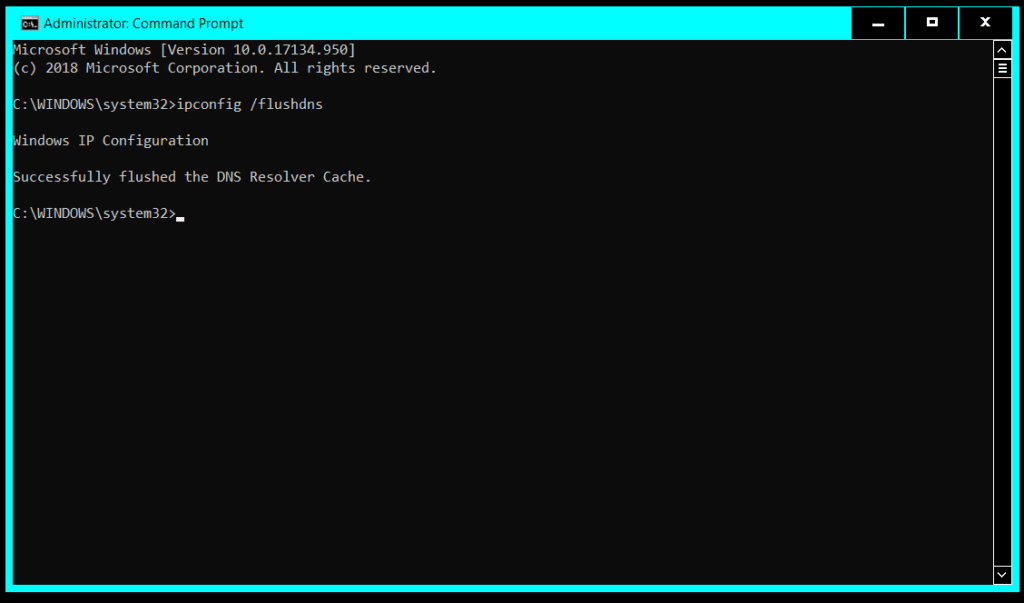
- Just like you did before to run Notepad as administrator, now search for cmd.exe on the Start Menu, right-click select the option Run as administrator.
- Type ipconfig /flushdns on the command prompt window and press “Enter” so the changes take effect. You can close the command prompt window after.
macOS & Linux
Follow these instructions to modify your hosts file in Mac and Linux.
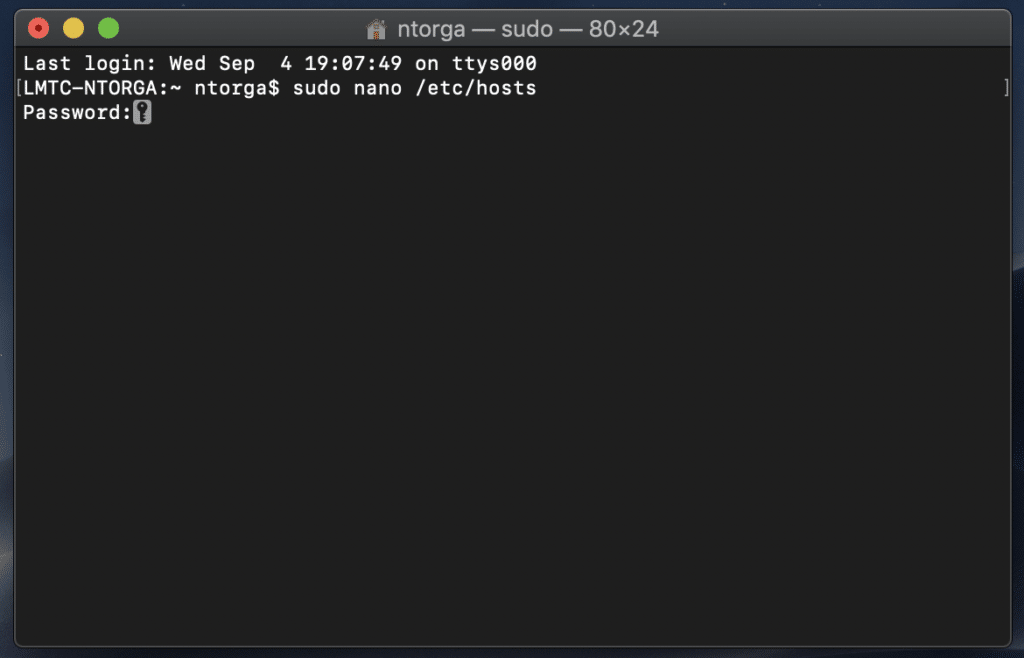
- Open the Terminal – if you are running a distro similar to Ubuntu, press Ctlr + Alt + T . On macOS, you can search on Spotlight or find the Terminal in the Applications -> Utilities folder.
- Type sudo nano /etc/hosts on the Terminal window and enter your password to open Nano Text Editor as root.
If you see Command ‘nano’ not found message, your Linux distribution may not have Nano Text Editor installed, therefore you can either choose a different editor such as Vim, Gedit, etc. You can also install Nano with your distribution package manager. If you are running a distro similar to Ubuntu, run the command sudo apt install nano on Terminal to install Nano Text Editor.
- At the very end of the file add a line following this structure:
208.104.52.26 www.awesomewebsite.com awesomewebsite.com
- Replace awesomewebsite.com with your domain and 208.104.52.26 with your hosting IP.
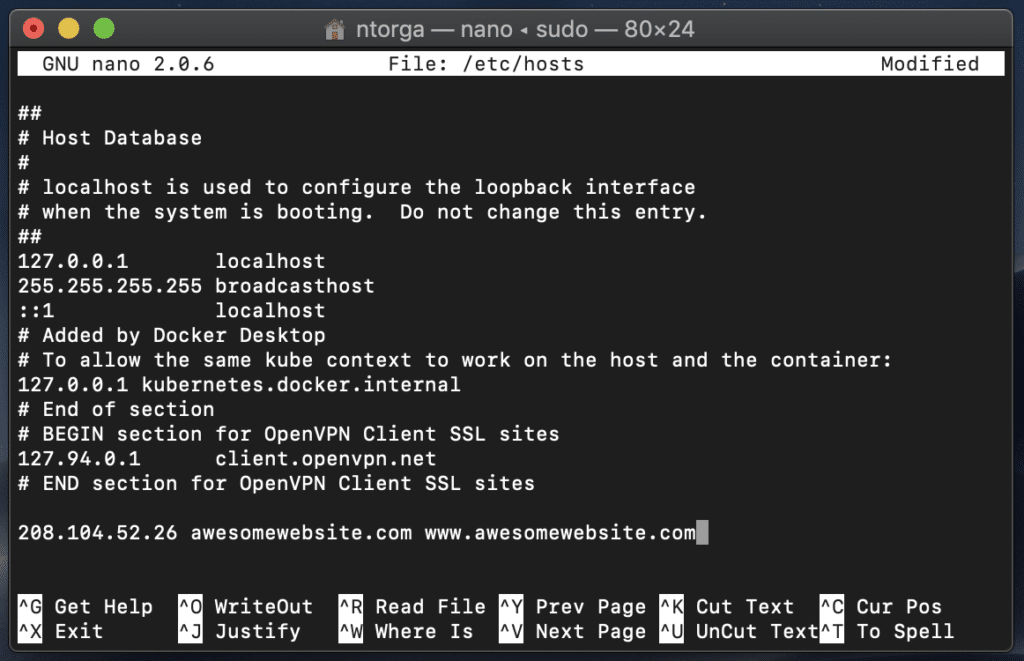
- Press “Ctrl + X“, then “Y” and then “Enter” to confirm saving the file with the same name.
That’s it. You should now be able to view your website directly from your hosting server. Please, use the incognito mode of the browser to make sure it didn’t cache the DNS.
In other cases, hosting security software may be blocking your firewall IP addresses. To resolve this, you will need to contact your hosting provider or system administrator and ask them to allowlist the following IP addresses:
192.88.134.0/23 185.93.228.0/22 66.248.200.0/22 208.109.0.0/22 2a02:fe80::/29
If this doesn’t resolve the issue, move on to the next step.
9. Check for large HTTP headers
In rarer cases, your application may be sending giant HTTP headers (larger than 16 KB) which cause the request to time out. To verify if this is the culprit, open your browser’s Developer Tools and inspect the size of the response headers.
The most common issue we find for large HTTP headers occurs when applications use multiple “Set-Cookies” headers for tracking purposes or repeatedly send the same HTTP headers.
9. Disable problematic plugins or themes
Plugins and themes are essential components of any WordPress website. They add functionality, design elements, and can enhance the user experience. However, they can also occasionally be sources of problems, causing errors such as a 502 bad gateway error. This is especially likely if the code within a plugin or theme is poorly written or outdated.
When a 502 error happens, one way to determine if it is caused by a plugin or theme is to temporarily deactivate all of them on your site. Don’t worry, you won’t lose any data by simply deactivating a plugin or theme.
If you can access your admin area, go to “Plugins“, select all the plugins, and pick “Deactivate” from the bulk actions drop-down menu.
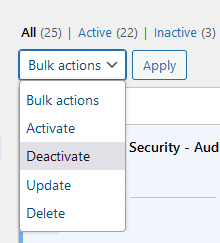
Do the same for your themes. If this resolves the issue, the problem lies with one of your plugins or themes.
When you reactivate a plugin or theme and the 502 error reoccurs, you have found the troublesome component.
At this point, you should contact the plugin or theme developer for assistance or post a support ticket in the WordPress repository.
10. Check your logs
Log files are essential components of troubleshooting. They record events and transactions that occur while software or an operating system is running. By providing a historical record of operations, error logs are instrumental in diagnosing and rectifying issues like the 502 bad gateway error.
If you are using a hosting service that features a logging tool, use that to check for errors. If your host is not equipped with a logging tool but you have a WordPress site, you can check your error logs in Apache and NGINX.
These are usually located at the following paths:
- Apache: /var/log/apache2/error.log
- NGINX: /var/log/nginx/error.log
11. Check for PHP Timeout Issues
PHP timeout issues often manifest as a 502 bad gateway error. These occur when a single PHP process is running for longer than the set `max_execution_time` or `max_input_time` in the PHP configuration on your server.
For example, if you’re conducting large WordPress imports or running complex scripts, your PHP processes might exceed the maximum execution time. It might cause the server to terminate the process prematurely, resulting in a 502 bad gateway error message.
To address this, you’ll have to increase these time limits. It involves editing your PHP configuration settings.
There are a few ways to do this:
- Edit your php.ini file: Try finding your php.ini file in your website’s root directory and adjust the max_execution_time or max_input_time values. For instance, to increase the limit to 300 seconds, you can set max_execution_time = 300.
- Use your .htaccess file: If you’re running on Apache, you can modify the .htaccess file in your website root directory. Add the lines `php_value max_execution_time 300` and `php_value max_input_time 300` to increase the time limits.
Remember, making these changes can have an impact on your server’s resources. Increasing the PHP processing time allows scripts to execute longer, potentially taking up more server resources.
After you’ve fixed the issue, you’ll still need to optimize your website to address the root cause of the problem. No website visitor wants to wait 5 minutes for a page to load (and Google won’t like it, either)!
You can consult with your hosting provider about the appropriate values suitable for your specific hosting plan.
And always remember to monitor your website’s performance after making these changes to ensure that it continues to run efficiently! If you continue facing issues, it would be best to consider optimizing your PHP code or talking to a PHP developer to address complex code issues.