A frustrating interruption to anyone’s day is the infamous HTTP Error 500 internal server error message. When it happens not only do you lose traffic or potential site revenue, but it can also reflect badly on your site’s reputation and even affect your search rankings.
Furthermore, 500 errors can sometimes be an indicator of compromise — the result of unsuccessful malware, damaged .htaccess files, or broken script injections nestled somewhere on the site.
In this article, we’ll explain more about 500 status codes, what they mean for you and your website visitors, and how to troubleshoot these errors to get your website back online again.
Contents:
- What is HTTP error 500?
- How are 500 errors different from other internal server errors?
- What are the most common causes of a 500 internal server error?
- Can HTTP error 500 be caused by malware?
- How to fix a 500 internal server error
- Do 500 errors impact SEO?
- Resolving 500 errors due to malware
What is HTTP error 500?
The HTTP 500 error is a server-side error that indicates that something went wrong on the website’s server, but the server is unable to provide specific details about the problem. It’s is a generic message displayed when no other message is suitable for the situation.
The Internet Engineering Task Force defines the 500 Internal Server Error as follows:
“The 500-error status code indicates that the server encountered an unexpected condition that prevented it from fulfilling the request.”
Something has gone wrong with the website, but the problem is not with your browser, your internet connection, or your computer. It’s a message that indicates there is a general problem with the site you’re trying to access or the server where the site resides, as seen below.
Common types of 500 error messages
500 error messages can come in all sorts of flavors, but they all mean the same thing. Here are a few variations of 500 errors you might encounter in your browser:
- 500 Internal Server Error
- 500 Error
- HTTP Error 500
- Temporary Error (500)
- 500
- The website cannot display the page – HTTP 500.
- Is currently unable to handle this request. HTTP ERROR 500.
These are only a handful of the possible messages you might find when encountering a 500 error. In fact, some websites even have their own custom internal server error messages.
But if you receive this message, you can be sure that an unexpected problem has been detected by the server.
How are 500 errors different from other internal server errors?
There are many types of internal server status error codes and they all mean different things.
To help you understand the difference between generic 500 errors and other types of internal server errors, we’ve outlined some of the common types of 5xx responses you might encounter on your site.
- 500 error: server encountered an unexpected problem. This error code comes up when something unexpected happens on the server which prevents it from completing the request, but no additional information is shown.
- 501 error: HTTP status code for not implemented. This indicates that the server is unable to execute the request and is either unable to identify the goal of the request, or does not have enough power to execute the request.
- 502 error: bad gateway. Essentially, an invalid response was detected. The server was doing a job as a proxy or a gateway and received an invalid response from a different upstream server. If you are using a WAF, this could indicate a problem with your server.
- 503 error: a service is unavailable. This occurs when the server gets too many tasks and is overloaded, down due to maintenance, or has been taken down by malware.
- 504 error: Gateway timeout. The server, which was performing as a proxy or a gateway, wasn’t able to identify the request within the fixed time limit.
- 505 error: HTTP version not supported by server. The server isn’t able to identify the HTTP protocol used in the request.
- 511 error: network authentication. The server requires user authentication to access the request.
With the exception of a 500 error, the majority of server errors provide clear reasons for the status response that can help you pinpoint the issue and resolve it.
But don’t despair; there are a number of potential causes for the vague and generic 500 server error. Let’s examine some of these sources before we move on to possible solutions.
What are the most common causes of a 500 error?
As the name suggests, a 500 internal server error is a general issue with a webserver. They can be caused by a plethora of issues ranging from relatively benign, like your browser cache needs to be cleared, to more serious server or database errors.
And unlike 503 or 504 errors, a 500 server error won’t clearly outline how to fix the problem nor what the problem is in the first place.
So, let’s take a look at some examples of elements that could be causing the problem.
- Your browser cache needs to be cleared
- Incorrect database login credentials have been used
- The website’s database is corrupt
- WordPress core files have become corrupted
- Issues exist within the database server
- PHP memory limit is exhausted
- The server has run out of disk space
- .htaccess file is corrupt or broken
- Issues exist with third-party plugins and themes
- There could be PHP timing out or errors with third-party plug-ins
- There are incorrect file/folder permissions
- There are CGI or Perl script errors
- Your hosting company made a change
Furthermore, many of these issues can arise due to a malware infection. Let’s explore how these issues could be indicators of compromise.
Can HTTP error 500 be caused by malware?
Hackers often make modifications to compromised sites — anything ranging from injecting extra code into existing files to creating thousands of malicious files and posts. These can result in 500 errors for your site.
The following scenarios can seriously affect website functioning and result in server errors if left unaddressed:
- Injected malicious code contains bugs
- Injected malicious code interferes with your website’s functionality
- Malicious code is injected into the wrong location, breaking legitimate website code
- Hackers completely replace legitimate code their own, breaking any site functionality that depended on the original legitimate file
- Hackers delete entire files or directories from the server
- Hackers encrypt legitimate files
- Too many malicious files (ie. doorways) exhaust disk quota
- The database becomes corrupted during compromise
- An attacker runs their own tools on the server, exhausting available resources required for site functionality (ie. cryptominers, DDoS bots, spam servers)
Example of how malware can cause 500 errors
Here’s an excerpt of a decoded black hat SEO doorway script that can lead to 500 errors on your website.
$search_bot=is_search_bot($ua); if($search_bot){ $response = post_url($indata_url,$data); if($response=="404"){ header("HTTP/1.0 404 Not Found"); exit; } else if($response=="500"){ header("HTTP/1.0 500 Internal Server Error"); exit; } else if($response=="blank"){ echo ''; exit; } else{ echo $response; exit; } } else{ header("HTTP/1.0 404 Not Found"); }
Since this code works for search engine crawlers, under certain conditions it can cause search engines and security scanners to return 500’s for your website.
Fortunately, there are a few ways to troubleshoot and resolve 500 internal server error notifications. Let’s dive in!
How do I fix a 500 error on my site?
Here are a few ways to troubleshoot 500 errors to get your site back up and running.
1. Clear your browser cache
This is a good troubleshooting step. This is done before looking for more debugging on your site to confirm that the issue isn’t cached on your end.
Below are instructions on how to clear cache on Google Chrome.
- Open Chrome.
- Click on the icon with the three dots icon at the top right of the browser window.
- Go to More tools then select Clear browsing data.
- Select the Time Range field, then choose one of the options that appear. To delete everything, select All time.
- Select Clear data to clear the cache.
You can opt to clear only your browsing history, or you can choose a more thorough clearing of your cache by including cookies and other site data in the cache clearing.
Note: Some website settings will get deleted and you’ll need to sign in to sessions again. You may also find that some websites seem slower, since content and images will need to load again.
2. Reload the page
When you receive the 500 error, wait a minute and then try reloading the page (F5/Ctrl + F5). It is possible that the host or server is overloaded, and the site should come back shortly. You could also try a different browser to rule out the issue.
To ensure that you are not seeing a cached page on the website, try loading the website with an appended variable like this: example.com?nocache
Another option to try is to paste the website into: downforeveryoneorjustme.com
This website can confirm if the problem is on your side, or the website is actually down. If you’re a Sucuri client, you can leverage our uptime monitoring to identify if your site is up and running or problems are detected there.
Something to note is that 500 server errors can happen immediately after you update a plug-in or theme on your WordPress site, but these are usually resolved after a refresh.
3. Check for recently installed or updated software
Investigate to see if any recently installed or upgraded software on your website failed to install or upgrade. To refresh your software, check the vendor’s website for specific instructions.
You’ll also want to audit your website for any new and unfamiliar plugins or themes. If you find anything unusual, this may be an indicator of compromise.
Investigate further to pinpoint:
- What the unfamiliar software or component is
- How long it’s been installed on your site
- Whether or not it’s legitimate
If you encounter anything that looks suspicious, remove the component and scan your website for malware.
Note: It’s always important to keep in mind that attackers regularly scan outdated and poorly maintained plugins, themes, and components for known vulnerabilities. Bad actors regularly run automated scripts to locate and target vulnerable websites. So as a rule of thumb, always keep your software up-to-date with the latest patches and security updates.
4. Check your server logs
Make use of your website monitoring and error logs. Server errors are usually logged in error.log and will contain any important information about what’s broken.
If your host doesn’t have a logging tool, you can also enable WordPress debug mode by adding the following code to your wp-config.php file to enable logging:
define( 'WP_DEBUG', true ); define( 'WP_DEBUG_LOG', true ); define( 'WP_DEBUG_DISPLAY', false );
Be sure to disable these WordPress debugging options as soon as you’re done troubleshooting. Any error messages found there may disclose sensitive information about your server and website, making it easier for a bad actor to hack it.
5. Check your plugins, extensions or themes
Extensible components like plugins and themes can often cause 500 internal server errors.
Most times you’ll see the error immediately after doing an update or installing something new. It’s advisable to do updates one at a time, otherwise it may become difficult to determine which update caused the internal server error.
You can again use the debug mode to coax your website into providing a specific error that will reference the broken component. As described in the last step, debug mode can be enabled in WordPress by adding the following line to your website’s wp-config.php file:
define( 'WP_DEBUG', true );
If you can get a specific error referencing a specific plugin or theme, try disabling that component and see if your website comes back online.
If not, continue troubleshooting. You can also check the error_log file in your website’s docroot to see if you can find the specific issue.
Another option is to try troubleshooting by deactivating all your plug-ins and testing them individually. We’ll outline a few options depending on whether you can access your Admin panel or not.
If you are still able to access your Admin panel in WordPress:
- Navigate to Plugins > Installed Plugins
- Select the checkbox at the top of the list to select all plugins
- Open Bulk Actions and select Deactivate.
- Click Apply to disable all your plugins to start troubleshooting.
If you are unable to access your WordPress Admin panel, try using sFTP to disable plugins:
- Connect to your server using your sFTP client.
- Navigate to the wp-content folder.
- Right-click on plugins and select Rename.
- Enter a new name for the folder. (ie. deactivated-plugins)
- Your WordPress site won’t be able to locate the folder and all plugins will be deactivated.
And if you find disabling all our plugins does in fact fix the issue, you’ll have to determine one caused the problem. Activate each of them one at a time and then reload the site after each activation. When you see the 500 internal server error return, you will know which one caused the error. Then reach out to the plugin developer for assistance.
Added bonus: You might find that having fewer active plug-ins on your site helps things run more smoothly.
6. Check for errors establishing a database connection
500 internal server errors can also occur from a database connection error.
Depending on your browser you might see a number of different errors, but both generate a 500 HTTP status code in your server logs. With this error, your entire page will appear blank as no data can be retrieved to render the page because the connection is not working properly. This will break the front-end of your site and will also prevent you from accessing your WordPress dashboard.
A few reasons why this happens:
- One of the most common reasons is that your database login credentials are incorrect.
- Your database could be corrupt. With a lot of moving parts with themes, plugins, and users constantly deleting and installing them, databases occasionally get corrupted. This could be due to a missing or individually corrupted table, or perhaps some information was deleted by accident.
- There are issues with your database server. A number of things could be wrong on the web hosts end. The database could be overloaded from a spike in traffic, or it could be unresponsive from too many concurrent connections.
To troubleshoot a database connection error, first take a backup of your website. Then run through the following steps:
- Check your database login credentials. This is a common issue that should be ruled out before troubleshooting further, so make sure details in your wp-config.php file are accurate.
- Check for a corrupted database. If your database has become corrupted, WordPress has a database repair mode you can initiate. Add the following to your wp-config.php file: define(‘WP_ALLOW_REPAIR’, true); then navigate to https://yourdomain.com/wp-admin/maint/repair.php. From here, you’ll have the option to repair and optimize your database.Be sure to remove the WP_ALLOW_REPAIR statement from wp-config once you’re done to ensure nobody else can access the page on your site.
- Check with your hosting provider. Too many concurrent connections can cause database connection errors and many hosts limit the number of connections that are permitted for any given server.
- Restore a backup. If you aren’t worried about losing any data, try restoring a backup of your website files and database.
7. Check for problems with your .htaccess file
The .htaccess is a crucial file for Apache server environments. If you are using WordPress with Apache and have recently started encountering 500 errors, your .htaccess file could be corrupt or damaged.
Moreover, the .htaccess file is notorious for being targeted during a compromise. Attackers can use the file to conceal malware, redirect search engines to spam websites, inject malicious content into a website, modify php.ini values, or even conceal backdoors.
To begin, you’ll want to assess if any problems with your .htaccess are the result of a hack or an update to your .htaccess file.
You can locate your .htaccess file by accessing your website files through a file manager like cPanel or via FTP/SFTP. The file will probably be located in your public_html directory. There’s a good chance your server will hide this file from view by default and you’ll need to toggle hidden files to see it.
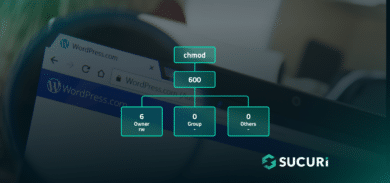
8. Check for permissions errors
Occasionally, file permissions may be accidentally altered or incorrectly set resulting in a permissions issue. A permissions error for an important file can result in 500 internal server errors.
To resolve this issue, you’ll need to connect to your server via FTP/SFTP and review your site’s file permissions. Each file and directory has unique file permissions that control access. These permissions are represented by a three-digit number. Each digit indicates the level of permission for the owner, group, and others (respectively).
The ideal file permissions for a WordPress site are:
- Files: 644 or 640
- Directories: 755 or 750
- wp-config.php: 440 or 400
You can refer to the WordPress Codex article on changing file permissions for more details.
9. Check for PHP memory limit on your server or website
A 500 internal server error could also be caused by exhausting the PHP memory limit on your server. Try increasing the limit.
PHP timeouts can also occur from the lack of PHP workers, although these typically cause 504 errors — not 500 errors. These determine how many simultaneous requests your site can handle at any given time. Simply put, each uncached request for your website is handled by a PHP Worker.
When PHP workers are already busy on a site, they start to build up a queue. Once you’ve reached your limit of PHP workers, the queue starts to push out older requests which could result in 500 errors or incomplete requests.
Follow the instructions below on how to change this limit in cPanel or Apache.
Increase PHP Memory Limit in cPanel
If you’re running on a host that uses cPanel, you can easily change this from the UI.
- Under Software click on Select PHP Version.
- To choose the PHP version, select Switch to PHP Options.
- Click on the memory_limit attribute and change its value.
- Click Save.
Increase PHP Memory Limit in Apache
You can modify server behavior from your .htaccess file right down to a directory specific level:
- Log into your site via FTP or SSH.
- Locate your .htaccess file.
- Add or replace the following line in your .htaccess file, modifying xxx with the new memory limit value in megabytes that you want to set: php_value memory_limit xxx
- Save the changes.
You can verify that the new setting is active by creating a PHP test file containing the following code in the same directory as your .htaccess file:
<?php phpinfo(); ?>
Simply load your new test file in a browser and the Local Value should display the value that you set in your .htaccess file.
Increase PHP Memory Limit in WordPress
Sometimes, all that needs to be done is to increase the amount of memory that WordPress itself is able to consume. This can be done by adding the following line to wp-config.php:
define('WP_MEMORY_LIMIT', '256M');
10. Check for server issues with your host
Sometimes these errors can be difficult to troubleshoot without an expert, so you can always check with your host. Ask your service provider to access your error logs and help you pinpoint the issue.
In some cases, you may also be experiencing connectivity issues with your host server due to some unexpected network failures at an upstream provider that affects the connectivity to your host server. If so, they will be able to shed some light on whether this is affecting you and your website visitors.
Do 500 errors impact SEO?
500 errors can have a negative impact on SEO if not addressed.
Googlebot will typically retry pages that are serving 500 errors. If they persist, Googlebot will reduce the crawl frequency and over time eventually drop the URLs from the index.
Moreover, if the 500 errors are happening due to a malware infection and Google identifies that your website has been hacked or is serving malicious content, the infection could result in blocklisting — and this can significantly impact your search rankings and organic traffic.
So, the first step is to determine why the 500 errors are occurring and address them to mitigate risk for your SEO.
Resolving a 500 error due to malware
500 internal server errors are extremely frustrating, but after these troubleshooting tips you should be able to get your website back up and running in no time.
Keep in mind that these types of errors can be caused by the plethora of issues outlined in this post, but sometimes malware infections can also result in 500 errors.
- It’s in malware’s best interest to keep the victim website online, but if a malware injection is buggy and breaks the code on the website it can result in a 500 error.
- Malware like cryptominers can eat up resources on the server, causing timeouts, slow performance and 500 errors.
- In the wake of a blackhat SEO infection, thousands of spam pages can be generated on a website. Search engines will continue to try to crawl these pages even after they’ve been removed, and result in degraded performance and sometimes server timeouts or 500 errors.
If you’ve followed these troubleshooting steps and suspect that your website has been hacked, you can refer to our guide on how to clean up malware. If you need a hand, we’d be happy to help clean up your infected website.