Education is essential for defending your website against emerging threats. That’s why we are thrilled to share our 2023 Hacked Website & Malware Threat Report. Disseminating this information to the community helps educate website owners about the latest trends and threats.
This year, we’ve included new insights to highlight the most prevalent tactics and techniques observed in compromised web environments and remote scanners.
Key takeaways
Some of the key findings from our 2023 Website Threat Research Report include:
- 39.1% of all CMS applications were outdated at the point of infection.
A CMS was considered outdated if it had not been updated with the latest security release at the time remediation was performed. Our data indicates that automatic updates in WordPress have aided in maintaining more up-to-date CMS installations, which has significantly reduced exploits in core CMS vulnerabilities.
- 13.97% of all compromised websites had at least 1 vulnerable plugin or theme present in the environment at the point of remediation.
This data point stresses the importance of patching and maintaining website software and third-party components to mitigate risk. Easily exploited vulnerabilities are a top choice for attackers. If they don’t require authentication, attackers are able to easily automate their attacks and monetize affected environments. By patching software to the latest version, website owners can minimize risks from bugs, known vulnerabilities, and other security threats.
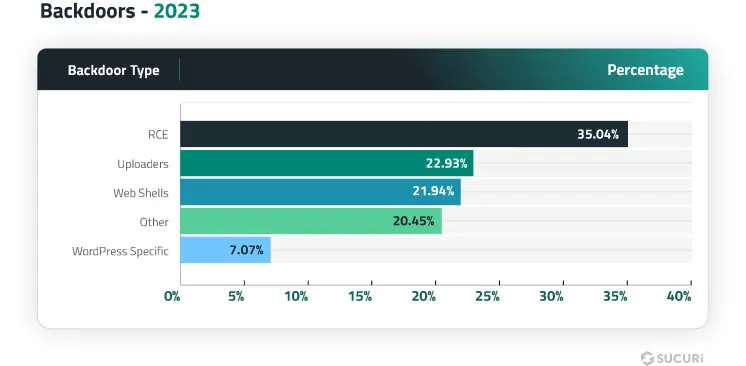
- 49.21% of compromised websites were found to have at least one backdoor at the point of remediation.
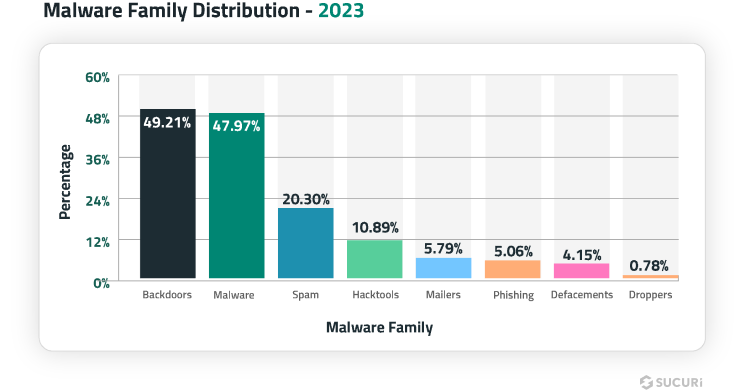
Backdoors can be difficult to detect and found in a wide range of formats — it’s common to find several different types of backdoors responsible for specific tasks on a compromised server environment. In total, our team removed 21,062 backdoors from infected websites last year.
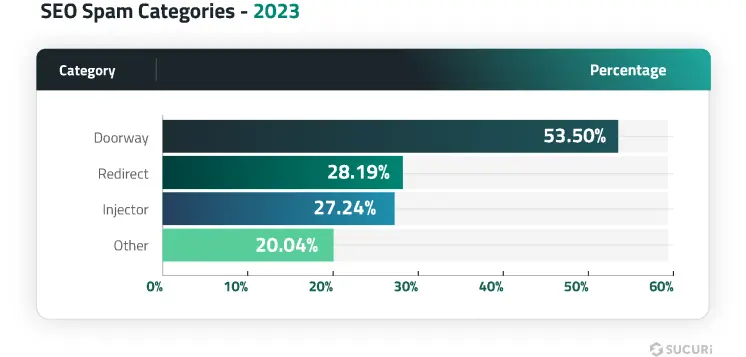
- SEO spam was detected on 42.22% of all infected websites in 2023.
SEO Spam ranked as the third most common malware family on compromised websites; 20.30% of all remediated sites were affected by some form of SEO spam. Our teams eliminated 4,131,724 spam instances from files and cleaned 430,934 spam entries from compromised databases.
- 10.89% of compromised websites contained at least one hack tool.
This category is used to identify automated tool kits like AnonymousFox along with configuration stealers, DDoS attack tools, botnet scripts, mass defacement tools, and spam mailers.
- Malicious WordPress admin users were found in 55.2% of infected databases.
Our data revealed the top ten most common user names and email addresses associated with these malicious admins.
| Top 10 malicious admin usernames | Top 10 malicious admin emails |
| wp_update-[random-chars] | wadminw@wordpress.com |
| wp-demouser-44 | 123@abc.com |
| Test[random-digits] | email@email.em |
| wp-import-user | support@wordpress.com |
| administratoirr | admin@gmail.com |
| administratoir | wp-security@hotmail.com |
| wwwadmin | wordpressuser@gmail.com |
| wpadminns | admin@admin.com |
| Sendsdesr | test@gmail.com |
| AdminZaxHH34 | mail11@maill5.xyz |
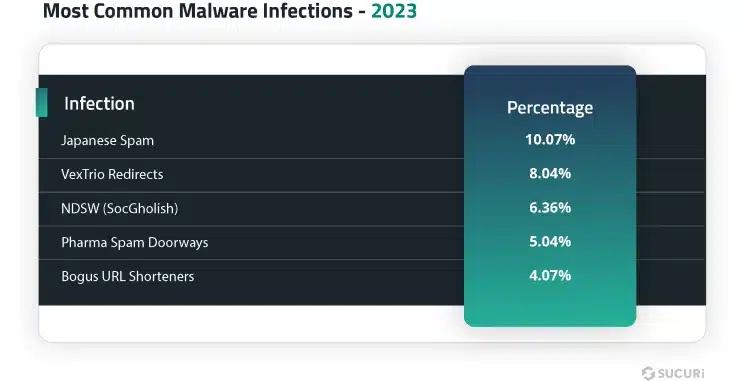
- The most common infection found during remediation was malicious allow/deny rules in .htaccess files associated with Japanese SEO spam (10.07%).
These infections are renowned for infecting or creating thousands of files within a website’s environment.
Download our full report for further insights,statistics, malware samples, and mitigation steps.
Closing thoughts
The data from our 2023 website malware and threat report highlights the importance of keeping CMS applications, plugins, and themes up-to-date to reduce the risk of infection. The high percentage of outdated CMS applications and vulnerable plugins or themes present in compromised websites suggests that there is still work to be done in terms of patching and essential security practices to prevent infection.
To combat these threats, website owners and developers must prioritize website security, leverage 2FA on admin panels among other website security best practices, and stay informed about emerging trends and attack vectors. You can leverage a web application firewall like the Sucuri WAF to help mitigate risk and protect your website from unauthorized access, brute force, and website malware infections.