The Magento team released a critical security patch (SUPEE-5344) to address a remote command execution (RCE) vulnerability back in February. It’s been more than two months since the release and still more than 50% of all the Magento installations have not been patched, leaving them open to attacks.
This means hundreds of thousands of websites are vulnerable right now, worse yet they are ecommerce websites. This means that these websites are used to sell goods online, and in the process they capture personal identifiable information (PII) including credit card details. The impact of Magento websites getting compromised can be devastating for every online buyer that uses, or has used a website built on the platform.
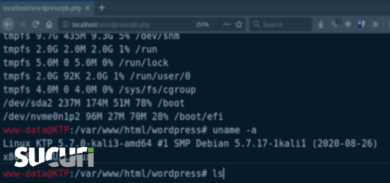
This is a very serious vulnerability, it allows allows an attacker to run any command they want on the server, allowing them to take full ownership of the vulnerable online shop and it’s associated web server.
Full Disclosure Going Live in a Couple of Days
This vulnerability was discovered by the Check Point research team and reported to Magento back in January. They gave us an early warning to help spread the word to as many Magento admins we could. In a few days (likely this Monday or Tuesday – April 21st), they will release full details of the vulnerability on their blog.
Once the details are released, it is expected that within hours there will be a working Proof of Concept (PoC) available for the masses. The severity of this issue cannot be understated, we cannot stress the importance of patching immediately.
If you own a Magento site, you must patch it immediately! Go to the download page, search for SUPEE-5344 and follow the instructions. If you can not apply the patch, I highly recommend putting your site behind a Website Firewall (WAF) or Intrusion Prevention System (IPS).
You have less than 72 hours.
Sucuri Website Firewall (CloudProxy) Customers Protected.
All customer websites behind our Website Firewall (CloudProxy) have been protected against this vulnerability via our Virtual Patching Engine.








8 comments
Server logs this morning are full of:
Request URI /magmi/web/plugin_upload.php
and similiar. Same as new RCE?
Nope, that’s not it. We are not seeing it in the wild yet, but it all will change once they release the details.
According to CheckPoint there are 3 different vulnerabilities in the mentioned update. Which of these vulnerabilites is mitigated in your WAF?
thanks for the Amazing Information
“You have less than 72 Hours” – Patch was added 9th of February. What kind of security guy are you? The 2 months late panicking security kind?
What kind of commenter are you? the kind that does not understand the difference between a silent patch release and a technical vulnerability description in a press release?
The kind that realizes dereliction in duty by failure of Magento to send out to the subscribers of their security email list that a patch had been released. They did not send out anything in February, I found out about it 5 days later on Stack Exchange, spent the next week dealing with an issue that it caused and patched it before the end of the month. AMAZINGLY, THE FAMOUS MAGENTO SECURITY EMAIL LIST POPPED TO LIFE TO LET US KNOW IN APRIL THAT A FEBRUARY PATCH NEEDED TO BE INSTALLED. Yeah, that was good times, followed by great fails.
It is truly amazing that the SUPEE-5344 events that followed guaranteed that Magento never, ever suffered dereliction of duty by failing to announce patches to their security email list after that. Several were notable for getting 3-5 announcements, just to make sure that subscribers were alerted.
We just had our webiste released to us on 1st of April. However the critical Magento message exists as I log in. The question is if the developer company who developed the site is liable to apply the updates for us? Can anyone help? Thanks!
Comments are closed.