Microsoft just disclosed a serious vulnerability (MS15-034) on their Web Server IIS that allows for remote and unauthenticated Denial of Service (DoS) and/or Remote Code Execution (RCE) on unpatched Windows servers. An attacker only needs to send a specially crafted HTTP request with the right header to exploit it. That’s how serious it is.
RCE is used to describe an attacker’s ability to execute any command on a target machine from a remote location, bypassing all security mechanisms.
This security update is rated critical for all supported editions of Windows 7, Windows Server 2008 R2, Windows 8, Windows Server 2012, Windows 8.1, and Windows Server 2012 R2. You can read more details about the versions affected in the Microsoft Security Bulletin.
What’s Happening in the Wild
A simple POC has been released so you can expect public exploits to be released very soon. The attack is based off a change in HTTP!UlpParseRange in which an error code is returned as a result of a call to HTTP!RtlULongLongAdd when evaluating the upper and lower range of an HTTP range request.
8a8b2112 56 push esi 8a8b2113 6a00 push 0 8a8b2115 2bc7 sub eax,edi 8a8b2117 6a01 push 1 8a8b2119 1bca sbb ecx,edx 8a8b211b 51 push ecx 8a8b211c 50 push eax 8a8b211d e8bf69fbff call HTTP!RtlULongLongAdd (8a868ae1) ; here
This is the code that has been released:

This code is using the Range header to trigger a buffer overflow and detect if the system is vulnerable or not. The attack is very similar to the “Apache Killer” that happened a few years ago.
The Range-Header is used to request only part of an object. It is commonly used by download managers to resume downloads.
Identifying a vulnerable system
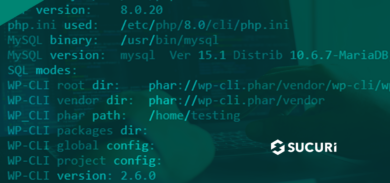
You can easily verify if your server is vulnerable using the following curl command:
curl -v SERVER_IP -H "Host: anything" -H "Range: bytes=0-18446744073709551615"
If you get something like this:

That means your server is not patched.
Fixing the Problem
All sites behind CloudProxy (our Website Firewall and Intrusion Prevention System for Websites) are already protected against this vulnerability. If you are not a customer you should apply the Microsoft patches ASAP.






3 comments
The “exploit” mentioned is just a DoS method. There’s no RCE exploit for this, and it’s likely there won’t be as exploiting a single integer value is not easy.
Imagine this Kevin: You ask IIS to provide you with the data from file X, you ask to resume your download of file X starting from byte number -1024 .. IIS then loads file X into the memory, it then goes to location ptr.X[-1024] and tries to load that location from the memory in order to serve it to the user … oops.
I will send it to some of my friends. And of course, thank you for your efforts in this article!
Comments are closed.