Ask Sucuri: My site is under a brute force attack. What can I do? How can we solve this password guessing problem known as brute forcing? This is a common question we get from users of our WordPress plugin and from the overall community. Brute force attacks are very common, but most people do not understand how they work and what they can do to stop them.
What is a Brute Force Attack?
First, let’s talk a bit more about brute force attacks. Brute force is just a generic term we use for attacks that try to guess the username and password for a site. This type of attack is incredibly common against popular CMS platforms (eg. WordPress, Joomla, etc) and against common services, like FTP and SSH. We actually keep track of how many brute force attacks occur against WordPress sites in our network on a daily basis.
There are many ways to perform a brute force attack. The most common method is dictionary-based attacks. In this case, the attackers use a list of the top 500 most common passwords (or password lists from the many data breaches over the years) and try each password against your site. They continue this attack until they find the right username and password combination.
Generally, it takes only a few minutes for them to try a few hundred combinations. Most dictionary-based attacks mix keywords from the domain itself to increase the success rate.
The majority of password-guessing attacks try to hit your login URL (/wp-admin or /wp-login for WordPress; /administrator for Joomla) or an API endpoint URL that accepts a user name and password (e.g., /xmlrpc for WordPress).
Protecting Against Brute Force Attacks
Password-guessing attacks are considered to be the simplest to execute by an attacker. It doesn’t require a vulnerability or an exploit, and can be performed by any bad actor.
It is also very easy to protect against brute-force attacks. You start by enforcing a very strong password for all the users of the site and you are set.
Again, there is no mystery to this: Enforce a strong password for all the users and a brute force attack will not succeed.
The underlying problem, however, is a bit more complicated
First, people tend to be really bad at picking strong passwords and the majority don’t use a password manager.
Second, brute force attacks can have other unwanted side effects, such as causing website availability issues due to denial-of-service errors. The repeated attempts can create unnecessary load on the web server’s local resources by passing too many requests at a time. As an active defender, they can also be problematic due to the noise that comes from all the logs (i.e., raw logs and email notifications you might be receiving). This makes it hard to manage and spot other attacks among the brute-force attempts.
There is also a maintenance issue that happens on the day-to-day operations. For example, even if all users have a strong password, a temporary or testing account with a weak one may be forgotten over time. This may be from a developer on the site, the agency responsible for deploying, or whoever is managing the site on behalf of the organization. It’s not done intentionally, but its effects can be dangerous. We see this a lot when performing our incident response services. The response we often get might sound something like, “Oh, I added it a while back for testing and forgot…”
Playbook Against Brute Force Attacks
- Enforce strong passwords. This is your first line of defense, and the only way to prevent an attacker from succeeding.
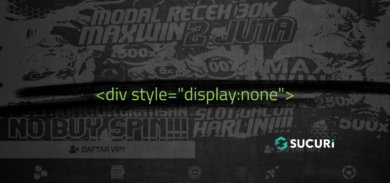
- Restrict access to the authentication URLs. Even if you have a strong password, the attackers will keep hitting your authentication URLs continuously. They won’t succeed, but they will keep trying.
We recommend restricting login page access to only authorized IP addresses if possible. For example, if you have a static IP address on a WordPress site (using Apache), you can restrict access to /wp-login to this IP via your .htaccess file. Even if you do not have a static IP, you can restrict it to your ISP common range:<Files /wp-login> order deny,allow allow from MYIP allow from MYIP2 deny from all </Files>
This alone will cut down the noise significantly by blocking all attempts. You can do the same for any other authentication URL that your CMS or application provides. If you are using a cloud-based WAF (like the Sucuri Firewall) you can restrict access to these URL’s via your dashboard without having to mess with .htaccess files.
- Captchas – Pre-login captchas are a powerful way to slow down brute force attempts and we highly recommend using them when you can not do the IP address restriction we recommended above. They are specially useful on open-registration sites to reduce the amount of spammers and bots from registering. There are multiple free-plugins that allow you to enable captcha and users behind our WAF can enable captcha on any URL using our Protected Page option.
- Two Factor Authentication (2FA) – We also recommend using two-factor authentication whenever possible. This helps reduce risk in the event that your password is compromised. It is an extra line of defense for your accounts and is one of the best ways to ensure your account cannot be easily broken into.
Brute force attacks are too simple, and we can’t allow it to continue to be a major source of today’s compromises. There are so many tools designed to help with securing the login process, and the steps to mitigate an attack are easy to implement.
Remember that while you can’t do much about stopping someone from trying, you can do everything you can to stop them from succeeding.
We can help you protect your website from brute force attacks.
Link References in Post:
[1] Understanding Brute Force and Denial of Service
[2] Active Brute Force Tracker
[3] Analysis of Yahoo Breach 2012