We are proud to be releasing our latest Hacked Website Trend Report for 2017.
This report is based on data collected and analyzed by the Sucuri Remediation Group (RG), which includes the Incident Response Team (IRT) and the Malware Research Team (MRT).
The data presented stems from the analysis of 34,371 infected websites summarizing the latest trends by bad actors. In this report, we build from data points seen in the 2016/Q3 report to identify the latest tactics, techniques, and procedures (TTPs) detected by the Remediation Group.
CMS Analysis
Based on our data, the three most commonly infected CMS platforms were WordPress (83%), Joomla! (13.1%) and Magento (6.5%).
This data does not imply that either platform is more or less secure than another. However, Sucuri is well established in the WordPress community and offers a free security plugin, which may have influenced the results of the analysis.
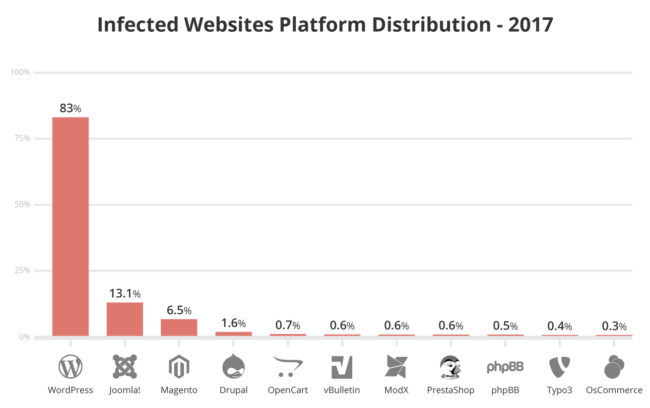
The majority of these analyzed compromises were associated with improper deployment, configuration, and overall maintenance by webmasters – not with the core of the CMS application itself.
Outdated CMS Analysis
In our new report, we also assess the number of outdated platforms at the point of infection.
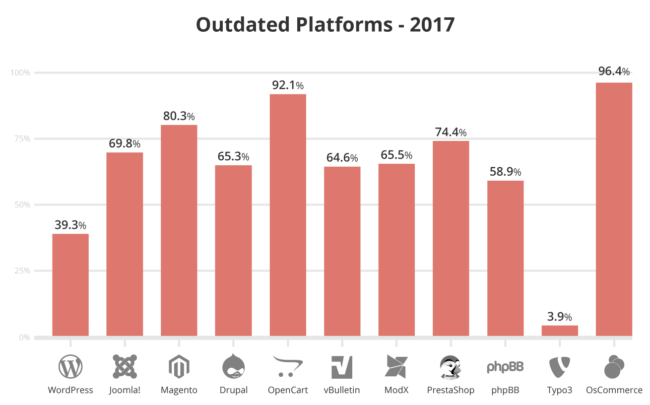
Our report identifies an interesting shift in the number of out of date, vulnerable versions of WordPress at the point of infection. At the end of Q3 2016, 61% of hacked WordPress sites recorded outdated installations, however, this amount has since decreased. In 2017, only 39.3% of clean up requests for WordPress had an outdated version.
Joomla and Drupal saw more than a 15% decrease in outdated versions from the previous year, down to 69.8% and 65.3% respectively.
Similar to previous years, Magento websites (80.3%) were mostly out of date and vulnerable at the point of infection; though this number has declined over 13% since Q3 2016.
Blacklist Analysis
Per our analysis, approximately 17% of the infected websites were blacklisted (a 2% increase from 15% in Q3 2016).
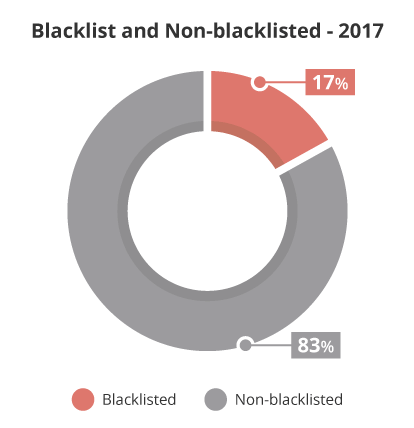
Our 2017 Hacked Website Trend Report also describes which blacklist authorities were responsible for flagging infected websites.
Malware Families
Part of our 2017 research included analyzing the various infection trends, specifically how they correlate to our malware families and the payloads used by cybercriminals. Understanding malware families is a crucial aspect of Sucuri’s research. It offers us insight into the Tactics, Techniques, and Procedures (TTP) that bad actors are employing.
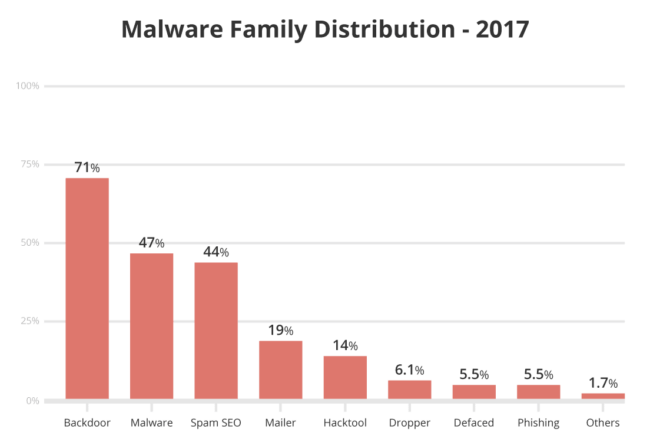
In our analysis of 2017 website infections, 71% of all compromises had a PHP-based backdoor hidden within the site. We also saw a marginal decline in malware distribution – from 50% in Q3 2016 to 47% in 2017.
Summary
A few key takeaways from this report include:
- WordPress continues to be the leading infected website CMS (83% of all websites cleaned in 2017).
- There was a notable decrease in out-of-date WordPress, Joomla, and Drupal installations at the point of infection. Magento continues to lead the pack for the number of out-of-date vulnerable installations at the point of infection.
- The blacklist telemetry showed a 1% reduction in sites that had been blacklisted (only 14%), increasing the number of infected websites that are going undetected by blacklist engines to 86%.
- The malware families analysis showed that SEO spam has risen to 62.8% (up 25.8% from Q3 2016). It also showed a slight decrease in mailer scripts (19% to 15.1%), and a sharp decline in malware distribution – from 50% in Q3 2016 to 35% in 2017.
The report is available both on our website and in PDF format.
We take great pride in our research efforts and hope that you’ve found these insights engaging and valuable. Our analysts and researchers will continue to expand on the data we collect and outline for website infections, but if you have any recommendations or feedback we’d love to hear from you!











