Sucuri malware analyst Kaushal Bhavsar recently brought our attention to a massive campaign responsible for adding either “1800ForBail” or “1800ForBail – One+Number” keywords to the titles of vulnerable WordPress sites.
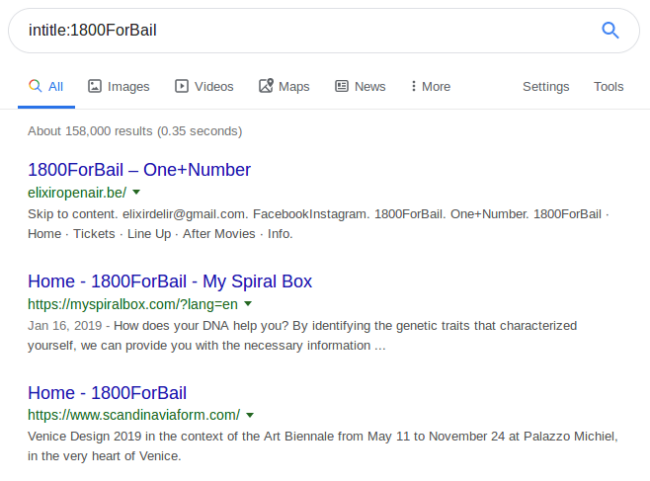
1800ForBail in Search Results
Google currently returns 158,000 results for the [intitle:1800ForBail] query.
At the same time, PublicWWW.com returns 692 results for “1800ForBail”, where one result per domain is typically listed.
Google’s cache shows that the majority of sites were hacked after June 12th, 2019.
Blogname and Siteurl Attacks
HTML page analysis of these hacked sites reveal a common picture — bad actors change the standard WordPress setting “blogname” used to generate web page titles.
This attack is very similar to so-called “siteurl attacks” we’ve been regularly seeing since last year. In this campaign, hackers massively exploit vulnerabilities in various plugins to change URLs of static resources, including JavaScript files, resulting in malicious code being loaded instead of legitimate scripts.
Old unpatched versions in a number of plugins and themes are currently known to be exploited: WordPress GDPR Compliance, TagDiv themes, Freemius Library (and all plugins that use it), Convert Plus, etc.
These “siteurl attacks” are a part of a massive campaign which actively exploit all newly discovered vulnerabilities in WordPress. They use the same domain names as the rest of the script injections. And it’s quite natural on sites with the “1800ForBail” title, that we often find altered siteurl options— their HTML markup features familiar malicious domains and looks like this:
<meta property="og:title" content="Home - 1800ForBail" /> <meta property="og:url" content="hxxps://deliverygoodstrategy[.]com/destiny?tt=2&/" /> <meta property="og:site_name" content="1800ForBail" />
Phonewords in Black Hat SEO
These seem to be two separate attacks. One of them (siteurl/home) redirects visitors to scam sites (tech support and push notification scams), while the other changes blog titles — a black hat SEO technique used to gain more visibility for the brand of the “bail service”.
This approach is similar to what we’ve seen in the Korean spam campaign, where hackers flooded search results with links to certain Korean sites without actually linking them. This tricks Google to index any “Not Found” search result pages mentioning respective domain names and relevant keywords on unhacked WordPress sites.
In the Korean spam campaign, this approach worked because the domain names were very short and people could manually type the domains into the browsers’ address bar.
In the case of this new “1800ForBail” campaign, bad actors leverage two distinct features: a simple domain name matching the injected keyword — which makes it effortless for users to manually enter it into their browsers — as well as a toll-free number using the mnemonic phoneword “ForBail”.
Conclusion
Hackers constantly find new ways to exploit vulnerabilities in website software. This new “blogname attack” doesn’t break the sites, making it harder to notice the hack if you don’t pay attention to the titles of the open browser tabs. These spam keywords are very prominent in search results, which affects the reputation of the website.
To mitigate the damage to a hacked website, site owners should change the “Blog title” setting from their WordPress admin interface (or the “blogname” option in the wp_options table) and update all themes and plugins to prevent reinfection. If the site was also affected by the “siteurl attack, you might need to revert other modified site settings”.
If you don’t have the time or expertise to deal with this problem, you can check out our malware removal service and employ a web application firewall.










