To better understand the difference between website malware and vulnerabilities, imagine your online property is a brick-and-mortar structure. You’d want to keep safe from burglars, so you take measures to protect your house, like locked doors and windows, and installing an alarm system.
It’s the same thing with website security. But with your online property, website malware is the burglar. And website vulnerabilities are the open doors and windows, and lack of an alarm. Simple, right?
Well, don’t stop there. That understanding helps a lot, but it’s important to dive a little deeper to understand how bad actors infect websites. Grab a cup of coffee, and let’s take a closer look at the difference between website malware and vulnerabilities.
What is website malware?
The term website malware refers to a family of software that bad actors create to compromise or otherwise damage websites. A hacker might want access to a website for the data it contains or receives. Or they might hold it hostage for financial gain. And they could just be acting like vandals defacing a building for street cred.
Common types of website malware
Our researchers have found there are quite a few varieties of website malware, which you can usually uncover with a free scanner like our SiteCheck (UnmaskParasites is pretty good, too.). Now let’s take a look at a few of the most common types of malware:
- SEO spam — The most common type of website malware, SEO spam hijacks the visibility of legit websites to promote scams. It’s why you might see a normal site with odd content advertising stuff like pharmaceuticals or sports jerseys. That content wouldn’t normally display in search results, so hackers gain access to innocent sites, and then add content to mislead searchers for a particular terms related to a scam.
- Backdoors — Backdoors give hackers access to a site that would normally be reserved for privileged users like admins or webmasters. With a backdoor in place, bad actors can reinfect a site with any of the malware on this list.
- Hacktools — This broad category of website malware covers tools that rely on the resources of a website or server to carry out a scam or another attack. One of the most common hacktools is a mailer, which sends out phishy emails from a seemingly trusted source.
- Defacements — Here’s where we find hackers acting like vandals. Politics aside, we saw a very visible example in 2013, when hackers defaced numerous online properties in Brazil to protest how the government hosted that year’s FIFA World Cup. With access allowing them to modify website content, these hackers posted political messages in surprising places, such as government websites.
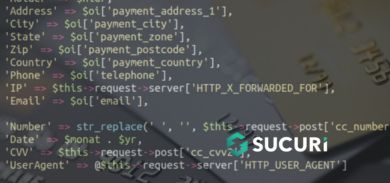
- Ecommerce stealers — This type of website malware is downright scary. Hackers often craft a one-off program designed to infect an ecommerce website, and then steal the credit card information of innocent shoppers.
What are website vulnerabilities?
Imagine leaving your home with open doors and windows inviting a burglar to sneak inside. With an online property, website vulnerabilities attract and offer easy access for bad actors to infect a site with malware.
Common website security vulnerabilities
Our researchers find the most common website vulnerabilities result from the bad habits and behaviour of site owners. Other vulnerabilities are technical in nature. Let’s look at examples of both types:
- Outdated files & apps — Website updates often include security patches that eliminate known vulnerabilities. Failing to install updates means those vulnerabilities remain available for bad actors to exploit unless you have a firewall with virtual-patching technology.
- Weak passwords — While it’s tempting to use short passwords that are easy to remember, these are also easy to hack. Make sure passwords are unique, random, and contain more than a dozen or so characters. With those basic rules, you have a much better chance of avoiding a password attack.
- Excessive permissions — Make sure people who can access your site only have the permissions necessary for their role. Otherwise, their bad security habits could put your entire website at risk of infection.
- SQL injection — Places where visitors interact with your site (e.g. data entry fields) can also be used to inject SQL statements. When executed, these give bad actors control over the site. Use one of the many free pen-test tools to uncover weak points and educate yourself about SQL injections.
- Cross-site scripting (XSS) — XSS attacks involve injecting a malicious program into a legit website. It then affects visitors by running something directly on their browser. Prevent it by controlling the manner in which visitors can enter data into your site (see the guide).
Recap: The difference between website vulnerabilities & website malware
There you have it, the difference between website malware and vulnerabilities. Yes, they’re two different things but so closely related it’s necessary to gain an understanding of both. Treat your site much as you would your home by making it more difficult to access — and keeping it that way.
If you’re finding this topic a little too stressful, consider putting your website behind a web application firewall (WAF) (you can even try ours free for 30 days). A WAF identifies and blocks bad actors before they can access your site. And if you need the ultimate in protection for your website, consider a suite of website security tools that work together to lock down your online property, or start a free trial today.