Have you ever set up a new server, database, or admin account but once it came time to create a password, you struggled to come up with a strong one? Panic sets in as the security suggestions prompt you to add more numbers and unique characters. It’s hard enough to remember one password, let alone multiple!
For many users, passwords are not as strong as they should be. We’ve previously written about the elements of a secure password and this topic is still incredibly important and relevant for website owners (and anyone with an account, really).
Hackers know that many site owners don’t have their password security on lockdown. Once initial compromise of the website occurs and a foothold is established, it’s possible for an attacker to move laterally within the environment — even if file and ownership permissions are correctly configured (depending on the configuration of the environment).
Most CMS platforms (WordPress included) also have administrator login panels publicly accessible, contain no limit on the number of failed login attempts, nor contain multi-factor authentication by default. The onus is on the website owner to configure these after the fact through the usage of third party plugins/extensionsor or by leveraging native features in newer CMS versions. Many do not bother doing this until after a website compromise takes place.
How to make a strong password
Take a few minutes to review the following password security best practices and apply them to any existing credentials that don’t currently meet these guidelines.
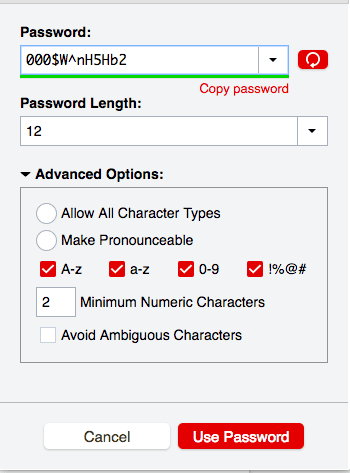
1. Use a combination of letters, numbers and symbols
A very important part of creating a strong password is to make it unpredictable.
You’ll want to make sure that anyone trying to guess the password will fail miserably which is why password complexity is key. Using a combination of special characters, symbols, and numbers is an effective way to ensure that your password is unpredictable and safe.
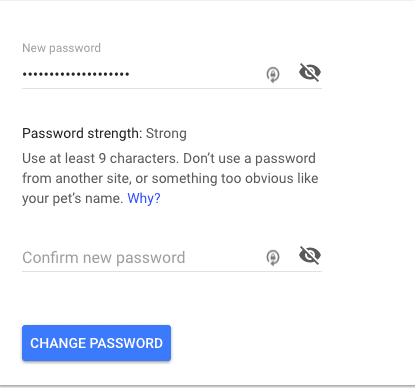
2. Ensure that all passwords are at least 16 characters long
Length is essential to creating a safe password. While most sites and tools historically required at least 8-10 characters, you should aim for passwords that are at least 16 characters long to counter modern GPU cracking speeds.
If you’re having trouble coming up with a very complex password, or you need a password that you’ll be able to remember without the help of a password manager, then err on the side of longer = better.
A password such as Gustwoshoeshavenpartyextraordinaire might not fit the first criteria (variety of characters), but it’s long which makes it that much harder to guess. Longer passwords will significantly improve entropy and help you create a secure password.
Passphrases are sequences of unrelated words like “battery-horse-staple-correct” and are often superior to complex short passwords because they are easier for humans to remember but harder for machines to guess due to length.
This chart with data sourced from Hive Systems and Security.org does a great job of demonstrating how password length clearly influences the security of your password.
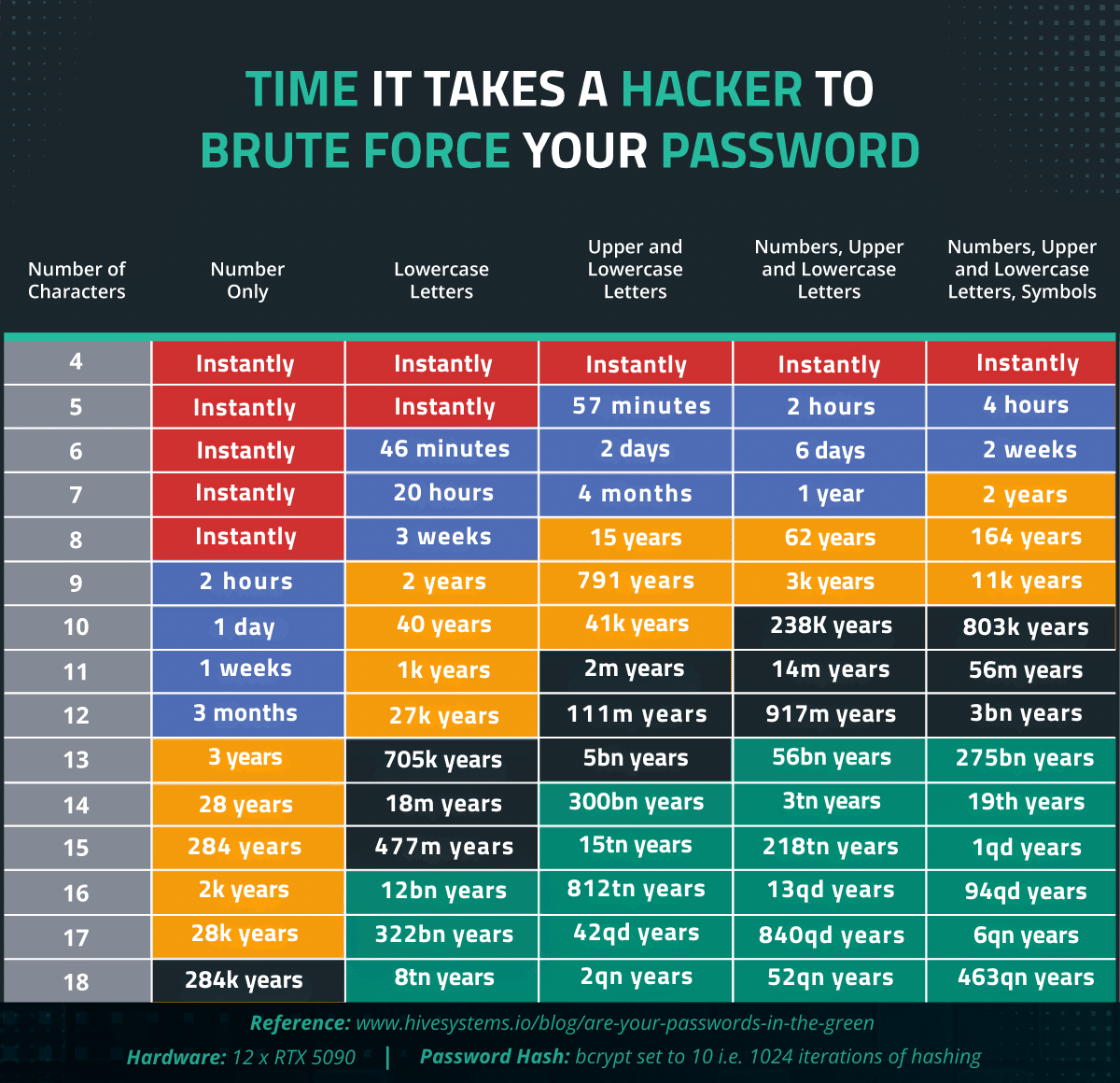
It’s really all about password entropy. The longer the password, the greater the time it will take to brute force.
3. Never include personal information in your passwords
More than likely, everyone on social media knows what your kids’ and pet’s names are. Keep those details out of your passwords!
You know those fun social media surveys that ask for your birthday and your favorite color? They’re mining your data hoping that you’ve used that info within your passwords.
Don’t make it that easy for them! Passwords should never include personal data that is unique to you. The more random, the better.
4. Avoid using passwords that have a record of being stolen
Attackers regularly leverage databases of known passwords in dictionary attacks. This type of attack is performed automatically by going through a list of passwords in the hopes that the password they’re guessing is contained in the list.
So, if you’ve already experienced a data breach, it’s likely that some of the passwords you’re currently using have been exposed.
You can comb through a list of exposed passwords and search for passwords that might be breached here: https://haveibeenpwned.com/Passwords
If you notice passwords similar to yours that have been compromised, change them immediately!
5. Don’t recycle your passwords
Every account needs to have an original, unique password — no exceptions!
Think about recent data breaches that have occurred. Not all of them are from really important accounts like your bank account, some have occurred on lesser accounts such as the Fitness app on your phone.
If a seemingly innocuous account (Fitness app) shares the password with a more important account (bank) and the data is leaked, then you’re in trouble. It might not matter if your Fitness app details get spilled, but your bank account info that shares the same password is a huge deal.
Making sure that all accounts have their own passwords is an obvious way to cut down on that threat and avoid being affected by credentials stuffing.
6. Use a password manager to securely encrypt and generate strong passwords
If the thought of trying to remember every unique password for all of your accounts makes you woozy, then I have the solution for you!
The easiest way to keep you on track is by using password managers such as Bitwarden, 1Password, LastPass and Dashlane. They will keep all of your passwords in one “vault” and even auto-fill passwords if you take advantage of the browser extension. You can also stop worrying about coming up with hard passwords as they can generate them for you.
7. Use Two-Factor Authentication (2FA)
Using 2FA will provide another layer of protection by ensuring the user logging in is actually meant to do so. We urge you to use 2FA on all accounts, but recommend doing so with an authentication app or hardware security key (like YubiKey) rather than SMS.
You can read more about why you shouldn’t use SMS for 2FA here.
Bonus tip: Passkeys – The Future is Here
Many major platforms (Google, Apple, Microsoft, Amazon) now support Passkeys as a primary login method. Passkeys replace passwords entirely by using cryptographic keys stored on your device, verified by your biometrics (FaceID, TouchID). Whenever possible, enable Passkeys in your account settings for a phishing-resistant login experience that requires no memorization.
Brute force attacks: the reason why you should use strong passwords
The reality is that passwords are often the only thing stopping bad actors from gaining unauthorized access to your site and server. And every day attackers gain new insight on how to break passwords. Password lists created from breaches continue to put your site at risk of brute force attacks.
So, what is brute force and why should you care anyways?
Brute force attacks are a common method that attackers use to guess account credentials and even access hidden web pages or admin panels. A tried and true technique that’s been around for decades, brute force attacks employ excessive force or dictionary attacks to attempt to gain unauthorized access to accounts.
For example — if you receive multiple Failed Login Attempts on an account by an unrecognized user, then it’s likely a sign of a brute force attack. Brute force attacks occur when someone (usually a bot or automated tool) continuously tries to login by guessing common password combinations.
Bots are relentless and have nothing but time on their hands. Furthermore, automated tools make it easy for attackers to pre-compute rainbow tables and operate dictionary attacks. Modern AI-enhanced cracking tools can now predict password patterns more effectively, adjusting their guesses based on likely human behavior. This combination makes dangerous territory for website owners who don’t leverage best practices to lock down and secure their accounts.
Let’s take a look at how hackers deploy brute force attacks and steps you can take to mitigate risk and protect your site.
If a hacker does gain access to your server through the administration panel or via FTP, you should be prepared to say goodbye to your great SEO rankings and reputation. Due to the nature of automated attacks, your site could be filled with malware within moments.
By ensuring your passwords are strong and ready to stand up against bots, you’re taking steps to prevent automated attacks and unauthorized access to your website.
Protect your website with strong passwords
Make sure to apply these recommendations to any existing credentials and update any of your accounts that don’t currently follow these password guidelines. That includes any database, FTP, admin, or server credentials in your ownership.
Most of all, ensure that you use strong, unique passwords on your admin panels. It’s not uncommon for older WordPress sites to use admin for the default admin user, which can render these sites especially vulnerable to brute force.
You can also leverage our Web Application Firewall to block unwanted IPs from logging into your site and harden your admin login pages so that you can avoid brute force on your site.
Hackers have lots of tools in their arsenal to hack our sites, let’s make life harder for them by creating strong unique passwords! You can also check out this video for more information on the essentials of maintaining a secure password.
Quick Summary of Password Dos and Don’ts
| Do | Don’t |
|---|---|
| Use at least 16 characters | Use 8-10 characters (too short for modern cracking) |
| Use a Password Manager or Passkeys | Recycle passwords across accounts |
| Enable 2FA (App or Hardware Key) | Rely on SMS 2FA (vulnerable to SIM swapping) |
| Use random passphrases | Include pet names, birthdays, or dictionary words |