Website hacking — the act of exploiting weaknesses to gain unauthorized access to a website, database, cPanel, or admin dashboard — is a reality that some webmasters struggle with. In the hands of bad actors, automated hack tools and exploit kits make it especially easy for hackers to gain access to a plethora of information, including passwords and credit card details.
Not all hackers use their abilities for harm, however. Some turn their expertise towards safeguarding sensitive data and infrastructure. These “Ethical Hackers” or “White Hat Hackers” employ their knowledge to protect against potential threats (instead of orchestrating them).
Nevertheless, the ugly truth remains: there are individuals who exploit their technical skills for nefarious reasons, driven by greed, revenge, or sometimes just for amusement.
The best defense? Understand the common hacking techniques they use and take a defensive stance to help protect against and prevent a compromise in your environment. In this post, we’ll cover the most common website hacking techniques — arming you with knowledge to protect your site from hackers and malware.
Contents:
Common Website Hacking Techniques
While website owners often implement security measures, overlooked vulnerabilities can leave them open to a hack — underscoring the importance of hardening your website and patching your website software against attackers. So, let’s take a look at the most common hacking techniques used by attackers.
1. Phishing & Social Engineering
Phishing is an attack that occurs when bad actors disguise themselves as trustworthy entities, luring victims into revealing sensitive information. Targets of phishing and social engineering techniques can range from individuals to large corporations, with attackers seeking login credentials, credit card numbers, or other personal data.
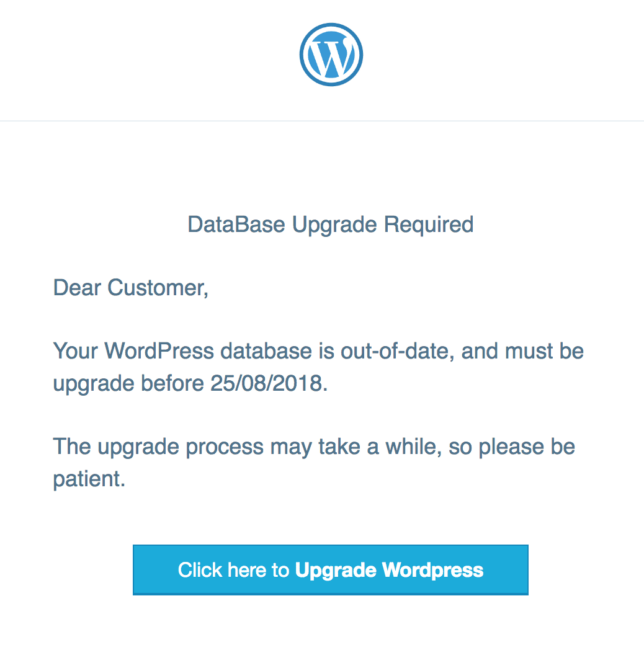
One of the most familiar phishing techniques is deceptive phishing, where hackers impersonate legitimate companies, duping victims into handing over their data. Link manipulation is another common method where attackers mask malicious URLs, making them appear as though they belong to authentic websites. Then there’s pharming, redirecting a legitimate website’s traffic to a fake alternative. Attackers are also using advanced technologies like AI to enhance phishing campaigns by crafting more persuasive and personalized messages.
Some common characteristics of a phishing attack include peculiar or urgent requests from familiar companies or individuals, or convincingly designed login pages. For example, we’ve seen fake WordPress database upgrade notifications aimed at harvesting user credentials for unauthorized access to systems.
2. Cross-Site Scripting (XSS) Attacks
Cross-site scripting (XSS) is a dangerous vulnerability frequently found in web applications. It allows attackers to inject malicious scripts into web pages viewed by others, enabling bad actors to attack unsuspecting visitors or steal their sensitive data.
XSS attacks can be categorized into a number of different forms, including:
- Stored XSS: where the injected malicious script is stored on target servers in places like databases or comment fields, which then becomes harmful when the victim retrieves the stored information.
- Reflected XSS: where the malicious script is mirrored off the web server in responses like error messages or search results and delivered to the victim through a medium like an email or malicious link; the harmful code is then executed when it is reflected back to the user’s browser from the “trusted” server.
- Blind XSS: where the hacker’s malicious payload is saved on the server via front-end forms and triggers when accessed by the backend user or admin.
- DOM-Based XSS: where the attack payload is executed by modifying the DOM “environment” in the victim’s browser.
Common indicators of an XSS attack include unpredicted activities on a site, such as pop-ups or unexpected content changes. For instance, attackers can hijack a WordPress admin session to create rogue users or install a malicious plugin.
To mitigate XSS attacks, user inputs need to be effectively sanitized to prevent intrusive scripts from rendering onto web pages. This could involve using allowlist values, managing HTML in inputs, sanitizing values, using HTTPOnly flags on cookies, and employing a web application firewall (WAF) for added protection against attacks.
3. SQL Injection Attacks
SQL injection (SQLi) is an attack targeting web applications and websites that use SQL databases. Attackers inject malicious SQL code through input fields on a website, providing them unauthorized access to sensitive data like customer records, intellectual property, or other sensitive personal data.
Attackers use various methods for SQL injections. They might manipulate web page input to alter and execute commands on the database server or exploit database errors to obtain confidential information. SQLi attacks typically occur via web page or application input such as search boxes, form fields, or URL parameters.
Common types of SQL injection techniques include:
- Union-based SQL Injection: This common method extracts data by extending the original query results with the UNION SQL operator.
- Blind SQL Injection: Attackers pose true or false questions to a database to decipher information based on the application’s response.
- Boolean-based SQL Injection: Attackers manipulate database responses using Boolean operators, enabling them to deduce whether their malicious input returned true or false, even when no explicit data is returned.
- Error-based SQL Injection: Used when error messages return full query results to reveal confidential database information.
- Time-based SQL Injection: The attacker delivers SQL queries that prompt the database to delay its response, thereby using the response time to determine whether the query outcome is true or false.
To protect against SQL injection attacks, you’ll want to keep your website software patched with the latest updates or use a web application firewall to mitigate risk.
4. DDoS Attacks
Distributed Denial of Service (DDoS) attacks primarily aim to disrupt the regular functioning of web services or applications. The attack overwhelms targeted servers, networks, or services with a surge of internet traffic, causing outages or substantially slowing down the website and service.
DDoS attacks cover a spectrum of tactics, exploiting various aspects of a network connection. Usually, they leverage multiple compromised devices to orchestrate a coordinated, massive traffic flood.
Some common types of DDoS attacks include:
- Volume-Based Attacks: These attacks overwhelm a system’s bandwidth with massive data volumes, causing network congestion. Common kinds include ICMP, UDP floods, and other spoofed-packet floods.
- Protocol Attacks: These focus on exploiting vulnerabilities in server protocols to consume server resources, thereby causing a denial of service. Examples include SYN floods, fragmented packet attacks, and Ping of Death.
- Application-Layer Attacks: These attacks target specific application layers, mimicking genuine requests to overwhelm the server. They are harder to detect due to their seeming authenticity.
Symptoms of a DDoS attack may include a sudden surge of requests to a specific endpoint, unusual traffic spikes, difficulty accessing your website, slow loading files, unresponsive servers, traffic overload from a single device type, geolocation or browser version, or internal server errors — all of which require immediate investigation.
Blocking attacks require a multi-layer approach. Network monitoring and traffic analysis can help identify unusual spikes that may signal a DDoS attack. Employing rate limiting, IP filtering, or geo-blocking can also help block suspicious traffic and mitigate DDoS.
5. Plugin & Theme Vulnerability Exploits
Plugins and themes are incredibly powerful components that can offer a wide range of benefits to your CMS. However, if a vulnerability or bug is present in the software that causes a security loophole, hackers may exploit these defects to infect your site or gain unauthorized control over your environment.
Attackers capitalize on these security loopholes to launch a variety of attacks ranging from unauthorized access to defacing websites, injecting malicious scripts, or even taking control of the entire server.
Nulled plugins and themes — pirated versions of premium components — provide another avenue for exploit, as attackers often embed malicious code and backdoors in the pirated software. Oversights in setting restrictions or defining roles can also potentially provide users more access than necessary, giving a gateway to exploit insecure permissions.
Automated hack tools make it even easier for hackers to identify and target websites with outdated software, underscoring the importance of regular software updates to help mitigate risk. And be sure to avoid installing nulled plugins or themes to help protect against malware and website backdoors.
6. Brute Force Attacks
Unlike a lot of the other techniques listed in this post, brute force attacks don’t rely on software vulnerabilities within your website’s environment. Instead, brute force relies on weak credentials and poor password security to gain unauthorized access to a website or account.
Brute force attacks primarily target login credentials of websites, emails, servers, or any secure network requiring password authentication.
Some common types of brute force include:
- Simple brute force attack: Attackers try all possible password combinations. This method is time-consuming and uses significant computational resources.
- Dictionary attack: With the help of common base terms from dictionaries, attackers sequentially attempt variations of these base terms, thereby increasing the success rate by exploiting the balance between users’ tendency to use common words and the need to meet password complexity requirements.
- Hybrid brute force attack: This method combines the dictionary attack alongside brute force techniques to guess more complex passwords. Having definitive information like the number of characters or other details about the makeup of a password can greatly speed up a hybrid attack.
- Credential stuffing: This attack leverages usernames and passwords leaked from data breaches to attempt login. This highlights the importance of updating your username and password if your data has been involved in a cybersecurity breach.
Brute force relies on weak passwords. A strong password combined with limiting unsuccessful login attempts and multi-factor authentication will make it much harder for attackers to guess your website credentials.
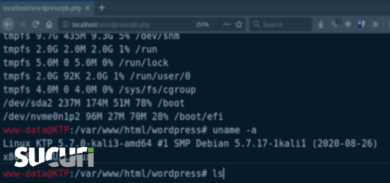
7. Code Injection Attacks
Code Injection, also referred to as Remote Code Execution, involves embedding harmful code into scripts or executable files. Hackers first locate attack surfaces in an application, such as file uploads, form fields, or cookies, that accept untrusted data for executing codes. This vulnerability can be used as a backdoor as the infiltrated code can help attackers upload and modify files, create or delete CMS users, and even launch full featured web shells.
Code injection attacks usually stem from poor quality of code in the web application. To mitigate risks, website developers should adhere to the recommended guidelines for developing secure applications. Webmasters who use third-party software for their websites should keep it fully patched. A good website firewall can also help block malicious requests trying to inject unwanted code into web applications.
8. DNS Spoofing
DNS Spoofing, also referred to as DNS Cache Poisoning, is an attack technique where DNS records are manipulated to redirect users to a deceptive, malicious website that mirrors the user’s anticipated destination. Upon landing on the fake site, users may unknowingly log into what they believe to be legitimate accounts, thus providing the attackers with access to credentials and sensitive information. Furthermore, the deceptive website could download and install worms or viruses on the user’s device, granting the attacker ongoing access to user data and devices.
This mode of attack exploits DNS and its associated vulnerabilities. The methodology can vary; attackers may manipulate the address resolution protocol (ARP) to access router traffic and alter domain name resolution records, modify the DNS server’s records to divert traffic to the malicious site, or manipulate an intermediate name server’s caching system to orchestrate a Man-in-the-Middle (MITM) attack.
Repercussions of DNS Spoofing can be severe, from stealing sensitive user data to gaining sustained access to users’ devices — and in rarer cases, resulting in ransomware. Additionally, by rerouting traffic from valid sites to an attackers’ rogue third party-site, hackers can boost their site’s authority and search ranking, thereby drawing more traffic to the malicious domain in the future.
9. Cookie Theft
Cookie theft, a threat to website owners and users alike, involves hackers stealing cookies from users’ computers to access personal data or login information. Cookies help websites remember users and customize experiences. However, if exploited by bad actors, they can be used to hijack user sessions, leading to unauthorized site access — a common method of session hijacking.
Cookie theft can originate from several sources, including:
- Web based: Personal cookies can be stolen when malicious code is injected into a website and executed in the user’s browser, as seen with XSS attacks.
- Client side: Cookies may be stolen from the browser by malware on the local computer.
- Man-in-the-middle (MITM) attacks: Attackers intercept communication between the user’s browser and the site to steal cookies or sensitive information.
Despite cookies being the safest way to store session data on the user’s end, they require proper protection as WordPress utilizes cookies to maintain user logins. You can help prevent cookie theft with proper website hardening and security measures such as secure SSL encryption for your site, website firewall, and keeping your computer free of malware.
10. Clickjacking
Clickjacking, also known as a UI redress attack, Is a technique that tricks users into clicking links or buttons that perform unexpected functions. This can involve overlaying a deceptive layer over a legitimate website, misleading users to interact with hidden elements unknowingly.
Some common clickjacking methods include:
- Invisible iframes: Involves layering an invisible iframe to bait users into clicking on malicious content.
- Pointer events: Floating div tags cover target UI elements to trick clicks onto underlying iframes.
- Transparent overlays: Transparent frames are layered over site buttons or links, hijacking unsuspecting users’ clicks.
Any action that involves a single click on your site could in theory be susceptible to clickjacking. However, you can mitigate risk by adding X-Frame-Options headers to your site, setting up a content security policy, and using a web application firewall.
11. Man-in-the-Middle Attacks
A man in the middle (MITM) attack occurs when a perpetrator intercepts communication between a user and an application to steal personal information like login credentials or credit card numbers.
E-commerce sites are often the targets of MITM attacks, with stolen information being used for identity theft, fund transfers, or advanced persistent threat (APT) assaults. MITM attacks are comparable to a mailman stealing account information from your sealed bank statement.
The execution of an MITM attack involves two stages: interception and decryption.
Interception can occur passively, through the creation of malicious WiFi hotspots, or actively, by employing techniques like IP spoofing, ARP spoofing, or DNS spoofing. These methods misdirect user data travel, channeling it through the attacker’s network instead.
After interception, the attacker then needs to decrypt any SSL traffic. This could involve HTTPS spoofing, SSL BEAST which targets a TLS version 1.0 vulnerability, SSL hijacking, or SSL stripping, each one designed to intercept, control, decrypt and reveal user session data.
Steps to protect your site from hackers
By knowing how hackers operate, you can better protect your site against attacks. Let’s review some basic steps to protect your website and server environments against a hack:
- Regularly patch and update your website software. Ensure all your website software, core CMS, plugins, and themes are up-to-date. Hackers often exploit known vulnerabilities in outdated software.
- Maintain strong passwords for every account. Use strong, complex passwords and ensure that credentials are unique to prevent lateral movement and credential stuffing attacks.
- Limit login attempts on your admin panels and login pages. This will help to prevent brute force attacks against your accounts.
- Set up SSL certificates on your site. Always use secure, encrypted connections (HTTPS) for all operations.
- Set a regular website backup schedule. Regularly backing up your website will make it easier to recover from a compromise or issue with your site.
- Implement two-factor authentication. Multi-factor authentication adds an extra layer of security to prevent unauthorized access to your accounts.
- Monitor website and server traffic. Regularly monitoring your traffic can help quickly identify any unusual spikes that could indicate a DDoS attack or indicators of compromise.
- Scan your website and server for malware. Regularly scan your website environment for malicious code and unusual activity. Respond quickly to threats that arise.
- Use secure and reliable DNS servers. Regularly monitoring your DNS records can help you catch any unauthorized changes early.
- Restrict file uploads to your website. Limit and secure file uploads, as they can be a pathway for hackers to introduce malicious scripts.
- Set up a Content Security Policy (CSP). A CSP can help prevent cross-site scripting and clickjacking attacks.
- Get a website firewall. Use a web application firewall (WAF) to help patch against known software vulnerabilities and filter out malicious traffic before it reaches your website and server.
Looking for a hand preventing hacks and cleaning up? Our team is available 24/7 and loves to chat about website security!