*By Tony Perez and Daniel Cid
As many of you are aware we released a website protection tool, CloudProxy WAF/IDS, at the beginning of the year and over the past few months we have been working with the data we’ve been accumulating. We’re finally at a place where we think we can provide better insight into the world of website attacks.
What we’re hoping to do is provide a monthly summary, similar to what you’ll read here that helps you understand the various website attacks we see via our CloudProxy WAF/IDS. It will also, hopefully, shed insight into the growing online threats that website owners face daily.
September 2013
We have some very small and some big sites with us. And the first thing we noticed is that even the smaller sites get attacked quite often. All sites do.
Every web site gets attacked. And that happens daily. Many times per day.
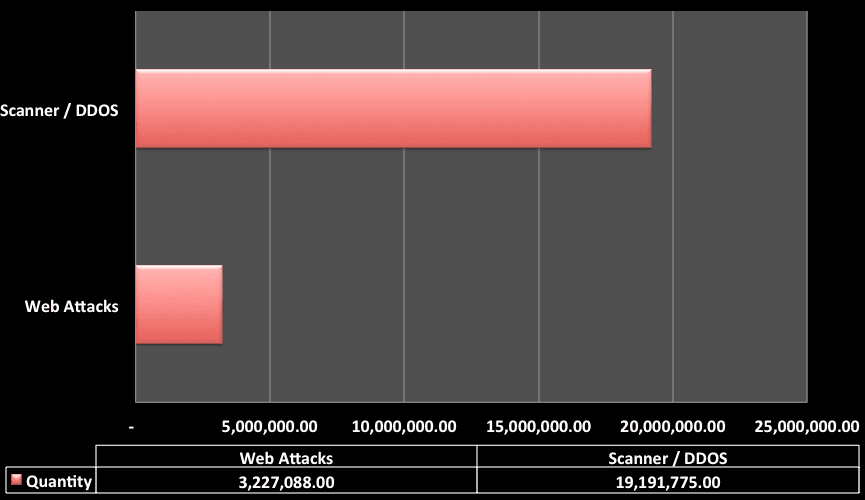
For the purpose of this report we’re going to break this into two high-level attack cateogires – Denial of Service (DOS) and Web Attacks. Although DOS attacks are a form of web attack to better understand and normalize the data it’s best we segment the information out, you’ll see why in the chart below:
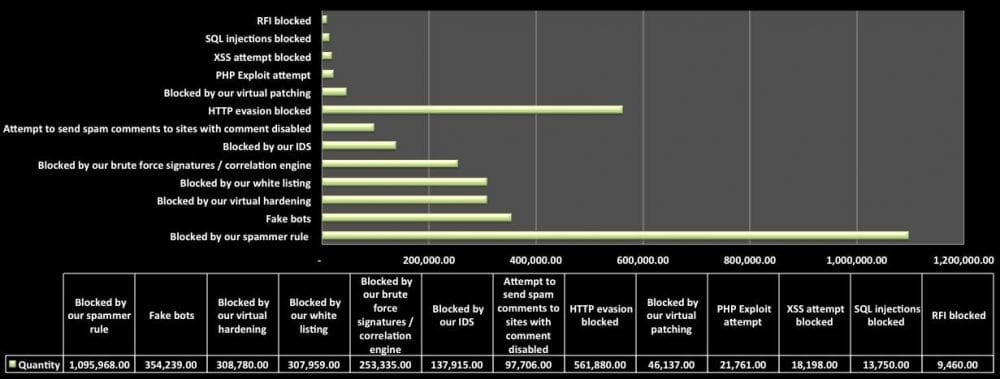
In this chart we see a total of 22,418,863.00 attacks were blocked via the CloudProxy. Interestingly enough, 85%, 19,1191,775, of those attacks were layer 7 DDoS, DoS / High frequency scanner type attacks. Note that we are talking about layer 7/HTTP denial of service, not the ones targeting lower layers. Of the 3 million or so attacks the distribution was as follows, based on our internal classification of attacks:
Interestingly enough, one of the biggest attacks we block are spammers, this includes those individuals trying to leave “buy me” comments on your posts to attackers that are trying to register to your site via registration forms and other similar access points.
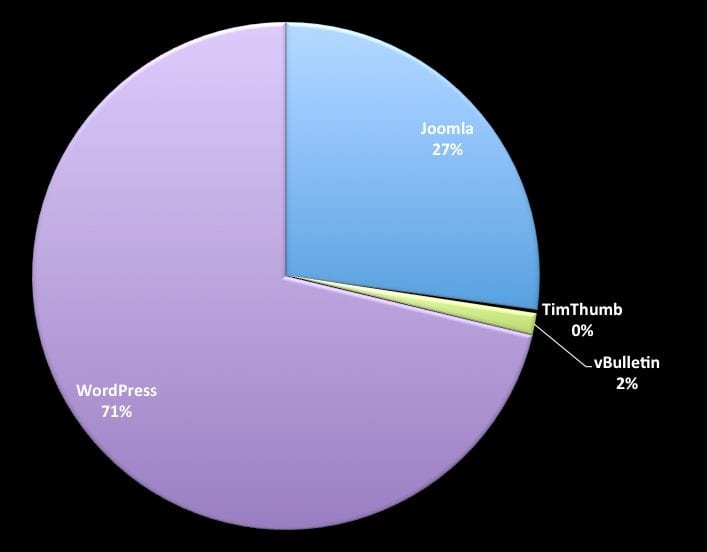
The other very obvious question we found ourselves asking is, “Which platforms appear to be the biggest targets?” Trying to answer this question we came across this distribution of attacks, granted, there will obviously be margin of error here and we don’t have enough data over a longer period to provide a more representative example, but it’s interesting enough none the less.
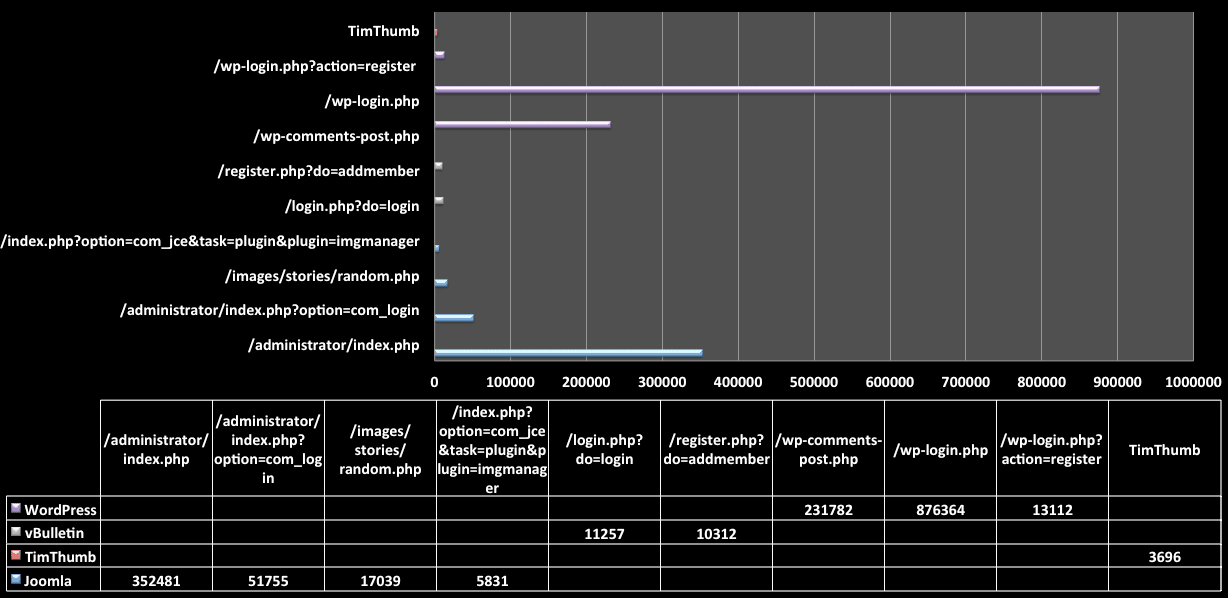
From this data we were able to derive some of the more prominent URL structures being attacked across the various platforms:
When you look at the last chart you might be thinking, ah they are just URL structures, but the focus should be what they’re attempting. In many cases the attack attempts are looking to exploit weaknesses in different features. Take for instance Joomla’s recent issue with the image manager here: /index.php?option=com_jce&task=plugin&plugin=imgmanager every one of the attacks helps us understand a little better what the attack is looking for and in some cases gives us a heads up that something is wrong before it is ever released in the wild.
What is interesting is that we can see the same attacker scanning different sites under our protection and looking for the same type of vulnerabilities.
And it shows what we have been saying to our clients that everyone is a target. Not because someone is really targeting you directly, but because most attacks are targeting a specific vulnerability or platform (or even IP range). If your site falls into their target category, it will be probed.
One example is the latest Joomla vulnerability. Once it was released, attackers started crawling the Internet (and using Google dorks) to find sites that could be vulnerable to it. They don’t care much about the website itself, who owns or what it does, they only care if it’s vulnerable or not.
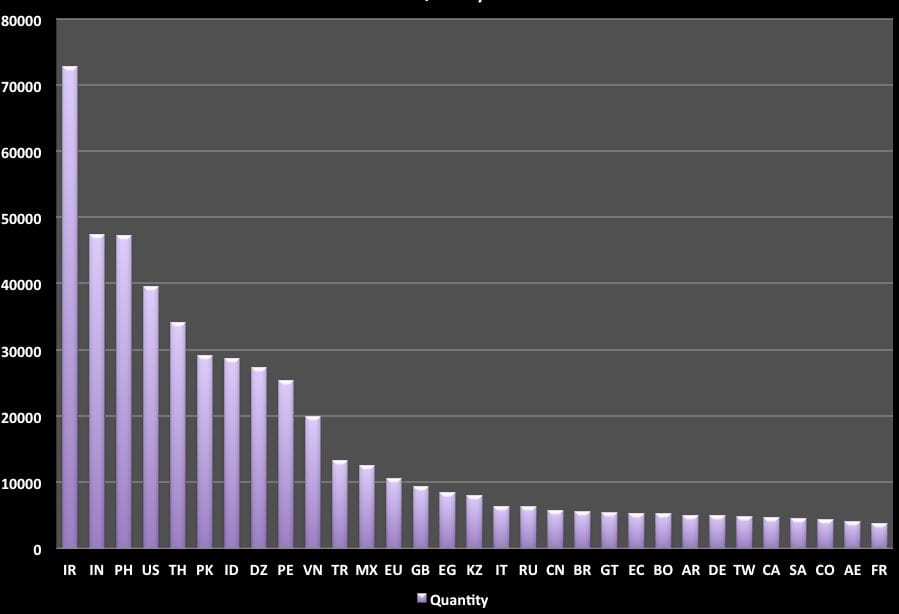
The very last piece of data we found very interesting was the source of the attacks. Looking at the attacks holistically this was the geographic distribution of the attacks by country.
Iran was very busy and the source of most attacks. However, when diving into the data, we saw that it was used mostly in the layer 7 DDoS attacks we were blocking.
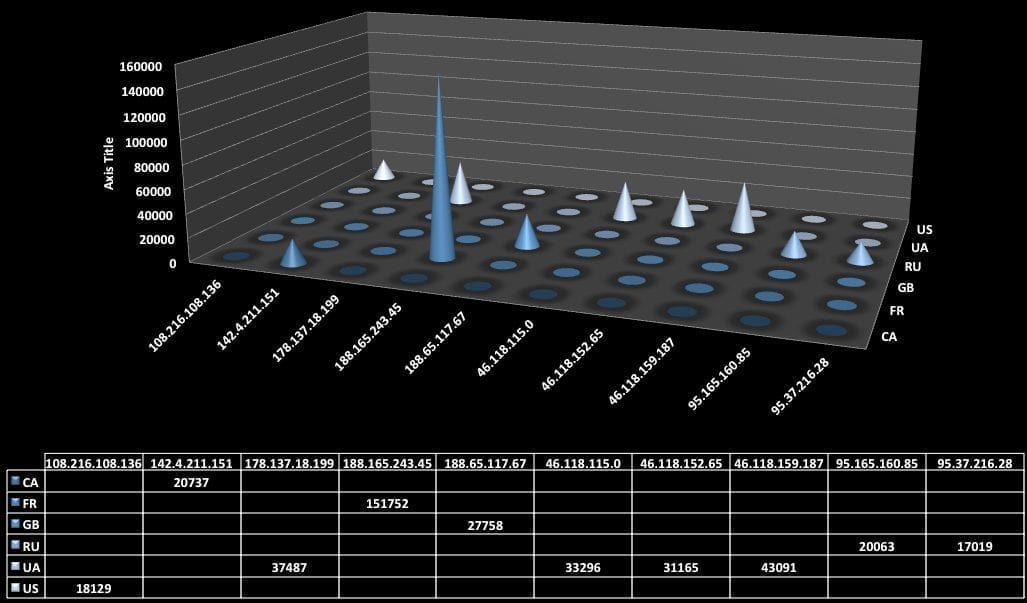
These were the top 10 attacker IP addresses for the month in terms of hits:
Reflecting
This is our first month sharing our data, but we plan to do that every month. Hopefully, with more actionable information to help everyone.
If you have ideas or recommendations for data we should try to include and / or capture please do let us know. We would love to hear them.








3 comments
Excellent article, thank you!
The report provides comprehensive information on the increase or decrease of the company last year, thank you for providing information.
This covers everything, Daniel! Just another awesome share of info! With this, we all have to be with eyes-opened and super-concious about the things, look more and keep track of activity logs.
Comments are closed.