If you are are a regular reader of our blog you probably know about our CloudProxy Website Firewall, it launched publicly a year ago. Since then, our team has been extremely focused on improving it, making it more effective and efficient for everyday website owners.
If you are not familiar with CloudProxy, I highly recommend reading some of the documentation and benefits of it:
In fact, if you have a website, why not try it out?
What is CloudProxy
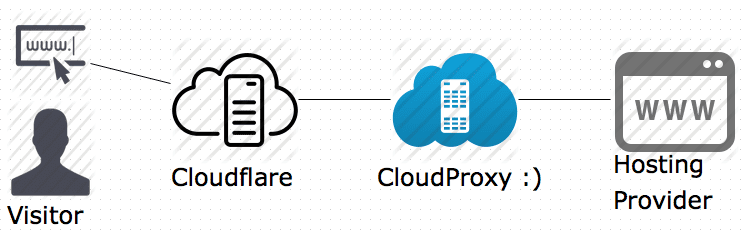
CloudProxy is a Cloud-based Website Firewall with a simple goal: To protect any website from being attacked or compromised. We do this by sitting in the middle, between the internet and your hosting company (origin server), filtering and blocking any malicious requests before they reach the site / server.
We do not like to use the term “WAF” anymore, we focus on threats specific to the website we’re protecting. We also mix in a powerful Intrusion Detection System (IDS), and a log correlation engine to aid the firewall in blocking all malicious attacks. It allows us to move from event-based blocks, to more heuristic and correlation based blocks.
Latest Updates
Let’s get to the point of this post. We have done so many updates lately that I will try to summarize them the best I can.
1 – Support for CDNs
We are focused on security, we’ve been very vocal about this, a byproduct has always been caching and performance. This however has introduced issues with true CDN providers. Because of this we set about reinventing the way we communicate between host servers, CDN’s and our Website Firewall. I’m happy to report this is now fixed and we’re ready for all the CDNs.
If you use Akamai, CloudFlare, MaxCDN or any other CDN service, our Website Firewall, CloudProxy, is now set up to better support you.
This is easily done by adding CloudProxy in between your CDN and your hosting provider, and by marking your site as “behind a CDN” in the configuration panel:
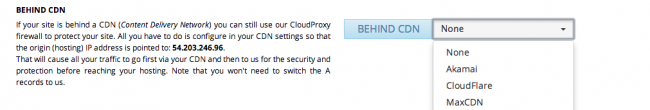
Once that’s done, just edit the “Origin” IP address on your CDN to be our CloudProxy IP address, and you are all set. Are you a client? Yes? This documentation explains how to configure it for CloudFlare.
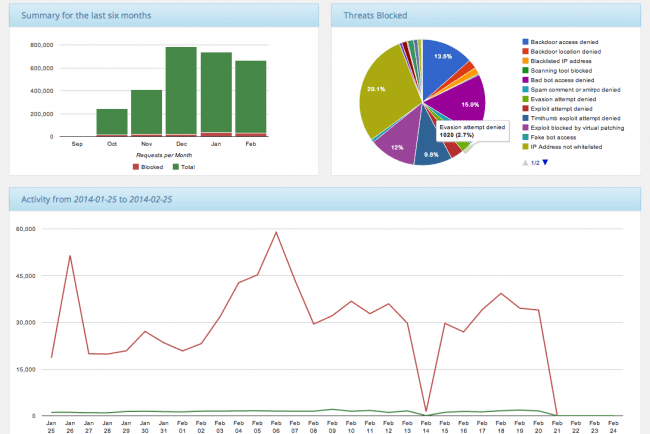
2 – Better Reporting
We have always had a full audit trail and logging in CloudProxy, but we were in need of a better way to drill into the data. Just last week we released a new reporting page, allowing you to see trends, and to analyize deep down into your site’s data. This is just a peek at what it looks like:
We hope that with this new reporting you can get better insight in the types of attacks you’re experiencing, allowing you to better validate your website security posture.
3 – More Points of Presence
Yes, the service is global and until now you were unable to identify a Point of Presence (POP), that has now changed. We have 100’s of servers globally and now you as the website owner can define the Geographic area you want your POP to be in.
In your dashboard, you’re able to define your desired location (e.g., USA, Canada, Japan, Australia, UK and Brazil) and now you can choose where you want your traffic to be from:

If you are in Europe, the UK location is likely your fastest option. Or, if you are in Asia, you can try either Japan or Australia. Don’t know what makes sense? No worries, you can let us choose the default location, allowing us to try and find the best/shortest path available.
4 – Rewritten Back-end, Better Performance, Improved Detection and Cleaner Experience
Everything outlined above talks to the aesthetic changes
Above are just some of the visual things we added, but more importantly we’ve rewritten the back-end, the core – the engine, to better scale and more effectively detect issues, allowing us to reduce the noise – i.e. false positives. We continue to use the same mulch-tiered approach to protection, application profiling, whitelisting, blacklisting and IDS, but it’s all more tightly integrated.
- We added hundreds of new virtual patching/hardening signatures.
- We greatly improved our SQL injection detection.
- Our correlation engine is now blocking and detecting brute force attacks and DDoS better than ever.
- And the whole experience has been re-designed while performance was greatly improved.
It looks like a sales pitch, but we are just proud of all the work our team has been putting on it lately.
Let us know if you have any questions or wish to share your experiences with CloudProxy. If you’re not using CloudProxy yet, we recommend you get our website firewall today.









6 comments
Since it’s the first time I put out a website, I was looking for something like the CloudProxy and the one by Sucuri is really good. I’m already using the service -they teach you and keep you updated on every little progress, and you know exactly where your money is going.
Well all i can say that Sucuri/Cloudproxy has been mitigating all the attacks to my website very well, few months ago I had to deal with a lot of attacks myself and false positives on my website, but now after been using cloudproxy for more than 4 months i hasn’t been take it down since then.
I highly recommend Sucuri/Cloudproxy services to anyone they have a great panel, they have the best ddos mitigation for layer 7 out yet in a click of a button you can activate and see in real time the attackers and where the ips are coming from I will highly recommend you to switch to Sucuri/Cloudproxy they day of today they won’t disappoint you.
My Website hxxp://Hfantasy.nl
Best Regards
I had CloudProxy but had to discontinue it. My host, which is BlueHost, interpreted all the incoming hits from the same IP address as an attack and would routinely shut down my blog. I had to stop the service, but I would love to have it again if any of these improvements you mention have solved this issue.
I’m having the exact same problem between Sucuri and GoDaddy. I’ve been ping ponged between their tech support departments for a couple weeks now. It is so discouraging and such a time suck– costing both my client and me time and money. It’s the same problem: GoDaddy says they’re not blocking the proxy server IP, Sucuri says they are.
Haven’t known whether to switch hosts (loss of $$, time) or find a different protection service.
The technical support I’ve received with Sucuri has been some of the most frustrating of my life. They have zero interest in actually helping us solve our problem. It’s clear that they just want to bounce back the support request with the minimum amount of work on their part. I’ve wondered if I’m talking to robots or people who don’t speak English very well?
I’m now searching for other people who have had similar problems with Sucuri, and am grateful to have found these comments so at least I know I’m not alone!
Hi Ashley
What is your ticket number? I’d like to get a better sense of what you are experiencing. This should not be as you are describing and think it can be resolved.
Would you mind sending me an email at tony@sucuri.net ?
I can assure you that your statements of the quality and care of support is inaccurate, and I’d like to get to the bottom of it.
Thanks
I’ve had the same issue as the previous commenter, Claudia. Spent several hours on the phone with Bluehost and frustrating back and forth via email with Sucuri, and finally had to stop the service. Bluehost says they’re not blocking the proxy server IP, Sucuri says they are. And I’m caught in between. The only way to at least get the site up is to remove the firewall. I’d love to have it up again, if the solution can be found.
Comments are closed.