When it comes to an organization’s security, business email compromise (BEC) attacks are a big problem. One primary reason impacts are so significant is that attacks often use a human victim to authorize a fraudulent transaction to bypass existing security controls that would normally be used to prevent fraud. Another reason is that social engineering lures may be expertly crafted by the attacker after they have been monitoring a victim’s activity for some time, resulting in more effective phishing campaigns with serious security implications.

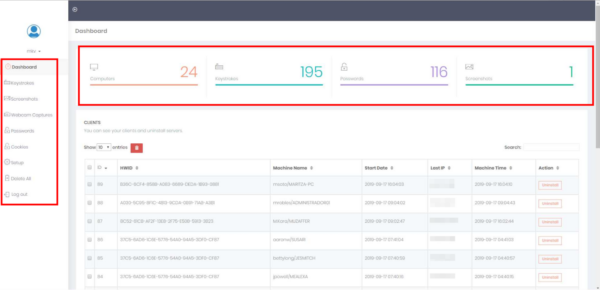
Earlier this year, we were cleaning an infected website when we found an interesting directory named ./webpanel/. Within the directory was a hosted control panel interface used to manage devices infected with a trojan malware variant.
Command & Control (C2) Panels and C2 Servers
Oftentimes when an attacker has infected multiple devices (e.g infected Windows computers), they will use what is known as a C2 server to host a control panel interface to remotely manage the infected devices from a centralized location. These interfaces are very convenient for the attacker, since they only have to visit the C2 server’s URL to control malware on the infected devices instead of individually for each infected device.
To set up the interface, attackers usually gain unauthorized access to a legitimate website, upload their C2 control panel interface, then “hide” it in a few levels of directories. This allows them to use an existing domain name and hosting server instead of fraudulently using someone else’s payment information to sign up for those services, significantly reducing effort on their end.
Trojan Spyware: Origin Logger
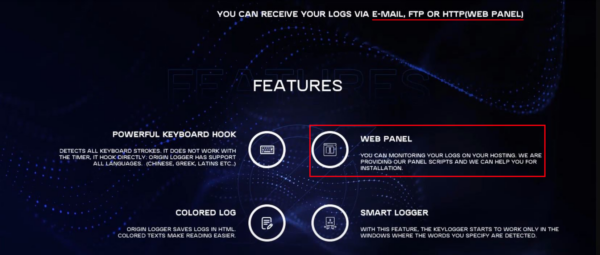
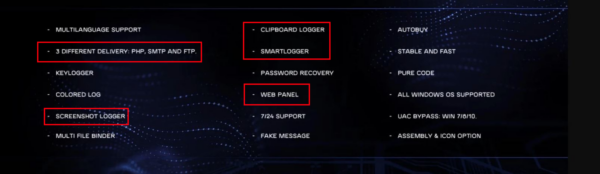
The C2 panel interface matches the same panel that is used for the malware Origin Logger, which is bundled with the C2 panel and then sold to attackers. As the name suggests, its primary purpose is logging keystrokes, clipboard data, HTTP cookies, taking periodic screenshots, and viewing the webcam of infected computers.
The creators even took the time to create marketing material for their Origin Logger malware:
Shadowing
When a device is infected with the Origin Logger malware, it becomes easy for an attacker to familiarize themselves with an employee’s sensitive information, including schedules and communications. For industries that use expensive equipment or large orders, this intel can create a plethora of opportunities for the attacker.
For example, during our investigation we found that one of the monitored infected devices was assigned to an oil field services supervisor. The attacker probably already knew that expensive, large, and hard-to-transport equipment is used on active oil fields, but they needed more specific information to craft a personalized phishing campaign.
The Origin Logger malware provided additional information to the attacker by taking a screenshot as the supervisor writes an email to management:
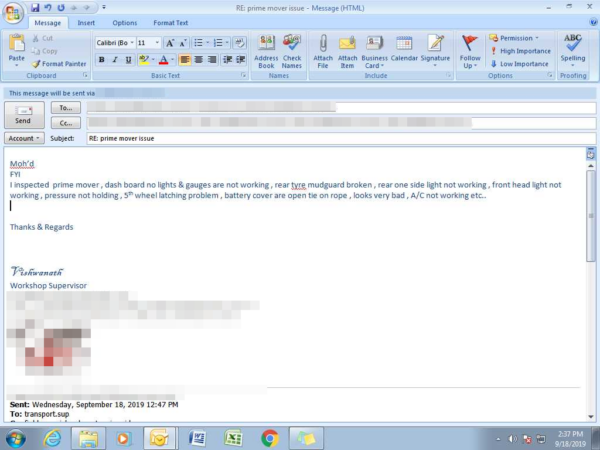
As shown in the above image, the email text is about a piece of equipment called a “prime mover” (heavy utility truck) that needs to be replaced/repaired. Operations could be disrupted if they don’t have the equipment to do their jobs, so this could be an opportunity for the attacker to craft a BEC email asking for payment for a “prime mover” truck. And to avoid suspicion when asking for payments to be routed to a new or unfamiliar bank account, the attacker can simply create a sense of urgency by saying it was ordered quickly to avoid service disruptions or some other similar excuse.

Attempted BEC
What’s especially interesting is that it seems that the attacker infected his own device, possibly for testing or troubleshooting purposes, but never actually removed the malware — so screenshots of their own device were also being sent back to the C2 server! This is a big failure in their operational security as it gives us direct insight into some of the attacker’s tactics and operation.
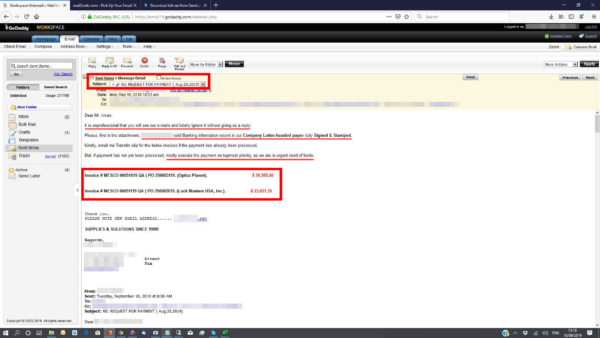
The following screenshot shows us a BEC email originally titled REQUEST FOR PAYMENT in the Sent folder. The email contents include a request for payment to the bank details provided in the attachment. Payments are for two invoices — together they total over $52,000 USD, so it is easy to see why attackers find it worthwhile to infect devices and monitor them for BEC opportunities.
And how do we know it is the attacker? We also found a screenshot of their Discord chat with a fellow attacker, where they discuss losing access to the C2 panel due to someone (likely the website owner) deleting files.
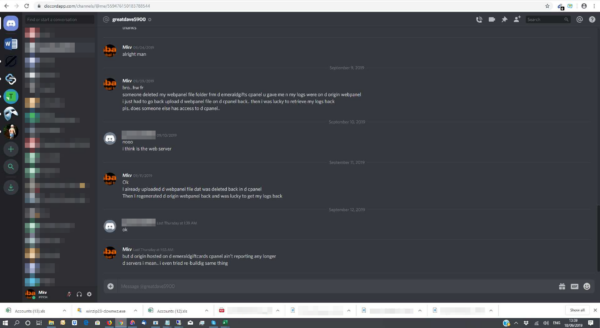
Unfortunately, deleting the ./webpanel/ directory containing the C2 panel interface files did not fix the problem. The attacker knew the website’s cPanel password, so they just re-uploaded the spyware. This is why we always recommend resetting all of your passwords after a compromise, along with any FTP/SSH users: removing the malware is not always enough to cut off unauthorized access to the website.
Conclusion
The infected website that was found hosting the C2 panel happened to share a server with a separate WordPress website with a known vulnerability. By exploiting the vulnerability, the attacker was able to access cPanel and plant their spyware.
This incident highlights the importance of ensuring all website software and extensible third-party components are patched with the latest security updates. If you want to detect malicious behavior and other indicators of compromise on your website, I strongly encourage you to employ file integrity monitoring and alert services.
In the event that your website is suffering from malware reinfections, you can refer to our hacked website guide which outlines steps to remove malware. If you need a hand, we’re always here to help.