Phishing is a malicious attempt to obtain personally identifiable information of a victim. The first thing to keep in mind about phishing is the goal of the attackers.
In the first post of this series, we have explained how to recognize a phishing campaign. Today, we will focus on the objectives behind phishing attacks.
Why do Hackers Create Phishing Campaigns?
There are many reasons why hackers design phishing campaigns, including attempts to obtain:
Financial Data
The most common goal for attackers is to obtain financial information. This might be your credit card information, banking credentials, or even for you to send money to them.
For example, in August we wrote about a skimmer campaign in which two site domains were created for phishing two Canadian banks:
- rbcroyalbank[.]com.ng – Real address of the Royal Bank of Canada is rbcroyalbank.com
- www1-bmo[.]com.co – Online banking for the Bank of Montreal is www1.bmo.com.
In this case, the blackhat hackers made fake bank websites in order to have access to a large amount of financial data.
Personal information
Personal information is very valuable for attackers as it allows them to steal a victim’s identity and profit from it. Personally identifiable information includes common personal data, such as:
- Social security number (SSN)
- Name
- Address
Attackers may also phish for less-known information that one might not consider secret, such as:
- Name of your favorite teacher
- Name of your first pet
- Street where you grew up
Did you notice something in common with this last list’s questions? Yes, these are commonly used questions for identity verification and account recovery!
With this information, it is possible for malicious users to recover personal accounts and reset passwords without even knowing what we usually consider “private” information about the account holder.
Clicks and Views
As we saw last year with a Fake Volkswagen Phishing Campaign, what attackers might want is more exposure.
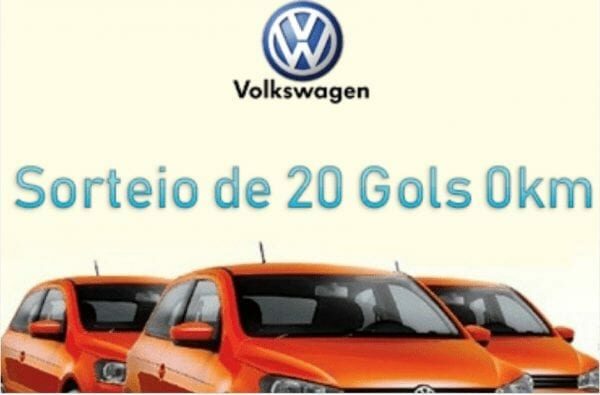
By pretending to give away desirable items — such as cars, money or free trips — the attackers can get a lot more exposure via social networks. They can profit from this exposure a few different ways:
- Including advertisements and getting ad revenue
- Harvesting personal information by adding forms requiring a name and address to pretend that someone won their contest
This is why if something looks too good to be true, it usually is a scam.
Access to a Website or Computer
Attackers may wish to add more victims to their compromised network. If you have a website, you might be familiar with compromise attempts against it.
In a recent post, we described what attackers do after gaining access to a website, and how these malicious users profit from gaining access to a larger network.
How to Protect Against Phishing Campaigns
The first thing to do is to ensure you can recognize the main signs of a phishing campaign:
- Pages that look legitimate, but includes unusual requests
- Pages that look a little bit odd
- Pages or emails that require immediate actions
When you see anything that looks phishy, don’t click at the page or don’t open the email. With the holiday season upon us, malicious actors do what they can to increase their profits. Don’t help them have happy holidays!
Sign up to our blog feed and be on top of the latest website security news.










