There’s a lot that goes into a website environment in terms of functionality. Due to this, it’s only natural for one of the most commonly asked questions being how websites are usually hacked. In my previous post I talk about the Most Interesting Vulnerabilities of 2021, which should provide more insight into the more recent hacks seen, or caught beforehand.
In this article we’ll be discussing the primary ways websites are infected, and how you can better prevent it from happening.
How to Recognize Spam
First of all, it’s important to recognize what spam is so you can better understand if your website has been compromised or not. Once a spammer has compromised a website they tend to fill either the database of file structure with hundreds or thousands of backlinks to spammy websites that they are trying to promote.
The more websites that point to their spam sites, the higher search engine ranking they will achieve (this is called blackhat SEO).
Spammers tend to promote the same types of products and services over and over again, and some of the major ones we see are the following:
- Pharmaceuticals
- Essay writing services
- Knockoff sports jerseys
- Counterfeit brand name products
- Escort services
- Bootlegged software programs
If you see search results associated with these sorts of keywords showing up in search results when you search your website then there’s a good chance that your site has been compromised with an SEO spam infection.
PRO TIP: To narrow Google searches to only show search results for your website alone, you can use the following “Google dork”:
site:mywebsite.comLogin Access
One of the main culprits involves access control, which means any login area can be vulnerable. Login access doesn’t necessarily have to be obtained via Brute Force.
Another method is also through social engineering which is usually done through a phishing campaign. Of course there are also keyloggers, man in the middle attacks (MITM), and cross-site scripting (XSS) attacks.
It’s important to assess how you authenticate into things such as your host, server, computer, email etc. You should also consider where you store all of your credentials.
Are you using an unencrypted notes app? Or, are you using an encrypted password manager or are you using a simple password so you can store it in your brain?
There are many options for a password manager on the web, and it’s highly encouraged to utilize one and ensure that the access to it is as secure as possible by making sure you have MFA enabled on it.
Vulnerabilities with Software, Themes, and Plugins
Outdated software, themes, and plugins are highly susceptible to being exploited. This isn’t just an occurrence with lesser known ones either, as there is no 100% in security.
Site owners are generally unable to address vulnerabilities themselves and will rely on security patches. That being said, for every plugin, theme, or software installed this is another potential point of intrusion.
A more seasoned hacker may obtain credentials through methods of elevated access via a SQL injection, or through a theme or plugin. Not to frighten anyone though, because as long as you’re keeping the amount of plugins and such to a minimum while keeping them up-to-date as frequently as possible, this should help mitigate many of the risks.
Third-party Integrations
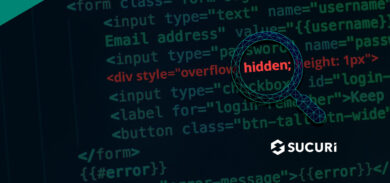
A lot of site owners will download free themes and plugins from non-reputable sources, without fully vetting them first. When this occurs you are possibly opening doors for malicious content to be added to your site without even noticing it.
For instance, if a plugin hasn’t been maintained within the last few years, there’s a significantly higher chance of it being more vulnerable than a regularly maintained plugin by a trusted source.
In order to prevent any third-party element from doing severe damage you’ll want to ensure they have limited permissions to only what’s necessary for the extension/plugin/collaborator to work. Plugins or themes in use on your website which have been abandoned should be avoided, and replaced with something more well maintained instead.
In Conclusion
In terms of security, you want to mitigate the risks as much as possible. Risk reduction, not risk elimination, is the motto to live by here.
Adding monitoring and firewall protection will also be beneficial in the case any vulnerabilities attempt to be exploited or end up being exploited.