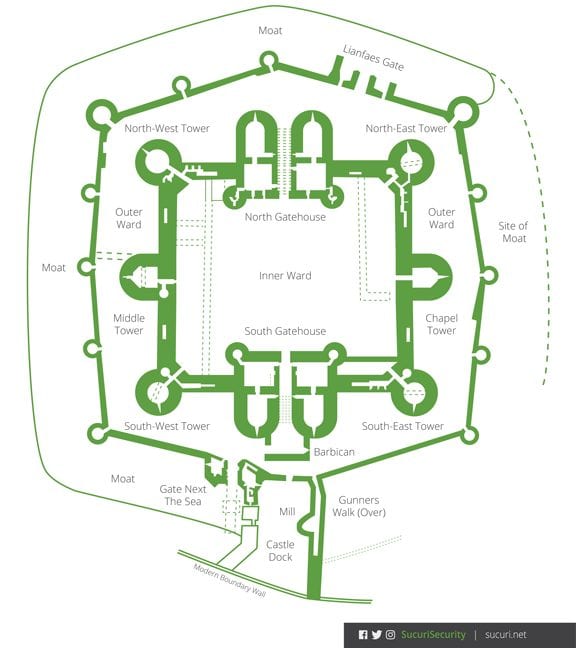
In the field of Information Security (InfoSec) we like to use the phrase defense in depth. Like many things, it is a borrowed term with roots dating back millennia (216 B.C. – the second Punic war). It’s a term that refers to tactics employed by militaries around the world in which they would deploy layers of defenses designed to impede an attacker’s progress, forcing them to exert and exhaust available resources, in turn making them susceptible to counter-attack.
Defense in depth is a concept that can be used to build a strategy designed to identify, mitigate, and eradicate cyber attacks. It’s used across a number of domains can also be employed in website security.
To appreciate this ideology, you have to subscribe to a very simple principle: There is no 100% complete solution capable of protecting any environment.
Website Security
When we talk about website security, like any other InfoSec domain, we view security holistically. Using a defense in depth strategy facilitates this process. A good defense in depth strategy not only looks the depth of the defensive controls but also takes into consideration the breadth of the attack surface and the differing tools across the stack. This approach provides you a more accurate picture of today’s threat landscape. It clearly illustrates that the problem extends well beyond the application or its extensible components.
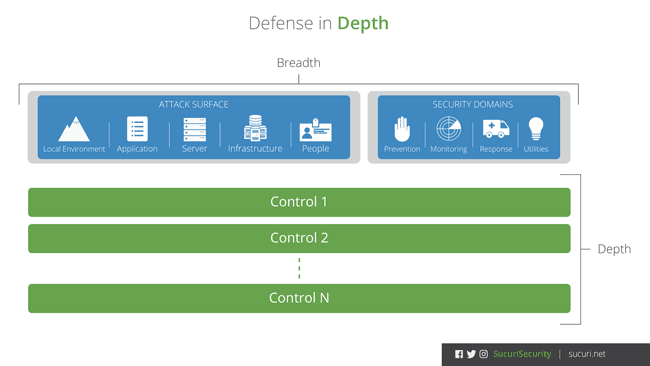
An effective defense in depth strategy will look to implement complementary overlapping defensive controls (i.e. layered defenses) designed to identify and mitigate attacks.
Additionally, employing a defense in depth strategy is something that your organization must subscribe to. The tools you leverage, whether it be an application or cloud security solution, are but a means to an end. No single tool will provide your organization a complete defense in depth strategy. This is because security is more than any one tool, but rather a marriage between people, process, and technology.
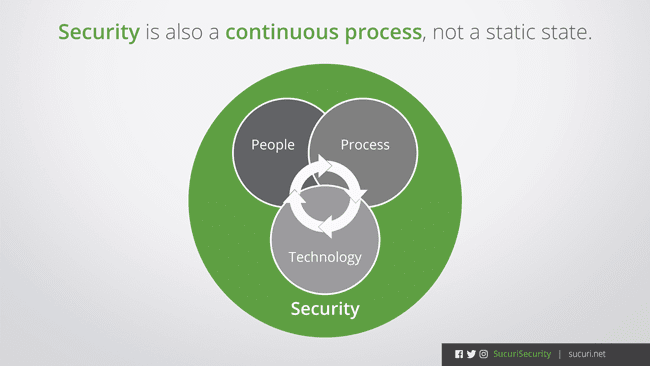
Lastly, it is imperative to understand the difference between a tool that employs defense in depth in its design and solution, versus the defense in depth strategy you must employ as an organization.
An example would be Sucuri’s product offering. Each of our tools is part of a layered defense strategy. From the cloud-firewall looking to mitigate external attacks to our monitors that look for changes, which then are sent to our Incident Response Team to remediate these security incidents.
While we boast the idea of employing a defense in depth strategy in the design of our offering, we can’t say it’s the only defense in depth strategy an organization will need. The strategy involves much more than our tools. Instead, we say that we are a complementary solution to your existing security posture and we encourage you to use any other tools you require to round out your defensive position.











3 comments
Happy to hear “There is no 100% complete solution capable of protecting any environment.”
It is true & so many think otherwize.
I should have been more clear when I wrote this post. I believe Sucuri is as close to 100% as you can get. I know this because I am a customer of Sucuri, Incapsula, Armor/FireHost & CloudFlare ( CloudFlare plans under $3000 are ineffective against most attacks.)
Sucuri is capable of offering levels equal to or better than Armor Complete & Armor Anywhere to put that in perspective Armor Anywhere $2,000 a month minimum.
Armor Complete is approximately $3,500 this is base price.
The ability to use Sucuri on the host of your choosing is a incredible benefit. For agencies like mine who require unique setups for different clients. Sucuri has ability to target many geographic location’s this is something more SEO’s and anyone that cares about their site should focus on the ability to serve content to the end-user with the fastest response time.
Sucuri Accomplishes this even if you’re on a server in the USA and targeting Brazil for instance.
Yes it is true nothing is impregnable and with new botnets and the IoT making it possible for super botnets it is wonderful to know there is protection at a price anyone can afford.
Sucuri’s capabilities are amazing and if you care about your website I would recommend signing up. I am saying this is a client not because I am gaining anything from writing this but to help people.
Thanks @tomzickell:disqus for stopping by and sharing the kind words. It’s a testament to what the whole team is working on.
Comments are closed.