The depiction in the media of hackers tends to be that of balaclava-wearing villains who type furiously in a dark basement, motivated by nothing but evil intentions. However, while this may be true in some instances, by and large the determining factors that result in malware attacks are largely motivated not by ideology or malice but by material interests.
In writing this post I couldn’t help but think of the self-parody TV series CSI: Cyber, specifically the episode where the basement-dwelling, greasy-haired, evil hacker hacks a roller coaster ride, killing everyone on board, simply because he is a bad evil guy who wants to do bad evil things to unsuspecting good people.
Rule number one of cybersecurity is to “think like an attacker“. For this reason it behooves us to understand what makes them tick. In this post we will try to demystify the reasons behind website malware attacks, why they happen, and review some of the most common online threats in order to try to understand them more thoroughly.
Where Malware Attacks Begin
It goes without saying that to engage in cyber crime requires some, let’s say, “flexible morals“. By and large, though, attacks tend to target victims in Western countries and attackers tend to reside elsewhere, far removed from legal frameworks which could provide consequences to their actions.
Top attack countries tend to have poor employment prospects for young people, have decent network infrastructure, and decent public technical colleges where would-be attackers can learn the ropes.
Money, ultimately, is the common denominator to almost all website attacks. After all, malware is a business. In many ways the black market mirrors the legitimate economy with some criminal enterprises reportedly having HR departments and Employee of the Month programs. Other threat actors do exist, such as low-level “hacktivists” and indeed even nation states who act as “Advanced Persistent Threats“, but the type of threat actors which pose the biggest problem to most website owners would fall somewhere in the middle of these different groups.
Let’s go ahead and break down some of the most common website malware attacks and review the financial motivations behind them.
SEO Spam
SEO (search engine optimisation) spam is without a doubt one of the biggest nuisances that website owners face. Backlinks and advertisements for knockoff pharmaceuticals, bootleg brand name products, fake designer watches, torrents, essay writing services, dodgy online casinos, and so on. But what exactly motivates these spammers to infect websites and pump them full of (usually hidden) links to these low-quality, bottom-of-the-barrel spam websites?

The answer is to pump their own SEO with the eventual goal of increasing traffic to their own spammy websites.
All of the less-than-reputable content that I described above all live on websites somewhere – and there is a lot of them. But, how do the owners of these spammy websites convince people to visit theirs? After all, there are many thousands of sites selling spammy goods or services, and many spam-website-operators trying to get in on the game. Not unlike the “regular economy” where websites in the same industry try to out-compete each other with SEO so that they can appear higher up in search results than their competitors, so too does the black market economy selling knockoff viagra and promoting questionable online casinos.
This chart helps illustrate how SEO in general works, both regular and “blackhat”:
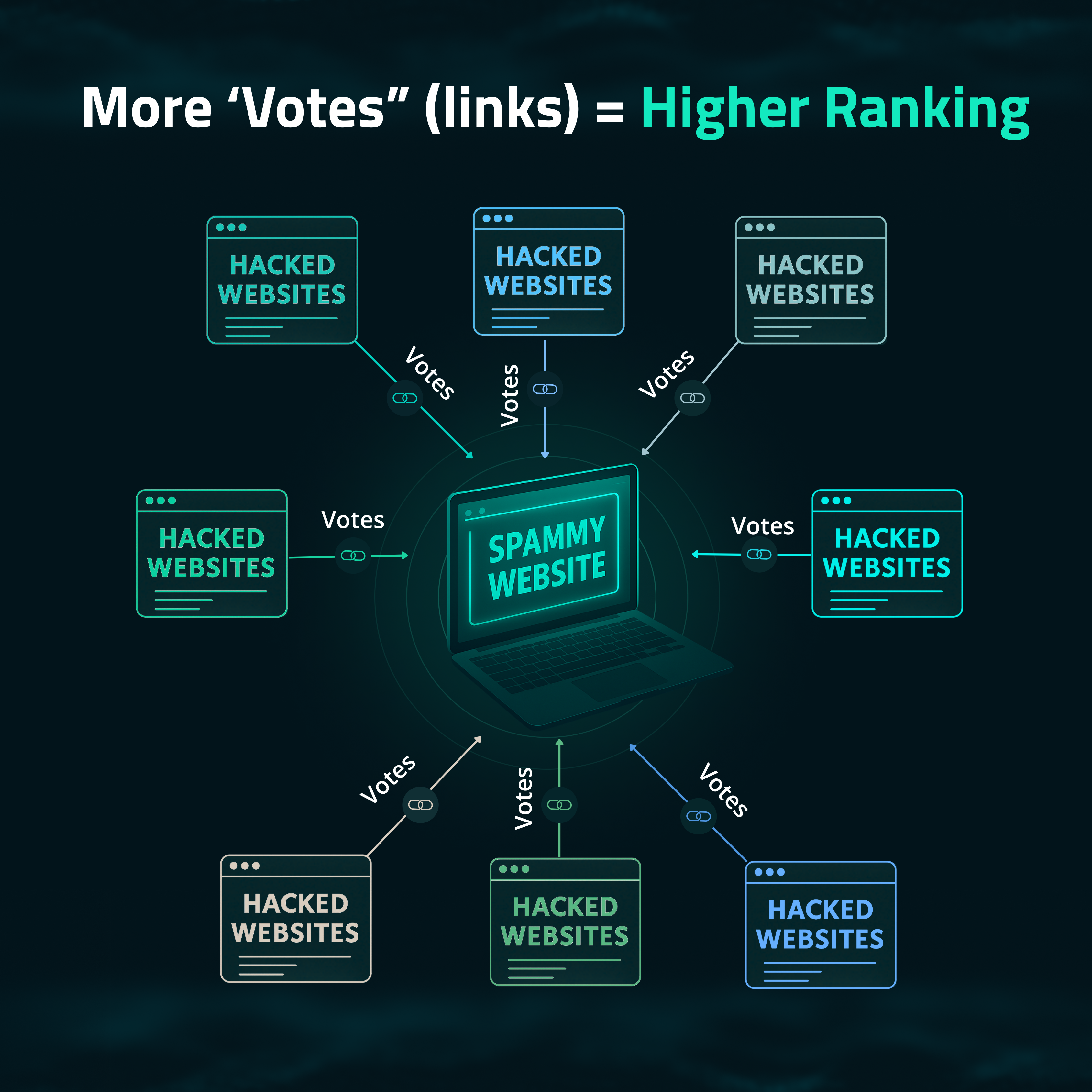
The key to understanding SEO spam is how Google’s search algorithm works. With over one billion websites present on the web, search engines need a way to rank them in order to show people relevant results when they search for things. One of the ways that search engines do this is to give more weight in search results to websites that a lot of other websites are linking to. A good example of this is if you search for “How do I fix _____” oftentimes websites like Reddit will come up near the top because many millions of people use that website and link to it frequently.
So, essentially, black hat SEO is an attempt to game search algorithms to “trick” them into thinking that these spam websites are more desirable than they actually are. In this way SEO spam is entirely driven by the desire to increase traffic to spam websites with the end goal of – you guessed it – profiting.
Browser Redirects
Another very common nuisance that website owners deal with are infections which redirect their website traffic to generally undesirable websites. Common culprits include online scams, adult video or dating websites, or sites that sell spammy knockoff products or pharma.
Not unlike the SEO spam mentioned earlier, browser redirects are a way for spammers and scammers to pump traffic to their shady websites. Except that in this case rather than stealthily lodging some backlinks into an infected website the attackers take a much more direct approach.
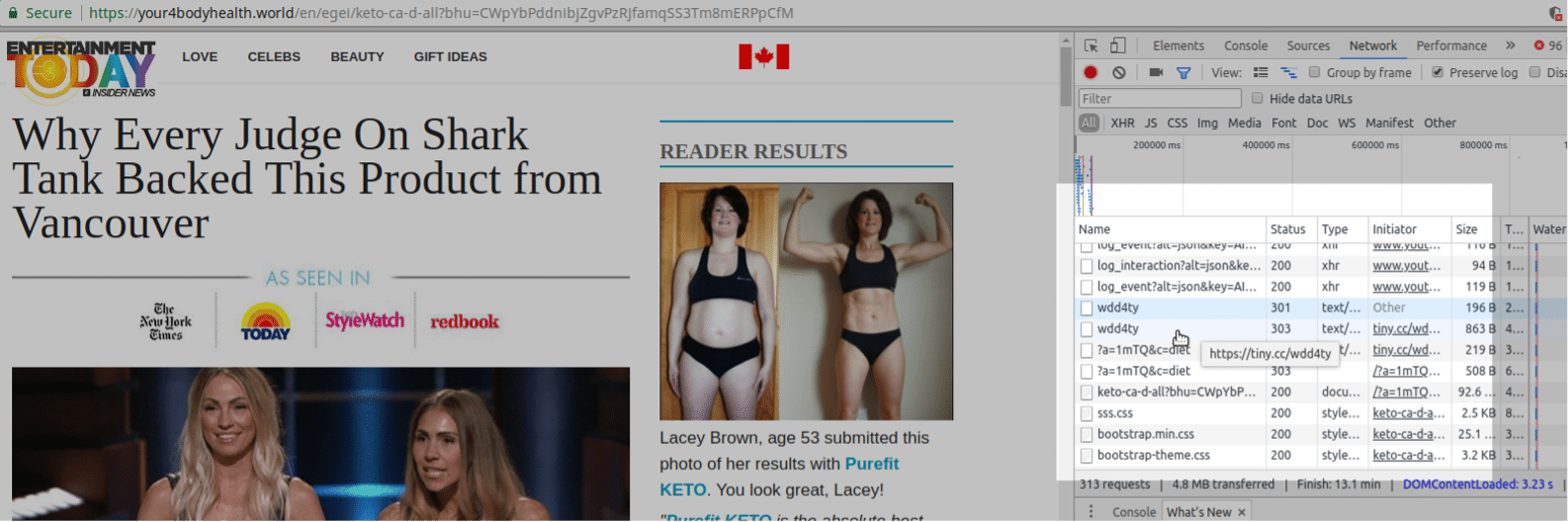
Websites considered “low quality” or “bottom of the barrel” or even ones that are very obvious scams don’t receive a lot of traffic for very good reason – people don’t want to visit them. So, the attackers resort to hijacking the traffic from legitimate websites in order to corral unsuspecting visitors to their own rubbish websites.
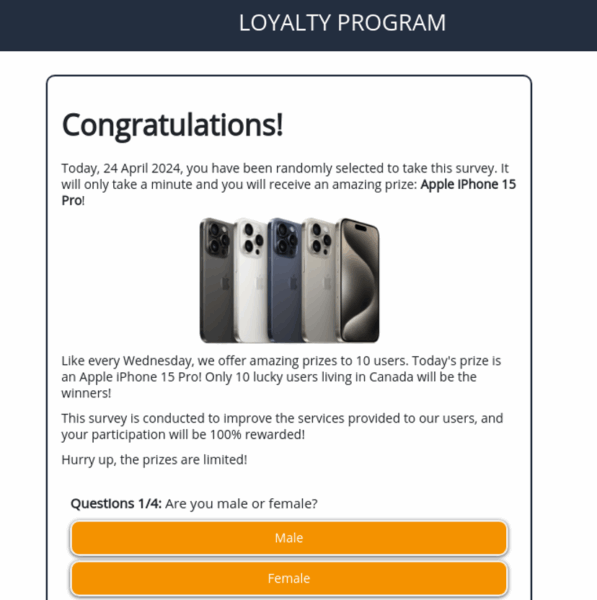
This is often done by modifying the website’s .htaccess file, core files, theme files, or by installing a malicious plugin into the compromised environment. Most people when faced with an obvious scam that indicates that you’re the “10,000th visitor, fill in your information to win a free iPhone” would know that it’s an obvious scam. However, for every few hundred people that get redirected, if even just one person falls for the scam, the attackers can still benefit.
Phishing
In the year twenty twenty-five almost everybody knows what phishing is; they even now educate kids about it in elementary school! Its connection to hacked websites, however, is not as well known.
As most of you know, phishing is when attackers set up a fake login page to look indistinguishable from a legitimate login page. Most often the attackers are aiming to steal credentials for banks, social media websites, and online retailers.
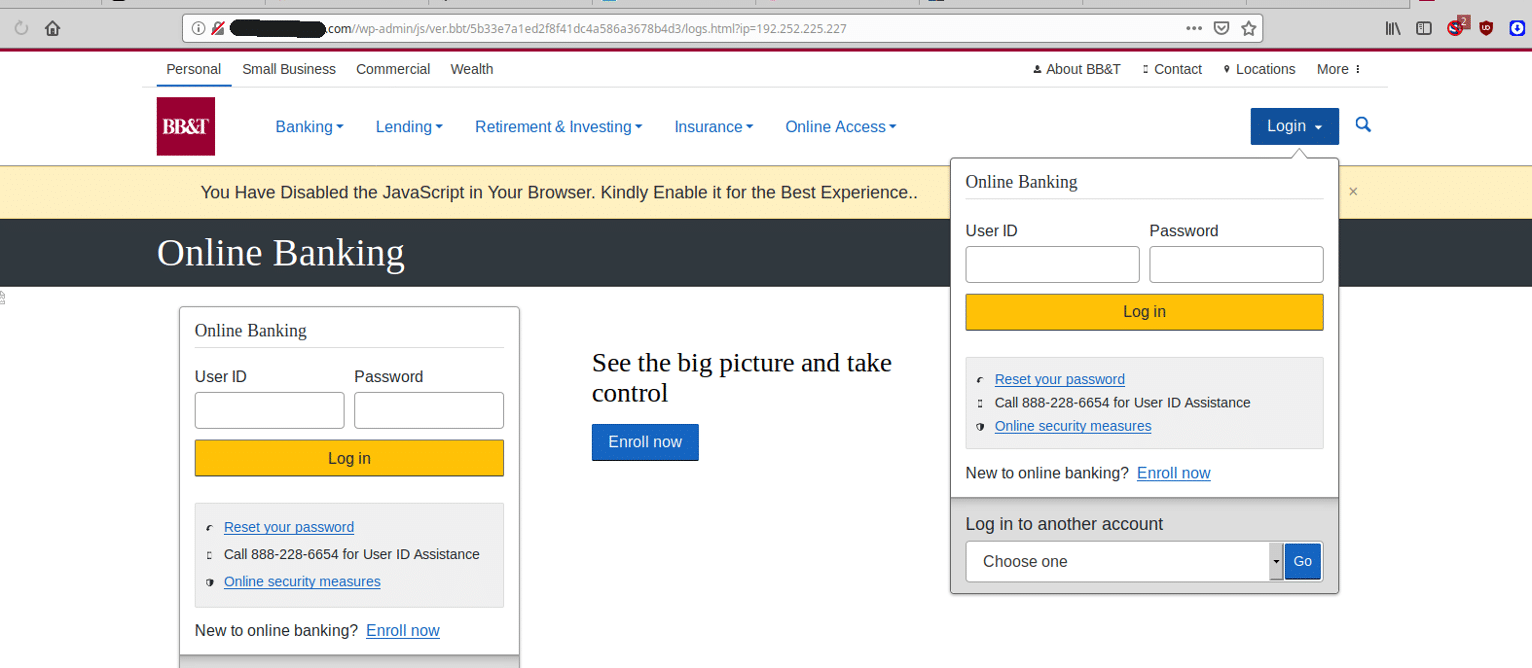
It’s worth examining exactly how phishing attacks relate to website security specifically. Now, phishing pages need to be hosted somewhere, and this typically involves domain names. Domains need to be purchased, and in order to do so, you need to provide your name, credit card number, and other identifying information. If your goal is to host illegal content like phishing this is not exactly an enticing prospect from the attacker’s perspective.
So, what do they do? They instead host their phishing pages on hacked websites that belong to other people.
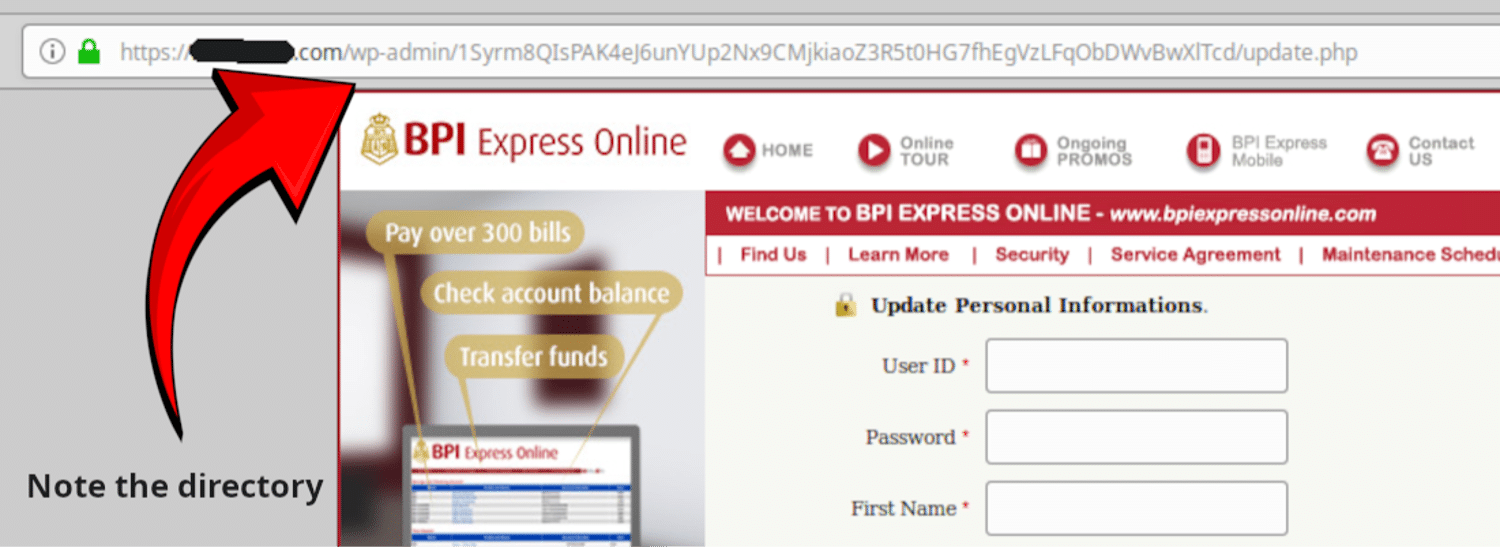
Phishing directories on hacked websites are oftentimes buried in obscure directories, sometimes lodged in core files, disguised as plugins or extensions. On hacked cPanel environments sometimes the attackers will even configure bogus/malicious subdomains such as this:
chasebank[.]infectedwebsite[.]comIn this way the attackers are able to remain hidden and anonymous while still being able to pilfer unsuspecting victim’s login information. Plus, as you can see in the above screen capture, the attackers can also sometimes take advantage of the infected website’s SSL certificate which grants them an extra layer of legitimacy.
Remember folks, always ensure that when entering in login details or personal information that it is to the official website and not an impersonator!
Fake Browser Updates / Ransomware
Ransomware attacks encrypt all files on the compromised filesystem. The attackers then demand that a ransom be paid (normally in Bitcoin or some other crypto currency) in order to decrypt the files. In order to entice users into deploying their malware, though, attackers need a way to trick people into installing it onto their systems. For this purpose they commonly use infected, otherwise legitimate websites.
Fake browser updates have been one of the most common website malware infections for many years. This malware is often dubbed Socgholish although many other copycat threat actors have jumped aboard the train. The malware hijacks the website environment and produces an overlay which tricks the user into downloading and installing malware disguised as an update to the victim’s browser like Chrome or Firefox.
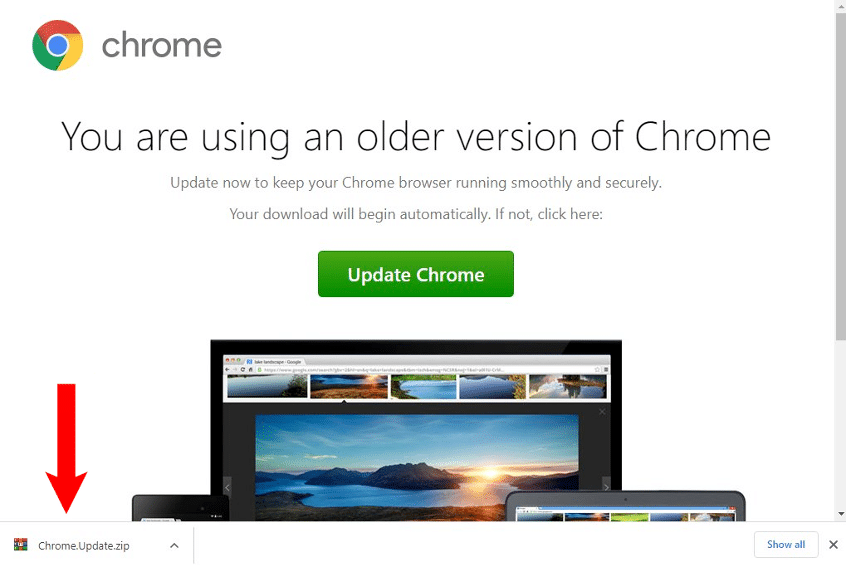
As malware attacks become more commonly known, users these days are increasingly practicing better and more cautious browsing habits. This is precisely why attackers target otherwise trustworthy websites that are oftentimes already well-known to the potential victims.
Fake browser updates tend to be the first stage of targeted ransomware attacks. Once the victim has installed the trojan application onto their (usually Windows) machine, the attackers have complete control over the environment. At this point they are able to detonate a ransomware attack onto the compromised device, or even the entire network (depending on how it’s configured).

Other times the attackers will actually encrypt the files of the website itself:

Users that are unfortunate enough to fall victim to a fake browser update on their work or corporate network are in for a reckoning, as the whole armada of computers on the same network could potentially be compromised.
For the record, it’s not generally recommended to pay the ransom as there is no guarantee that they’ll be true to their word. It’s better to keep this as a reminder to make sure that you have backups of your important files stowed away for a rainy day.
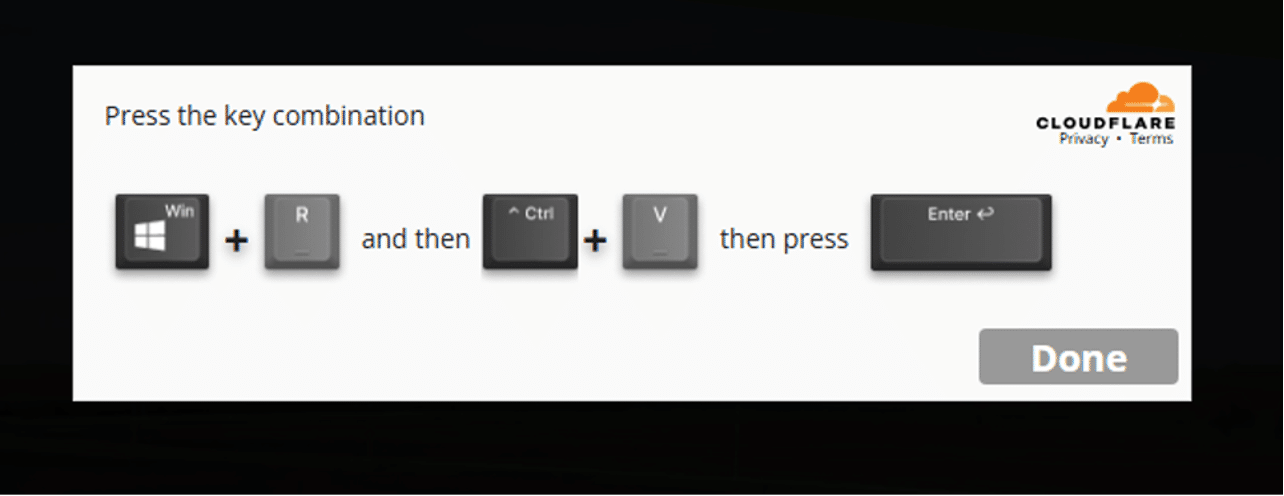
Fake CloudFlare and CAPTCHA Overlays
Another similar infection that we’ve seen a huge increase in as of late produces fake CloudFlare or Google CAPTCHA verification overlays:
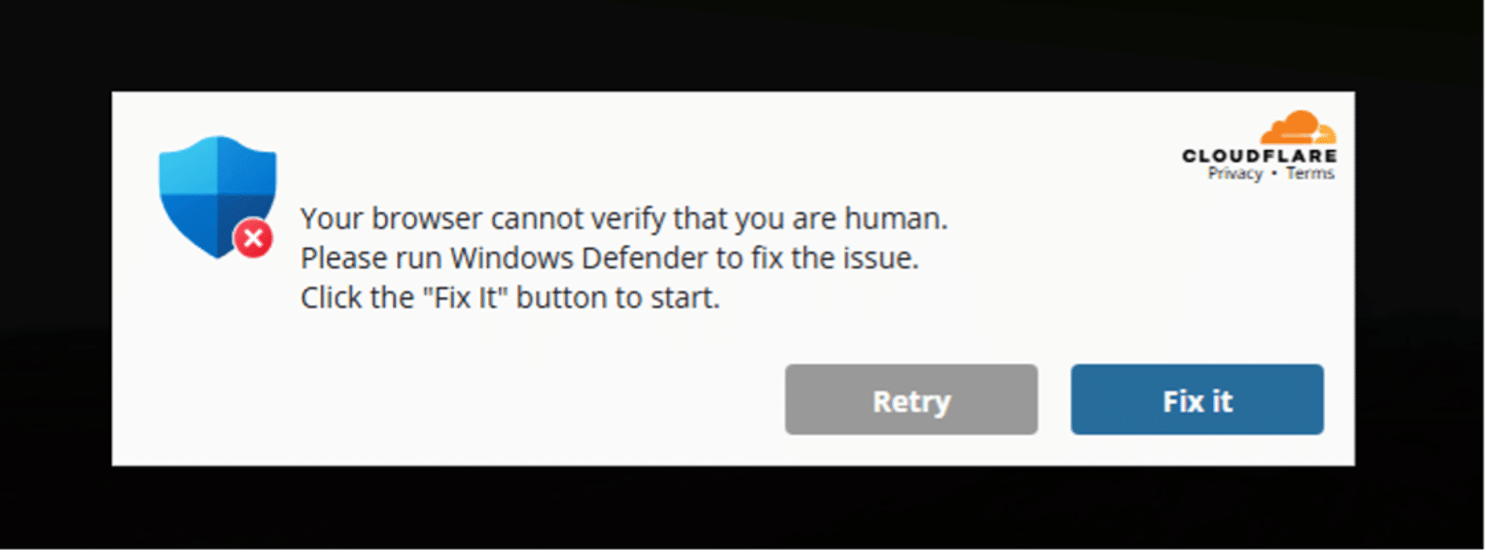
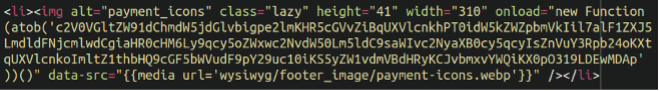
The user is then prompted to run some malicious powershell commands which, similar to Socgholish, infect the target computer with a remote access trojan:
It’s entirely possible that the attackers could also deploy ransomware, but these infections tend to be associated with Lumastealer malware which harvests login credentials from victim machines as well as drain cryptocurrency wallets. In any event, we also see a clear financial motivation behind these attacks.
Remember, folks! Only download and install browser updates from the official source, and if anybody (whether it be a website or tech support scammer) asks you to press Windows + R, run away. And if in doubt, don’t click!
MageCart / CC Theft
Perhaps the most overt connection to attackers making a profit off of website malware is the ongoing MageCart credit card theft infections. Commonly targeting eCommerce platforms such as WooCommerce/WordPress and Magento, infected storefronts leak credit card and other identifying data to attackers who then turn around and sell it on the black market for a profit.
MageCart has been a scourge to online retailers since roughly 2015 when the first major card theft campaigns began on the heels of several severe vulnerabilities disclosed within the Magento eCommerce platform. It’s worth mentioning that many independently run online stores are not properly maintained and many of them lack updates or critical security patches, rendering them vulnerable to attacks and the ensuing card theft which occurs.
Online credit card theft is a profitable business run by criminal syndicates. Zero day exploits affecting major eCommerce platforms (particularly Magento) can sell for tens of thousands of dollars as attackers are virtually guaranteed to make substantial profits by pilfering card details from compromised stores, although in more recent years WordPress / WooCommerce appears to have taken the lead in infections, due to its sheer popularity.
If you are responsible for maintaining an online website then make sure that you keep all core files and extensions up to date, and pay special attention to any available security patches which require installation.
Defacements
With all that being said it must be mentioned that from time to time there are attackers who aren’t motivated by profit or financial gain, but for the love of the game. This is where defacements come into play.
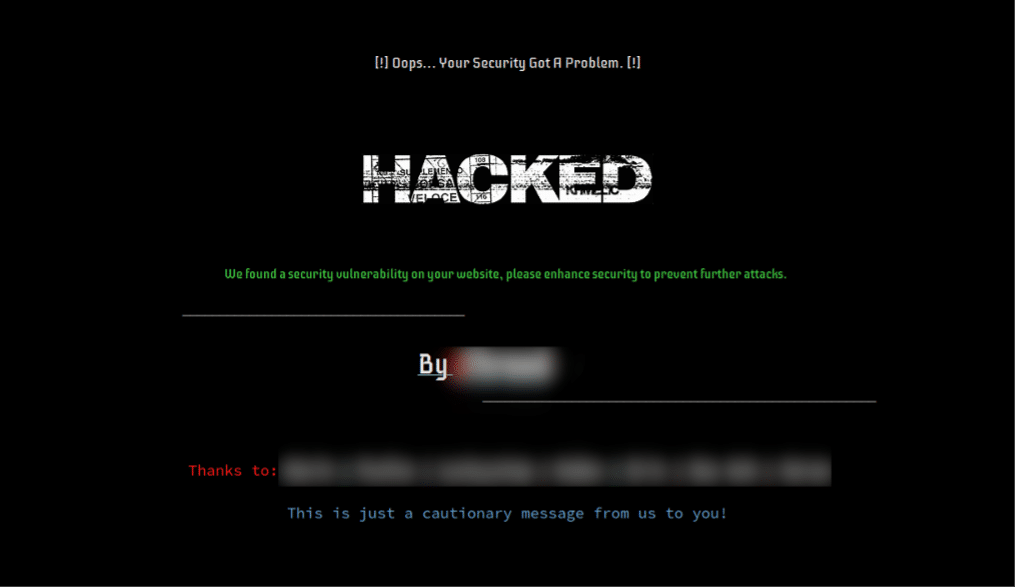
Defacements don’t make any money, don’t compromise any personal information or produce anything meaningful for the attackers, except perhaps notoriety. Defacements are the digital equivalent of graffiti tags. Most often they simply contain the online handle of the attacker, although sometimes they contain ideological or religious messages.
These attackers aren’t aiming to make any money, just a little street cred for the most part.
Conclusion
There’s a lot of money to be made in the criminal world, that’s nothing new. What is new, though, is that the criminal world has shifted into the online world over the course of this century.
In some ways the web has made the life of criminals much easier, allowing them to pick someone’s pocket from half way around the world and from the comfort of their own home.
Website owners and regular users alike need to be on guard now more than ever.